Klusterkit
- Transfer
KlusterKit: An open source toolkit for simplifying Kubernetes deployments and working in physically isolated local environments
Today, we are pleased to announce that Platform9 opens the source code for Klusterkit, a three-tool kit, under the Apache v2.0 license on GitHub.
Our customers roll out software in private data centers, which are often not connected to the Internet (for security reasons or for other reasons). These large companies want to take advantage of Kubernetes and modernize their applications and at the same time roll them out to different data centers, which often have no connection with the outside world. And here Klusterkit comes to the rescue, which simplifies the delivery and management of K8s clusters in physically isolated environments.
Klusterkit includes three independent tools that can be used together or separately to manage the life cycle of the Kubernetes production cluster:
- etcdadm , CLI for simplified cluster management etcd.
- nodeadm , a node administration CLI that complements kubeadm and deploys the dependencies needed by kubeadm.
- cctl , a cluster lifecycle management tool that accepts the Cluster API from the Kubernetes community and uses nodeadm and etcdadm to easily supply and maintain highly available Kubernetes clusters in local and even physically isolated environments.
Together, these three tools perform the following tasks:
- Easy delivery and management of the high-availability etcd cluster and Kubernetes control panel in physically isolated local environments through the Cluster API.
- Restore the cluster control panel after a failure using the etcd backup.
- Packaging all artifacts needed to deliver Kubernetes in physically isolated environments.
Klusterkit features
- Multiple wizard support (K8s HA cluster).
- Supply and management of secure clusters etcd
- Work in physically isolated environments.
- Support sequential update and rollback.
- Flannel (vxlan) as CNI for the backend; plans to support other CNI.
- Backing up and restoring etcd clusters after losing a quorum.
- Protects the control panel from running out of memory and CPU time.
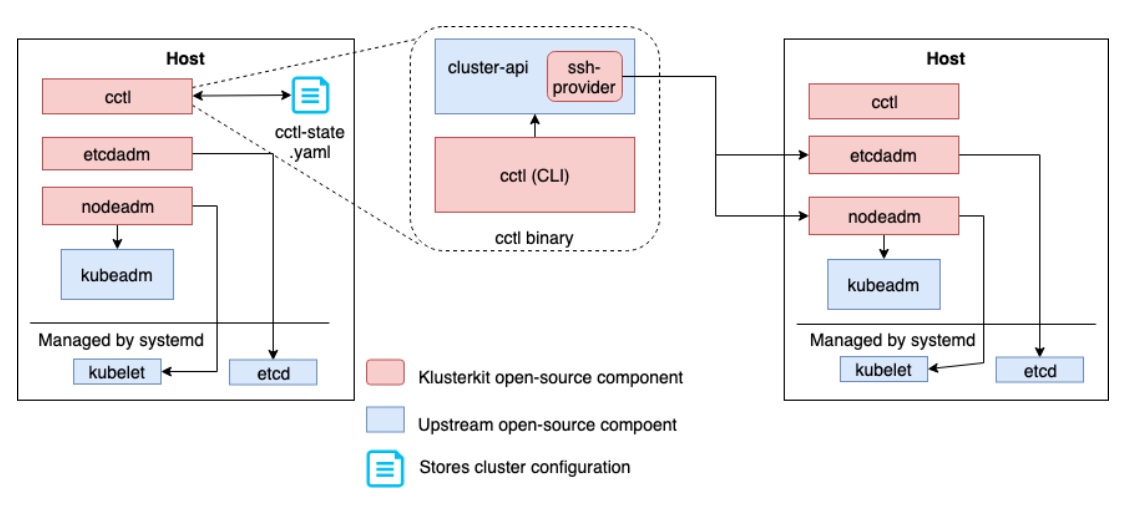
Klusterkit Solution Architecture
For fault tolerance and simplicity, Klusterkit uses a single cctl-state.yaml file to store Kubernetes cluster metadata. Through the cctl CLI, you can manage the life cycle of a Kubernetes cluster on any machine that has this status file. This can be an operator’s laptop or any other computer that is part of a Kubernetes cluster.
Cctl implements and calls from the upstream interface cluster-api as a library of CRUD operations on clusters. It uses ssh-provider , a bare-metal open source cluster-api provider from Platform9, which in turn calls etcdadm and nodeadm to perform operations on the cluster.
How to use Klusterkit and its components:
1 - Any of the three tools can be easily assembled with the go get command:
go get -u github.com/platform9/cctl
go get -u github.com/platform9/nodeadm
go get -u github.com/kubernetes-sigs/etcdadm2 - Then these executable files can be packaged and copied to the target machines where the highly accessible Kubernetes cluster should run. Put the nodeadm and etcdadm files in the version directories:
cp $GOPATH/bin/nodeadm /var/cache/ssh-provider/nodeadm//
cp $GOPATH/bin/etcdadm /var/cache/ssh-provider/etcdadm//3 - If necessary, orchestrate a Kubernetes cluster locally, in a physically isolated environment, the necessary dependencies can be easily downloaded in advance on a computer with access to the Internet using the nodeadm and etcdadm download command. Then the downloaded elements (i.e. kubelet and the kubelet unit file for systemd, CNI executable file, kubeadm file, all container images, including Kubernetes, keepalived image and systemd file, container image etcd and the corresponding configuration files) can be easily copied to physically isolated hosts along with cctl, nodeadm and etcdadm. (See the wiki for details ).
4 - When everything is in place, you can create the first Kubernetes cluster with a couple of commands:
- First create credentials for the cluster.
$GOPATH/bin/cctl create credential --user root --private-key ~/.ssh/id_rsa- Then create a cluster object. –Help lists the supported options.
$GOPATH/bin/cctl create cluster --pod-network 192.168.0.0/16 --service-network 192.169.0.0/24- Finally, create the first machine in the cluster.
$GOPATH/bin/cctl create machine --ip $MACHINE_IP --role masterRead more documentation on GitHub .