Stealthphone Software - cryptographic protection of information in mobile phones
Each of us uses a mobile phone or tablet, which, having ceased to be elements of luxury, have become necessary tools in everyday life and production activities. Currently, there are about 6 billion mobile devices in the world, while computers are just 1.5 billion.
The use of mobile phones and tablets involves the transfer of various kinds of information in voice, text and graphic form. This may be data containing details of a personal and even intimate nature. But in modern conditions, when using a mobile phone or tablet, there is no clear distinction between the scope of their application, which, in turn, leads to the accumulation in the device’s memory of not only private information, but also used in the work. One of the consequences of this in 60% of cases, according toPonemon Institute , is the seizure of important corporate information by hackers in the event of the loss of a mobile device by an negligent employee, as a result of which the employing company loses its competitive advantage.
We live in an information space whose borders are endless and legally unlimited by anyone. The emerging situation is taken into account by experts all over the world when determining the approach to solving issues of ensuring information security (cyber security).
It’s not for nothing that US President Barack Obama made a statement in August 2012 that “the cyber threat is one of the most serious economic and national security problems”, he determined that “America’s economic prosperity in the 21st century will depend on cyber security ". Therefore, now all US government agencies of federal subordination are engaged in the development and implementation of a unified information security strategy for energy companies, commercial and non-profit organizations working in strategic sectors of the country's economy.
Information security technologies were also an important sector of the largest international exhibitions held in 2012 on information and telecommunication technologies. Of particular interest at these exhibitions was the section on ensuring information security of mobile devices.
Taking into account that by 2014, 80% of all Internet access will be via mobile phones and tablets, foreign companies are actively developing various information protection systems for mobile devices. In most cases, a fully software solution is used that is installed on a mobile phone or tablet in order to reduce costs and provide convenience for the user.
As a result, “avaricious pays twice”: modern hackers using complex virus programs, as well as various attacks via BlueTooth, Wi-Fi and easily bypass such protection. It must also be understood that the technical means used by them for this purpose are comparable in their characteristics with the means that the special services use. For example, for the purpose of cyber thefts, computers are used that can collect several trillion passwords per second. Given that this article is aimed at the mass user, we will not dwell on the consideration of “secure” technologies, as for President Obama, the development of which costs tens of millions and costs tens of thousands of dollars. In our case, this is unacceptable.
The solution to the problem described above was the creation of conditions for the protection of information outside of mobile devices. The company ROHDE & SCHWARZ went this way, but the device developed by it is able to encrypt only voice.
The Stealthphone Software solution, created by Ancort specialists, is software that can be supplemented with hardware to provide the necessary level of protection for the information array.
“Stealthphone Software” is a software application for a mobile phone or tablet running on the operating systems iOS, Android, Symbian and BlackBarry.
This application is intended to protect the information of your mobile phone or tablet during data transfer via voice, SMS, MMS and e-mail. This application, installed on your mobile phone or tablet that supports the function of connecting to the Internet, will ensure the confidentiality of any information transmitted over communication networks 3G, 3,5G, EDGE, Wi-Fi, WiMAX. “Stealthphone Software” works through Ancort’s IP servers, which transmit information transmitted through them in a secure form, which excludes access to data by the operators of such a server and reduces the cost of communication services for subscribers. The quality of voice transmission is comparable to that provided by the latest program for IP-telephony Viber, widely distributed in the West, having 70 million users and being the main competitor of Skype. Viber user capabilities (SIP-client, SMS), being provided for use, in the Stealthphone Software application are supplemented with the possibility of sending encrypted SMS, MMS, e-mail and secure chat.
A number of competitive software solutions are presented on the information security market, which, according to the developers, guarantee the protection of information when working in IP networks.
In particular, Ancort experts conducted a preliminary analysis of the capabilities of the Stealthphone Software application and the SilentCircle solution. As a result, it was concluded that when comparing the two specified software products, the advantages of Stealthphone Software are:
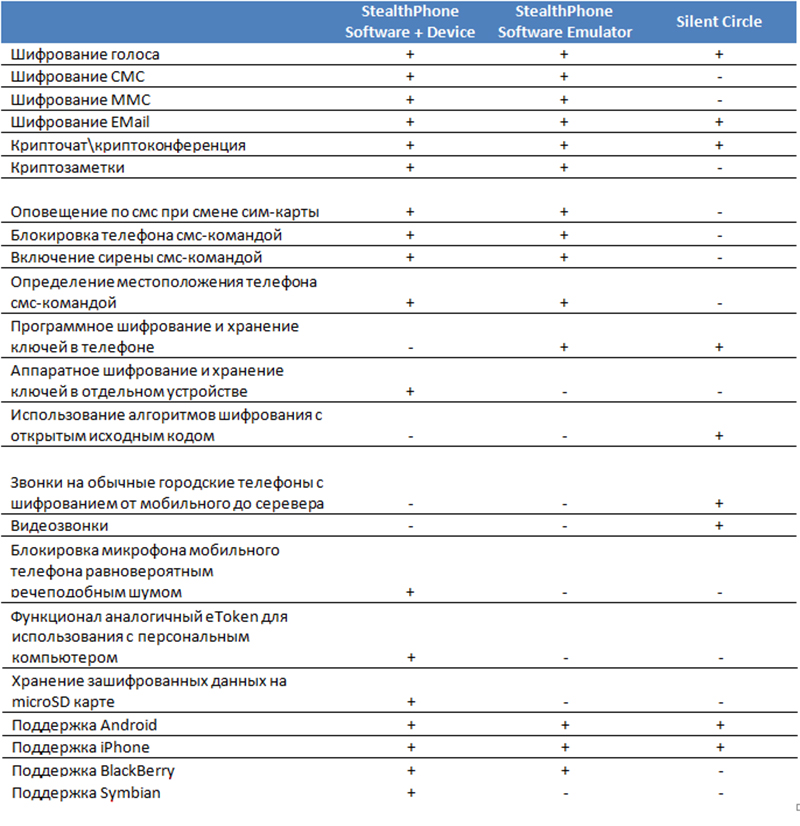
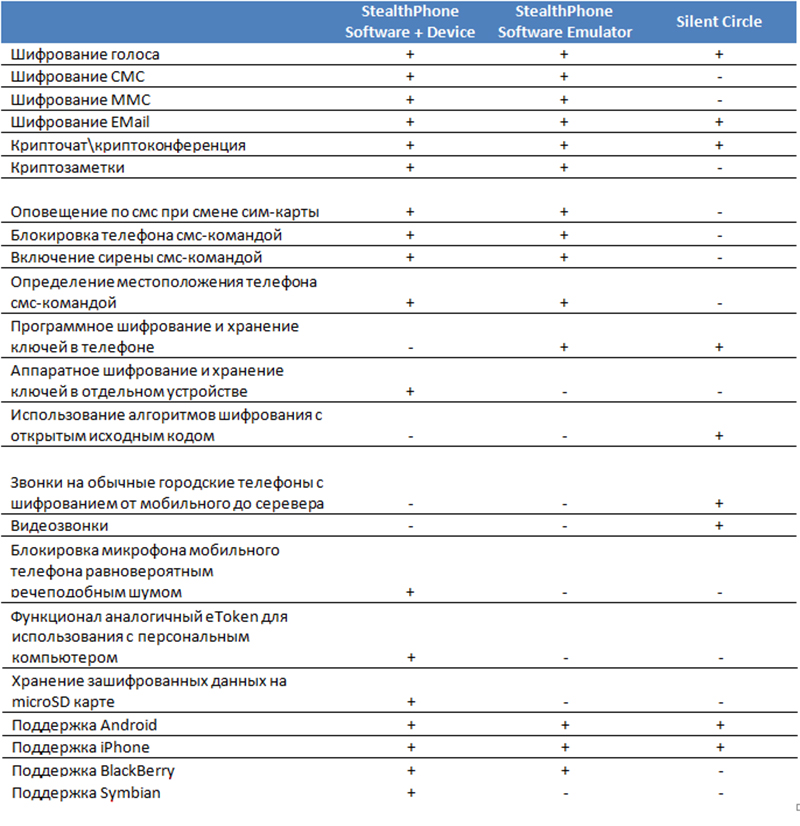
More detailed comparative information is also presented in the table below:
Thus, the Stealthphone Software application, corresponding to the current state of development of information resources and infrastructure, is designed for a wide range of consumers, but first of all, it should interest representatives of those professional communities (political figures , bankers and brokers, journalists, lawyers, managers of commercial firms, etc.) who have to deal with strictly confidential information.
You can familiarize yourself with the demo version of "Stealthphone Software" on Google Play
The use of mobile phones and tablets involves the transfer of various kinds of information in voice, text and graphic form. This may be data containing details of a personal and even intimate nature. But in modern conditions, when using a mobile phone or tablet, there is no clear distinction between the scope of their application, which, in turn, leads to the accumulation in the device’s memory of not only private information, but also used in the work. One of the consequences of this in 60% of cases, according toPonemon Institute , is the seizure of important corporate information by hackers in the event of the loss of a mobile device by an negligent employee, as a result of which the employing company loses its competitive advantage.
We live in an information space whose borders are endless and legally unlimited by anyone. The emerging situation is taken into account by experts all over the world when determining the approach to solving issues of ensuring information security (cyber security).
It’s not for nothing that US President Barack Obama made a statement in August 2012 that “the cyber threat is one of the most serious economic and national security problems”, he determined that “America’s economic prosperity in the 21st century will depend on cyber security ". Therefore, now all US government agencies of federal subordination are engaged in the development and implementation of a unified information security strategy for energy companies, commercial and non-profit organizations working in strategic sectors of the country's economy.
Information security technologies were also an important sector of the largest international exhibitions held in 2012 on information and telecommunication technologies. Of particular interest at these exhibitions was the section on ensuring information security of mobile devices.
Taking into account that by 2014, 80% of all Internet access will be via mobile phones and tablets, foreign companies are actively developing various information protection systems for mobile devices. In most cases, a fully software solution is used that is installed on a mobile phone or tablet in order to reduce costs and provide convenience for the user.
As a result, “avaricious pays twice”: modern hackers using complex virus programs, as well as various attacks via BlueTooth, Wi-Fi and easily bypass such protection. It must also be understood that the technical means used by them for this purpose are comparable in their characteristics with the means that the special services use. For example, for the purpose of cyber thefts, computers are used that can collect several trillion passwords per second. Given that this article is aimed at the mass user, we will not dwell on the consideration of “secure” technologies, as for President Obama, the development of which costs tens of millions and costs tens of thousands of dollars. In our case, this is unacceptable.
The solution to the problem described above was the creation of conditions for the protection of information outside of mobile devices. The company ROHDE & SCHWARZ went this way, but the device developed by it is able to encrypt only voice.
The Stealthphone Software solution, created by Ancort specialists, is software that can be supplemented with hardware to provide the necessary level of protection for the information array.
“Stealthphone Software” is a software application for a mobile phone or tablet running on the operating systems iOS, Android, Symbian and BlackBarry.
This application is intended to protect the information of your mobile phone or tablet during data transfer via voice, SMS, MMS and e-mail. This application, installed on your mobile phone or tablet that supports the function of connecting to the Internet, will ensure the confidentiality of any information transmitted over communication networks 3G, 3,5G, EDGE, Wi-Fi, WiMAX. “Stealthphone Software” works through Ancort’s IP servers, which transmit information transmitted through them in a secure form, which excludes access to data by the operators of such a server and reduces the cost of communication services for subscribers. The quality of voice transmission is comparable to that provided by the latest program for IP-telephony Viber, widely distributed in the West, having 70 million users and being the main competitor of Skype. Viber user capabilities (SIP-client, SMS), being provided for use, in the Stealthphone Software application are supplemented with the possibility of sending encrypted SMS, MMS, e-mail and secure chat.
A number of competitive software solutions are presented on the information security market, which, according to the developers, guarantee the protection of information when working in IP networks.
In particular, Ancort experts conducted a preliminary analysis of the capabilities of the Stealthphone Software application and the SilentCircle solution. As a result, it was concluded that when comparing the two specified software products, the advantages of Stealthphone Software are:
- high quality voice transmission;
- secure information transfer via 3G, 3,5G, EDGE, Wi-Fi, WiMAX communication channels;
- guarantee of confidentiality of data in case of loss of a mobile device;
- Stealthphone Software support for low-speed mobile Internet connections;
- using our own developed encryption algorithm, certified by the governments of Sweden and South Africa;
- the ability to generate encryption keys by the user;
- the ability to supplement the Stealthphone Software application with the Stealthphone Touch hardware encoder, which increases the security of the transmitted information.
More detailed comparative information is also presented in the table below:
Thus, the Stealthphone Software application, corresponding to the current state of development of information resources and infrastructure, is designed for a wide range of consumers, but first of all, it should interest representatives of those professional communities (political figures , bankers and brokers, journalists, lawyers, managers of commercial firms, etc.) who have to deal with strictly confidential information.
You can familiarize yourself with the demo version of "Stealthphone Software" on Google Play
