Fingerprinting through banner ads? Now this is common
A strange question was asked yesterday at Stack Overflow : why does loading a Stack Overflow page trigger audio content? What kind of sound on a text site?
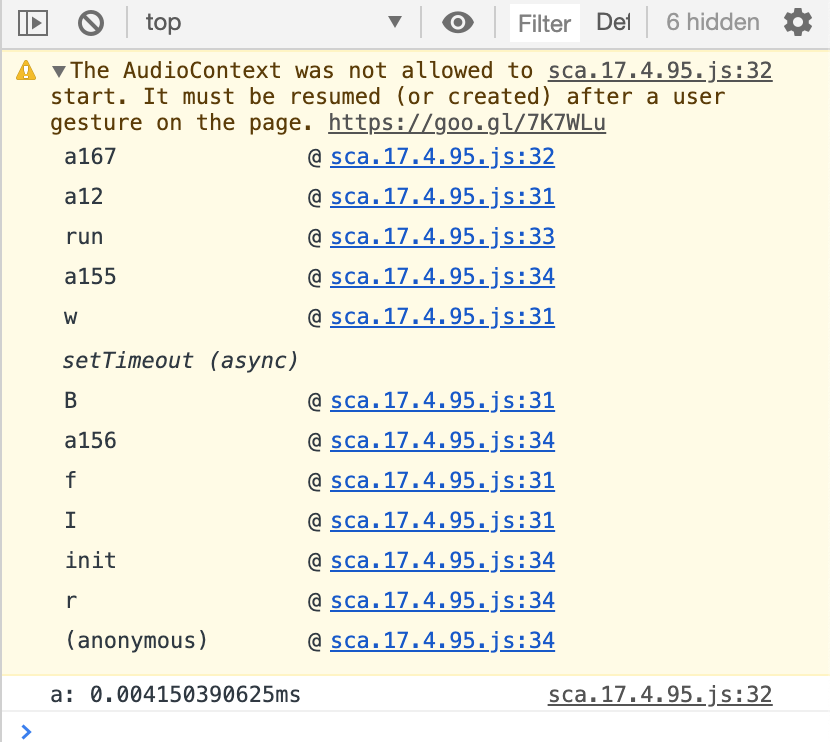
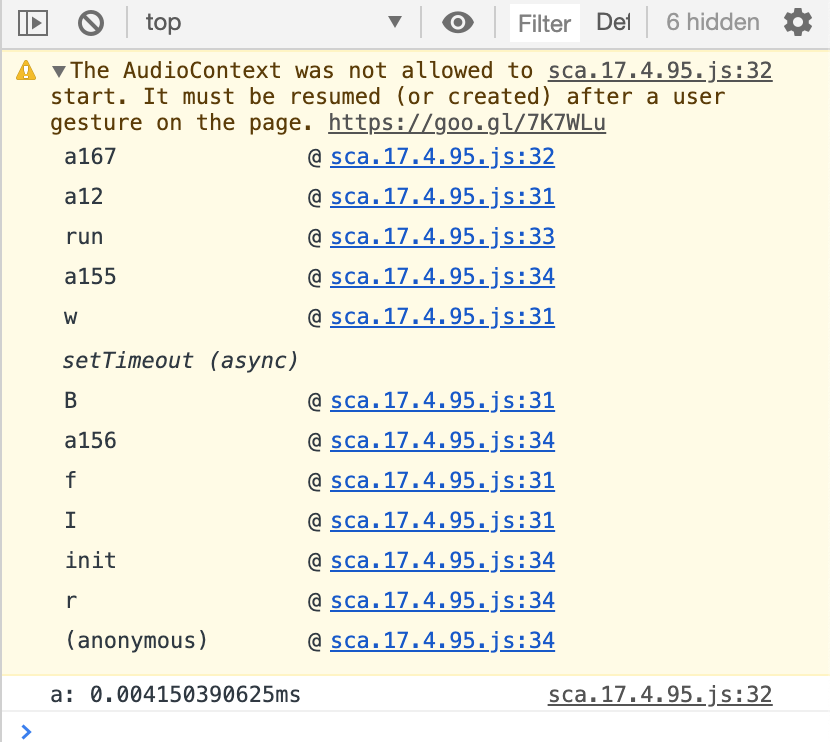
Screenshot from developer tools:
The answer turned out to be more interesting than could be expected.
The author himself carefully examined the traffic and figured out that the requests are related to the script:
... and appear only if there is a certain banner on the page that is delivered through the Google AdSense advertising network.
Readers at first thought it was an April Fool’s joke. But one of the developers did not spare the time and carefully figured out what exactly the above script does.
It turned out a very interesting thing. It turned out that the banner is trying to use the Audio API as one of the hundreds of pieces of data that it collects about the browser, trying to fingerprint it. This is necessary to uniquely identify the browser on various sites, regardless of privacy settings. Although the browser blocks the transfer of data specifically through the Audio API, it does not block most of the rest of the data, so the banner owners successfully fingerprint and possibly deanonymize users.
The discovered functionality is definitely not needed for the banner to work, that is, it is not used to enable or disable some interactive functions. They are used only collectively to create a unique “fingerprint” of the user, which then passes the banner along with the advertising ID when recording analytics for the advertiser.
For example, this fragment defines the display resolution and accessibility parameters in the system:
Checking for specific cryptographic APIs:
Retrieving a list of installed fonts:
Identifying Audio API Features:
Defining specific APIs in mobile browsers:
Verify DRM support for a specific platform.
And hundreds of other parameters, which together make up a unique "portrait" of the browser. It is assigned a unique ID, which is then used to track user activity on the Internet.
It seems that fingerprinting methods have already left the category of “dark practices” and are openly used by major advertisers and ad networks. An ad blocker helps protect against such a system scan.
In such a situation, ad blocking becomes not just a convenient option, but a mandatory requirement for normal work on the Internet. This is a minimal but not sufficient requirement for protection against tracking.
The Electronic Frontier Foundation has long warned about the use of fingerprinting by advertisers. The Panopticlick tool runs on their website, which emulates the actions of a hostile tracker and determines how unique the fingerprint of your browser is.
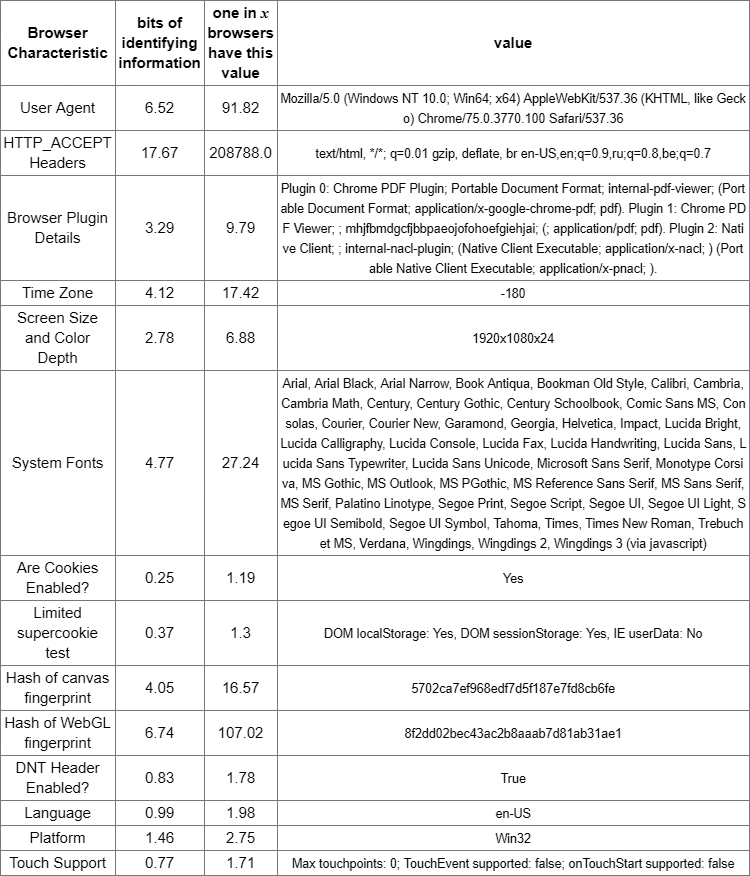
For example, the table at the top corresponds to the actual results of scanning the browser with the identification of 17.67 bits of identifying information. This is a unique print among all 208,788 users who have been tested on the site over the past 45 days.
And this is a desktop browser, and fingerprinting is even easier on a mobile device, because scripts scan data from the phone’s sensors . Such scripts are found on many large sites on the Internet. Scanning sensors helps block bots, and is also used for tracking and analytics.
Stack Overflow representatives saidthat they are aware of the problem. They do not like this situation and they think how to deal with it. But the fact is that banners with tracking can be found on absolutely any site.
SPECIAL CONDITIONS for PKI solutions for enterprises are valid until November 30, 2019 under the promo code AL002HRFR for new customers. For details, contact the managers +7 (499) 678 2210, sales-ru@globalsign.com.
Screenshot from developer tools:
The answer turned out to be more interesting than could be expected.
The author himself carefully examined the traffic and figured out that the requests are related to the script:
https://static.adsafeprotected.com/sca.17.4.95.js... and appear only if there is a certain banner on the page that is delivered through the Google AdSense advertising network.
Readers at first thought it was an April Fool’s joke. But one of the developers did not spare the time and carefully figured out what exactly the above script does.
It turned out a very interesting thing. It turned out that the banner is trying to use the Audio API as one of the hundreds of pieces of data that it collects about the browser, trying to fingerprint it. This is necessary to uniquely identify the browser on various sites, regardless of privacy settings. Although the browser blocks the transfer of data specifically through the Audio API, it does not block most of the rest of the data, so the banner owners successfully fingerprint and possibly deanonymize users.
The discovered functionality is definitely not needed for the banner to work, that is, it is not used to enable or disable some interactive functions. They are used only collectively to create a unique “fingerprint” of the user, which then passes the banner along with the advertising ID when recording analytics for the advertiser.
For example, this fragment defines the display resolution and accessibility parameters in the system:
function "==typeof matchMedia&&a239.a341.a77 ("
all and(min--moz - device - pixel - ratio: 0) and(min - resolution: .001 dpcm)
")},function(){return"
function "==typeof matchMedia&&a239.a341.a77 ("
all and(-moz - images - in -menus: 0) and(min - resolution: .001 dpcm)
")},function(){return"
function "==typeof matchMedia&&a239.a341.a77 ("
screen and(-ms - high - contrast: active) and(-webkit - min - device - pixel - ratio: 0), (-ms - high - contrast: none) and(-webkit - min - device - pixel - ratio: 0)
")},function(){return"
function "==typeof matchMedia&&a239.a341.a77 ("
screen and(-webkit - min - device - pixel - ratio: 0)
")},function(){return"Checking for specific cryptographic APIs:
return "function" == typeof MSCredentials && a239.a341.a66(MSCredentials)
}, function() {
return "function" == typeof MSFIDOSignature && a239.a341.a66(MSFIDOSignature)
}, function() {
return "function" == typeof MSManipulationEvent && a239.a341.a66(MSManipulationEvent)
}, function() {Retrieving a list of installed fonts:
return "object" == typeof document && a239.a341.a68("fonts", document.fonts)Identifying Audio API Features:
return "undefined" != typeof window && "undefined" !== window.StereoPatternNode && a239.a341.a66(window.StereoPannerNode)Defining specific APIs in mobile browsers:
return "function" == typeof AppBannerPromptResult && a239.a341.a66(AppBannerPromptResult)Verify DRM support for a specific platform.
}, function() {
return !!a239.a341.a72() && a239.a341.a66(a239.a341.a72().webkitGenerateKeyRequest) && a239.a341.a66(a239.a341.a72().webkitCancelKeyRequest) && a239.a341.a66(a239.a341.a72().webkitSetMediaKeys) && a239.a341.a66(a239.a341.a72().webkitAddKey)
}, function() {And hundreds of other parameters, which together make up a unique "portrait" of the browser. It is assigned a unique ID, which is then used to track user activity on the Internet.
It seems that fingerprinting methods have already left the category of “dark practices” and are openly used by major advertisers and ad networks. An ad blocker helps protect against such a system scan.
In such a situation, ad blocking becomes not just a convenient option, but a mandatory requirement for normal work on the Internet. This is a minimal but not sufficient requirement for protection against tracking.
The Electronic Frontier Foundation has long warned about the use of fingerprinting by advertisers. The Panopticlick tool runs on their website, which emulates the actions of a hostile tracker and determines how unique the fingerprint of your browser is.
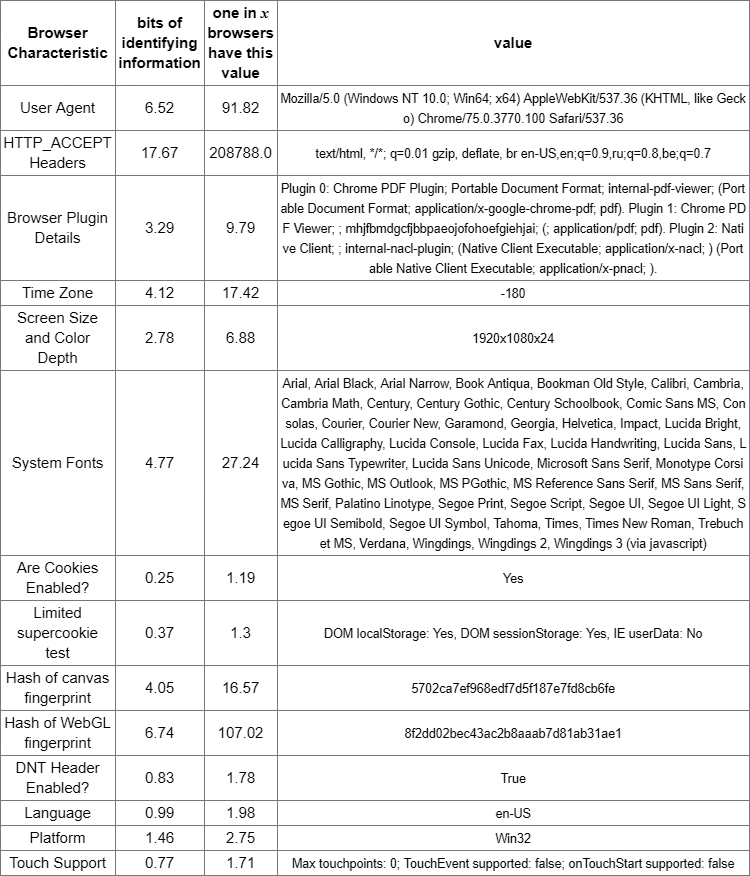
For example, the table at the top corresponds to the actual results of scanning the browser with the identification of 17.67 bits of identifying information. This is a unique print among all 208,788 users who have been tested on the site over the past 45 days.
And this is a desktop browser, and fingerprinting is even easier on a mobile device, because scripts scan data from the phone’s sensors . Such scripts are found on many large sites on the Internet. Scanning sensors helps block bots, and is also used for tracking and analytics.
Stack Overflow representatives saidthat they are aware of the problem. They do not like this situation and they think how to deal with it. But the fact is that banners with tracking can be found on absolutely any site.
SPECIAL CONDITIONS for PKI solutions for enterprises are valid until November 30, 2019 under the promo code AL002HRFR for new customers. For details, contact the managers +7 (499) 678 2210, sales-ru@globalsign.com.
