Comparison of Android applications for data encryption
The purpose of this article is to compare three Android applications for data encryption - LUKS Manager, Cryptonite and CyberSafe Mobile. It should be noted right away that the comparison will be honest, and not with the aim of highlighting the advantages of a particular program. Each program has its own advantages and disadvantages, in this article they will be disclosed in full.

First of all, I want to note why exactly these applications participate in the review. With the CyberSafe Mobile program , I think everything is clear, because you read the CyberSoft blog , so it’s quite logical to see our program in the review. But the rest of the programs were chosen by the so-called Cauchy method , it is also a method of scientific poking, that is, randomly. Of course, when choosing programs, their popularity and ratings were taken into account. So, the Cryptonite program currently has more than 50 thousand downloads and its rating is 4.3, and the LUKS Manager program has the same rating, but five times less downloads - more than 10 thousand.
For Android, many data encryption programs have been developed, so we physically will not be able to consider all of them. Perhaps in the future a similar review of other programs and their comparison with the CyberSafe Mobile program will be written. In the meantime, we restrict ourselves to the previously mentioned programs.
LUKS Manager is one of the first real encryption programs in Android. Before it, the “encryption” programs didn’t actually do encryption, but did all kinds of nonsense, like assigning a hidden attribute to a file.
The LUKS Manager program left a double impression. I'll start in order - from the very installation of the program. The program requires that you have root access, and SuperSU and BusyBox must be installed. The requirement of root access is a characteristic feature of all serious encryption programs in Android, since there is little that can be done without maximum privileges. But the requirement of SuperSU and BusyBox gave me the idea that the program, in fact, does nothing by itself, and instead of using Android system calls, it uses BusyBox utilities. In other words, the program is just a shell for system commands. Well, okay, novice users are unlikely to deal with all these commands, so the shell is just what you need - the main thing is that it works.
I already had root access to my device, SuperSU was installed, but BusyBox had to be installed from the Play Market. However, after installing BusyBox, the program still happily informed me that it did not see it (Fig. 1).
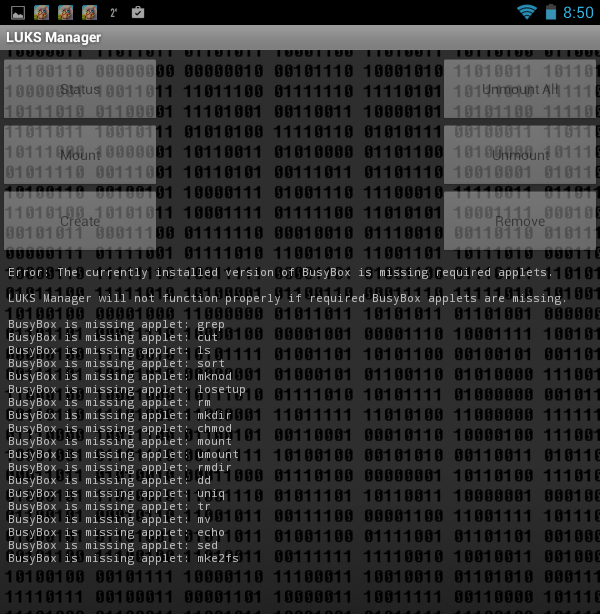
Fig. 1. The LUKS Manager program does not see the installed BusyBox.
I will not describe what I did so that the program “saw” it, I will only say that the tablet reboot helped. Somehow it smacks of Windows even, and not UNIX, which, anyway, is Android. By the way, bullying occurred on the Acer B1 tablet with Android 4.1.2. Not a single tablet was injured as a result of experiments :)
After rebooting, the program still started (Fig. 2). The program interface is very simple. I would even say Spartan. I crop the screenshots so as not to reduce their size and so that you can see them better.
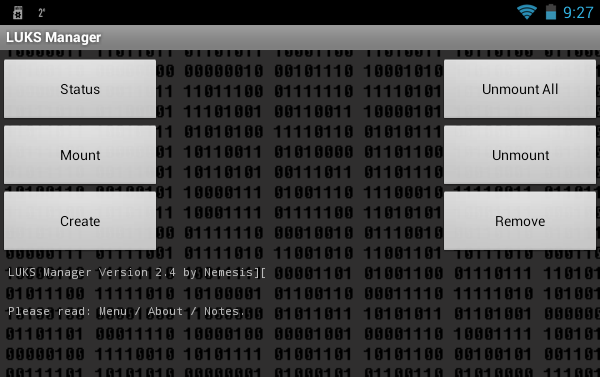
Fig. 2. LUKS Manager
program. The functionality of the program is also Spartan. You can view which container is mounted ( Status button ), create a container ( Create button ), mount it ( Mount button ) and unmount it ( Unmount button ), unmount all containers ( Unmount All ), remove the container ( Remove) The fact that the program can create encrypted containers and mount them is good. But nowadays, I want to see the possibility of cloud encryption, the ability to mount network folders so that you can work with a remote container. I also wanted to see the built-in file manager in case the user had no such program installed. After all, and so for LUKS Manager to work, I had to root the device, install SuperSu and BusyBox. It turns out that the file manager is also needed. The basic functionality (display of files and folders) in the program is, was it really difficult to add functions to copy / move / delete files and folders? To access the "explorer" built into the program, press the button to open the program menu and select the Explore command . However, we will talk more about this.
Let's look at the program in work. Click the Create button to create the container. The program will prompt you to select the directory in which the container will be stored (Fig. 3, Fig. 4).
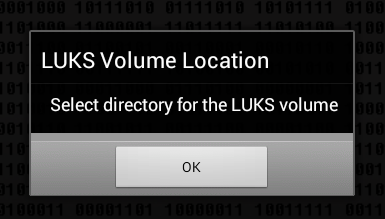
Fig. 3. Click OK
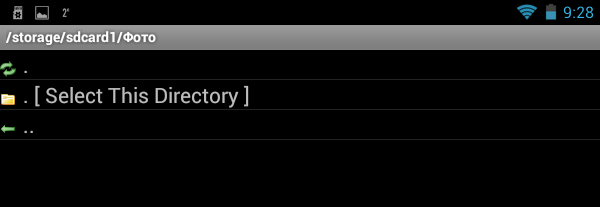
. Fig. 4. Select a directory and click Select This Directory
Next you need to enter the name of the container (Fig. 5), the password for access (Fig. 6) to it and the size of the container (Fig. 7). The program does not display the entered password and does not offer to enter a password confirmation, therefore there is a chance of an error when entering the password - then the created container will not be mounted and this should be taken into account when working with the program.
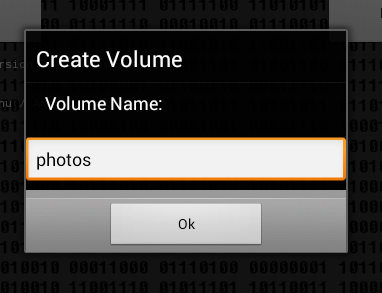
Fig. 5. Name of container
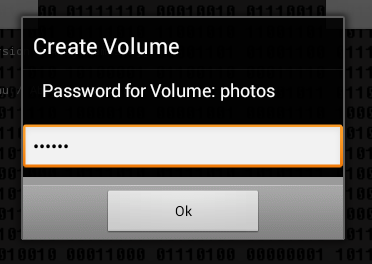
Fig. 6. Password to access the container
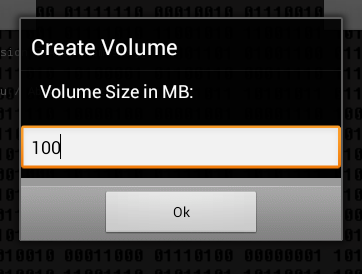
Fig. 7. Container size
The next question is how to format the container: as FAT (will be compatible with FreeeOTFE) or as ext2 (Fig. 8). LUKS Manager creates containers compatible with the FreeOTFE Windows program. As for me, it would be better if the program supported TrueCrypt. However, it should be noted that at last FreeOTFE now has support for 64-bit versions of Windows, which makes it possible to more fully use the LUKS Manager + FreeOTFE bundle on modern computers. It would be nice if LUKS Manager had the ability to remotely mount the container, which is located on a Windows-based computer. Then you could create a container on your PC using FreeOTFE and remotely mount it on your Android device. The advantage of this solution is that there is no need to litter the device’s memory, and even the data itself would not be physically stored on an Android device, the chances of losing it are much greater than a regular PC.
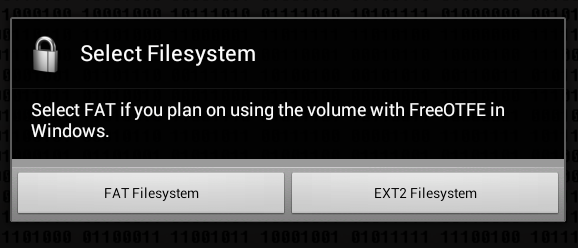
Fig. 8. How to format the container?
Next, the program will inform you that the container is created and mounted to the / mnt / sdcard / <container name> folder, in our case it is / mnt / sdcard / photos (Fig. 9). In the program settings, you can change the name of this folder.
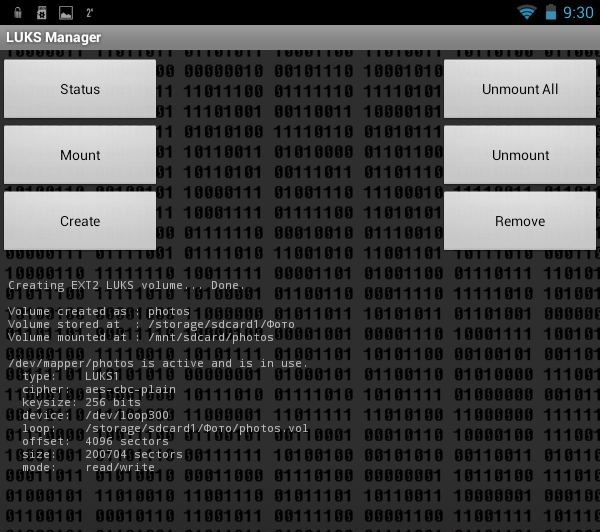
Fig. 9. The container is mounted. It
remains to run some third-party file manager and copy the files to the created container (Fig. 10).
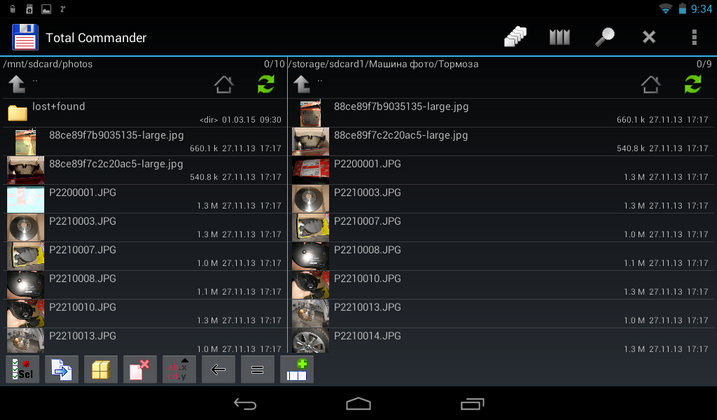
Fig. 10. Files are copied.
We try to unmount the container ( Unmount button ), while the program displays a window that allows you to choose which container to unmount (Fig. 11).
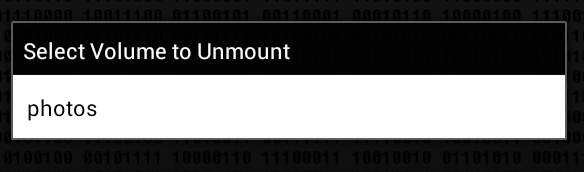
Fig. 11. Unmounting the container
After that, run the file manager and go to / mnt / sdcard /. The photos folder exists and for some reason it has not been deleted, but access to it is prohibited (Fig. 12). Typically, these temporary folders should be deleted after unmounting. But these are trifles, in principle.
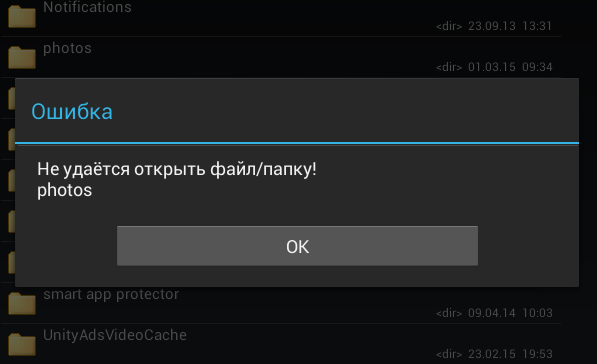
Fig. 12. Access to / mnt / sdcard / photos is denied.
Now let's see what the program has in the settings. Press the menu button and select the Preferences command (Fig. 13). Here is what is useful we see (Fig. 14):

Fig. 13. Program menu
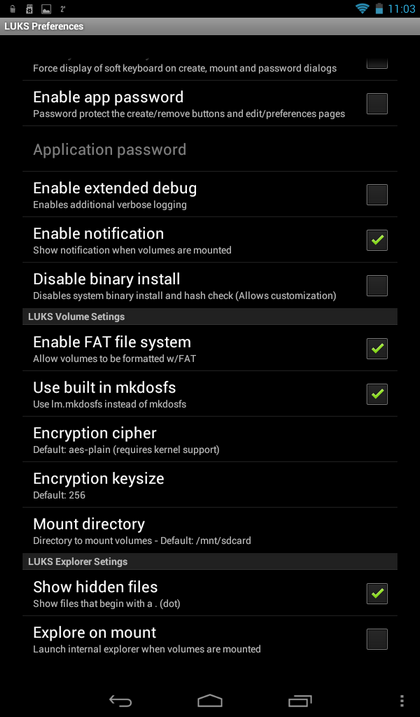
Fig. 14. Program settings
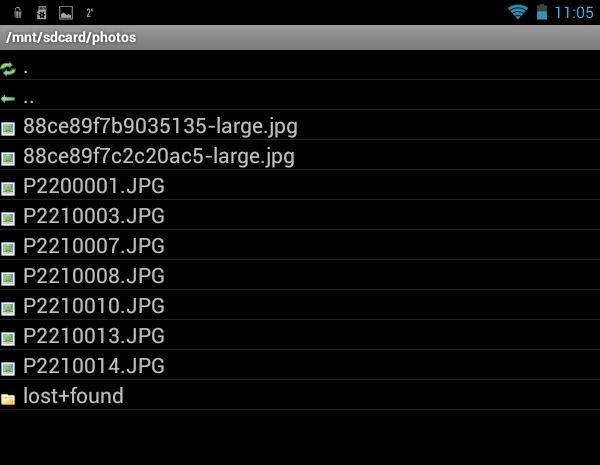
Fig. 15. Built-in file manager

Fig. 16. Window with information about the file
Now, to summarize. The advantages of the LUKS Manager program include:
But the program has many shortcomings:
The Cryptonite program is quite young and is at the testing stage, so it can hardly be used to encrypt some very important data. In fairness, it should be noted that developers honestly warn about this when they first launch the program (Fig. 17).
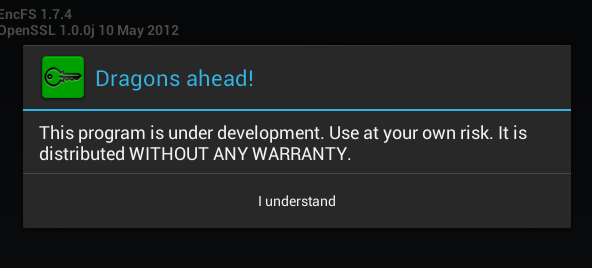
Fig. 17. The first launch of Cryptonite
With regard to system requirements, the program needs root access and a kernel with FUSE support (Filesystem in Userspace, File system in user space). The requirement of FUSE support can be safely attributed to the shortcomings of the program, since not all devices support FUSE. You do not need to reinstall any additional programs (except for the file manager).
The functionality of the program is already slightly better than that of LUKS Manager. She is able to create not only local containers, but also encrypt your files on DropBox. Support for DropBox automatically means support for cloud encryption, so this program already stands head and shoulders higher than LUKS Manager.
In fig. Figure 18 shows the Cryptonite program after closing an annoying message that you are using an experimental version of the program. The Dropbox tab allows you to encrypt files on your Dropbox, the Local tab is used to create a local container, and on the Expert tab, an ordinary user has nothing to do.
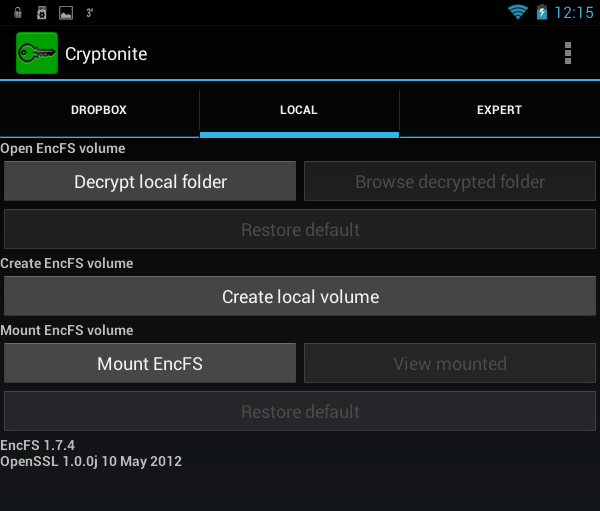
Fig. 18. Cryptonite program
To create a local container, click the buttonCreate local volume , after which you will again see a warning that this function is experimental (Fig. 19). Next, as usual, you need to select the encryption method (Fig. 20), the location of the container, enter the password and confirm it (Fig. 21). I liked that the program offers to enter a password confirmation, which eliminates its incorrect entry when creating the container.
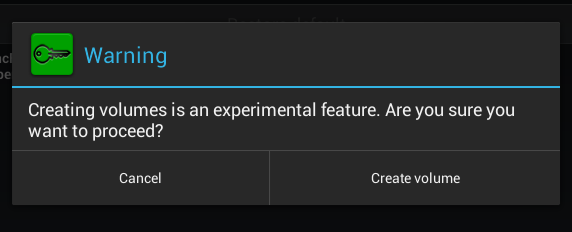
Fig. 19. Again annoying warning
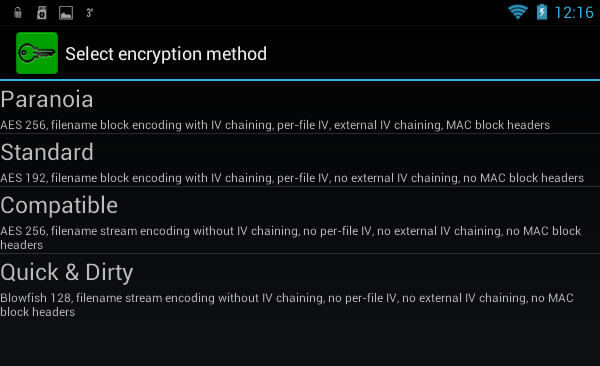
Fig. 20. The choice of encryption method
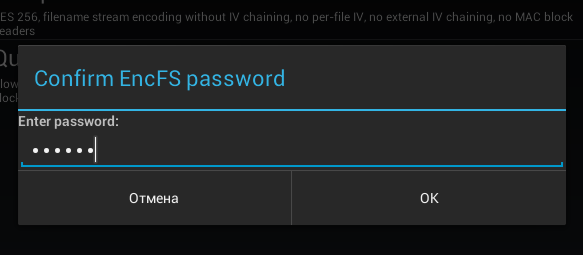
Fig. 21. Entering password confirmation You
can mount the created container with the Mount EncFS command on the Local tab. The program will prompt you to select a container. After entering the password to it, the container will be mounted to the /mnt/sdcard/csh.cryptonite/mnt directory (Fig. 22). The mounting directory is set in the program settings (Fig. 23).
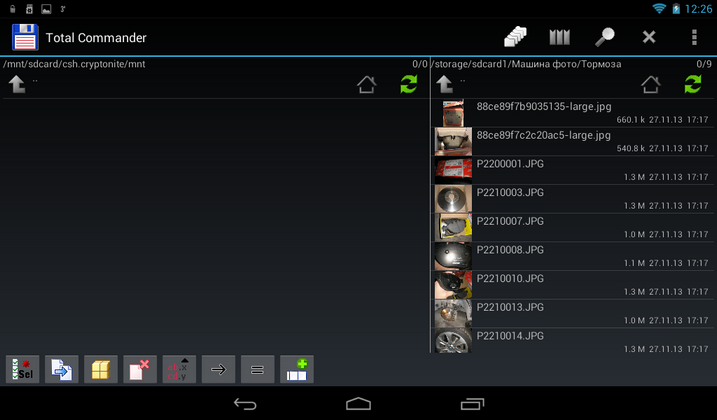
Fig. 22. The container is mounted

Fig. 23. Program
settings There is nothing particularly interesting in the settings, except for the Mount point folder , as well as the Chuck Norris mode, which allows you to disable annoying and meaningless warnings. You can also enable the use of built-in file manager when mounting the container ( Use built-in file browser), but given the traditionally meager functionality of this part of the program (Fig. 24), I do not recommend including this parameter. This “file manager” cannot even open a file. It allows you to only view the contents of the container and nothing more.

Fig. 24. Built-in container viewer.
Advantages of the program:
Disadvantages:
We have already reviewed the CyberSafe Mobile program on our blog, so there will be no detailed description of it. I strongly recommend reading the article “Sharing cryptodisks on PC and Android” , which describes one of the cases of using the program.
Therefore, instead of reviewing the program, so as not to be repeated, it will be compared with the programs previously described in this article.
The first thing to note is that you do not need root privileges to work with the program. Yes, in this case the program’s functionality will be limited, and you won’t be able to mount the created safe (this is the name of the encrypted container in CyberSafe Mobile), but your smartphone will not “fly off” the guarantee if you get root access. However, given that the program has a full-fledged file manager, this is not a problem. You can work with files in a safe without mounting it and installing a third-party file manager. For security reasons, the program does not allow you to take some screenshots, so the window of the built-in file manager, which displays the contents of the safe, could only be photographed with an ordinary camera (Fig. 25). As you can see, the program has a full-fledged file manager. It’s not ES Explorer, but unlike the previously described programs, the built-in file manager of Cybersafe Mobile can manage files - copy, move, delete, create new files and folders. I apologize for the quality of the picture, but in order to avoid glare, the tablet was photographed without a flash, so the photo is a bit dark.
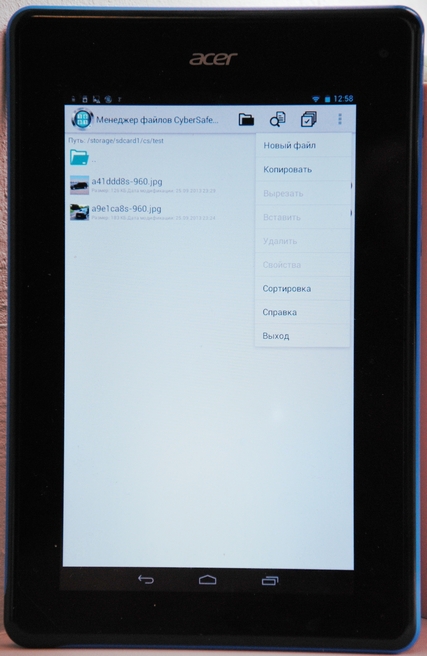
Fig. 25. Built-in file manager of CyberSafe
In the settings for mounting the program, you can choose (Fig. 26):
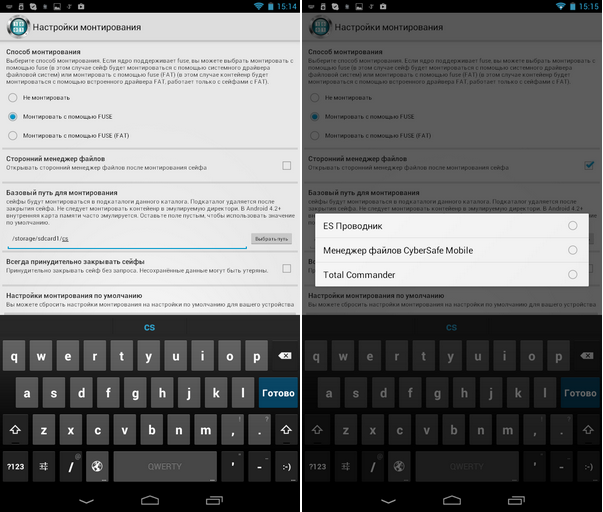
Fig. 26. Mounting options
It is also worth noting the Russian-language interface of the CyberSafe Mobile program, which makes it easier for users who do not speak English to work with the program (Fig. 27).
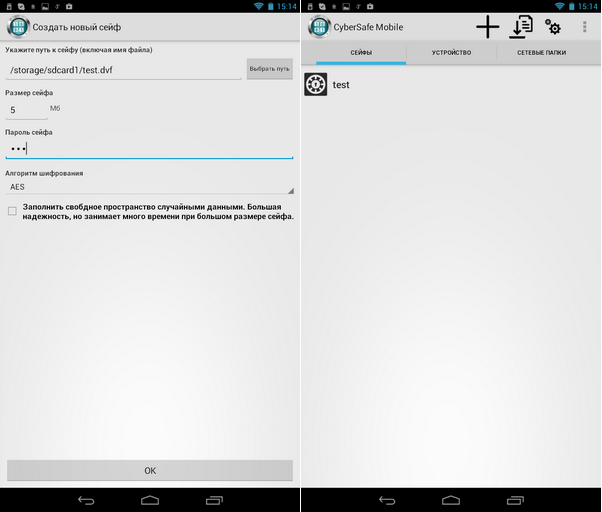
Fig. 27. The program interface. Creating a safe
Only thanks to all this (the ability to work without root and FUSE, a full-fledged file manager and a Russian-language interface) the program is a cut above LUKS Manager and Cryptonite. But that is not all. The program has a number of functions that lead to knockout of competitors.
Firstly, it supports the GOST algorithm - unlike other programs that use only AES or Blowfish (Fig. 28).
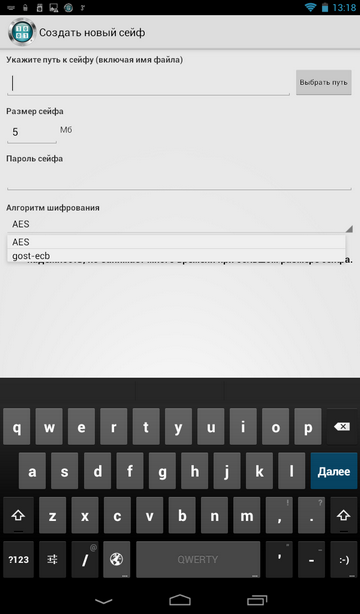
Fig. 28. The choice of encryption algorithm when creating a safe
Secondly, the program supports mounting network folders, which allows the use of a remote safe located on a remote PC (Fig. 29). The principle is simple: the container itself is stored on a PC, it is shared over the network. It turns out that the container opens on the smartphone, on the PC it is always stored in encrypted form, data over the network is also transmitted encrypted, which eliminates their interception. All data encryption and decryption operations are carried out on a mobile device. Even if you lose your device, no one will even gain access to encrypted data, since it is stored on a remote computer.
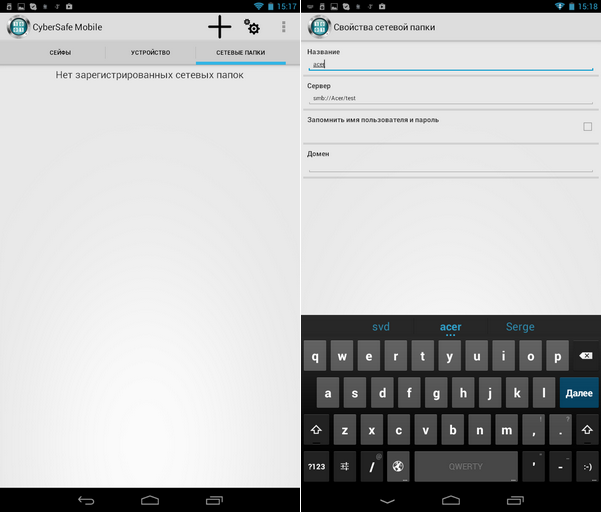
Fig. 29. Working with network folders
You can create a safe both using the CyberSafe Mobile program and using the desktop version of the program - CyberSafe Top Secret. It should be noted that to fully work with the safe, the CyberSafe Top Secret program is not needed - you can create a safe on your mobile device and copy it to your PC. In other words, you do not need to buy the CyberSafe Top Secret program for remote use of the safe on your smartphone. But if you need to organize the sharing of the safe on your PC and Android , then, of course, you will need the CyberSafe Top Secret program.
When installing the free URSafe Media Redirector program, it is possible to automatically redirect the photos you create (and other files, such as documents) to a safe that is physically located on the remote computer. More about this you can read in the article "Protection of personal photos on Android phones" . And in the article“Storing data in a cryptocontainer on a remote server and working with them from Android devices” shows how to store containers on a remote server, and not on a PC connected to your local wireless network.
Everything has flaws. However, CyberSafe Mobile has almost none. The disadvantages include the need to support FUSE, but this disadvantage is offset by the fact that the created safes can be opened without mounting, but only in the built-in file manager. It should also be noted that the program is paid, but its price is not high for a program of this class (do not forget what functionality the program has and do not forget that it supports GOST in addition to the AES algorithm). Well, I don’t really like the impossibility of creating some screenshots of the program, but it’s better from a security point of view :)
Now to summarize. Advantages of the CyberSafe Mobile program:
Disadvantages:
As you can see, there are no such shortcomings in the program and their selection is more my nit-picking for the program, so that no one will accuse me of bias. I think no one doubts that the winner of our comparison today is the CyberSafe Mobile program. If you have any questions, we will be happy to answer them in the comments to this article.

What determines the choice of applications?
First of all, I want to note why exactly these applications participate in the review. With the CyberSafe Mobile program , I think everything is clear, because you read the CyberSoft blog , so it’s quite logical to see our program in the review. But the rest of the programs were chosen by the so-called Cauchy method , it is also a method of scientific poking, that is, randomly. Of course, when choosing programs, their popularity and ratings were taken into account. So, the Cryptonite program currently has more than 50 thousand downloads and its rating is 4.3, and the LUKS Manager program has the same rating, but five times less downloads - more than 10 thousand.
For Android, many data encryption programs have been developed, so we physically will not be able to consider all of them. Perhaps in the future a similar review of other programs and their comparison with the CyberSafe Mobile program will be written. In the meantime, we restrict ourselves to the previously mentioned programs.
LUKS Manager
LUKS Manager is one of the first real encryption programs in Android. Before it, the “encryption” programs didn’t actually do encryption, but did all kinds of nonsense, like assigning a hidden attribute to a file.
The LUKS Manager program left a double impression. I'll start in order - from the very installation of the program. The program requires that you have root access, and SuperSU and BusyBox must be installed. The requirement of root access is a characteristic feature of all serious encryption programs in Android, since there is little that can be done without maximum privileges. But the requirement of SuperSU and BusyBox gave me the idea that the program, in fact, does nothing by itself, and instead of using Android system calls, it uses BusyBox utilities. In other words, the program is just a shell for system commands. Well, okay, novice users are unlikely to deal with all these commands, so the shell is just what you need - the main thing is that it works.
I already had root access to my device, SuperSU was installed, but BusyBox had to be installed from the Play Market. However, after installing BusyBox, the program still happily informed me that it did not see it (Fig. 1).
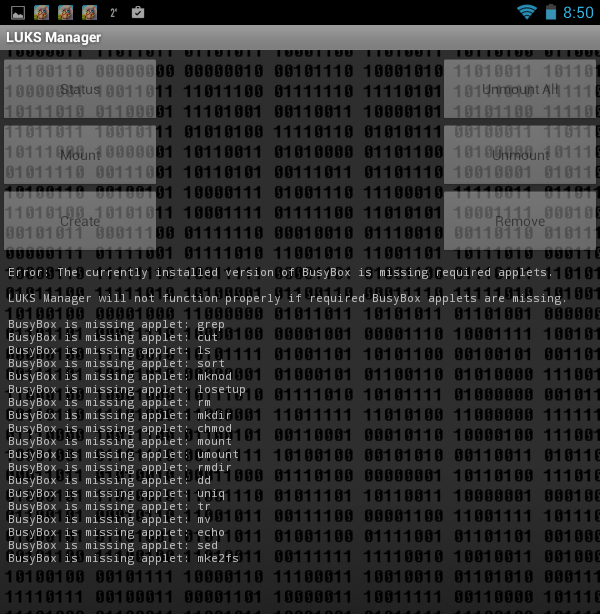
Fig. 1. The LUKS Manager program does not see the installed BusyBox.
I will not describe what I did so that the program “saw” it, I will only say that the tablet reboot helped. Somehow it smacks of Windows even, and not UNIX, which, anyway, is Android. By the way, bullying occurred on the Acer B1 tablet with Android 4.1.2. Not a single tablet was injured as a result of experiments :)
After rebooting, the program still started (Fig. 2). The program interface is very simple. I would even say Spartan. I crop the screenshots so as not to reduce their size and so that you can see them better.
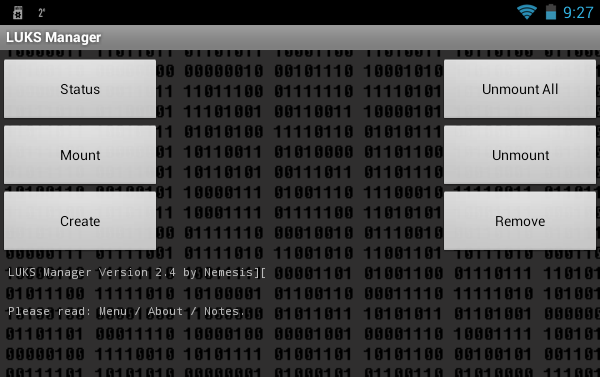
Fig. 2. LUKS Manager
program. The functionality of the program is also Spartan. You can view which container is mounted ( Status button ), create a container ( Create button ), mount it ( Mount button ) and unmount it ( Unmount button ), unmount all containers ( Unmount All ), remove the container ( Remove) The fact that the program can create encrypted containers and mount them is good. But nowadays, I want to see the possibility of cloud encryption, the ability to mount network folders so that you can work with a remote container. I also wanted to see the built-in file manager in case the user had no such program installed. After all, and so for LUKS Manager to work, I had to root the device, install SuperSu and BusyBox. It turns out that the file manager is also needed. The basic functionality (display of files and folders) in the program is, was it really difficult to add functions to copy / move / delete files and folders? To access the "explorer" built into the program, press the button to open the program menu and select the Explore command . However, we will talk more about this.
Let's look at the program in work. Click the Create button to create the container. The program will prompt you to select the directory in which the container will be stored (Fig. 3, Fig. 4).
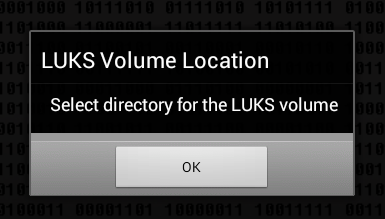
Fig. 3. Click OK
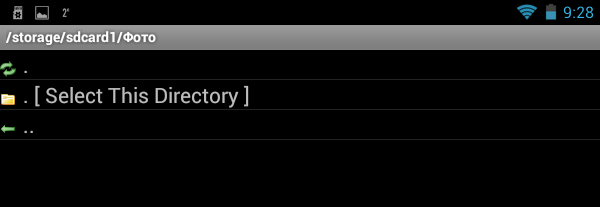
. Fig. 4. Select a directory and click Select This Directory
Next you need to enter the name of the container (Fig. 5), the password for access (Fig. 6) to it and the size of the container (Fig. 7). The program does not display the entered password and does not offer to enter a password confirmation, therefore there is a chance of an error when entering the password - then the created container will not be mounted and this should be taken into account when working with the program.
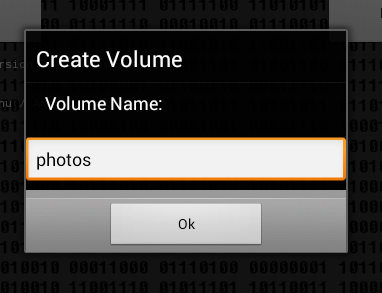
Fig. 5. Name of container
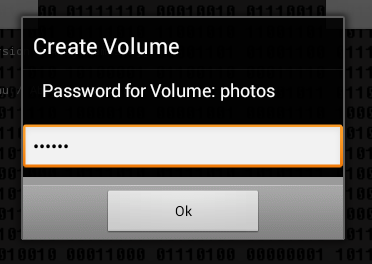
Fig. 6. Password to access the container
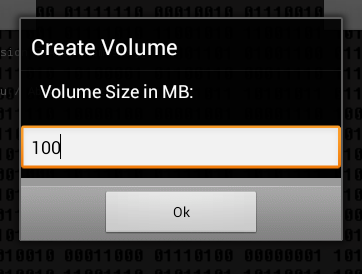
Fig. 7. Container size
The next question is how to format the container: as FAT (will be compatible with FreeeOTFE) or as ext2 (Fig. 8). LUKS Manager creates containers compatible with the FreeOTFE Windows program. As for me, it would be better if the program supported TrueCrypt. However, it should be noted that at last FreeOTFE now has support for 64-bit versions of Windows, which makes it possible to more fully use the LUKS Manager + FreeOTFE bundle on modern computers. It would be nice if LUKS Manager had the ability to remotely mount the container, which is located on a Windows-based computer. Then you could create a container on your PC using FreeOTFE and remotely mount it on your Android device. The advantage of this solution is that there is no need to litter the device’s memory, and even the data itself would not be physically stored on an Android device, the chances of losing it are much greater than a regular PC.
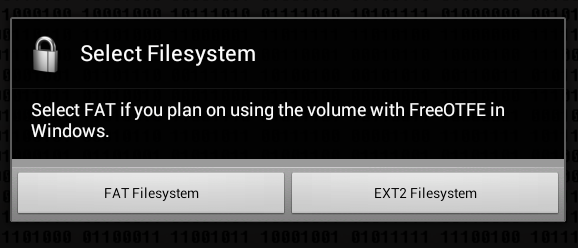
Fig. 8. How to format the container?
Next, the program will inform you that the container is created and mounted to the / mnt / sdcard / <container name> folder, in our case it is / mnt / sdcard / photos (Fig. 9). In the program settings, you can change the name of this folder.
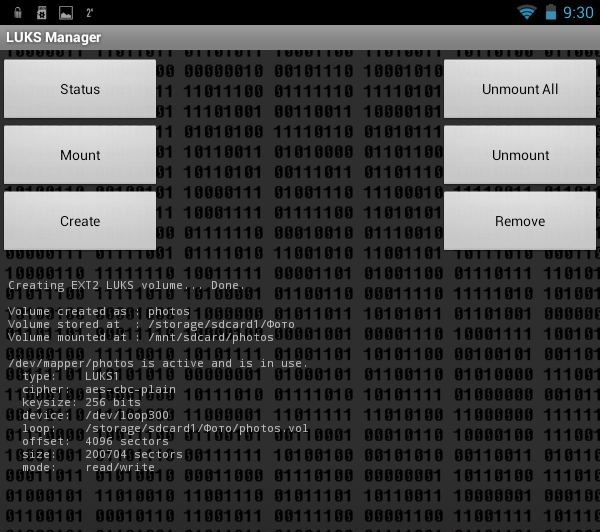
Fig. 9. The container is mounted. It
remains to run some third-party file manager and copy the files to the created container (Fig. 10).
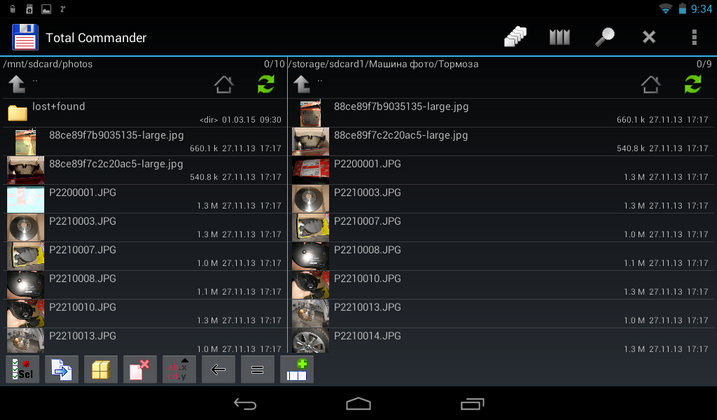
Fig. 10. Files are copied.
We try to unmount the container ( Unmount button ), while the program displays a window that allows you to choose which container to unmount (Fig. 11).
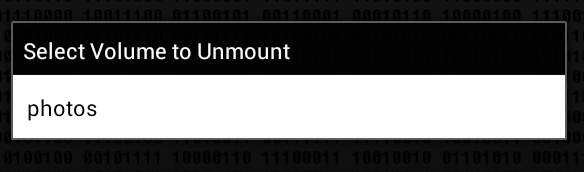
Fig. 11. Unmounting the container
After that, run the file manager and go to / mnt / sdcard /. The photos folder exists and for some reason it has not been deleted, but access to it is prohibited (Fig. 12). Typically, these temporary folders should be deleted after unmounting. But these are trifles, in principle.
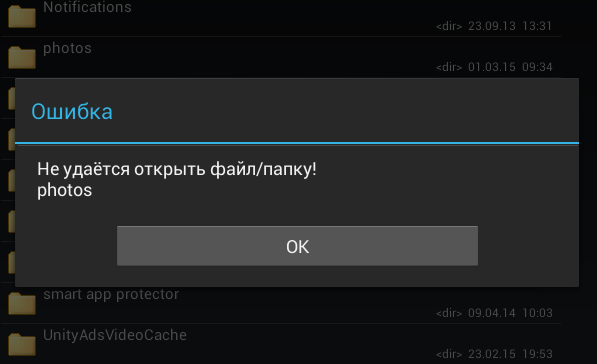
Fig. 12. Access to / mnt / sdcard / photos is denied.
Now let's see what the program has in the settings. Press the menu button and select the Preferences command (Fig. 13). Here is what is useful we see (Fig. 14):
- Encryption keysize - encryption key size, default 256 bits.
- Mount directory - the folder to which the containers will be mounted.
- Explore on mount - if this option is enabled, after mounting the container, its contents will be displayed in the built-in "explorer" (Fig. 15). However, the built-in file manager allows you to only view the contents of the container, it does not allow you to manage files. The maximum that is useful in it is a window with information about the file that appears if you click on the file in the container and hold your finger for a while (Fig. 16).

Fig. 13. Program menu
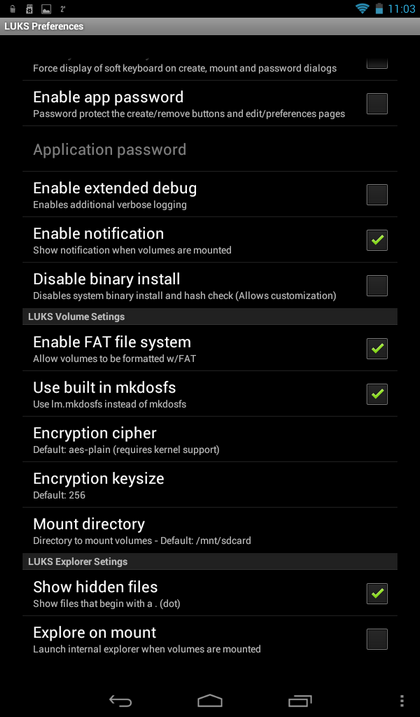
Fig. 14. Program settings
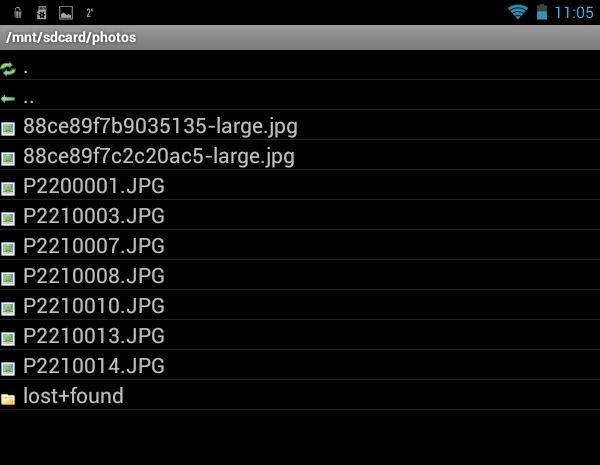
Fig. 15. Built-in file manager

Fig. 16. Window with information about the file
Now, to summarize. The advantages of the LUKS Manager program include:
- The program is free, but requires a paid BusyBox (however, there is also its limited free version)
- Encryption is on the fly
- Work with the mounted container is carried out as with a regular folder. Everything is pretty simple.
But the program has many shortcomings:
- In addition to the program, you need to install additional SuperSU and BusyBox applications (which, incidentally, is not free, although LUKS Manager itself is free).
- Limited functionality of the program: there is no possibility of mounting remote containers, there is no possibility of cloud encryption, there is no support for mounting network folders.
- An inconvenient built-in file manager that allows you to only view files and folders.
- There is no way to select an external file manager.
- Folders to which the container is mounted are not automatically deleted after unmounting the container.
- There is no support for the Russian language.
Cryptonite
The Cryptonite program is quite young and is at the testing stage, so it can hardly be used to encrypt some very important data. In fairness, it should be noted that developers honestly warn about this when they first launch the program (Fig. 17).
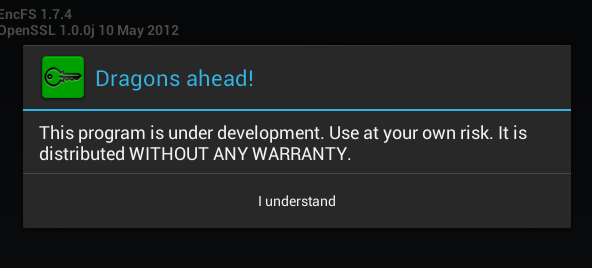
Fig. 17. The first launch of Cryptonite
With regard to system requirements, the program needs root access and a kernel with FUSE support (Filesystem in Userspace, File system in user space). The requirement of FUSE support can be safely attributed to the shortcomings of the program, since not all devices support FUSE. You do not need to reinstall any additional programs (except for the file manager).
The functionality of the program is already slightly better than that of LUKS Manager. She is able to create not only local containers, but also encrypt your files on DropBox. Support for DropBox automatically means support for cloud encryption, so this program already stands head and shoulders higher than LUKS Manager.
In fig. Figure 18 shows the Cryptonite program after closing an annoying message that you are using an experimental version of the program. The Dropbox tab allows you to encrypt files on your Dropbox, the Local tab is used to create a local container, and on the Expert tab, an ordinary user has nothing to do.
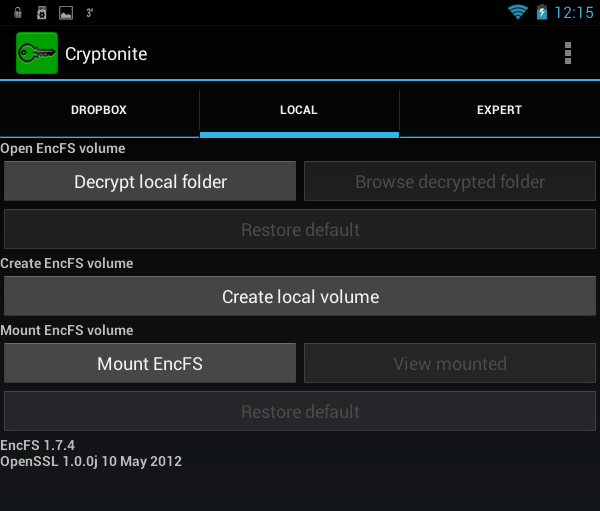
Fig. 18. Cryptonite program
To create a local container, click the buttonCreate local volume , after which you will again see a warning that this function is experimental (Fig. 19). Next, as usual, you need to select the encryption method (Fig. 20), the location of the container, enter the password and confirm it (Fig. 21). I liked that the program offers to enter a password confirmation, which eliminates its incorrect entry when creating the container.
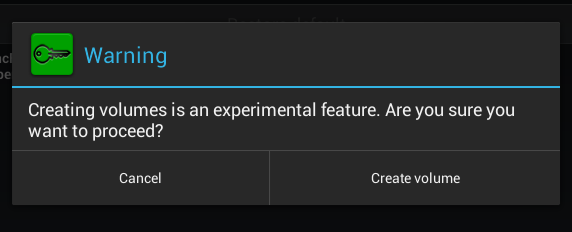
Fig. 19. Again annoying warning
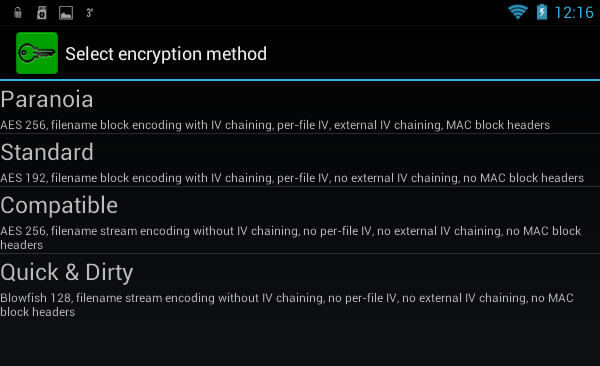
Fig. 20. The choice of encryption method
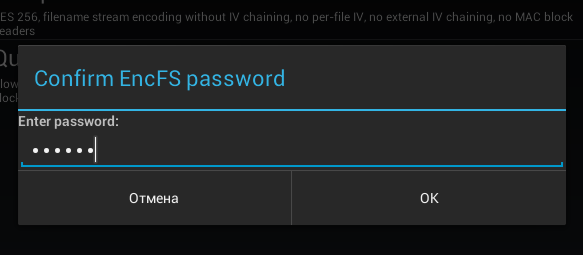
Fig. 21. Entering password confirmation You
can mount the created container with the Mount EncFS command on the Local tab. The program will prompt you to select a container. After entering the password to it, the container will be mounted to the /mnt/sdcard/csh.cryptonite/mnt directory (Fig. 22). The mounting directory is set in the program settings (Fig. 23).
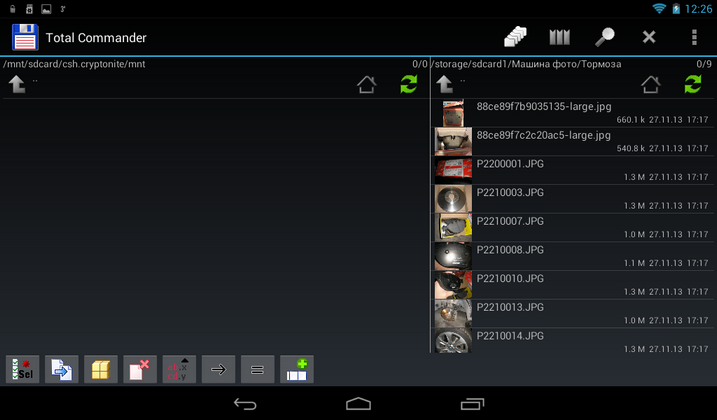
Fig. 22. The container is mounted

Fig. 23. Program
settings There is nothing particularly interesting in the settings, except for the Mount point folder , as well as the Chuck Norris mode, which allows you to disable annoying and meaningless warnings. You can also enable the use of built-in file manager when mounting the container ( Use built-in file browser), but given the traditionally meager functionality of this part of the program (Fig. 24), I do not recommend including this parameter. This “file manager” cannot even open a file. It allows you to only view the contents of the container and nothing more.

Fig. 24. Built-in container viewer.
Advantages of the program:
- Cloud Encryption Support (Dropbox).
- Encryption on the fly.
- Support for TrueCrypt containers, which is useful if you need to work with the container on a desktop PC.
Disadvantages:
- Requires FUSE support, which not every device has.
- Very meager file manager, allowing you to only view the contents of the container and nothing more
- No support for network folders (although this drawback is slightly brightened up with Dropbox support)
- The program is still experimental (although it appeared a long time ago, and since then it has been downloaded by more than 50,000 people). Whether or not to use it is up to you, but I would not use it to protect important data. Better to look for another program.
- There is no support for the Russian language.
CyberSafe Mobile
We have already reviewed the CyberSafe Mobile program on our blog, so there will be no detailed description of it. I strongly recommend reading the article “Sharing cryptodisks on PC and Android” , which describes one of the cases of using the program.
Therefore, instead of reviewing the program, so as not to be repeated, it will be compared with the programs previously described in this article.
The first thing to note is that you do not need root privileges to work with the program. Yes, in this case the program’s functionality will be limited, and you won’t be able to mount the created safe (this is the name of the encrypted container in CyberSafe Mobile), but your smartphone will not “fly off” the guarantee if you get root access. However, given that the program has a full-fledged file manager, this is not a problem. You can work with files in a safe without mounting it and installing a third-party file manager. For security reasons, the program does not allow you to take some screenshots, so the window of the built-in file manager, which displays the contents of the safe, could only be photographed with an ordinary camera (Fig. 25). As you can see, the program has a full-fledged file manager. It’s not ES Explorer, but unlike the previously described programs, the built-in file manager of Cybersafe Mobile can manage files - copy, move, delete, create new files and folders. I apologize for the quality of the picture, but in order to avoid glare, the tablet was photographed without a flash, so the photo is a bit dark.
Fig. 25. Built-in file manager of CyberSafe
In the settings for mounting the program, you can choose (Fig. 26):
- Mounting method - as already noted, if your device does not have root access or does not support FUSE, then you can not mount the safe, but work with it through the built-in file manager.
- The base mount path is the directory to which safes will be mounted.
- Third-party file manager - the program allows you to use both the built-in and the external file manager, and it detects the managers already installed on your device and allows you to select one of them.
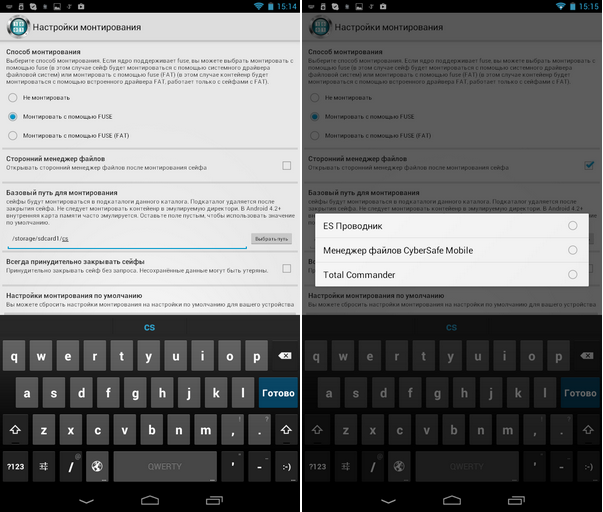
Fig. 26. Mounting options
It is also worth noting the Russian-language interface of the CyberSafe Mobile program, which makes it easier for users who do not speak English to work with the program (Fig. 27).
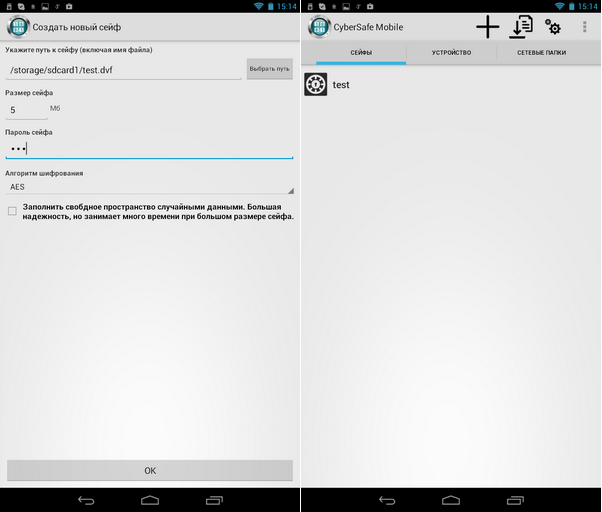
Fig. 27. The program interface. Creating a safe
Only thanks to all this (the ability to work without root and FUSE, a full-fledged file manager and a Russian-language interface) the program is a cut above LUKS Manager and Cryptonite. But that is not all. The program has a number of functions that lead to knockout of competitors.
Firstly, it supports the GOST algorithm - unlike other programs that use only AES or Blowfish (Fig. 28).
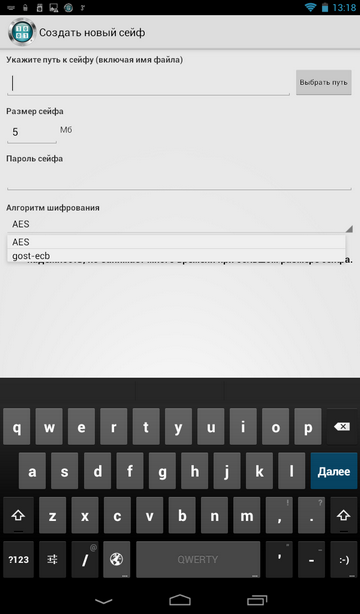
Fig. 28. The choice of encryption algorithm when creating a safe
Secondly, the program supports mounting network folders, which allows the use of a remote safe located on a remote PC (Fig. 29). The principle is simple: the container itself is stored on a PC, it is shared over the network. It turns out that the container opens on the smartphone, on the PC it is always stored in encrypted form, data over the network is also transmitted encrypted, which eliminates their interception. All data encryption and decryption operations are carried out on a mobile device. Even if you lose your device, no one will even gain access to encrypted data, since it is stored on a remote computer.
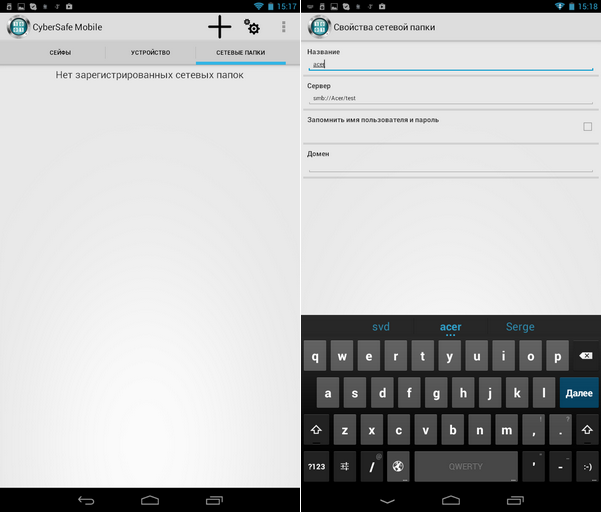
Fig. 29. Working with network folders
You can create a safe both using the CyberSafe Mobile program and using the desktop version of the program - CyberSafe Top Secret. It should be noted that to fully work with the safe, the CyberSafe Top Secret program is not needed - you can create a safe on your mobile device and copy it to your PC. In other words, you do not need to buy the CyberSafe Top Secret program for remote use of the safe on your smartphone. But if you need to organize the sharing of the safe on your PC and Android , then, of course, you will need the CyberSafe Top Secret program.
When installing the free URSafe Media Redirector program, it is possible to automatically redirect the photos you create (and other files, such as documents) to a safe that is physically located on the remote computer. More about this you can read in the article "Protection of personal photos on Android phones" . And in the article“Storing data in a cryptocontainer on a remote server and working with them from Android devices” shows how to store containers on a remote server, and not on a PC connected to your local wireless network.
Everything has flaws. However, CyberSafe Mobile has almost none. The disadvantages include the need to support FUSE, but this disadvantage is offset by the fact that the created safes can be opened without mounting, but only in the built-in file manager. It should also be noted that the program is paid, but its price is not high for a program of this class (do not forget what functionality the program has and do not forget that it supports GOST in addition to the AES algorithm). Well, I don’t really like the impossibility of creating some screenshots of the program, but it’s better from a security point of view :)
Now to summarize. Advantages of the CyberSafe Mobile program:
- Ability to work without root access and FUSE support (just safes will not be mounted).
- Transparent encryption on the fly
- Own full-fledged file manager
- Russian language interface
- GOST encryption algorithm support
- Ability to select a third-party file manager in which the contents of the safe will be opened
- Support for mounting network folders
- Ability to work with remote containers (VPN-safe)
- The ability to share the same container on a smartphone and on a PC (using the CyberSafe Top Secret program).
- No need to install (buy) third-party applications (as is the case with LUKS Manager)
Disadvantages:
- Программа не бесплатная, но есть ее Lite-версия, не поддерживающая монтирование и сетевые папки. Если вы не планируете использовать удаленные сейфы, и ваше устройство не поддерживает FUSE или же вы не хотите получать root-доступ, чтобы не «слететь» с гарантии, тогда Lite-версия — как раз то, что вам нужно. Для вас CyberSafe Mobile будет бесплатной, а функционал Lite-версии будет даже лучше, чем у бесплатной LUKS Manager, учитывая полноценный файловый менеджер.
- Для полноценной работы программы нужна поддержка FUSE (однако, на современных устройствах — это уже не проблема).
As you can see, there are no such shortcomings in the program and their selection is more my nit-picking for the program, so that no one will accuse me of bias. I think no one doubts that the winner of our comparison today is the CyberSafe Mobile program. If you have any questions, we will be happy to answer them in the comments to this article.
