How the "ethical hack" of the manufacturer of gambling software turned into a complete nightmare
- Transfer
"Ethical hackers" tried to open the eyes of a company that makes programs for gambling, to errors in its products - but in the end everything went to hell

People who find a security problem in a company often have difficulty trying to let it know. However, much less often, such situations acquire the character of fair confrontations and mutual accusations of attacks and blackmail.
And yet, that’s exactly what happened when Atrient’s casino technology top management, headquartered in West Bloomfield, Michigan, stopped responding to two cybersecurity researchers from Britain reporting about alleged deficiencies in the protection of the company. Researchers thought they had agreed to pay for their work, but received nothing. On February 5, 2019, one of them, Dylan Wheeler, a 23-year-old Australian living in Britain, came to the Atrient booth at a London exhibition to personally deal with the company's chief operating officer.
What happened next is not entirely clear. Wheeler says that Jesse Gill, Atrient's COO, argued with him and eventually tore off his badge; Gill insists he did nothing of the kind, and accuses Wheeler of trying to extort.
These troubles resulted in legal threats and mutual mudsliding, with commenting on Twitter. Tod Beardsley, research director at Rapid7, was one of the spectators of this performance. “My first reaction,” Beardsley jokes, “was“ eh, I would like the supplier to hit me for exposing the vulnerability. ” This is better than any reward for errors found "".

Bingo for revealing vulnerabilities:
- we still have not had any hacks;
- we cannot accept your report without a technical support contract;
- our ordinary users will not do this, this is not a problem;
- this product will close soon;
- an order to ban unlawful acts;
- complete silence;
- we called the police;
- we use military-grade encryption;
- so it was conceived;
- we know about it, we are working on a new version;
- we do not consider this a vulnerability;
- we left all the default settings;
- who do you work for?
- this restriction is reflected in the documentation and everyone knows about it, there is no reason to fix it;
- This product is intended for internal use and should not have Internet access.
This story is just a textbook example of the problems that can arise when researching and discovering vulnerabilities.
Many large companies and technology suppliers support rewards for mistakes, redirecting the efforts of third-party hackers and security researchers to solve problems in software and infrastructure - however, the vast majority of companies do not have a clear mechanism for third parties to share information about holes in them. security.
Uncovering vulnerabilities for such companies, Beardsley says, “In response, I received everything from silence to active ignoring -“ I do not want to hear this! ”- and letters demanding the cessation of illegal actions. There was all that, but I received many positive reviews. "I worked with people who did not have enough experience in disclosing vulnerabilities, and I helped them figure it out."
In this case, two relatively inexperienced "ethical hackers" tried to sort out a security problem that seemed relatively serious to them, and Atrient directors thought that a couple of unprincipled hackers were trying to make money from them. Thanks to months-long recording of calls and email correspondence between Wheeler, Atrient and other shareholders - including a major casino operator in the USA and the FBI cyber division - we have a good idea of how things have developed.
Company

Atrient Las Vegas office, close at hand to McCarran International Airport

Atrient's headquarters in West Bloomfield is located in this
Atrient building , a small company with a very narrow casino and gaming industry niche.
Atrient, founded in April 2002 by Sam Attisha and Dashinder Gill, was first named Vistron, Inc., and a year later renamed, according to the state register, initially engaged in technical consultations. She offered “custom solutions” for recruiting IT staff, software development, creative services, and project management. For a short time, the company went into the wireless business by opening Vistron Wireless Inc. To "provide marketing and technological services for the wireless industry," as stated in the company’s registration documents.
Over the several years of its existence, the integration of online casino software has also entered the company's field of activity. By 2015, Atrient focused mainly on the PowerKiosk casino user loyalty system, combining individual slot machines, electronic devices and mobile applications to track gambling players and give them rewards, special games and marketing offers. The system can track users through loyalty cards or via Bluetooth beacons and geolocation using mobile applications, as well as store the cost of bonuses received by the player.
Atrient has an office in Las Vegas for sales and customer support, but its headquarters are located in a small business center in West Bloomfield (Michigan). It is located on the second floor with the dentist’s office and the H&R Block Advisors office, and underneath are a donut cafe and a mattress shop. Atrient’s office is another outsourced IT company, Azilen , which has two more offices in India and one in Belgium. The relationship between Atrient and Azilen is not fully understood; at least one developer from Azilen now works at the Atrient in Hyderabad, India, registered in May 2018.
Atrient, apparently, feels rather well in its niche, and has partners among the largest companies in the field of casinos and gambling. Konami in 2014 made a deal with her for exclusive rights to distribute the Atrient software product to existing Konami customers. Atrient also integrated its software into the Scientific Games Bally Technology and International Game Technology gaming systems.
Over the past year, Atrient has been in talks with Everi Holdings, a game and financial software company, culminating in March 12, 2019, when it was announced that Everi would “acquire certain assets and intellectual property” from Atrient. The deal was spent on $ 40 million through $ 20 million in live money and additional payments in the next two years based on certain conditions specified in the contract. Security researchers sought to be heard during these negotiations.
Researchers
Our researchers have some experience in information security, but you can’t name them industry veterans. Wheeler is 23 years old, and his Atrient partner was a 17-year-old Briton who was called Ben by email and phone. Ben studies information technology, and on Twitter and other networks writes under the nickname @ Me9187, or simply “Me.”
Wheeler in the past had quite serious problems with the law - Gill immediately noted this in the editorial response, commenting on the events of February 5 at the London exhibition. Once in Australia, Wheeler was accused of hacking when he was a minor, and then at the age of 20 he escaped from bail to the Czech Republic in order to avoid criminal prosecution. Wheeler himself claims that his case was closed in Australia and decided not to pursue him further. He is now legally present in Britain, and authorities are aware of his “criminal past,” he said.
“He was turned on when I was 14,” Wheeler told the editorial office, and stated that under Australian law his case could not be published in print (although many Australian newspapers described the case in detail). “But anyway, the past is over.” I try to be as transparent as possible, and I don’t like the fact that my past agitates Atrient. This is an information security industry, and many people have a dark past. ”
Hunt through Shodan

From the Internet, you can access over 100,000 Jenkins servers; many of them have vulnerabilities that can be found through Shodan.io and Censys.io.
On October 29, 2018, Wheeler and Me were searching for vulnerable systems on the Internet. They sent requests to two vulnerability search engines - Censys and Shodan - through a combination of web requests and direct commands through the command line that these tools support. During the search, they stumbled upon an “open door” - the Jenkins server , which, they say, did not have access control turned on.
The Jenkins project, originally owned by Sun Microsystems, needs to be used in the software development process. It allows you to continuously integrate, compile and deploy assemblies. He has quite serious security problems, including past shortcomings that allowed him to remotely execute code, which enabled the attacker to organize a bridgehead in the company's software development chain. Wheeler and Me claim that Atrient's Jenkins server, which was running on a Windows virtual machine in the cloud, did not have user authorization set up, and simply accessing the server’s web console gave the user administrator privileges. In this statement, Atrient claims that this couple used brute force password guessing to gain access to the server.
Wheeler and Me decided to rummage there and see if they could determine the owner of the server. Using server access to execute a two-line Groovy script, they created a remote command line that allowed them, according to them, to examine the entire server. Based on the documents and data they found, they decided that the server was used by Atrient and Azilen employees to develop and send error messages about the PowerKiosk platform, as well as code repositories for mobile applications and kiosk options for various casinos. They also found that the server has the FileZilla File Transfer Protocol, as well as communication with several databases, a source code repository, and working code that supports the PowerKiosk API.
Gill claims that the couple just found a demo platform where there was no working code. At least one of the casinos listed on the server was a demo environment. Casino Monaco was a fake casino used to showcase products at fairs and marketing materials from Atrient.
On November 4, 2018, Me and Wheeler sent emails to a whole set of addresses in Atrient and Azilen - including the director Sam Attish - with a warning about a security problem on the server. “Please pass these details on to the relevant security teams and advise them to contact me,” the emails said. It also listed the databases and APIs associated with PowerKiosk, its web interface and mobile applications tailored for specific Atrient clients.
Often these emails go unanswered. They were full of grammatical errors and typos, and they did not look like typical professional correspondence. Wheeler says Attisha informed him that these letters were in the Spam folder.
But Beardsley said that in his experience even professionally formatted messages can be ignored. “We wrote a message about Guardzilla, a WiFi home surveillance camera sold in large supermarkets. And we have not achieved anything, ”he said. “We made a support request, tracked people working for the company through LinkedIn, and one journalist even found company representatives and talked to one of them.”
And after all this, the company did not respond. “The camera is still dangerous to use,” Beardsley said. “Her storage on AWS S3, where all your home videos are, is not protected.”
Wheeler didn't go that far. She and Me began to tweet, trying to get public attention to this occasion. At this point, Guise Bule was involved in the situation.
Attention attracted

Guise Bühl, a former government security contractor and co-founder of WebGap, a secure web-based company, also founded SecJuice, an “information security-related authors club”. Trying to enlist help in promoting the situation, Wheeler and Me turned to Bule, who reposted the records concerning Atrient. Now these tweets are already deleted.
Beul's help attracted the attention of two interested organizations - a large casino operator using Atrient software, and the FBI.
On November 9, casino security guards contacted Me. On November 10, Wheeler intervened in the case and sent them a brief description of what they found a couple:
I’m Me’s colleague with whom you chatted on Twitter, and then sent a letter. The vulnerability is related to one of your suppliers, Atrient, and their terrible approach to security, due to which kiosks process and transmit unprotected data via HTTP.
These shortcomings, which we are trying to make them correct, forced us to publicly announce their existence. Among them there are small problems (I will not disclose all the details, but one of the good examples is that your data stored by the provider is on FTP, the login and password for which are simply the names of companies in lowercase letters), and large holes associated with their products (PowerKiosk).
On the same day, Bule was contacted by the FBI about his retweets. Beul arranged a general telephone conversation with Wheeler, Me, and FBI agents from the Cybercrime Division and the Las Vegas Branch. Wheeler recorded their conversation.
Wheeler told the FBI that he and Me had no intention of publishing the information they found, because they were worried about the severity of the problems. It, in fact, could be used to “print money,” Wheeler told agents. He also said that he and Me had a conversation with the casino operator, but were unable to reach Atrient.
“Perhaps we can help you with this,” said one FBI agent.
Wheeler’s interaction with the casino on November 11 was praised by the company's security director in a letter. He wrote to Wheeler, "I wanted to personally thank you for the professional approach to information disclosure, and that although you did not receive an immediate response from the supplier, you gave him a second chance to fix it." He suggested “send any merchants to Wheeler,” and asked about the size of his T-shirt and headgear.
On the same day, the FBI organized another joint call - this time involving Atrient's Gill. In a conversation also recorded by Wheeler, Gill said: “The information you gave us is amazing. We would like to own it. How can this be organized? ”
Up to this point, money was not mentioned in the conversations. Researchers were planning to someday present their findings at a computer security conference, so Wheeler and Me only asked the “merchants” of the casino operator to be “shining” during the performance.
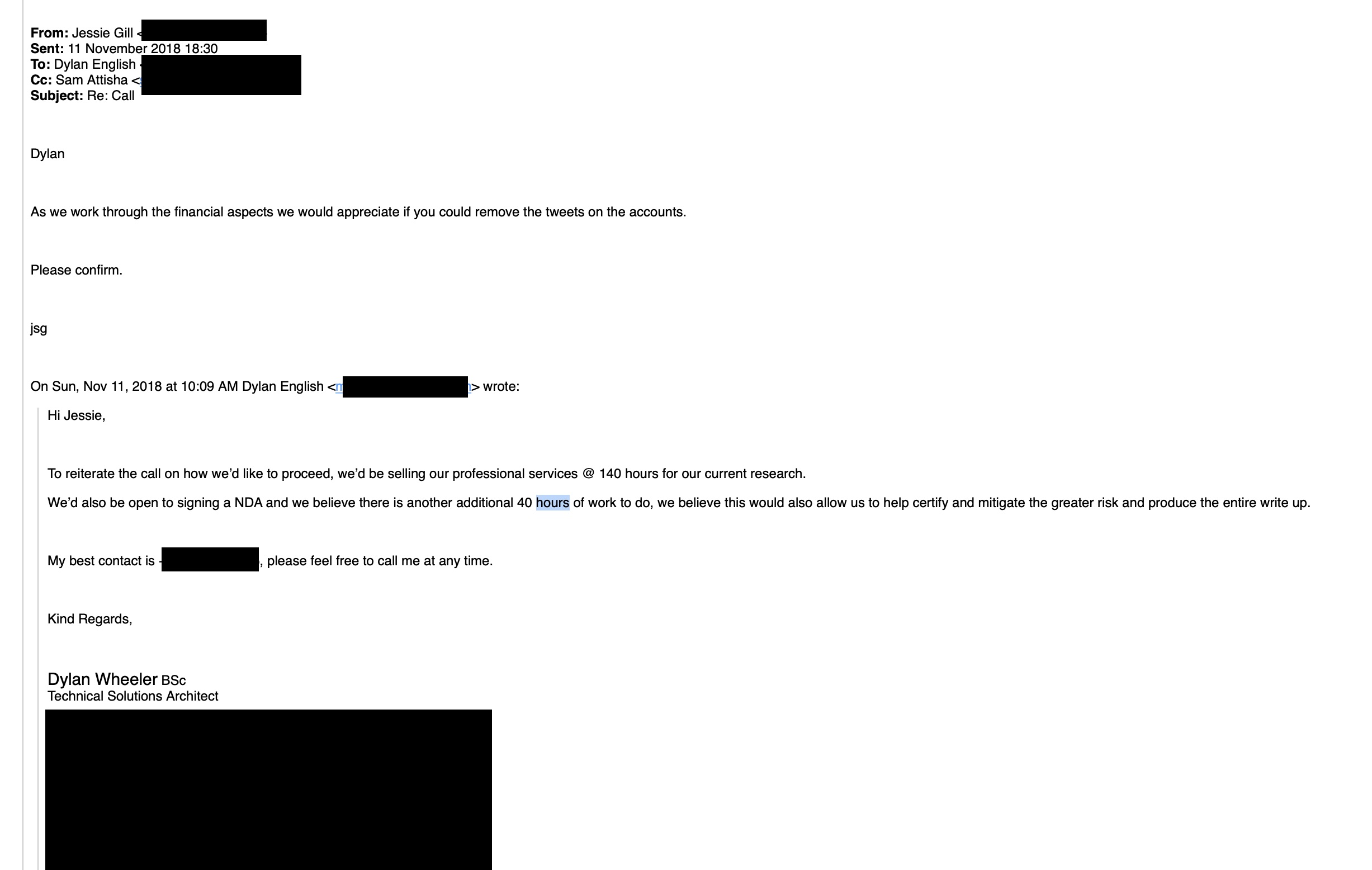
However, after the idea of a non-disclosure agreement appeared in the negotiations, Wheeler mentioned the reward for detecting a bug. He suggested that Atrient pay his company the equivalent of 140 hours of consultations, which is about $ 60,000. Apparently, at that moment everything went on.
The check, please
“When I make a consistent disclosure of vulnerability information - I call the software vendor for the first time - it’s very important for me to emphasize that“ I’m not trying to sell anything, I’m not blackmailing you, I’m not trying to make this call a presentation for selling my future products “, Says Beardsley. “I always stress this for a couple of reasons. Firstly, I do not want to go to jail. Secondly, for most people this is a very emotional event, especially for those who have not previously dealt with vulnerability disclosure. "
Beardsley said that often when he reveals vulnerabilities, “I turn out to be the first third-party security specialist that people talk to.” Therefore, “I am trying to mitigate the situation to the maximum, and it seems to me that such a skill in the field of IT security is just not enough.”
However, now the idea of payments appeared in the conversation, and the researchers decided that they would be paid. That call ended, but negotiations continued. After requests to remove “negative Atrient tweets” from Me’s account and after requests for the location of the data that the couple downloaded from Atrient’s server, Gill, Attisha and Atrient’s lawyer talked to Wheeler during 2018. They said they would send him a draft non-disclosure agreement so that he could discuss it with his lawyer.
On December 7, 2018, Atrient lawyer wrote to Wheeler an email saying: “We have a draft ready. Would you like us to forward it to your lawyer. " Wheeler asked me to send him a draft. But he was never expelled.
A week later, Gill informed Wheeler in a letter that a draft “arrived at us this week. Sam and I study it. We can send it to you by Monday [December 17]. ” But all the holidays there was no news from them. On January 4, 2019, Attisha explained in an email that he and Gill went on business trips.
A few weeks passed in silence. Then, on January 21, 2019, Attisha wrote:
I am sending the agreement soon. In late January - early February we will be in London. We can meet there and sign an agreement, if that suits you.
Wheeler agreed, and said that he could come to the ICE conference in London, as he registered as a visitor. But as the conference date approached, letters from Atrient stopped arriving.
Atrient was negotiating a purchase with Everi at this time. At the ICE conference, Everi announced the start of a “partnership” with Atrient, and both companies shared one stand to demonstrate joint products. Wheeler began to suspect that he was simply thrown and would not be paid - and he wanted to personally speak with the Atrient directors.

Incendiary party
When a company encounters vulnerability disclosure, Katie Mussouri, founder and director of Luta Security, told us, “At the very least, it’s always best not to resort to unethical measures.” Companies can do this by creating or clarifying their attitude to disclosing vulnerabilities, and restricting their public statements to the statement that the company is aware of the problem and is engaged in its solution [holding statement].
“You cannot win in a court of public opinion,” Mussouri explained. “The larger the organization, the more ethical its actions must be, or it will get the image of a rude.” But researchers, she says, “the easier it is to defend themselves legally and before public opinion, the more professional they are.”
However, in this case, no one took this path .
Wheeler and his friend visited the joint Atrient and Everi booth at the February 5th ICE conference. There he saw Gill, which led to a skirmish. Wheeler states that Gill mentioned something about Wheeler's “friends”. Wheeler immediately posted a video of how he accuses Gill of assault - although there was no attack on the video itself. Gill denied everything.
In an email to Wheeler, and in a subsequent telephone interview with our editors, Gill accused Wheeler of participating in the blackmail of Atrient. Gill soon sent an e-mail to Wheeler, Me, and Beaule:
Regarding your letter from today, and the appearance of your accomplice at our company booth at the ICE fair, which made certain statements regarding the security of our systems.
You and your colleagues are responsible for the unauthorized hacking of our demo platform in November 2018, as a result of which confidential information belonging to us and our customers fell into your hands. You and your accomplices demanded money from us in exchange for this information. We are not ready to pay you compensation for your illegal actions and DO NOT RESPOND TO THREATS.
As you know, we contacted the Federal Bureau of Investigation about your illegal activities in November last year, and now we are working with the relevant authorities in Britain, Europe and Australia.
We demand that you immediately:
- Stopped threatening us, our employees, representatives, clients and advisers.
- Returned all copies of confidential information at your disposal.
- They informed where the confidential information is stored electronically, whether it is located on the device or storage system that you have, or on the server or in the cloud storage, took all the steps necessary to guarantee the complete and irreversible erasure of all confidential information, including all copies and backups, all temporary or other copies, so that no one has access to confidential information or any part of it.
You should not publish any part of confidential information or any information related to illegal hacking, or in any other way post confidential information in the public domain.
Please confirm by reply no later than 9am tomorrow UK time that you will satisfy these requests.
We consult with lawyers about actions that we can take against you and your associates in the civil and criminal codes. In the meantime, refrain from any action in this regard.
Your opinion regarding the consequences of this incident for Atrient or its customers is based on fiction.
Atrient quickly posted on Twitter a statement regarding the incident at the exhibition, and then deleted it. (Gill said this was due to "restitution"). Then another version of this statement was sent to our editorial staff and other editions of Britain. It says:
We became aware of false claims related to the vulnerability of one of our products and the alleged attack. In November 2018, one of our product selling sites was brutally attacked by a demo server that did not have personal data. The attack affected the demo sites of our sales team.
Then a group of individuals contacted us, among whom was a person who called himself Dylan English, which, as is now known, is the pseudonym of Giza Bule from secjuice.com, as well as a person who refused to give his name. Soon after
, it became clear that a financial motive was involved in the case. The FBI is aware of the existence of this group.
On February 6, 2019, one of the “security researchers” made an unplanned visit to the Atrient booth at ICE London. His name was written on his badge, Dylan Wheeler, and we believe that this is his real name. After he was informed that Atrient would not pay him money, he made another false accusation, this time about the attack on him, the groundlessness of which was revealed by the investigation conducted by the ExCel exhibition center.
Now this case is in the hands of legal consultants of the company and law enforcement agencies. Therefore, additional comments would be redundant.
The name Dylan English is really attached to Wheeler's email - he uses this nickname to work in his information security company. However, in the signature of all his letters to Atrient, to the casino operator and the FBI was his real full name, so all participants in the events should have known it.
By sending a response to Atrient, Wheeler sent letters to FBI agents and the casino operator, saying that he was attacked and that Atrient was not concerned about fixing the vulnerability. He then told everything to Beul, and also gave him links to recordings of conversations with the FBI and screenshots for publication on SecJuice. Now the details of the security issues that Wheeler and Me have reported to Atrient have been made public.
Know when to support, and when to pass
No episodes of the development of this situation surprise Beardsley. “People involved in disclosing vulnerabilities quickly learn about the current situation - usually people do this not too often, so we all do it badly. We don’t have instructions on how to preferably act. ”
Even when the agreed disclosure goes well — without any non-disclosure agreements, legal threats, and all that — it can take months. But the advantage of the right approach, according to Beardsley, is that “perhaps the company will better perceive the next guy who will come to them with disclosure, and perhaps not be as delicate as you. That’s all you can hope for. ”
The interaction between Wheeler and the casino operator is an example of how the disclosure can be done well - and it went well, because the operator had its own security service, which was ready and wanted to respond. The lack of discussion of rewards also helped.
But the animosity between Atrient and the researchers seems to have arisen not only because of money. The moment of this disclosure also played a role, when the $ 40 million deal was nearing completion. Given the business situation, the relatively short period of time (by disclosure standards), and the way the conversation went, it is not surprising that Atrient’s emotions were heating up. Fireworks were almost inevitable.
Beardsley, a veteran of disclosures, said: “Know that this is a normal situation, and that we can expect little, but if someone does not have experience, emotions can leap up and he can perceive everything that is too personal. It is our responsibility not only to train corporate America in dealing with disclosures, but also to train people who find these errors - especially today, in an era when public disclosure of bugs has become the norm, so you should not expect that when a bug is disclosed, a person must will be grateful to this. ”
