Sandbox Wars - Part 1
Warning
The article describes the adventures of a friend of mine .
Background
Events take place during the
A freshman neighbor, who, like me, studied at the Naval Forces and was interested in information technology, lived with me in a student dormitory in the same room. For definiteness, in the future I will call him N. I
liked this comrade to engage in small network hooliganism, such as finding someone a simple password for VKontakte and changing the avatar, or writing something vulgar in status. I did not approve of this, but did nothing. In addition to that, he had less theoretical knowledge than was necessary for such actions, so he used mostly ready-made programs, with a poor understanding of how they work - I did not even approve of this.
I myself was not a guru, but at least I tried to study the theory before using "magic" scripts and programs. Well, he directed his activities more into a constructive, rather than destructive, channel.
And I considered myself sufficiently protected from network attacks, since I know the basics of computer literacy, I don’t put my birth date or phone number as passwords, I update the OS and software in a timely manner, I don’t start anything from the Internet.
And then, one day, he sends me an e-mail and he smiles cunningly. And in the letter is the file, and in the file is a tablet with most of my passwords. The most valuable passwords (to mail and domains) were not there, but I still have a butchert, because how is it that I did everything correctly, but this is a failure, and I don’t even know where I have a problem, and what needs to be fixed ! I ask him, he refuses to explain where and how he got them.
The analysis showed that the set of passwords sent to me coincides with the set of passwords stored in Opera Wand, I put the master password on Wand in the opera. I change all the passwords, download the Cure It Live CD, restart the computer, run a full scan. Night passes - no viruses detected. I’m downloading a similar product from Kaspersky Lab - the result is the same. The idea comes that he could use the Live CD to steal wand.dat - the drive is not encrypted with me. N says that I did not guess, but just in case I put the password in the BIOS to boot and change the bootable media. A plan of terrible revenge is born in my head (all the more so since my hands were scratching something like this for a long time, but they held back moral standards - and there seems to be an excuse: “he first started”). I record a Live CD with some kind of mini-Linux, test it on my computer, everything works.
The next day, while N passes the exam, I close myself in the room, load his PC from the CD prepared on the eve of the Live CD. I copy the% AppData% directory to my USB flash drive, also copy the SAM and SYSTEM registry files, turn off the PC.
On my computer, I decrypt the passwords from its Opera Wand, the password for the mail is also there. One of them matches his Windows login password.
Also in the mailbox by searching for the words “password”, “password” I find passwords from services that send the password in clear text to the mail after each change.
I am writing a reply letter with his passwords. After a short time I get disconnected ICQ and Jabber. Having understood that he also has a database of my Miranda, I recover passwords for all used IM protocols, I put a database encryption plug-in for Miranda.
After several hours of negotiations, we agree on the exchange of information on methods of "hacking". It turned out that a few weeks ago, while I was away from the computer, I copied my% APPDATA% to the USB flash drive. And that day I decided to go through this directory with decoder programs. It turned out that while I was thinking over some complicated options, he just took and copied the directory - where is it easier? Since then, my computer has been blocked after two minutes of inactivity, as well as manually, when I do not forget.
This incident had no effect on good neighborly relations, since no one had used other people's passwords for evil purposes, and both only gained extra experience. In addition, we agreed not to use physical access to the neighbor’s computer in the future, because this will not bring any experience, and protecting the PC from physical access is already beyond what we are interested in.
History
A month has passed. And again, I see how N learned the password from the e-mail of his classmate, and, with worthy of the best use of persistence, resets her contact password and writes everything on her behalf on the wall, in messages to friends, etc. She recovers the VKontakte password through the mail, and he changes it back. She does not know the password to change the mail (in this she has no excuse).
And again my hands were combed to do something bad, and here again there is a moral justification - N illiterate the illiterate himself here, so if I get access to his passwords, there will be nothing wrong with that.
Since we agreed not to use physical access to the computer, and also because it would not be interesting to repeat focus from the Live CD, a less trivial way is needed.
Glance falls on a couple of switches and a bunch of wires through which the Internet works in our room.
Modification of network infrastructure
Initially, the network configuration was as follows:
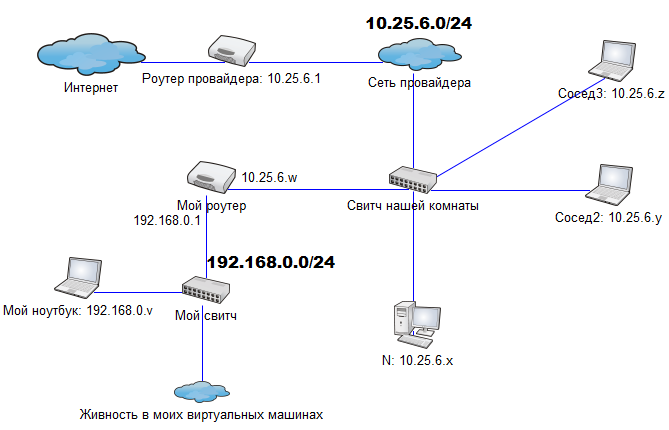
IP addresses are static, N goes to the Internet through a 10.25.6.1 gateway. I am sitting at a separate router for experiments. Thus, I have a network 192.168.0.0/24 to host the necessary machines.
First of all, you need a router that will be used by the victim instead of the provider. Of course, there is no way to single out a separate machine for this, so I do everything in VirtualBox.
The internal IP address for the virtual router will be 10.25.6.1 (since the victim will connect to this address exactly), what to do with the external one? He cannot receive the Internet from the provider router, so then the address ranges of the external and internal networks will coincide. Let the external interface be connected to my private network: 192.168.0.0/24.
As a result: Debian is installed in VirtualBox, the address of the internal interface: 10.25.6.1, external: 192.168.0.u. We configure NAT on it.
Since there is actually only one network adapter on the laptop inside which VirtualBox is running, you have to cheat. In the virtual machine settings, we bridge the two interfaces of the virtual machine with the only interface of the real machine. Thus, two logical networks now coexist in the same hardware segment: 192.168.0.0/24 and fake 10.25.6.0/24. On an ongoing basis, this is not worth doing, but in this case, nothing terrible happened.
We also create another virtual machine that will act as a victim until everything is debugged; we also connect it in the bridge mode to the same internal network.
Now the network looks like this (red arrows show the packet route from the virtual victim to the Internet):
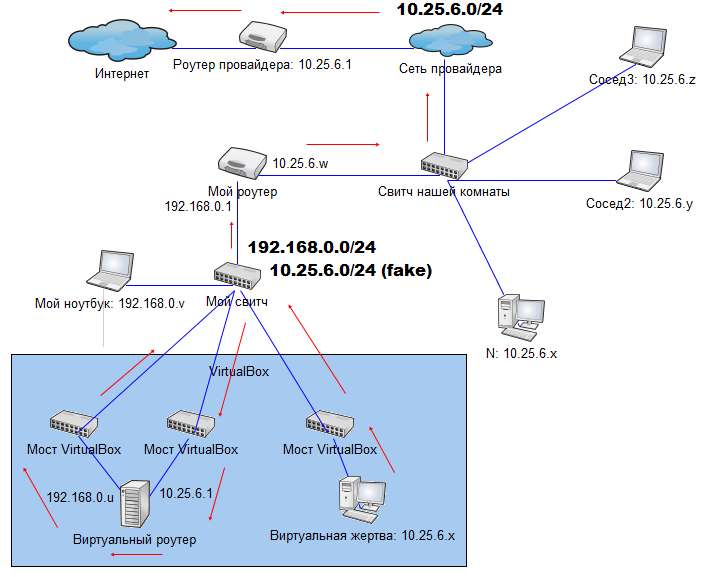
For the real victim, instead of the first two arrows, there will be one arrow directly to the switch - this will happen if you switch the N wire from the room switch to your own, while the victim will notice only short-term disconnect.
One can see many things at once, for which networkers will probably hang me:
- One switch is used in two logical networks, and, as a result, the packet passes through this switch twice. That is, it turns out the path with self-intersection
- The packet, during its path, passes through two different networks 10.25.6.0/24, first through the fake, then through the real
- traceroute from the victim to some server on the Internet will show the address 10.25.6.1 twice, an extremely atypical situation
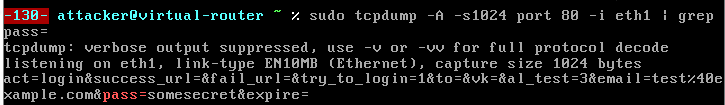
To check, run vkontakte.ru on the victim, on the tcpdump router, and see the following:
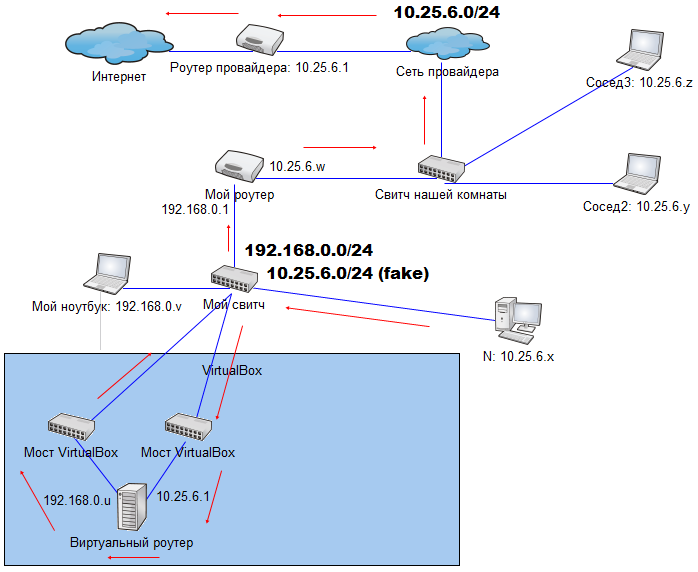
Turning off the victim virtual machine, switch cable N from the main switch to ours, after a few seconds we get VKontakte cookies. Entering cookies into your browser, we end the session (here you could be more careful, but to hell with it!). A few minutes later, the password from VKontakte was received.
The network diagram is in a “combat” state:
But just listening to traffic will not work, most sites transmit passwords using the https protocol, so the maximum that I get is the password from VKontakte, which it will then recover through e-mail, you need something more interesting .
conclusions
- use the password on the BIOS, or data encryption on the hard drive (TrueCrypt)
- short idle lock-up time
- Webmasters: do not transmit important data via http, use encryption. Durov, do you hear?
- Users: Do not use sites that transmit your passwords via http
- Do not be “bad guys”, maybe your neighbor is just waiting for a reason
Continuation
HTTPS Bypass
