20th century pirates
 In the 1990s, the software market in freshly formed Russia was developing actively, but somewhat one-sidedly: the bulk of the PC programs were foreign programs with removed (or initially absent) copy protection; often the same Russian craftsmen translated the program into Russian (sometimes overwriting the original copyrights), dealt with copy protection, and eventually sold the program at the price of a carrier and without any support. This was different from the modern warez scene, half-underground and completely virtual: Russian sellers of other people's software didn’t hide at all, on the contrary - they advertised in magazines, issued completely physical diskettes and (later) CDs, and they pulled whole shelves in computer stores . It is clear that domestic software development in such an environment was not too viable: the already mentionedThe Lexicon - a program of quite worthy quality, which freshly educated Russian businessmen tried to put on a commercial footing - was bought "legally" well if one out of a hundred users.
In the 1990s, the software market in freshly formed Russia was developing actively, but somewhat one-sidedly: the bulk of the PC programs were foreign programs with removed (or initially absent) copy protection; often the same Russian craftsmen translated the program into Russian (sometimes overwriting the original copyrights), dealt with copy protection, and eventually sold the program at the price of a carrier and without any support. This was different from the modern warez scene, half-underground and completely virtual: Russian sellers of other people's software didn’t hide at all, on the contrary - they advertised in magazines, issued completely physical diskettes and (later) CDs, and they pulled whole shelves in computer stores . It is clear that domestic software development in such an environment was not too viable: the already mentionedThe Lexicon - a program of quite worthy quality, which freshly educated Russian businessmen tried to put on a commercial footing - was bought "legally" well if one out of a hundred users. (When I first entered the math, our professor warned us: “ Do not even expect that in Russia you can make a living by programming. Of the domestic software companies, only 1C is profitable, and that only because regulatory documents change every year , and the stolen version of the software after a year becomes useless. Probably, this is such a state policy to support programmers - to change accounting requirements every year. ")
Therefore, it is natural that the magazines of the 1990s actively discuss the current unfavorable situation for programmers, and suggest ways to influence it. Everyone agrees that the dominance of piracy is a feature of the transition period, caused by a temporary lack of interest of Western copyright holders in the Russian market; and that in a few years, the software market in Russia will develop into a similar European one. But even now, fifteen years later, the layman’s attitude towards software copyright has changed little. So, some recommendations of that time remain relevant to this day.
Last time, I promised to publish an article by Olga Uskova , now the owner of so many awards and honors, that they managed to fill an entire article on Wikipedia: (ComputerPress, January 1995)

In this article, the vice-president of Cognitive Technologies OA Uskova will raise the topic of marketing software products in Russia.
How to sell programs in Russia,
or Berries Commercial Director
A year and a half ago in Russia there was an idea that the program is such a thing that learned cranks or naive foreign companies provide free to resourceful Russian users. Having a licensed copy was just as embarrassing as buying a ticket on public transport or following traffic rules. A discussion of the psychological aspects of this problem would have to start from the time of Ivan the Terrible ...
It is all the more surprising that for such a short period (one and a half years - nothing compared to the existence of commodity-money relations in Russia), a fantastic shift occurred in the minds of our compatriots. There was a layer of intelligent users, who finally realized that “stealing more is expensive”, “avaricious pays twice”, etc.
The international policy of companies - suppliers of software products is aimed at maximum benefits to honest users. The “admission to paradise" here, of course, is the user registration procedure. Say, on the registration card of our CuneiForm for Windows product, the user reads that after registration he will be able, in particular. buy the following copies of the product with a 25% discount, get upgrade with a 70% discount, buy other products of our company at reduced prices, receive a free update for 2 months, use the hot-line for free and receive our mailing list. If promises are not kept, the company should be legally liable to its customers.
The concept of “software market” includes many serious points: the organization of advertising, sales, user support and the like. It is about this, and not about the exciting successes of Microsoft and Lotus, that you should think in the first place. Remarkable in terms of artistic power, the tales of a cashless start and an instant take-off to millions of sales made life difficult for domestic entrepreneurs with a desire for quick success, because they left behind the hard work of manufacturers and sellers of programs to shape their product markets.
Often, wonderful work of authorship (especially for complex programs with serious scientific stuffing) simply does not reach its buyer. The excellent developments of Russian scientists in the field of speech synthesis, gaming, training and presentation programs literally disappear, work on the workstation has been abandoned, and large data management systems that could become Klondike for energetic entrepreneurs have not been transferred to the EU computer. Why?
Of course, the term “production” in Russia in recent years has become synonymous with “hopeless enterprise”, for the production of anything it is impossible to get a loan from any Russian bank. Indeed, the cost of renting space in Moscow far surpassed the European one. And the cost of an advertising company is approaching international standards, although it lags behind in quality. But the potential sales market in Russia is huge. The activity of the business part of the population is rapidly gaining momentum. So the question is not whether it is possible to sell programs in Russia, but how to do it.
Of course, Russian marketing necessarily contains all the components of a textbook Western textbooks. This may not even be discussed. But it is very important that marketing in Russia has regional psychological specificity. These Russian features are infinitely difficult to feel for foreign specialists, whether they are thrice professional, and often this leads to the conclusions of venerable foreign companies: “Wild country! The market is unpredictable or nonexistent. It’s impossible to work. ” Therefore, individual Russian representative offices of large Western companies still exist at the expense of parent companies.
At the same time, the non-cash starts of many Russian companies are due, on the one hand, to the cautious policies of banks, and on the other hand, to the style of work and the system of outlook on the life of the leadership of such companies that do not want to get involved with mafia structures. Therefore, the production and sale of software products, one of the most profitable business areas with a high profit margin and an almost unlimited sales market, in Russia is still a risk zone and an activity for desperate entrepreneurs.
Planning the development of our company and relying on the results of the six-month work of the Cognitive Technologies analytical group, I myself specified in some way this same Russian “strawberry”, the knowledge of which partially ensured our company a high speed of promoting its products over the past year and a half on the Russian market. But when I offer my observations to a wide court of the public, I would like to warn well-known marketers in advance that these considerations do not carry a shade of scientific generalization, but are some squeezes from a not very long, but rather successful practice.
Berry number 1
So, dear entrepreneur, you decided to trade in products that your potential customers can get for free at any time, although in a rather shabby form. Therefore, the organization of the most attractive and as simple as possible structure of the near-sales service, when even the most greedy and short-sighted lover of free software becomes aware of the benefits of a legal purchase, can fully justify itself both on the moral and material side. Perhaps, the newly formed legislation and appeals from the stands will also help someone. But the Russians are a shot people, as they say: “There are a lot of us, you won’t fine everyone!”
You want your product to be bought. In the case of software products, this marriage is possible only for love. It should be preceded by attentive and professional courtship of each client separately and of the layers of consumers as a whole, planning the inevitability of some quite tangible expenses. Believe me, they will pay off handsomely. In our work in this area, we use some “ABC of love for a client” partially accepted, partially homegrown.
Common approaches include:
- mandatory registration of the entire clientele of the company with periodic informing registered users of new movements in the market and updating the range of services of the company;
- necessarily beneficial to the buyer policy of selling new versions (upgrade) with a substantial discount and delivery of add-ons (update) for free;
- refusal to use protection methods inconvenient for the client, or better, a complete rejection of the protection of software products (which, as a rule, does not protect against anything);
- organization of a convenient and qualified technical support service with a dedicated telephone line and, if possible, a specialist visit to the place:
- providing the same, or better, greater amenities when organizing sales on your distribution and dealer network;
- the client should not seek to purchase at the central office, provide him with the opportunity to spend less on transport (extensive dealer network, direct distribution of products to the customer's address, and so on).
Next, see the relevant sections in the proceedings on the organization of sales of programs abroad.
The following can be attributed to homegrown principles.
The principle of the presumption of innocence
If you find faults in the delivery set, you should not conduct a lengthy investigation under the slogan: “Who is to blame?”, Did the villain reveal protection and so on. It’s better to consider that you always only communicate with good people. Another thing is if you suddenly really get direct evidence of malicious intent. Then a bad person should be punished, do not be afraid to set a precedent and arrange a show trial. But in no case do not spread suspicion to the rest of humanity.

The principle of free pies
We always remember with pleasure the “guests” where we were fed deliciously. The path to the heart through the stomach lies not only in the man, but also in the woman who is most enthusiastic about the diet. Therefore, I advise you to pay serious attention to the periodic arrangement of FREE seminars for various layers of potential clients or for new layers of potential users who have long been moving into a well-organized “party”. Such an approach is like a bridge to the creation of a club of company lovers. This is necessary simply for the formation of a layer of people who are qualified to use new technologies, that is, the introduction of a fashion in Russia for cultural office work. Doing business with the help of counts and crowds of girls ready for any salary (and not very sensible) is a difficult legacy of 1917.The principle of meeting clothes
When one of my acquaintances, an entrepreneur, comes to a potential client, he looks like this: BMW, a secretary in a mink, a suit from Carden. When he appears with a request to defer payment, he is dressed, of course, in a cloak crushed by public transport and a hat from the time of the beginning of perestroika. Yes, working in the software market is similar to a performance with changing clothes; moreover, this is a real premiere during the period when the market began to exist. And whether it will end with a full house or if rotten products of a completely different market will fly into you depends on the thoughtfulness of a huge number of little things, including the costumes of the characters.Whether your office is in the kitchen of your own apartment, or if you occupy several floors of a building overlooking Red Square, your suit and your managers should demonstrate the full degree of respect for your customers. In the same way, the natural charm (not to be confused with the length of the legs) of managers directly communicating with the client automatically increases the quotation of your products on the market.
Play a game with me and be sure to win!
When my younger brother, at a tender age, played chess with himself, he was madly upset when he lost to himself. You must completely exclude even such an innocent situation for your customers during lotteries, raffles and similar events. Each event at your stand at exhibitions is an occasion for the distribution of presentations from the company to all participants. You should always be sincerely grateful to the people who paid attention to you. Moreover, the presentations should lie in the field of the company so that your wonderful programs will not be lost behind the prizes. It is better not to use distracted household gifts such as perfumes and watches.Break a saucer with a blue border!
Which of us did not have to close our eyes at times to imagine a saucer with a blue border, filled with millions of registration cards of users of your programs for a month. My advice to you: immediately break this favorite Ostap Bender dish. Such visions undoubtedly do great harm to the fragile minds of Russian managers. Do not despair when you receive a promise from a mouth-watering client (after several weeks of “processing”) to think about the possibility of acquiring your products for another year. The expectation of speedy victories will liken you to the person who planted a tree and dig it up every day to find out how it grew over night. Here it is more reasonable to choose a strategy of a bore, annoying, but painstakingly moving towards a goal, than a touchy hurry who knows how to effectively slam doors and flunk one thing after another.Berry number 2
In order for you to have problems with the theft of your products, the demand for these products must first arise. For this, unfortunately, unfavorable initial conditions have developed in Russia. On the one hand, the Russians distrust of domestic production, on the other hand, there is a strong lag and immaturity of the computer market and related industries.
Oddly enough, it seems most useful, having removed protection for the first release of the program, to give the opportunity to install your products on as many computers as possible, even by illegal copying. If you are able to regularly develop your program. then very soon it will become clear to your underground users that it’s easier to BUY the latest version with full documentation and automatically join the support line and subsequent discounts from the company. Of course, it remains outside the brackets that all of the above is true only for a program that has matured as a product. The program should not only be a cool written code (only families and friends of developers will understand this), but also have a thoughtful, modern interface, convenient and understandable documentation.
By the way, I believe that in Russian conditions for start-up companies, the requirements for excellent quality packaging printing are not indispensable. If a company starts without initial investment, then at very high prices for printing services in Russia, it simply cannot immediately afford good packaging. With the high quality of the program itself and the right choice of the client market, the company can gain good momentum, gradually improving the quality of packaging. The first box of the well-known TIGEr OCR system resembled a box of marshmallows.
Berry No. 3, or Business in short pants
When the children begin to play some kind of game, they first agree on the rules: who drives, how to “get off” and so on. In Russia, the game of computer business at the very beginning and the rules are only being worked out. You will have to work under the conditions of freshly baked legislation, many of the points of which have not been tested in real situations. Therefore, the probability of collision with the boorish behavior of unscrupulous partners is very high, especially in the field of printing and advertising services. The only way to combat dishonesty in the market is to carefully draw up contracts at every step, with well-designed penalties. And do not stand aside, swallowing resentment. Having a properly organized legal document in hand, contact the arbitration. Only if we ourselves will take seriously the adopted legislation, it will finally begin to act in full force. By the way, I do not recommend partnering with close relatives and friends. Maintaining a business and discerning style in such conditions is almost impossible.
Carnegie at the beginning of the century introduced the concept of moral business. And almost a century passed before us, which in practice proved the full validity of this simple (and ingenious like all simple) theory. Its essence is the observance in its work of universal moral principles of behavior and the old Russian proverb: “Without labor, you can’t take a fish out of a pond.” Now, at the very beginning of the market, a lot of all the turbidity has been lifted from the bottom. Many, wanting to achieve quick success, literally went over their heads. This is acceptable if the company wants to break fast money and quietly disperse, but do not call it a business. If you build a business firmly and for a long time, it is better to remember Carnegie.
This article is based on a book that I am going to release in 1995. This book is more like a diary of a commercial director than a serious scientific work. But if someone ever learned something from the mistakes of others, then this work will certainly help you, since it contains a description of the huge number of my personal and collective mistakes in the course of mastering by me and my colleagues from Cognitive Technologies a difficult business - selling programs in Russia.
Cognitive Technologies, tel: (095) 135-50-88.
It is gratifying that Cognitive Technologies are still developing software (they even had a blog on Habré! ), Unlike Microinform, with their purely western approach to marketing (the main thing is a smart box! ) And with raids on Moscow BBS. But in a paradoxical way, in the same issue of ComputerPress as Uskova’s article, on a full-color tab, collections of “Stop other people's games on one disk” from a certain Tech Express Software are advertised:
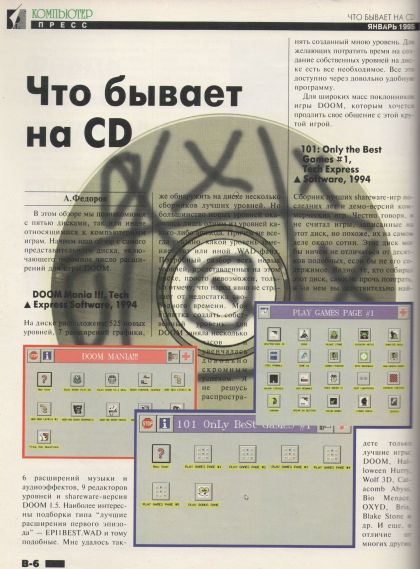
What happens on CD
A. Fedorov
In this review we will get acquainted with five discs, one way or another related to computer games. We begin our review with the most representative disc, including a huge number of extensions for the game DOOM.DOOM Mania !!!, Tech Express Software, 1994
The disk contains 525 new levels, 7 graphics extensions, 6 music and audio effects extensions, 9 level editors and the shareware version of DOOM 1.5. The most interesting are collections of the type “best extensions of the first episode” - EPI1BEST.WAD and the like. I also managed to find several collections of the best levels on the disk. But most of the new levels turned out to be only one of the levels of any episode. Moreover, it is not always indicated which level replaces one or another .WAD file. A detailed analysis of all the new levels presented on this disc is simply impossible, I only note that people clearly do not suffer from a lack of free time. My attempt to create my own level for DOOM took several hours and was a rather modest success. I will not dare to spread the level I created. For those who want to spend time creating their own levels on the disk, there is everything necessary. All this is available through a fairly convenient program.For the masses of fans of the game DOOM who want to extend their communication with this cool game.
101: Only the Best Games # 1, Tech Express Software, 1994
A collection of the best shareware games of recent years and demos of commercial games. Honestly, I did not count the games recorded on this disc, but it looks like there are actually about a hundred of them. This disk could not differ from dozens of similar ones if not for its contents. It can be seen that those who collected this disc are not averse to playing themselves, and on it you really will find only the best games: DOOM, Halloween Hurry, Wolf 3D, Сatacomb Abyss, Bio Menace, OXYD, Brix, Blake Stone, etc. And yet, unlike many other discs, games can be launched directly from the CD, they have annotation, and all this is available through a convenient menu. Here is such a disk.However, who will surprise a pirated DOOM? Even now, anyone can make their Quake clone with the stolen pak1.pak, leave at the end of the game the developers message " What is important is you love our game, and gave us your money. Congratulations, you are probably not a thief. " - and all the same, no one has claims to the legality of such a clone.
An interesting analysis of the attitude of programmers to the prohibition of copying software and copy protection hardware was published in ComputerPress 8'92: Choosing an NSC protection system for software always causes difficulties. How to overcome the subjective factor when comparing two or more systems of protection against NSC with each other? How to evaluate the reliability of protective mechanisms?

This article is devoted to these issues.
Buy or steal? Protection rating
Currently, software packages aimed at protecting executable modules from NSC (unauthorized copying) and unauthorized access (unauthorized access) appear like mushrooms after rain. If at the beginning of the summer of 1991 we were able to catch about 20 protection systems [1] in murky streams of unauthorized copies, today this number has at least tripled. They are written by almost everyone who knows how to calculate the checksum, knows the structure of the .exe file, and has a lot of free time. The cost of protection systems is the most diverse - from 100 rubles to 30 thousand rubles. Workmanship and capabilities are also very different and are practically not connected with the package price. Therefore, it is sometimes difficult for an inexperienced user to make the right choice in the market for such products.
The purpose of this article is to develop an approach to the examination of systems of protection against NSC.
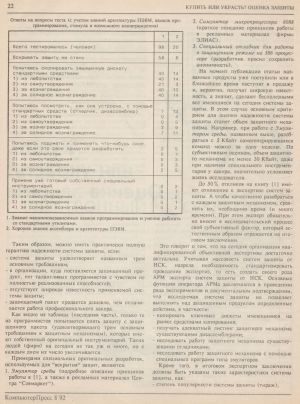
The first step in conducting research was aimed at studying the methods of work of hackers and just lovers of “undressing” protected programs for their own satisfaction. To begin with, we tested 118 programmers with different professional backgrounds and representing various institutions for their interaction with the protected package. Respondents' answers to test questions are shown in the table below.
Interestingly, such an incentive as self-affirmation is not much inferior to monetary reward, especially in the conditions of our specific market. This is understandable, because one of the indicators of the developer’s professionalism is the presence of independently obtained listings of widely known protection mechanisms, for example, the COPYLOCK package. Therefore, one of the important characteristics of a protection system is its popularity. Nobody will be engaged in research of a little-known defense system for the sake of self-affirmation.
Testing results show that 98% of programmers will not try to overcome the defense mechanism if the protection system of the executable module guarantees:
- the impossibility of copying a key floppy disk with the widely known copying tools available to almost every developer, such as the COPY II — PC, COPYWRITE, UNLOCK;
- the impossibility of researching a software product using widely known debuggers, disassemblers,
Thus, it is possible to have an almost complete guarantee of the reliability of the protection system if:
- protection system meets the three basic requirements;
- in the organization where the protected product is delivered, there are no talented programmers with a sense of incompletely realized abilities;
- there is no widespread popularity of the applied protection system;
- the protected package is sold cheaper than the work of a professional hacker.
As can be seen from the table (last part), only those of the programmers will try to remove protection from the protected package (satisfying the three basic requirements for protective mechanisms) that have their own original toolkit. There are not so many such people (firms) today, but their number is increasing every day.
Examples of special original designs used to “open” the defenses are:
- Environment emulator (a detailed description of the principles of work in [1], as well as in promotional materials of the Sovmarket Center).
- Microprocessor simulator 8088 (a brief description of the principles of work in ELIAS advertising materials).
- A special debugger for working in protected mode on a 386 processor (the developer asked to remain anonymous).
At the time of publication of the article, these products have already arrived or will soon go on sale and are likely to become widely known, which means that they will render all protection systems available today unhelpful. In this case, the main criterion for assessing the reliability of the protection system will be the volume of the protective mechanism. For example, when working with the Environment Emulator , mentioned above, you can deal with 5 Kbytes of self-generated commands in one week. According to subjective estimates, the volume of the defense mechanism is at least 30 Kbytes, even if a hacker has special tools, significantly complicates the life of the researcher.
Up to 50% of responses to the book [1] are related to the examination of protection systems. And in order to qualitatively deal with each protective mechanism, to compare them, it takes time (and a lot of time). At the same time, the expert necessarily introduces his subjective factor into the research process, which naturally reflects on the final conclusion.
This suggests that today the organization of qualified objective examination is quite relevant. Given the mass protection systems against NSC, there is a need to standardize the conduct of examinations, that is, to create a kind of automated workplace of an expert of protection systems against NSC. The main functions of the operator of the automated workplace are to conduct a series of experiments and documentary evidence that the protection system under study does not allow certain actions to be performed on the protected product, in particular:
- copy key floppy disks on the market by means of copying;
- receive an adequate listing of the defense mechanism by existing disassemblers;
- to investigate the work of the protective mechanism by existing debuggers;
- explore the work of the protective mechanism using special programs such as emulators.
...
The rest of the article is devoted to the methodology for comparing protection systems against NSCs, and I skipped it.
Answers to test questions (taking into account knowledge of PC architecture, programming languages, incentive and possible reward)
| 1 | 2 | |
| Total tested (person) | 98 | 20 |
| I will not open protection | 58 | 6 |
| I will try to copy the protected diskette by standard means | 40 | 14 |
| 1) out of curiosity | 40 | 14 |
| 2) from self-affirmation | 21 | 3 |
| 3) for a fee | 40 | thirteen |
| 4) for a substantial fee | 40 | 14 |
| I'll try to see how it works using standard tools (debugger, disassembler) | 7 | thirteen |
| 1) out of curiosity | 0 | 4 |
| 2) from self-affirmation | 0 | 5 |
| 3) for a fee | 3 | 9 |
| 4) for a substantial fee | 7 | eleven |
| I’ll try to think and apply something of my own, even if I have to develop my own | 2 | 5 |
| 1) out of curiosity | 0 | 1 |
| 2) from self-affirmation | 0 | 3 |
| 3) for a fee | 0 | 3 |
| 4) for a substantial fee | 2 | 5 |
| I’ll use ready-made own special tools | 0 | 2 |
| 1) out of curiosity | 0 | 1 |
| 2) from self-affirmation | 0 | 2 |
| 3) for a fee | 0 | 1 |
| 4) for a substantial fee | 0 | 2 |
2. Good knowledge of assembler and PC architecture.
In other words, the more professional the programmer, the more willing he will be to crack the copy protection - although it would seem, who can respect it more than professional programmers whose well-being directly depends on the inviolability of copy protection?
But let's move forward five years. The last article I want to share today relates to the Computerra issue number topic for August 1997 - the development of global and local networks made the thin client architecture and Software-as-a-Service model relevant and promising, which, as it seemed then, will inflict a crushing blow to piracy.

... Barrier # 1 - illegal distribution of programs on which you can save as much as no NC will give. In Russia, the laws of the global software market are true only in relation to a small part of it, first of all, to corporate users who value their reputation. It's no secret that pirates are rampaging on the PC software market, thanks to which Russian users are deprived of the problems of their Western colleagues, who are forced to spend considerable money on regular upgrades.
Ilya Billig, Marketing Manager, Microsoft Office in Moscow:“Often in Russian organizations the question posed by the director is: Do you need to buy? - Yes, it is. - How much is? - 10 thousand dollars. - And can we do it differently? - We can go to the "Little pink". For 10 dollars. - And if we steal, what will happen to us? - Nothing. “Well, then we won’t pay 10 thousand!”
Suspicion may crept in that in the face of the looming expansion of NC, pirates are Microsoft's objective allies. So is Microsoft profitable of piracy?
I.B .:“No, not profitable, because the development of piracy in Russia is holding back the software market. Microsoft benefits from a large number of firms supporting its technology. In Russia this is impossible due to the fact that not a single person in their right mind and solid memory will invest money in the development of software with the current level of piracy. “We are losing money not only on sales, but also on the fact that there is no corresponding support in the industry.”
According to Billig, the eradication of piracy in the coming years is out of the question: “If we look at Eastern Europe, the level of piracy is about 70-80%. They started from the same as we. Microsoft is selling more in Czechoslovakia and Poland than in Russia. The immediate task is 80%. The five-year plan is 40-50%. ”
If a networked computer takes root in Russia, it will be a blow to piracy: the client-server architecture and the smart card mechanism exclude it in principle. Another question: but will not 1000-1500 dollars a year prove to be burdensome for Russian users even with undeniable savings on hardware?
Now we have to talk about changes of a more modest scale. As the attack on the pirates continues, more and more corporate users will stop purchasing software on the gray market, in addition to those who today acquire software legally. For Russian companies that cannot do without sufficiently powerful corporate networks, NC may well become a more attractive alternative.
Microsoft fights piracy both through a judicial mechanism and by signing agreements with Russian PC vendors to preinstall Microsoft software to the maximum extent (for example, Microsoft Office in addition to the minimum configuration of Windows 95 on a newly acquired PC). It seems that in this case, user inconvenience is minimized. So much so that the PC remains more profitable than NC thanks to the well-known user conservatism? According to Bruzgin, the very real task for Oracle in the coming years is to deprive Microsoft of about three million dollars in revenue from the sale of pre-installed software products to Russian corporate users by introducing NC.
An Internet-connected network computer for an individual consumer in Russia has more vague prospects. The reasons are known: the same piracy, extremely backward telephone communications and the insufficient degree of development of the Internet, which holds back the language barrier. But this is not so fatal.
I.B .:"Revolution? - Naturally, is coming. Russia follows the same path as all countries. Another thing is that it is in rather peculiar forms, slower. People on the streets know what the Internet is. Looking at home computer sales, we can expect that the next step these people will take is connecting to the Internet. It is about millions of users. But it will be very important to have Russian content. October 25 will strike at a time when a critical mass of Russian content will accumulate. Just look at the provincial newspaper in the world. There in any advertisement: “here is our Internet address”. The Internet is largely destroying the concept of a province. "
Despite all the difficulties, there are people in Russia who want to purchase a computer precisely because of the Internet. Starting next year, they can also become one of the objects of a fierce struggle between supporters of PC and NC, especially between Oracle and Microsoft. Everything can be used here: aggressive advertising, price reduction, struggle for partners. If in Russia assembling a PC turned out to be so profitable that now 64% of the computers sold are domestic brands, one can expect attempts to build simpler and cheaper network computers in Russia.
Interest in NC can show and system integrators. For them, this is a reserve for overcoming the crisis of the industry due to the possible emergence of demand for corporate information systems using NC. Due to its low cost, compared to PC-based systems, this market may turn out to be more massive.
The secular chronicle also testifies that Russia will not remain aloof from the unfolding struggle. In October 1996, Allison met with the president of Most Bank, Vladimir Gusinsky. Ellison’s visit to Russia is scheduled for April 1997, the purpose of which, obviously, will be to promote a network computer and create infrastructure.
What awaits us in the coming years?
Most experts are inclined to believe that we are waiting for the coexistence of NC and PC. At the same time, network computers will establish themselves in offices, and personal computers will retain their positions as home computers. The forecasts of representatives of Microsoft, Oracle and the neutral side are not so different from each other:
IB: “There will be three types of devices. The first of these is corporate PCs. What they will be until no one knows for sure. Diskless stations? - I completely admit. The second type - phones connected to the Internet, combined with computers. The third type is home PCs, to which, in fact, the house will be connected. Which concept is the only correct one? - Neither one nor the other. There will be a fairly wide range of more specialized computers. "
A.B .:“Of course, no one says that a network computer will replace a personal one, especially at home. But where simplicity and unity of the interface and software are necessary, a networked computer can completely replace personal computers in the next 10 years. For example, all public services: hotels, clinics, banking institutions - everywhere you can put a network computer to get help, insert a credit card or dial a personal code. A networked computer is a device for receiving information. ”
CompuLink CEO Mikhail Lyashch is also confident that NC will be able to establish itself in the office, and PC will retain its position at home, as well as that in Russia the transition to NC will be limited mainly to large offices and banks.
How much these forecasts come true - time will tell.
