Configuring MikroTik hAP mini for IPTV Beeline
At the last MUM in Moscow , I, like everyone else, was handed the MikroTik hAP mini router.
I decided to replace the old, constantly hanging router with my parents.
To get maximum performance, I decided to use a switch chip. I did not find suitable instructions on the Internet, where there would be a description of the settings and the wired and wireless parts, so I decided to share my experience.
Looking a little ahead, I will say that hAP mini did an excellent job.
The scheme is as follows:
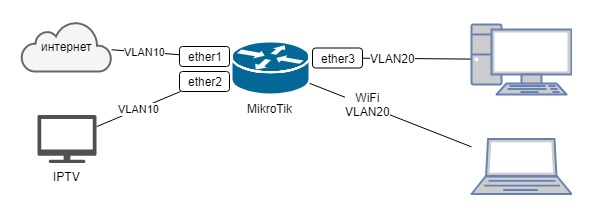
Internet and IPTV from Beeline, IPOE connection. The Internet comes through the first port, the prefix on the second IPTV port, and the local area network via wifi 3.
And so, let's get started:
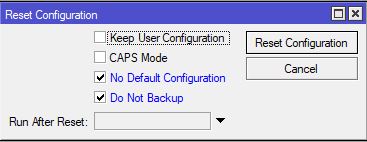
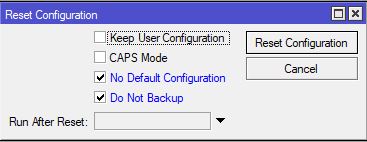
1. Without connecting the router to the Internet, turn it on, connect it to the third port with a cable, launch WinBox, go to the router and reset the settings, remembering to cancel the creation of the backup copy and use the default config.
2. After the router is rebooted, we reconnect to it through Winbox at the MAC address
3. Run New terminal and enter the following commands:
The very first thing is to change the password for the admin user.
Ideally, create another user, and delete admin.
Create a bridge:
Add interfaces to the bridge:
We create two additional VLAN interfaces on the bridge:
Configure on VLAN interfaces:
Configure WiFi (do not forget to replace the SSID and password with your own):
Internet connection us IPOE, i.e. we get the address via DHCP. Note that dhcp-client is configured on VLAN:
Configure the local network:
For convenience, we combine the interfaces into groups:
Create the minimum rules for the firewall:
In the ManageIP group, add the addresses from which access to the router will be:
Configure NAT to access the Internet from LAN:
Well, in conclusion, not mandatory, but useful commands:
Allow neighbor discovery only from the local network.
If you have not updated ROS and you have 6.40.4:
If updated to the latest, then:
But in this case, the MAC connection from the wifi network does not work. Any ideas why?
That's all.
You can connect the provider cable to the first port and test.
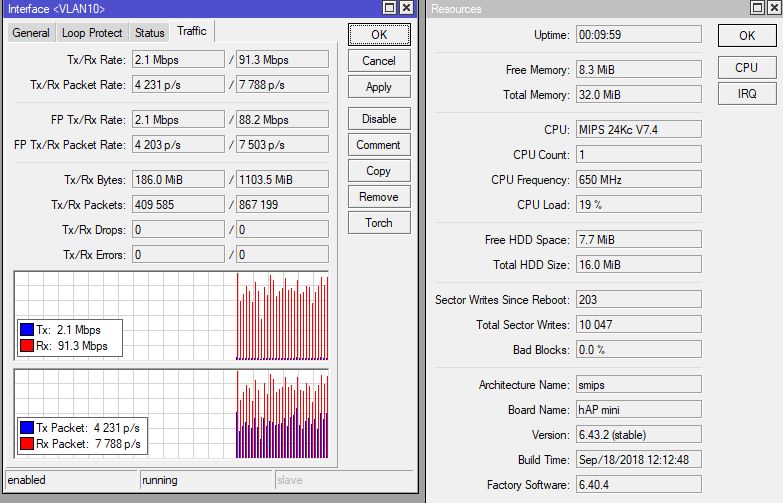
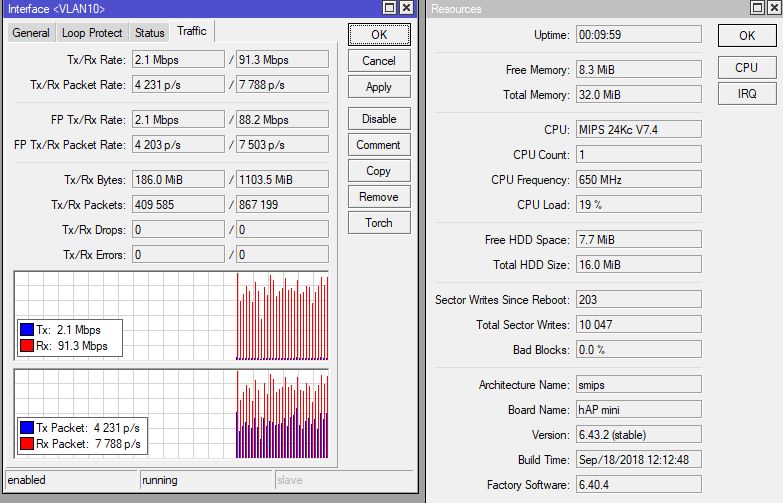
The results of a small test showed that the cable received almost all of the 100Mbps that the provider gives (launched the torrent), the IPTV set-top box works, while the processor load on the router was only 20%. By WiFi it was possible to get only 25 Mbps, the air is too badly polluted, but this speed is enough.
I decided to replace the old, constantly hanging router with my parents.
To get maximum performance, I decided to use a switch chip. I did not find suitable instructions on the Internet, where there would be a description of the settings and the wired and wireless parts, so I decided to share my experience.
Looking a little ahead, I will say that hAP mini did an excellent job.
The scheme is as follows:
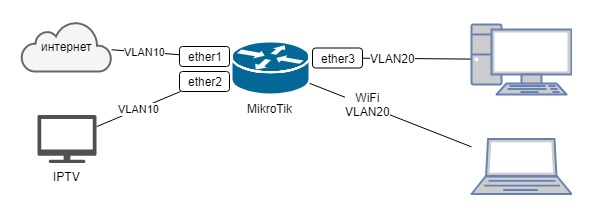
Internet and IPTV from Beeline, IPOE connection. The Internet comes through the first port, the prefix on the second IPTV port, and the local area network via wifi 3.
And so, let's get started:
1. Without connecting the router to the Internet, turn it on, connect it to the third port with a cable, launch WinBox, go to the router and reset the settings, remembering to cancel the creation of the backup copy and use the default config.
2. After the router is rebooted, we reconnect to it through Winbox at the MAC address
3. Run New terminal and enter the following commands:
The very first thing is to change the password for the admin user.
Ideally, create another user, and delete admin.
/user set admin password=qwFnnNn#4$2hWR#QirExCreate a bridge:
/interface bridge add name=bridge1 protocol-mode=noneAdd interfaces to the bridge:
/interface bridge port
add bridge=bridge1 interface=ether1
add bridge=bridge1 interface=ether2
add bridge=bridge1 interface=ether3
add bridge=bridge1 interface=wlan1
We create two additional VLAN interfaces on the bridge:
/interface vlan
add interface=bridge1 name=VLAN10 vlan-id=10
add interface=bridge1 name=VLAN20 vlan-id=20
Configure on VLAN interfaces:
/interface ethernet switch vlan
add independent-learning=yes ports=ether1,ether2,switch1-cpu switch=switch1 vlan-id=10
add independent-learning=yes ports=ether3,switch1-cpu switch=switch1 vlan-id=20
/interface ethernet switch port
set 0 default-vlan-id=10 vlan-header=always-strip vlan-mode=secure
set 1 default-vlan-id=10 vlan-header=always-strip vlan-mode=secure
set 2 default-vlan-id=20 vlan-header=always-strip vlan-mode=secure
set 3 vlan-mode=secure
Configure WiFi (do not forget to replace the SSID and password with your own):
/interface wireless security-profiles
set [ find default=yes ] authentication-types=wpa2-psk eap-methods="" mode=dynamic-keys wpa2-pre-shared-key=MyWifiPassword
/interface wireless
set [ find default-name=wlan1 ] band=2ghz-onlyn disabled=no mode=ap-bridge ssid=MyWifiName vlan-id=20 vlan-mode=use-tag wireless-protocol=802.11 wps-mode=disabled
Internet connection us IPOE, i.e. we get the address via DHCP. Note that dhcp-client is configured on VLAN:
/ip dhcp-client add dhcp-options=hostname,clientid disabled=no interface=VLAN10
Configure the local network:
/ip address add address=192.168.11.1/24 interface=VLAN20 network=192.168.11.0
/ip pool add name=pool-lan ranges=192.168.11.2-192.168.11.99
/ip dhcp-server add address-pool=pool-lan disabled=no interface=VLAN20 lease-time=1h name=dhcp-server
/ip dhcp-server network add address=192.168.11.0/24 dns-server=192.168.11.1 gateway=192.168.11.1
/ip dns set allow-remote-requests=yes
For convenience, we combine the interfaces into groups:
/interface list
add name=WAN
add name=LAN
/interface list member
add interface=VLAN10 list=WAN
add interface=VLAN20 list=LAN
Create the minimum rules for the firewall:
/ip firewall filter
add action=accept chain=input comment="Allow icmp" protocol=icmp
add action=accept chain=input comment="Allow established & related" connection-state=established,related
add action=accept chain=input comment="Allow access for ManageIP group" src-address-list=ManageIP
add action=drop chain=input comment="All other drop"
add action=fasttrack-connection chain=forward comment=Fasttrack connection-state=established,related
add action=accept chain=forward comment="Allow established & related" connection-state=established,related,untracked
add action=drop chain=forward comment="Drop invalid connection packets" connection-state=invalid
add action=accept chain=forward comment="Allow Internet" in-interface-list=LAN out-interface-list=WAN
add action=drop chain=forward comment="All other drop"
In the ManageIP group, add the addresses from which access to the router will be:
/ip firewall address-list add address=192.168.11.0/24 list=ManageIPConfigure NAT to access the Internet from LAN:
/ip firewall nat add action=masquerade chain=srcnat out-interface-list=WANWell, in conclusion, not mandatory, but useful commands:
/ip cloud set ddns-enabled=yes update-time=no
/system clock set time-zone-autodetect=no
/system clock manual set time-zone=+03:00
/system identity set name=MyHome
/system ntp client set enabled=yes primary-ntp=95.165.138.248 secondary-ntp=89.175.20.7
Allow neighbor discovery only from the local network.
If you have not updated ROS and you have 6.40.4:
/ip neighbor discovery
set ether1 discover=no
set ether2 discover=no
set ether3 discover=no
set wlan1 discover=no
set bridge1 discover=no
If updated to the latest, then:
/ip neighbor discovery-settings set discover-interface-list=LAN
But in this case, the MAC connection from the wifi network does not work. Any ideas why?
That's all.
You can connect the provider cable to the first port and test.
The results of a small test showed that the cable received almost all of the 100Mbps that the provider gives (launched the torrent), the IPTV set-top box works, while the processor load on the router was only 20%. By WiFi it was possible to get only 25 Mbps, the air is too badly polluted, but this speed is enough.