So, you decided to create a security department ...
This article answers the question of what he should do and how, with all the intimate details. It is understood that there is a project (startup) with a web part that worked for some time without security testing, but for some reason decided to implement it. For the last 2 years I have been working security in a startup with very large clients (startup is one of the leaders in the world in its field), and I'm sure I have something to say on this topic (naturally, all the information below is just my ideas, approaches and thoughts, and not a howto guide and not a step to the side). The article is dedicated to the concerned authorities, PMs, as well as the person who will be referred to as the Security Testing Team Lead and create a similar department from scratch.

So, you decided to create a security department ...
My congratulations, even if you just thought about it (and it's really cool, if you are taking this moment into account when hiring new employees, I wrote about it ). They break everything and everywhere, and more and more often. Nowadays, a business can really be shaken from leaks of information (including user information). Over the past year, full access has been gained to LinkedIN, Stratfor, Gamigo, NVidia, Adobe, eHarmony, Blizzard and many others. But for example, yesterday they broke into Ubi, did you hear ? Although, it’s not surprising, they write that they have vulnerabilities right on the password change page

Oh well, let's get down to business. And so, human-security appears in the company. He is a specialist from himself, who, first of all, owns the skills of a pentest and can do this job. Also, some team management skills, knowledge of CI systems, as well as redmines or similar things (depending on the specifics of the project, but generally similar approaches everywhere). What should he do?
First month - second
Start testing everything yourself, and in blackbox mode. We get a list of projects (their domains). Perhaps a list of IP addresses of all the servers involved in the project (will reduce the time for reconnaissance). And we begin to test.
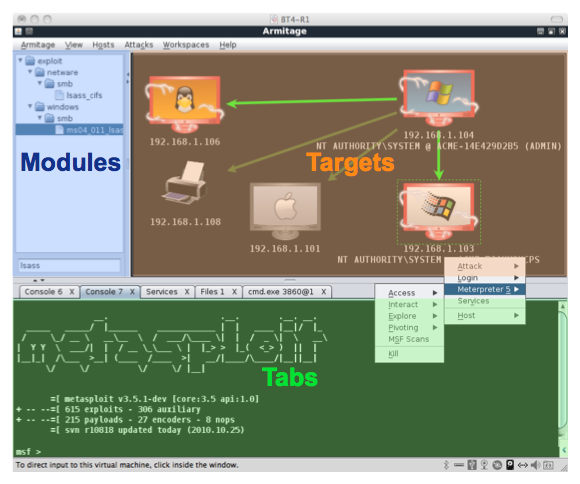
First network services . We will scan the ports, arm ourselves with msf + armitage, check all exploits, the configuration of the dns server ( axfr , dns replay attack), and the web server . We test the "weak" accounts, not forgetting to use the pairs startupname: startupname and the like. In general, we are trying to break through the network in full, do not touch the web (if only during breaks). Along the way, write to ourselves all the software used (nginx / apache / pgsql). We will use this info later. For me it's just a text file with IPs and nmap results.
Weekdays
As soon as we finished, reported, with the administrator everything was corrected, they went to the web. And so, you need a quick, but more or less high-quality bypass. We launch various scanners that will allow us to test the resource “head on”, or maybe even find something. We arm ourselves with a burp-suite and go explore the functionality. Everywhere we endlessly send a universal xss vector (an old thing, but what kind):
Hidden text
"> [img = 1] javascript:/*-->We look at various parameters that can be easily replaced or enumerated, in general we are looking for some obvious parameter tampering . We pay special attention to uploading files there. We try slave-unknown files (for example, in the case of php scripts with mime type jpg or png (idat chunks)). Quotation marks are everywhere. In general, it’s not for me to talk about this here, everyone has their own techniques. We hope, by the way (depending on the size of the project), how much time we will spend on sorting out “for luck,” for example, 10 working days.
Putting it all together, maybe you will find something that needs to be “twisted”. In general, we spend this time on “head-on” attacks and fix everything that an attacker would find if he had nothing to do with the company (as a fact, he knows almost nothing about it). Most likely, it is during this period that the most critical bugs will be found and fixed.
Month Three-Six
In a month or two we can study the project, understand its logic and work. And we begin to take root in the development ... Whitebox in all its glory.
Much depends on the workflow in the project. The main idea of the implementation is to implement security code review and / or security testing of features that are being prepared for the next release. New -> in progress -> done -> in testing -> tested -> security in testing -> security tested . The point is that one person simply can’t cope with security testing of all features (it’s obvious), so for now (if we haven’t taken anyone to ourselves) we only test critically important things (evaluate them subjectively).
Here, before each release, you can do a full diff with the production server and watch all the new code written. Very helpful.
And here we start, not in the "crazy" mode, but more calmly and measuredly, dividing the functionality in parts to test it. Every parameter, every ajax request, and especially all kinds of forgotten things that nobody uses and that were written by a developer who quit 2 years ago (usually a lot of mistakes are made at the beginning of development, because everything needs to be “urgently urgent, release soon!”) . At this stage, the leadership of the security team lead should not expect the same “booms” as in the first 2 months of work.
Sixth month + or we took someone else
At the moment when we decide that we have free time (the project as a whole is covered with tests, the source code has already been received and its analysis has been carried out, in the database where salt has to be added, md5 has been “cut” everywhere, etc.) we start to automate we implement our work and implement security auto-tests, which we can create on the basis of various scanners (for example, nmap - saved everything in the database, if the state port changed the next time we launch it, we report it). Screwed webui to w3af from Yandex (By the way, I do not yuzal). In general, we begin to write code and this is normal (even though the position is not a programmer).
If there is still a person (or maybe not one) and if people are creative, we are discussing to check on the project. And so - we delegate to them part (or all) of the work of 3-6 months (sometimes remembering to check what and how), expanding the set of autotests and not only.
Well, the office, employees. We read , apply. If possible, we do a mass mailing about the need to update some kind of plugin / browser, if necessary.
All the time
We carry out staff training (mainly developers, point out their mistakes, expand our horizons, etc.), monitor exploits (remember, did we record all the software in the first two months of work?), We look at the reports of scanners implemented in CI development, constantly, constantly (!) we read new news and twitter from various security persons and companies (or just different news aggregators), attend / speak at conferences (PHDays / ZN at least, if we take the Russian Federation), play CTF. Perhaps the period of some "freebie", but most often there is (or is invented by ourselves) some new technique that needs to be urgently tested on the project. We support security from all sides and set periods of “full bypass”. When, with a fresh head, as if for the first time, the whole project is being handled again (see months 1-2).
Generally
Many points depend on the project, but according to my personal feelings, if you organize the work, as I described above, it will turn out efficiently (and there will be no similar reviews about it ). Efficiency is expressed in lowering the risks of violating the security of the resource and its users. In monetary terms, security is expressed quite difficultly (although there are methods).
And as a small ad, if you know any interesting startup / project / company in St. Petersburg (or distance), where (maybe) such a person is needed, or a QA with such “inclinations”, or a researcher who is ready to learn and develop , then let me know (I will be grateful), I am looking for work and various options. Or just if you have something to say on the topic of job search, then write :-)
Startups with dev-offices and decent salaries who are ready to hire non-Russian citizens in St. Petersburg almost do not know (preferably working abroad, I do not want to leave constant communication on English).
Thank you for your attention and reading, I will be glad to discuss the article and expand my views on the organization of such a process.
