What is a Mirai botnet, and how can I protect my devices?
- Transfer

First discovered in 2016, the Mirai botnet captured an unprecedented number of devices and caused massive damage to the Internet. Now he is back and more dangerous than ever.
New and improved Mirai infects more devices
On March 18, 2019, security researchers at the Palo Alto Networks revealed that Mirai was redesigned and updated to achieve the same goal on a larger scale. The researchers found that Mirai uses 11 new types of exports, bringing the total to 27, and a new list of default administrator credentials for the sample. Some changes are focused on business equipment, including LG Supersign TVs and Wipg-1000 Wireless Presentation Systems.
Mirai can be even more powerful if it can take on business equipment and command business networks. According to Ruhna Nigam, a senior threat researcher on the Palo Alto networks:
These new features provide the botnet with a large attack surface. In particular, targeting industrial links also gives him access to more bandwidth, which ultimately leads to more botnet power for DDoS attacks.
This version of Mirai continues to attack client routers, cameras, and other devices connected to the network. For destructive purposes, the more devices are infected, the better. Ironically, the malicious virus was posted on a website promoting a business that dealt with “electronic security, implementation and monitoring of alarms.”
Mirai is a botnet that attacks IOT devices
If you do not remember, in 2016 the Mirai botnet seemed to be everywhere. He aimed at routers, DVR systems, IP cameras and more. These are often called Internet of Things (IoT) devices and include simple devices, such as thermostats, that connect to the Internet . Botnets work by infecting groups of computers and other devices connected to the Internet , and then force these infected machines to attack systems or work on other targets in a coordinated manner.
Mirai went for devices with default administrator credentials, either because no one changed them, or because the manufacturer hard-coded them. The botnet has captured a huge number of devices. Even if most systems were not very powerful, a large number of processors could work together to achieve more than a powerful zombie computer could do on its own.
Mirai has captured nearly 500,000 devices. Using this large-scale botnet of IoT devices, Mirai damaged services such as Xbox Live and Spotify and websites such as BBC and Github , targeting directly to DNS providers . With so many infected machines, Dyn (the DNS provider) was stopped by a DDOS attack from 1.1 terabytes of traffic. A DDOS attack works by flooding the target with a huge amount of Internet traffic, more than the target can handle. This causes the victim’s website or service to slow down or completely disconnect from the Internet.
The original creators of the Marai botnet software were arrested, pleaded guilty and received a suspended sentence . For a while, Mirai was turned off. But enough code survived for the other criminals who took over Mirai and changed it to suit their needs. Now there is another version of Mirai.
How to protect yourself from Mirai
Mirai, like other botnets, uses well-known exploits to attack devices and compromise them. He is also trying to use the known default credentials to work on the device and take it upon himself. Thus, your three best lines of defense are simple.
Always update the firmware and software of everything that you have in your home or workplace and that can connect to the Internet. Hacking is a cat and mouse game, and as soon as a researcher discovers a new exploit, patches will follow to fix the problem. Botnets like this thrive on unpatched devices and this version of Mirai is no different. Exploits aimed at business equipment were identified in September last year and in 2017.

Fig. 1. Updating the firmware of the router.
Change the administrator credentials of your devices, username and password as soon as possible. For routers, this can be done in the web interface of your router or mobile application (if any). For other devices that you log in with the default username or password, refer to the device manual.
If you can log in using admin , password or an empty field, you need to change this. Remember to change the default credentials when setting up a new device. If you have already set up your devices and forgot to change your password, do it now. This new Mirai Varsia targets new combinations of default usernames and passwords.
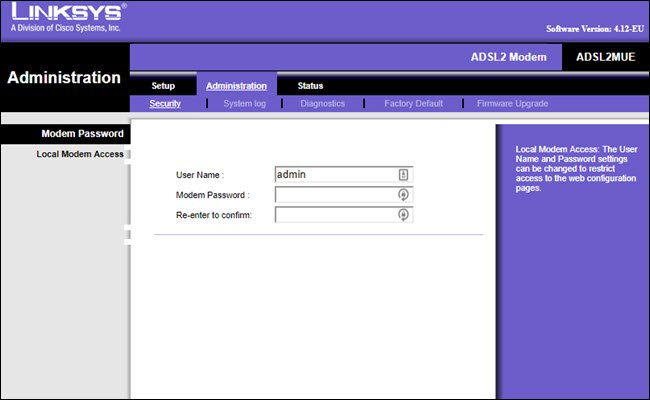
Fig. 2. Bad username example.
If the device manufacturer has stopped releasing new firmware updates or hard-coded administrator credentials and cannot be changed, consider replacing the device.
The best way to check is to start with your manufacturer’s website. Find the support page for your device and find any notifications of firmware updates. Check when the last one was released. If many years have passed since the firmware update, the manufacturer probably no longer supports the device.
Instructions for changing administration credentials can also be found on the device manufacturer’s support website. If you cannot find the latest firmware updates or a way to change the device password, it is probably time to replace the device itself. You should not leave something vulnerable and constantly connected to your network.
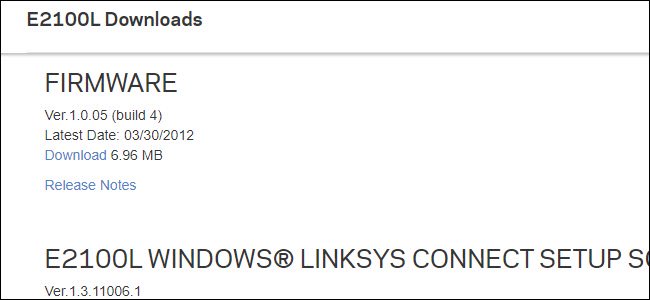
Fig. 3. If the latest firmware you can find is from 2012, you must replace your device.
Replacing devices may seem like a radical measure, but if it is vulnerable, then this is your best option. Botnets like Mirai won't go anywhere. You must protect your devices. And by protecting your own devices, you will protect the rest of the Internet.
