Search hack, carelessness and my accomplice GitHub

Introduction
One fine, bright morning, shocked by the fact that the temperature outside the window seemed to be 5 degrees higher than usual, I felt an influx of unprecedented illumination and an idea crept into my brain - “but those offers and accounts that are sold on the “black market” - they are also stolen by all kinds of phishing sites and stylers, and as far as I know the stylers - all logs should be stored on some host on the Internet. ”
From this moment there was no time to hesitate - it was necessary to test. I ran headlong into the computer, frantically driving “google.com” into the address bar and was the first to enter the search query “stealer filetype: txt”. What I saw did not surprise me at all - among the search queries I saw the expected logs of one of the popular stylers.
View screenshot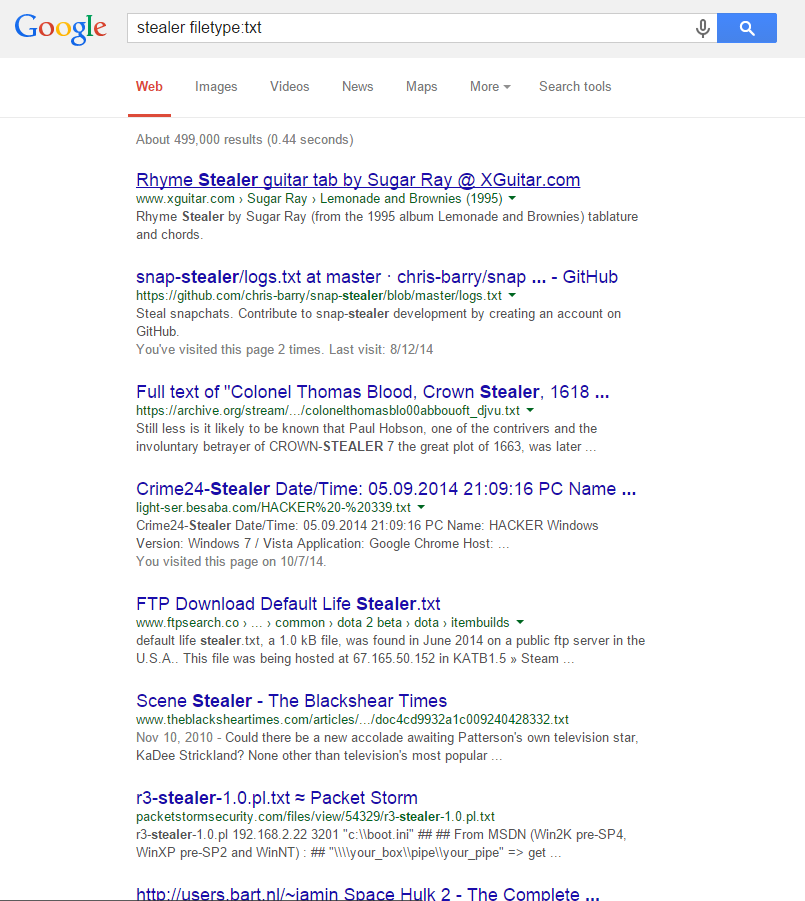
Chapter 1. Why use robots.txt, nofollow tags, and stubs
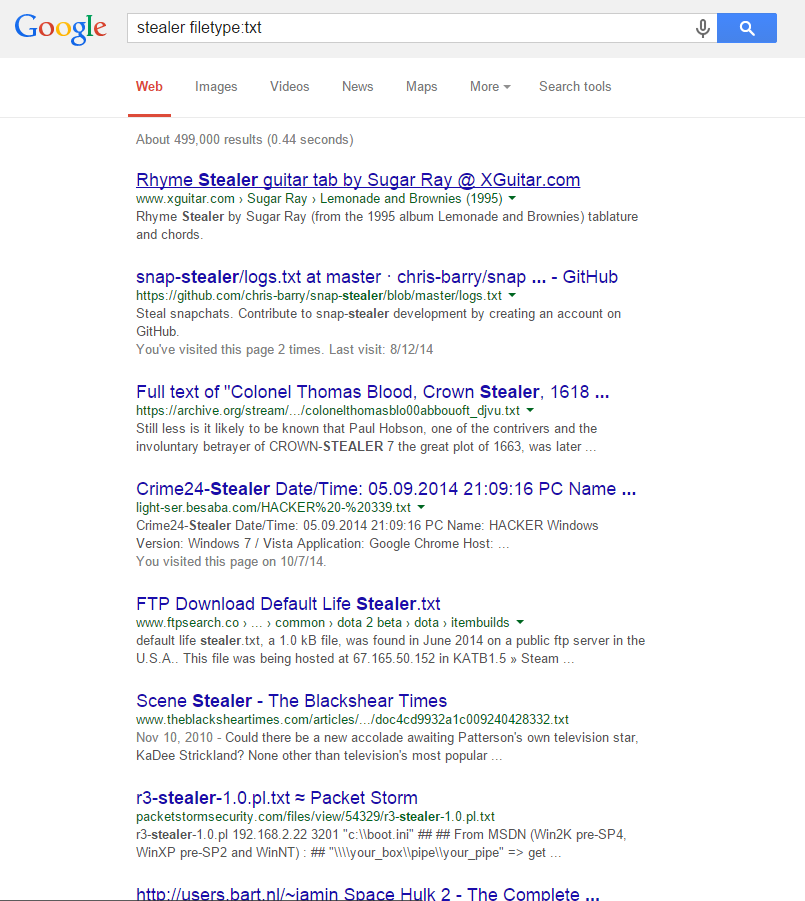
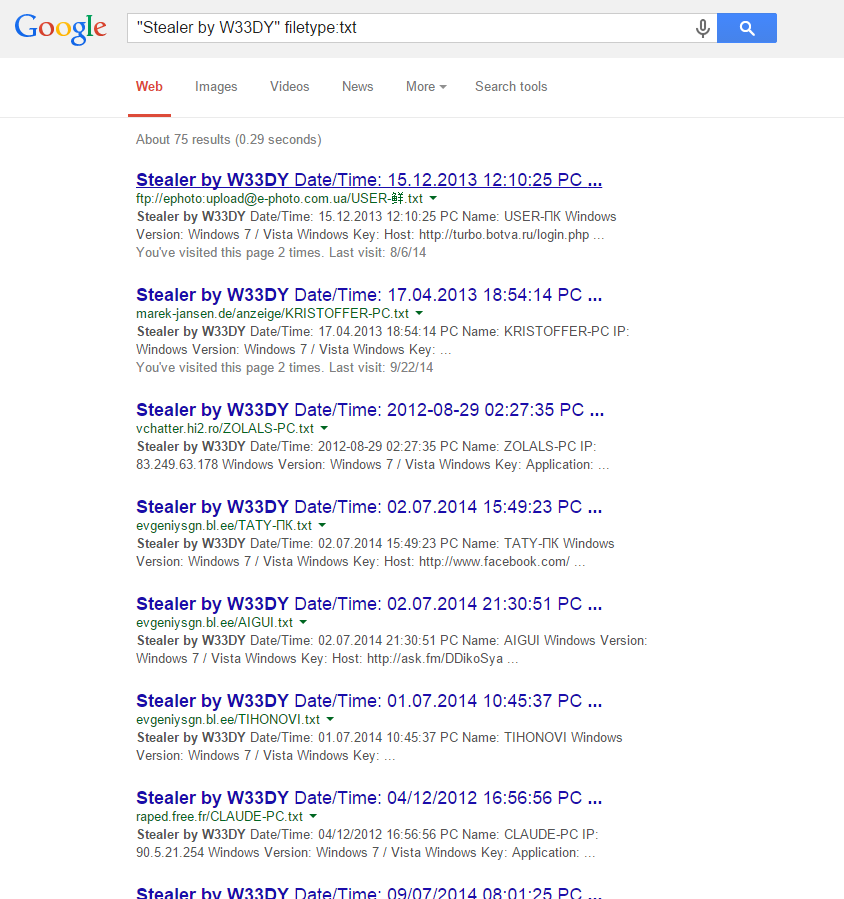
After that, I could not be stopped. I, like a wolf who sensed the blood of his victim, continued to search, but with requests that are more oriented to the specific names of the stylers:
View screenshot # 1

View screenshot # 2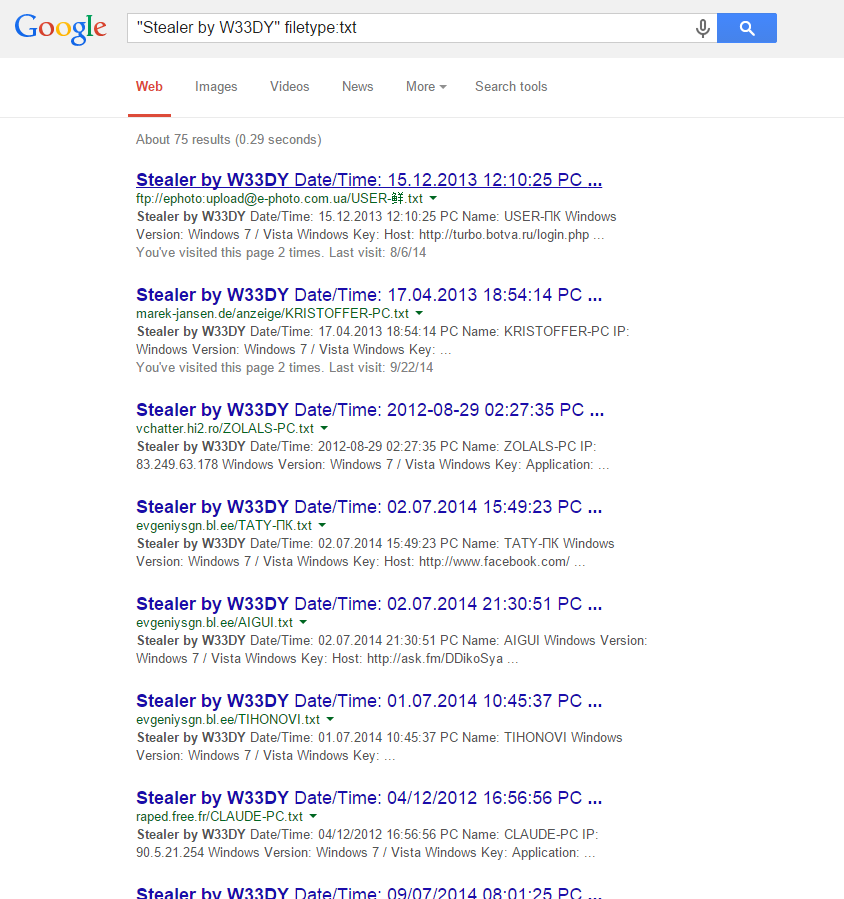
And then it dawned on me again - “but in addition to logs with accounts, unsuccessful users who got to the“ thief program “, you can also find something more serious, for example configs” and I went to GitHub.
Chapter 2. Why do I need to block files with configs via .gitignore
Speaking openly, the opportunity to do what I did and see what I saw was due to the carelessness or laziness of some users who prefer to use GitHub instead of alternative services that allow you to create private repositories ( gitlab , bitbucket ).
Take, for example, the mask of the automatically generated MYSQL host of one popular hosting and get, again, the expected result:
View screenshot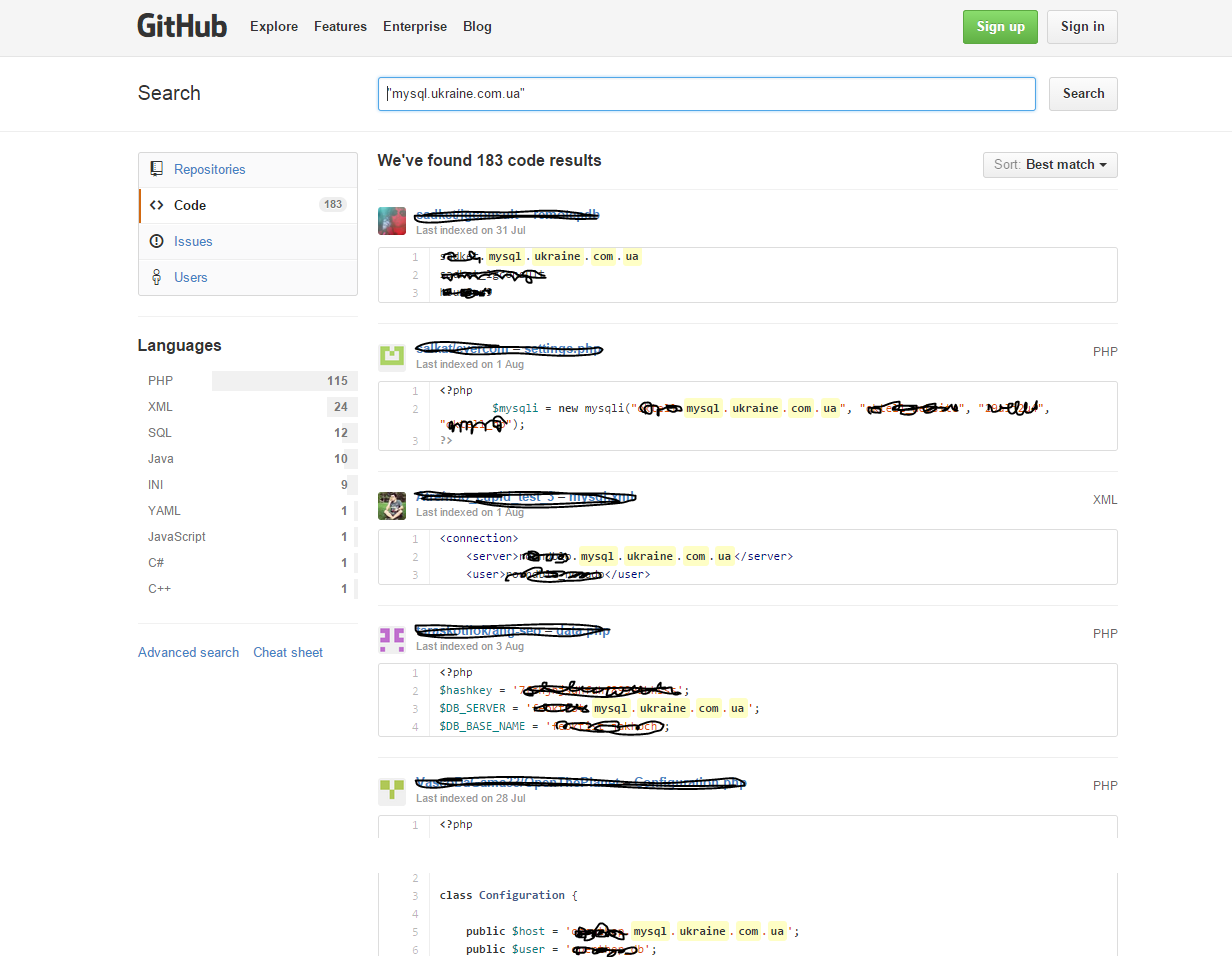
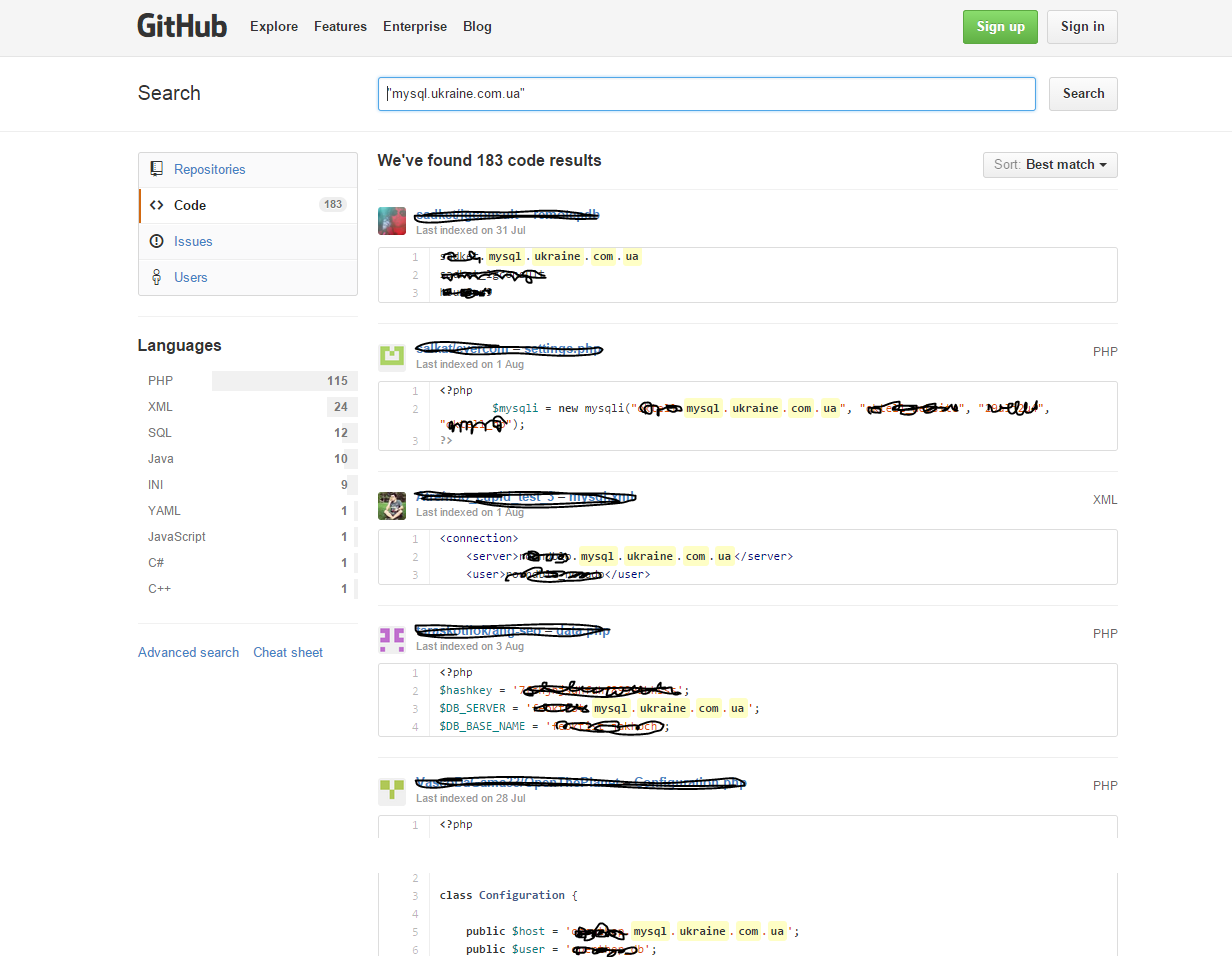
Then you don’t need to have a lot of imagination to understand what you need to do with all this.
Conclusion
Please use the .gitignore file and do not deploy your configs.
Only registered users can participate in the survey. Please come in.
