How to protect 5G in a smart city: apply a new security architecture
- Tutorial

In our last post, we were talking about a study by the international team of scientists
A Security Architecture for 5G Networks, who were looking for a way to protect fifth-generation networks. Researchers are proposing a new security architecture for this. To better understand the terms and concepts that relate to the study, you should familiarize yourself with the first post or with the full text of the work . Here we will focus on the practical application of security architecture, and immediately on the example of such a huge object as a "smart" city.
5G in smart cities
One of the important features of the ecosystem of the “smart” city is a large number of Internet of things devices included in it. These IoT devices collect data, which are then analyzed and used to increase the management efficiency (including automated) of various elements of the smart city. Moreover, 5G technology for smart cities is a cost-effective and easily scalable solution that will allow you to create dedicated logical networks (slices) with the ability to fully configure security rules and tools and does not depend on physical networks (Wi-Fi).
Thanks to the data transfer speed in 5G networks, information received from various sensors and devices is transmitted almost instantly between parts of the ecosystem and allows you to optimize, for example, the production and consumption of electricity in the city and quickly respond to accidents or malfunctions in the network. But for a smart city to function safely, 5G networks must be protected from extraneous influences and failures. The basic security requirements of such networks relate to communication methods, confidentiality and integrity, as well as the ability to access them. The 5G network security architecture is described in more detail in the diagram below, using the example of smart electric meters.
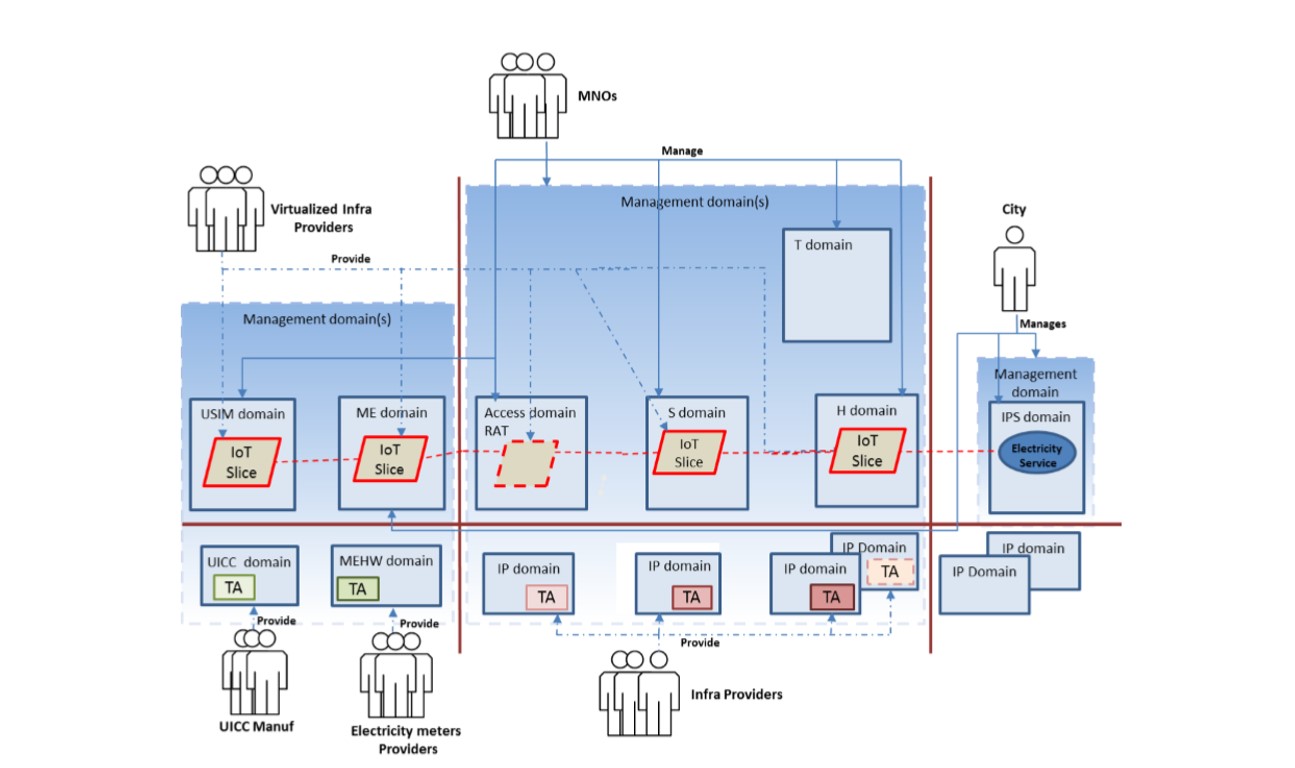 Figure 1. Smart city security architecture
Figure 1. Smart city security architectureFigure 1 shows the relationships and relationships between participants, processes, and resources that are included in the domains of the security architecture of the smart city. In this case, these are:
· manufacturers of UICC modules
· suppliers of electric meters
· suppliers of 5G infrastructure and virtualized infrastructure
· MNO (mobile operators)
· the city itself, which is responsible for power supply.
The dedicated slice, which covers all the data transfer processes between IoT gadgets (the dashed red line in Figure 1), is completely controlled by mobile operators.
The electric meters in the diagram belong to the common domain of the UE (user equipment), which consists of the domains of UICC modules, USIM modules, MEHW (hardware for mobile communications) and ME (mobile devices). Operator network hardware is a host of infrastructure provider (IP) domains. The city’s power supply is part of a common external network domain, which includes infrastructure provider domains and Internet connection protocols (IPS). IoT slices are created using virtualized network functions (VNFs). Participants in the architecture either manage the domains (blue lines) or are their suppliers (dashed blue lines).
Moreover, in general, the relationship between participants in the architecture can be described as follows:
1. The city “trusts” mobile operators to restrict access to a specific network slice and provide it only to authorized meters.
2. Also, the city “trusts” mobile operators to protect data received from these meters in the process of their transfer to the power supply service.
3. Users “trust” the city and mobile operators with the task of safely collecting and transmitting information.
4. Mobile operators "trust" the manufacturers of UUIC modules to safely store network keys in these modules.
Areas and classes of security management in the architecture of smart city networks
In the table below, the authors of the study collected safety management classes and safety areas related to the normal operation of electric meters and the power supply system of a smart city. For each area, they selected the appropriate classes, and for classes, potential problems and solutions. For the chosen scenario of using the architecture, the main problems arise due to the limitations of the devices themselves and unique patterns of data transfer between these devices.
To overcome these limitations, it is necessary to implement effective protocols and solutions related to application domains, networks and access networks. Outdated software and data transfer patterns of IoT devices can create access problems in some and security issues in other network domains. To deal with these problems, the authors, for example, propose using the technology of "slicing" the network into slices, which will isolate individual applications, as well as the use of hardware to monitor the status of the network.


An example of a network attack and its consequences
The two most important technologies for the work of the smart power supply system described above are NFV (virtualization of network functions) and SDN (software-configured networks). These technologies allow operators to create cost-effective tools for “slicing” networks into separate slices for data transfer. The functions of the mobile network in this case are virtualized, and the data flows between them are controlled by SDN controllers. In addition, SDN technology allows you to separate the areas of control and data from each other thanks to the ability to program network settings and network policies.
One of the main threats to any mobile network is a loss of connection. Moreover, such a loss may result from a DoS attack (denial of service), when an attacker overloads the SDN controllers in the domains of “home”, “service” or “access”. This type of attack affects one of the functions in the transport layer (more precisely, the forwarding function) through the function in the control layer (for example, through the reconfiguration function of routing tables). In this case, hackers can measure the response time of the network and determine how to start changing the configuration of the routing tables. Thanks to such a fingerprinting attack (from “fingerprinting”) and the information obtained during it, subsequent DoS attacks by hackers, during which they will endlessly call this function to overload the SDN controller, will become much more effective.
The consequences of such attacks will be:
1. Loss of communication between “customers” (in this case, electric meters) with the network and the power supply service.
2. Deterioration of the general condition of the network and the negative impact on the implementation of virtualized network functions. The mobile operator can either independently assume responsibility for eliminating the threat, or transfer this task to infrastructure providers.
3. Loss of user confidence in mobile operators. In this case, the operator is responsible for the operation of the meters and for the elimination of such threats.
The security architecture in this example is used to identify all security areas and domains that are affected by a particular threat and to which, therefore, certain security management classes must be applied. Fingerprinting attacks are related to the accessibility management class in infrastructure and virtualization. One of the potential protection mechanisms against them may be the delay of the first packets of each data stream and, thus, the hiding of timing information that can be used by hackers.
conclusions
In two posts on 5G security architecture, we tried to present the main tools and ways that the authors of A Security Architecture for 5G Networks study offer to protect 5G networks from possible attacks, and at the same time consider the practical application of their ideas. It is possible that the approach described in this study will soon be applied around the world, as well as the concepts of domains, layers, spheres and security management classes or the logical idea that it is necessary to evaluate and ensure the network security at the deployment stage. And this is really important, because the deployment of fifth-generation networks in the world is happening now, before our eyes.
With the advent of 5G, new elements and tools will appear in the infrastructure, for example, “slicing” networks into slices, virtualization of network functions and software-configured networks, and the scale of systems (as well as their security requirements) will grow significantly. Security methods for previous generation networks are not able to cover all attack vectors for 5G infrastructure. At a minimum, they are not prepared for new use cases with a large number of participants with different rights who simultaneously have access to this infrastructure. This is especially noticeable on the example of large 5G ecosystems, such as smart cities. Therefore, the emergence of new concepts such as 5G network security architecture, which offer an alternative to established approaches and are ready to protect the fifth generation networks, may become vital for the normal implementation and development of 5G technologies in the future. Which has already arrived.
