Metasploit Framework 5.0 has been released
Metasploit Framework is the most well-known tool for creating, testing and using exploits. Allows to operate and post-exploit vulnerabilities, deliver payloads to the attacked target.
Metasploit Framework 5.0 is the largest update of the framework since 2011.
The developer Metasploit company Rapid7 has pleased many experts on both sides of the information security barricades, releasing a new release of its product. Part of the features, for example, GoLang support (and this is very cool!) For writing your own modules, was announced just a month ago in the dev-branch of the product.
The update was especially welcome, given the new possibilities of integration and customization of this unique toolkit. Updates relate to optimizing the work of the framework, adding methods of obfuscation, external integration and empowering using new programming languages.
Major innovations
Metasploit Framework users can run the PostgreSQL database separately as a RESTful service that allows multiple Metasploit consoles and external tools to interact with it.
Improved performance for parallel processing of queries to the database and the main actions of msfconsole due to unloading and optimization of some bulk operations to the database service.
The JSON-RPC API allows you to integrate Metasploit with additional tools and languages.
The general structure of web services has been added, providing access to the database and automation APIs; This structure supports extended authentication and concurrent operations.
The metashell function allows users to run background sessions and interact with shell sessions without having to update to a Meterpreter session using the background function.
External modules add Metasploit support for Python and Go in addition to Ruby.
Any module can be sent to multiple hosts. To do this, specify the range of IP addresses using the RHOSTS parameter or specify a link to the file using the file: // parameter. Metasploit now treats RHOST and RHOSTS as identical parameters.
The updated search engine improves the launch time of the Metasploit Framework and eliminates database dependency.
Added evasion modules and libraries to create an obfuscated payload without the need for external tools.
What I want to note
The new JSON-RPC API from Metasploit will be a great addition for users who want to integrate Metasploit with new tools and languages. Metasploit has long supported automation through its own unique network protocol, but its uniqueness also meant that it was harder to test or debug using standard tools such as “curl”.
Added the ability to write a shell code in C, which is definitely simpler and more exciting than in assembler, and with the new Metasploit 5.0 libraries this has become possible. There is a good whitepaper for this technology and writing your own shellcodes or using the evasion-technician.
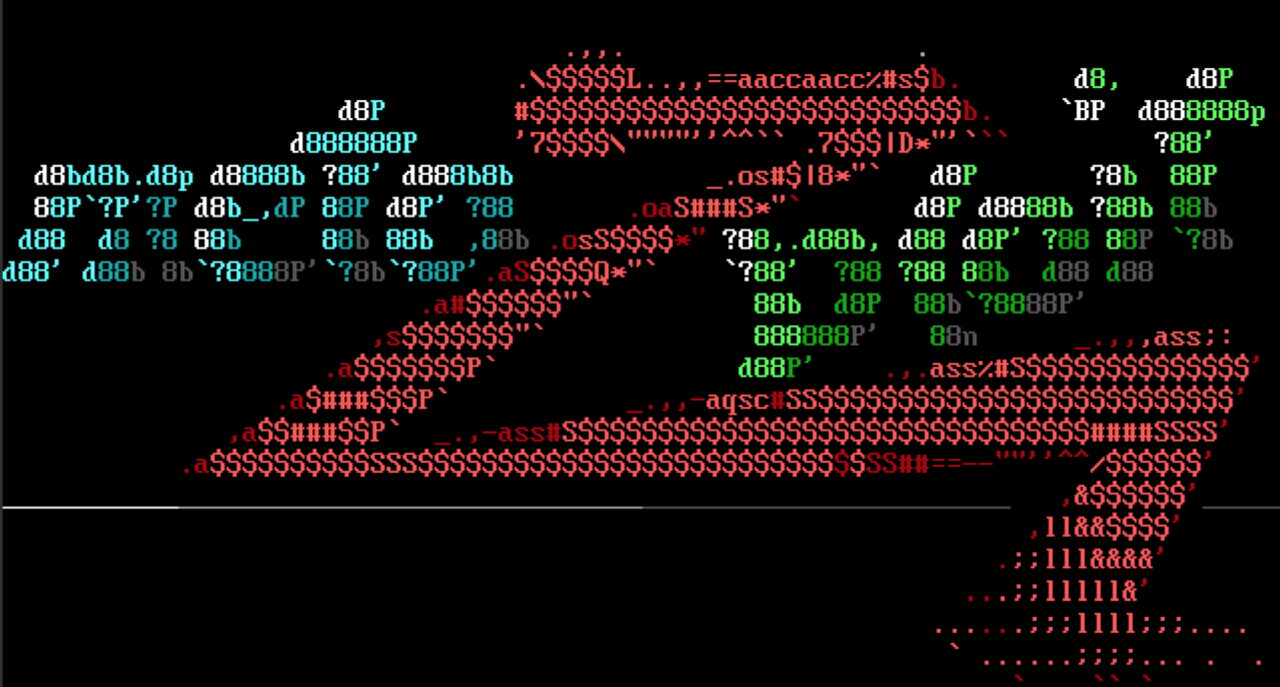
Here is an example of obfuscating payloads without using external tools:

Is there something that is difficult to port to run in the Metasploit Framework without a long finish? Now Metasploit 5.0 includes support for three different module languages: Go, Python and Ruby, this will greatly simplify the addition of new functionality.
Despite the large number of new features, for backward compatibility, Metasploit 5.0 still supports working only with a local database or without a database at all, and also, as before, supports the original RPC protocol based on MessagePack.

Updating such a wonderful framework will not leave anyone indifferent, nevertheless, it would not be superfluous to warn that the use of such tools for illegal or unlawful purposes may entail criminal liability.
