DEFCON 21. “The Secret Life of SIM Cards” Conference. Eric Butler, Karl Kosher
- Transfer
My name is Eric Butler, and this is Karl Kosher, and we want to talk with you about reading, creating, downloading and using the code on SIM cards. This project started last year when I found out about the Tourcamp 2012 event, a hacker camp on the Washington state coast, such an exit DEFCON. No hotels, life in tents in the open air, this was the second camp, the first I really liked, I invited friends and we decided to go there. This event was dedicated to launching a GSM network in several areas of the United States, and my task was to get several SIM cards for this.
I did not know anything about what SIM cards are, so I had to study the issue and find out the following:
The last point surprised me because I had never heard before that SIM cards can work with applications. It turns out, a long time ago, when there were no “iPhones” or “androids”, the applications were located on a SIM card. The phone was a simple dialer - you could remove the SIM card from it and rearrange it to another phone along with all your contacts, programs, and so on. Some operators, for example, Telcom, were the owners of SIM cards, controlling the applications installed on them.
After a decade, everything changed radically. Today, the SIM card is a tiny handheld computer that you cannot control. However, many of the principles of the mid-90s have been preserved to this day, and I tried to understand how this all works. I had a great opportunity to play with SIM cards in the camp, and I thought it would be nice to get cards that run applications.
This was not an easy task, because there are many operators who want to sell about 500 thousand of these cards, but we only needed 500 pieces. Most of the operators are forcing us to sign an agreement on the non-disclosure of confidential information of the NDA, which we did not want to do, because we were going to tell everything that we would know when studying such cards.
Some of the cards that we found supported the work of applications, but did not support GSM, and this did not suit us. In addition, there was too little documentation on how to program them. It took us a long time to summarize all the information found, but we learned a lot of interesting things about the technology of programmable SIM cards.
The SIM cards that we finally managed to get had such characteristics.
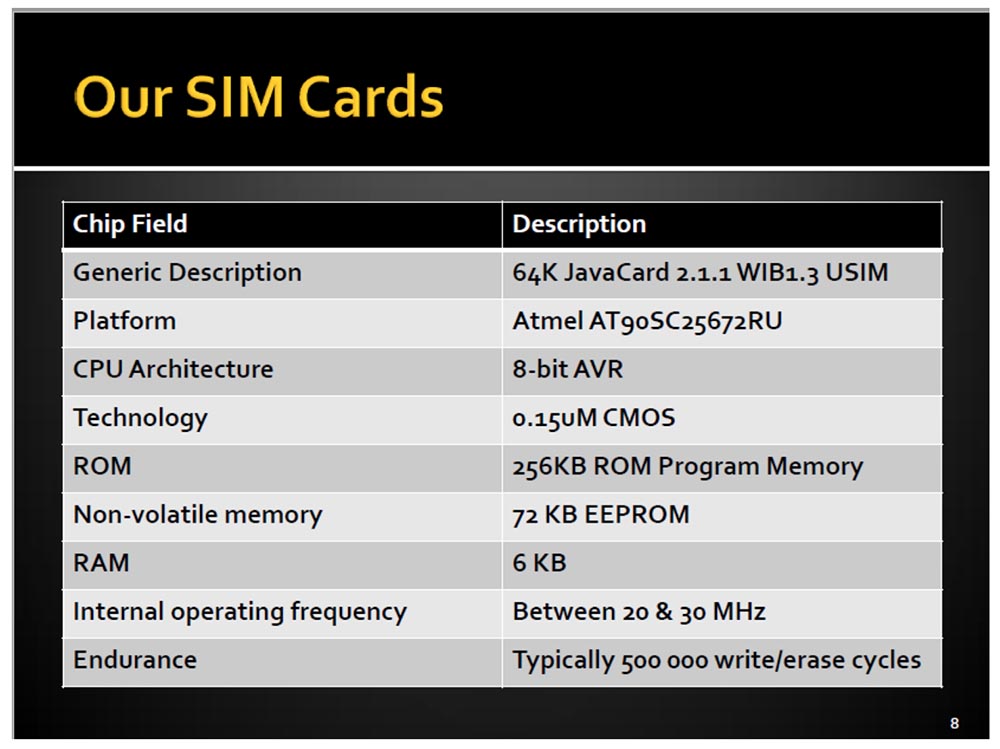
They had their own AVR processor, not the same as the Arduino, with 64 KB of memory and a tiny 6 KB of RAM. They were called JavaCards and ran from 20 to 30 MHz, so these mini-computers had their limitations.
Based on these SIM cards, we came up with our own cellular network for our camp. I wanted people who come to the camp to choose their tent, go through registration and receive a schedule, receive our SIM cards at the entrance for use in a common internal network called Shadytel.
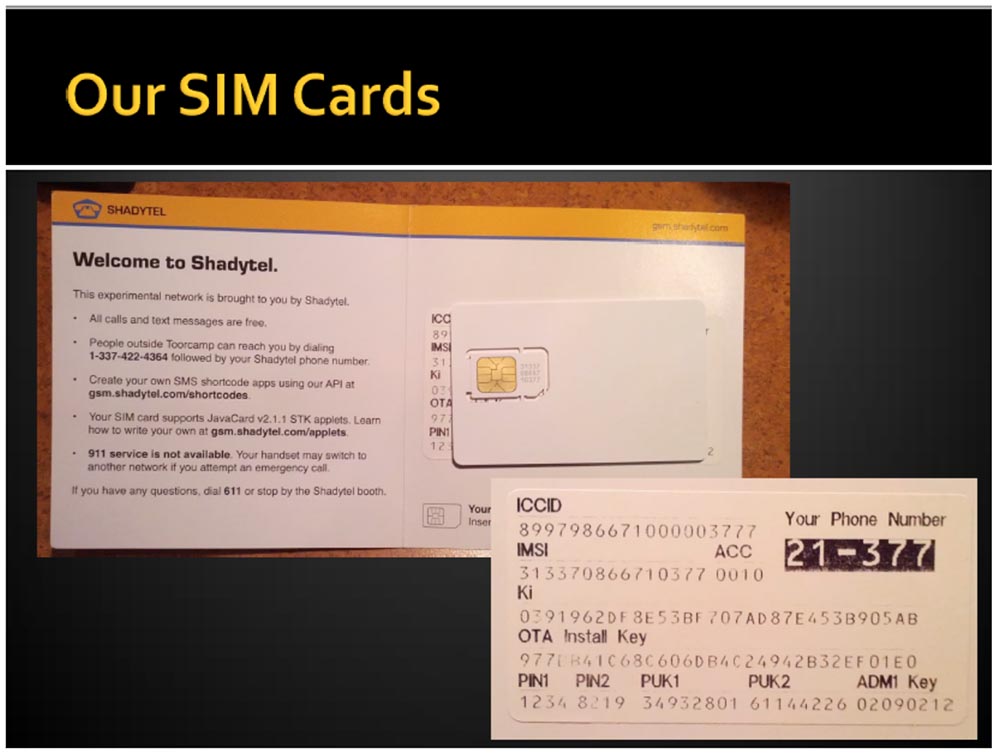
So we gave out more than 400 of our 500 cards, and each received his own mobile number. Our experimental network had the following capabilities:
We handed the guests not only a SIM card, but also all the private information necessary for its use, similar to that which goes to a regular SIM card, as well as open codes, which are usually encrypted on the operator’s cards. In addition, our network provided the opportunity to call anywhere for free, so that you could freely call even your mom to Australia. Our network was very functional and not at all expensive, we even had a license from the Federal Communications Commission (FCC), so our network worked quite legally.
Consider what the applications or applets that we programmed on the SIM cards allowed.
They were run on the processor of the SIM card, regardless of the phone, so that it did not even “see” what was happening, and depending on the operating system used, they directly connected to BaseBand (in the case of the iPhone). Applications could be remotely installed on the card in the "silent installation" mode using the media. What is a "carrier", I will explain a little later. Today, most SIM card carriers support such applications.
Our cards supported the operation of several applications that were selected using AID and controlled by the standard Card Manager card selection application.
In essence, GSM SIM support is simply an application on a physical card with an integrated circuit (UICC).
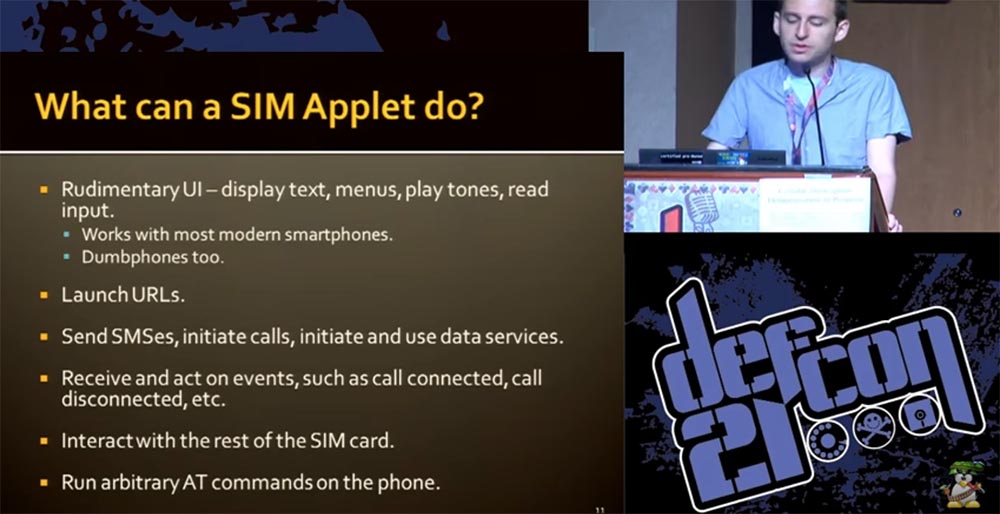
Here is what our applets were able to do:
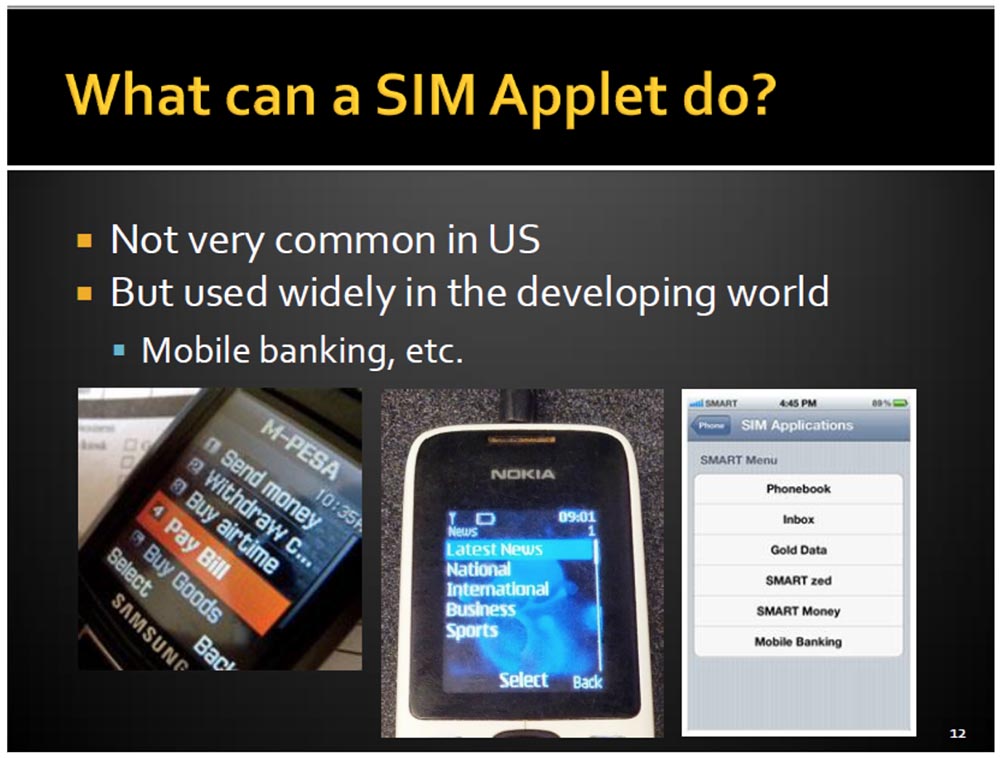
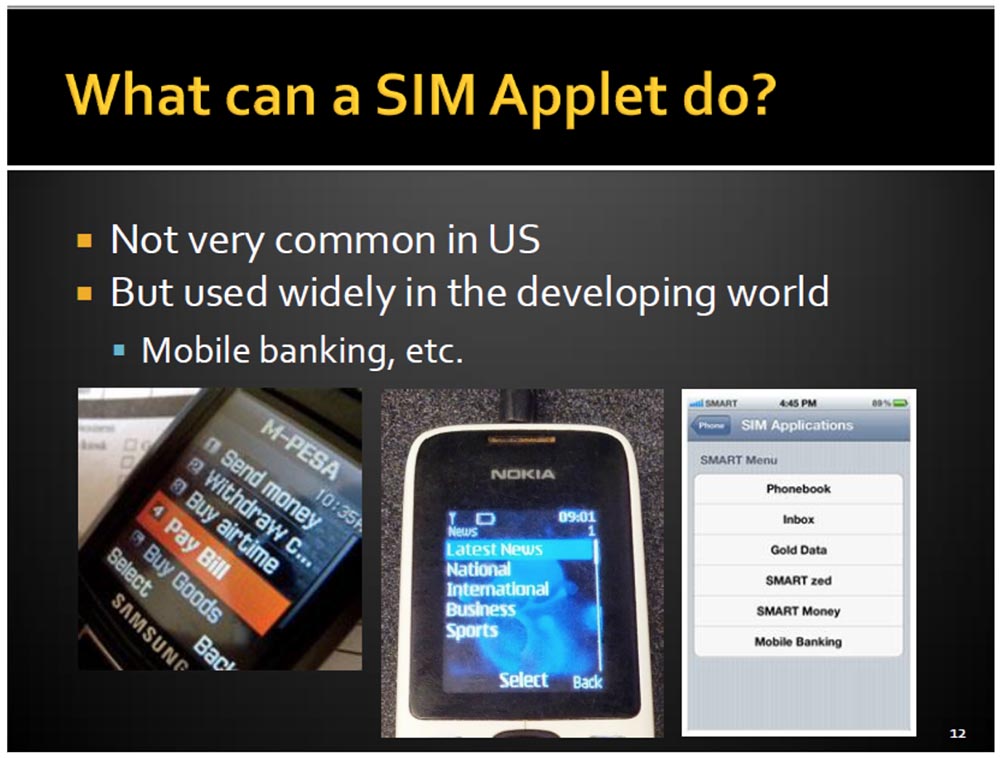
I will show you some examples of how the screen of smartphones looks when using our cards. Here are the features of mobile banking, not particularly common in the United States, but widely used throughout the world.
And now Karl will tell you how our applications work.

We used the following technologies:
The design of the smart card is designed to ensure the safety of data storage and processing, and communication is carried out using packages called APDUs.
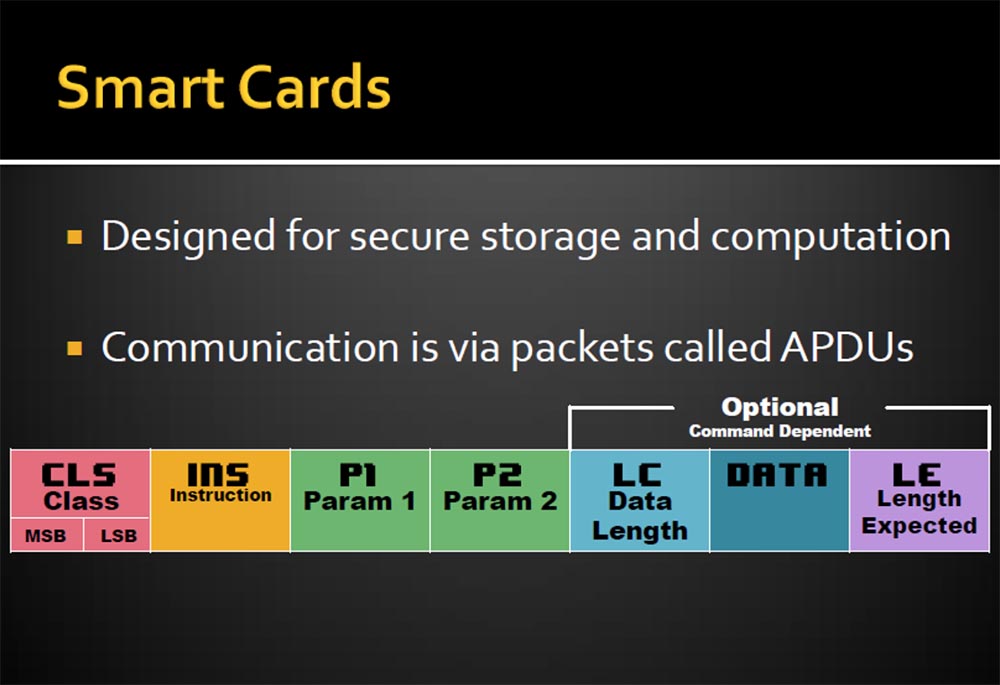
A feature of smart cards is the non-removability of keys and the encryption-decryption procedure, so you can use such personal data as passwords and logins to access the banking system, digital signatures, and access to satellite television. The CLS parameter is responsible for this. The following are instructions for processing INS information. APDUs are a stream of bytes that are described by parameters P1 and P2, and additional records, such as the length of the LC data transmission, the data itself, and the extension of the length of the LE.
On the next slide, you see JavaCard. This is Java and at the same time not entirely Java, because there is no garbage, no letters, strings, multidimensional arrays. If you are lucky, you can find several integer int data types. The structure of these cards is extremely simple. It goes without saying that there are no standard APIs, such as files or themes, you can get rid of verification, but there are some exceptions. Samples and classes of variables are stored in EEPROM memory, which has a limited number of write cycles, approximately 500 thousand. Therefore, depending on the type of map, you may have problems updating these variables.
I will tell you how we created our smart card applications. There are several specialized commercial IDE development environments, but you can do without them, because firstly, we wanted to make our applications as open as possible for everyone, and secondly, these commercial tools cost about $ 3000.
From Oracle, we downloaded the free Java Card Development Kit editor. If you use Eclipse, you must remove the standard JRE library system (Java Runtime) from the card and add the Java Card library to help describe classes and the like. In addition, we ourselves have written several programs to facilitate the work.
The STK application operates as follows:
Thus, after downloading the phone, the application can use all 200 available functions, selecting an application from the menu triggers the corresponding event, after which the application sends UI requests back to the phone.
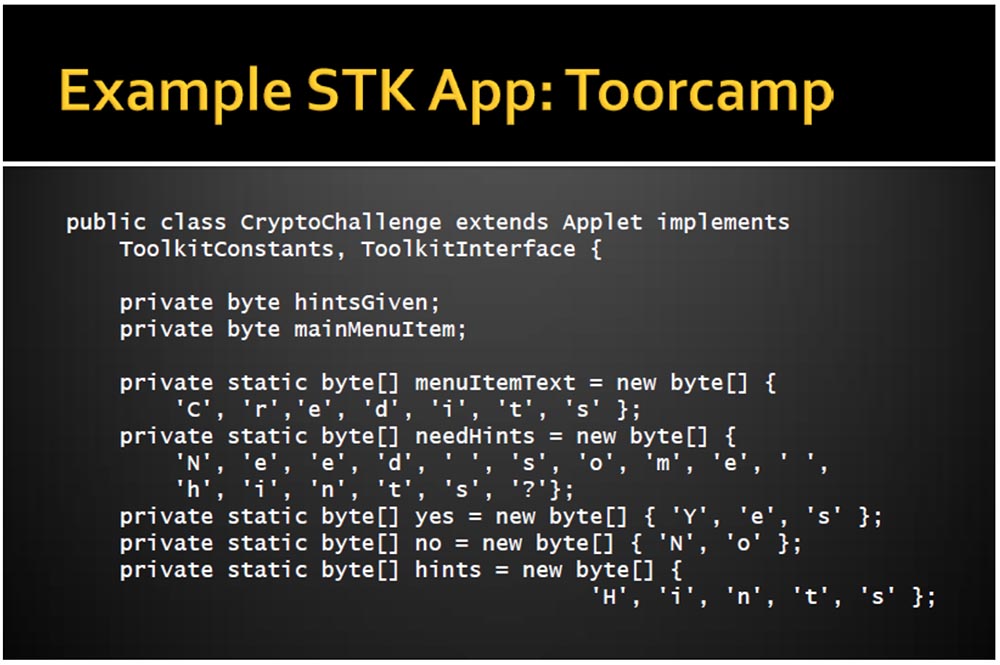
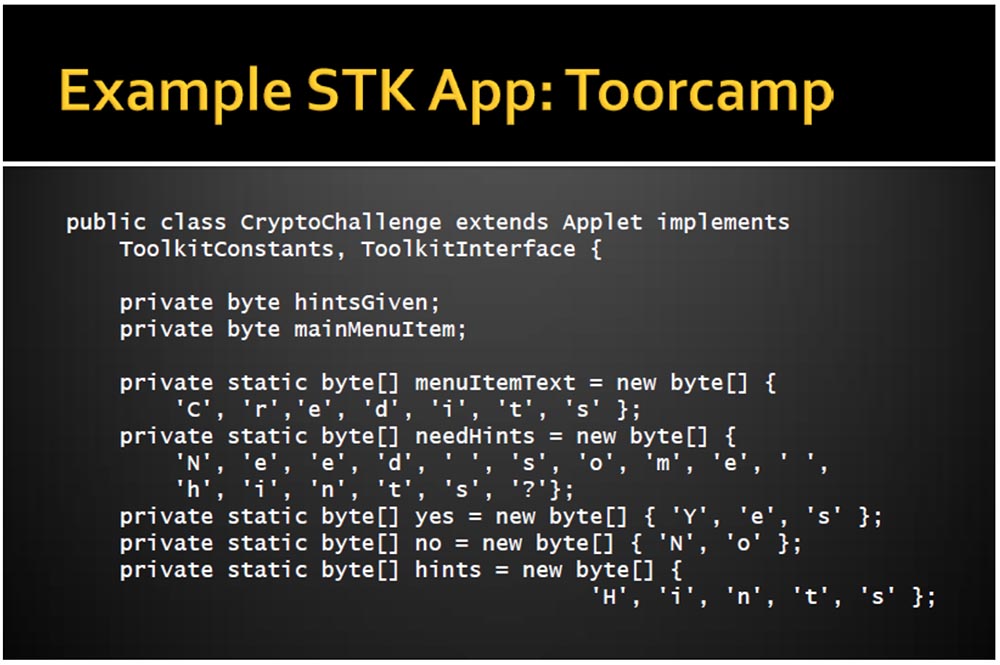
This is what our code looks like.

Java allows you to set a card class using two standard methods: creating and registering a class using the Java Runtime and installing the class using the SIM toolkit. The latter method is used when some event needs to be transferred to the card from the phone.
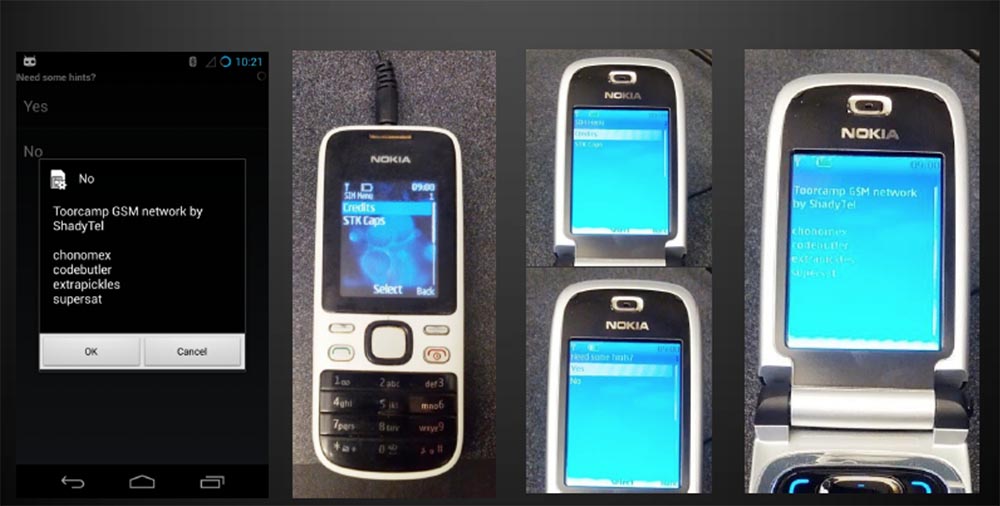
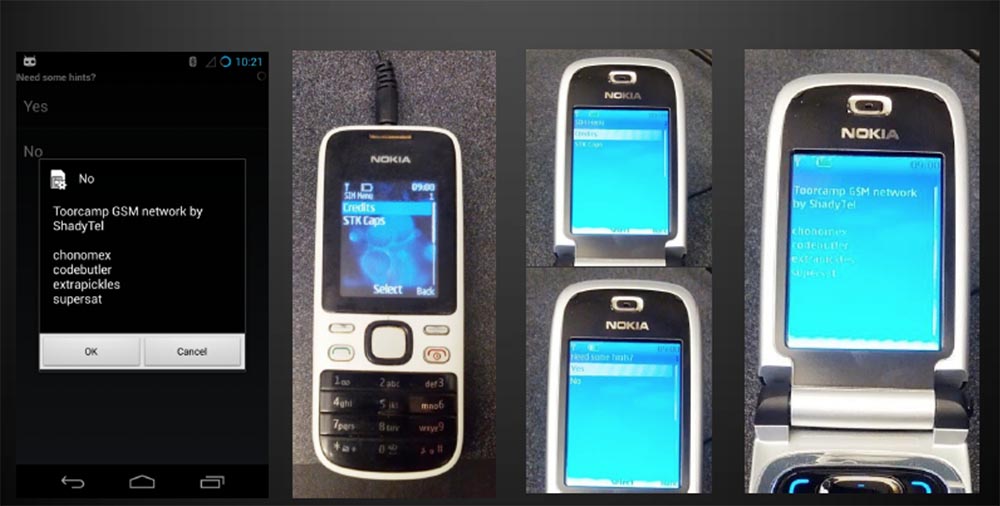
The next slide shows what the app we created for Tourcamp looks like. By activating the card, you can select one of the available networks. When you restart and connect to our network, you will be asked if you want to enable encryption, and this is another interesting feature of our application. It allows you to save prompts on a protected device so that they cannot be removed from there. In addition, we have introduced markers of unwanted interference, which allow you to find out whether these hints were viewed by someone, and allow you to view content remotely, which I will discuss later.
I warn you that the program code of our application looks pretty ugly. If you remember, there are no lines or groups here, so we are forced to create arrays of individual bytes with individual letters. This is a rather painful process, but we withstood it.
Next, we programmatically described the procedure for self-registration of the application using the SIM Toolkit, the process of selecting a program in the phone menu, displaying prompts on the screen and other functionality. We tried to prescribe everything to the maximum as we could, it looks awful, but it works. A full description of the program is given on our website, so you do not need to memorize what is shown on these slides. Now our report will continue Eric.

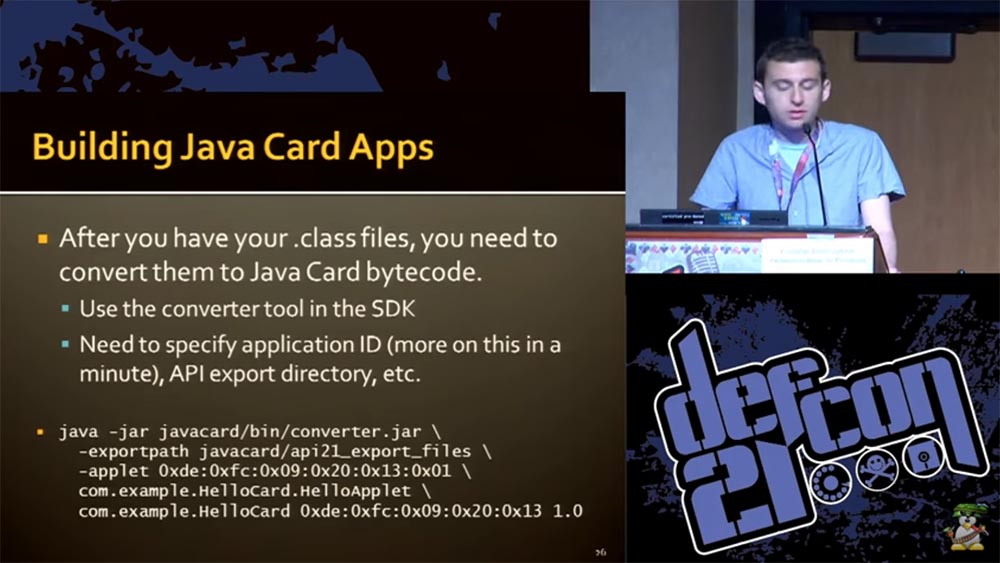
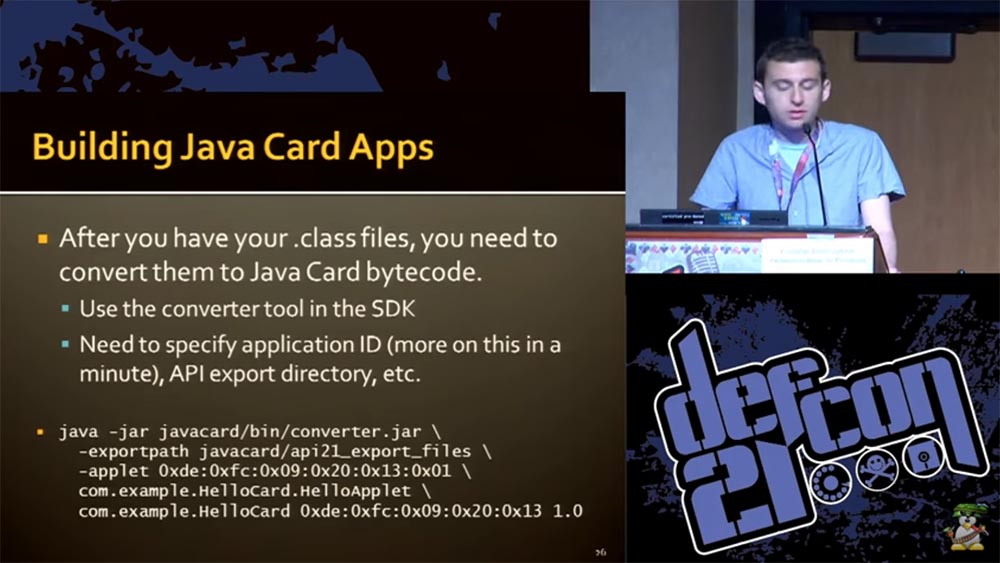
The easiest way is to use the old version of Java 1.1 encoding and the code compatibility version 1.3. After you have created the class files, you must transcode them for the Java Card. To do this, use the converter available in our SDK. You will also need some ID applications (most literally for one minute), an API export directory, and so on. These files must be understandable by the phone OS, so they are made in .jar format.
We also developed a special Makefiles program, which is available on the site . The converter produces a CAP file, which is a Zip archive of CAP components (Java Card code).
One of the important questions that had to be answered before starting work on the project was the question of how to interact with a SIM card. We needed a card reader. They are of two types: for connection to the PCSC port (PC / Smart Card API) and connected to the serial port Serial. The first ones are usually universal, so you need to have an adapter for working with a standard size SIM card, and the second ones are much smaller and are used specifically for SIM cards.
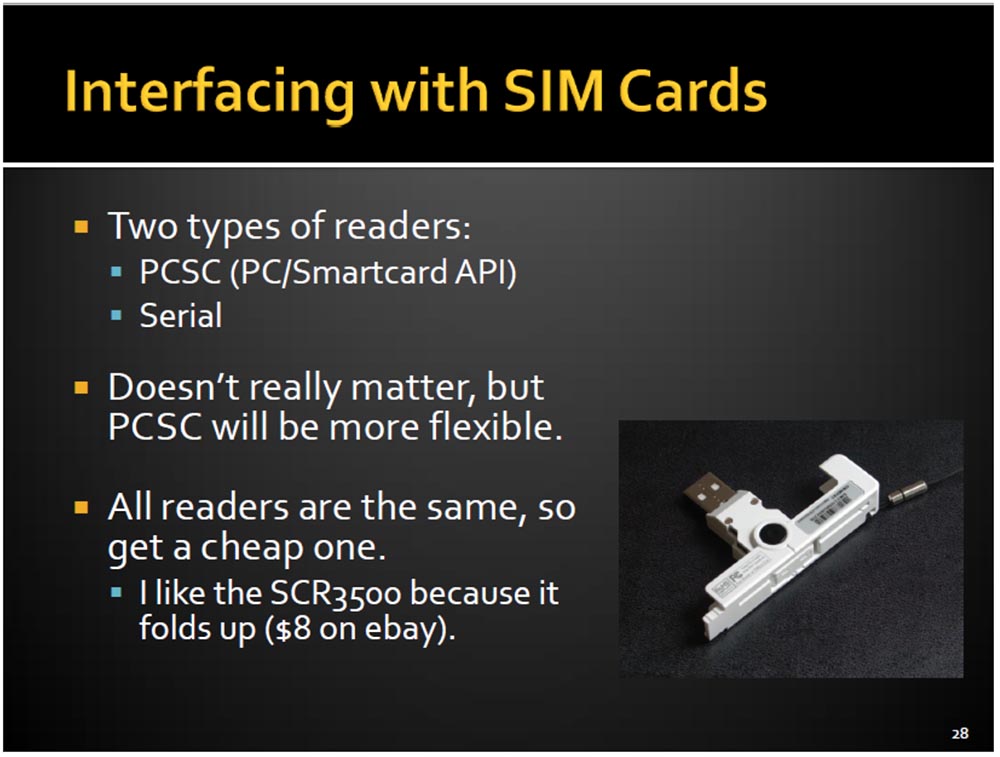
Functionally, there is no difference, but the PCSC option is more convenient to use. It uses official software designed specifically for the API and makes working with a computer easier. In addition, there are many open applications for working with SIM cards, which are easier to use with the PCSC option. All card readers are the same, so I used the cheapest SCR3500, bought on eBay for $ 8.
So, we wrote this awful looking code, then processed it with a Java compiler and converted it into a CAP file. Next, we tried to place it on a SIM card, for which we used the popular GPShell Tool, but we did not succeed. The seller of SIM cards advised us of another program with a simple and convenient interface that could not be found anywhere, and then promised to sell it for $ 600, although he did not have this program either.
Therefore, we used a program called SIM Alliance Loader, the slide below shows its window. We used the first version of this program, but now the second version is already available. SIM Alliance is a group that develops software for working with SIM cards. SIM Alliance Loader is an adaptation of Java applications for Windows and is designed for experts who understand what they are doing.

But if you understand the matter, transferring the application to the SIM card will take just a couple of minutes. However, given that we had about a thousand cards that we wanted to prepare for Tourcamp, such a recording technology would take too much time, so we decided to use something more productive. Therefore, we turned to Global Platform, the standard for downloading, installing, and managing Java Card applications. Depending on the application, this software allows the use of protocols and commands, as well as encryption and authentication. It also allows you to perform some external procedures without the participation of a SIM card, for example, verify the binary codes of our applets.
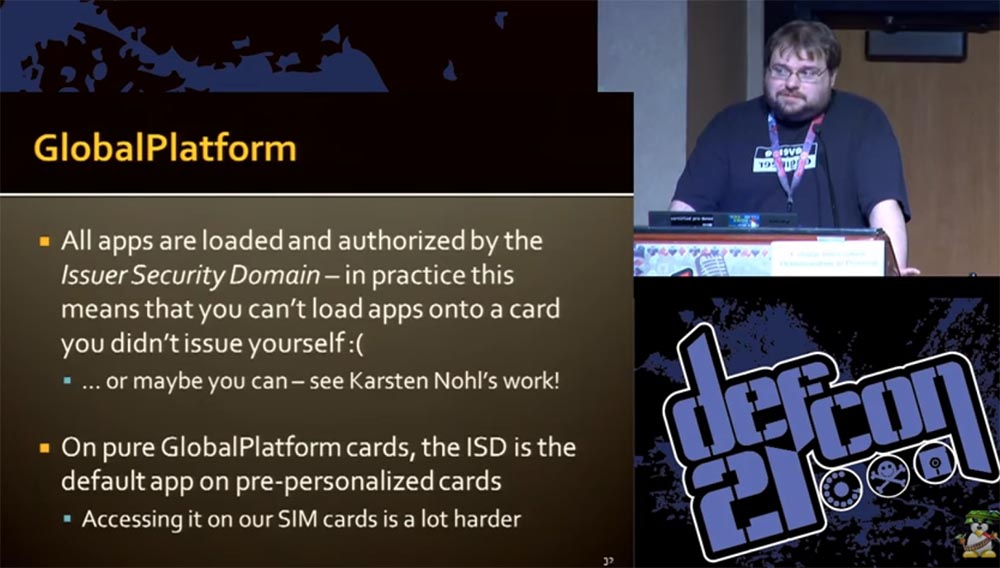
In the process, it turned out that all applications are downloaded and authenticated in the Issuer Security Domain (ISD) application, the Global Platform authentication system. In practice, this means that you cannot download the application to the map if you have not developed it yourself, but there are exceptions described in the work of Carsten Knowle.
On clean Global Platform SIM cards, the ISD application is available by default, access to it is much more difficult for our cards, because the GSM application is installed on them by default and there is not even an opportunity to access the Global Platform application. I will briefly describe the procedure for installing our application on a SIM card.
The process consists of two stages: the DOWNLOAD command (loading an array of binary codes) and the INSTALL command (creating an instance of the application on the SIM card). Single CAP components are combined together and sent to the card in blocks using the DOWNLOAD command. There are three types of Application IDs (AIDs) involved in this process:
As a result, the CAP file is unzipped, data is extracted and written to the SIM card. The only way to “communicate” the Global Platform application with our SIM card is through the air, ie via SMS messages. In fact, we did not send traditional SMS, but simply generated commands on the map using SMS packets.
It was a long and rather laborious process. For the GSM 03.48 standard, it consisted of using the CAT shell (AoC2), which allows us to perform the necessary actions with the card. At the first stage of the process, it includes the SMS PP (D1) download, which, in turn, consists of the device identification and the SMS TPDU transport protocol data packet.

SMS TPDU includes header and user data. User data also includes a header, a command package, a subtitle (security settings, application selection). He, in turn, uses a TAR ID of 3 bytes (I wonder how PowerPoint withstood such nonsense). On this, the limit of internal data is exhausted, and at the very end of the list there is the very APDU that our Global Platform so needs. Thus, all this bulky mechanism serves to transfer a tiny array of data.
In case you do not want to do this, there is another mechanism for remotely sending APDUs to a SIM card. It requires the use of cellular communication to send SMS with installation commands, which requires authentication on the network. However, Karsten Knowle describes a method where encryption errors allow brute-force keys to obtain keys of a symmetric DES encryption algorithm, that is, without network authentication.
The Shadysim boot script is written in Python and runs on OSX, Linux, and Windows. The next slide shows how it looks. Downloading is done using a PC to which a card reader with a SIM card is connected.

The next slide shows the parameters that must be set to install the application on the card.
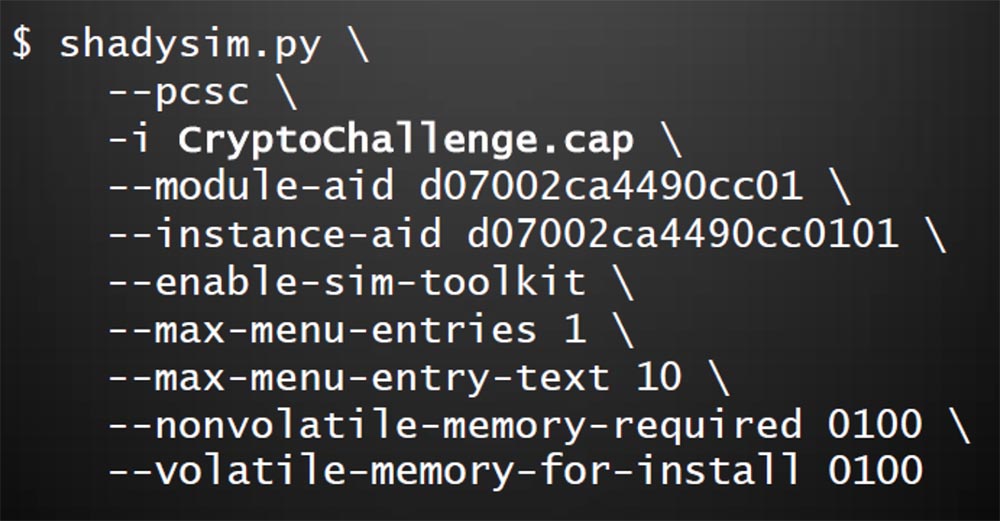
Here the main class of the map is set, the physical and RAM memory is reserved, the size of the text menu that will be displayed on the smartphone screen is determined, the command for launching the Toolkit is recorded, and so on. You can enter any other parameters using the hex code. Finally, a list of applications is introduced with the - t parameter, which allows you to update the phone book.
How do we know that our application is working? Eric will tell you about this.
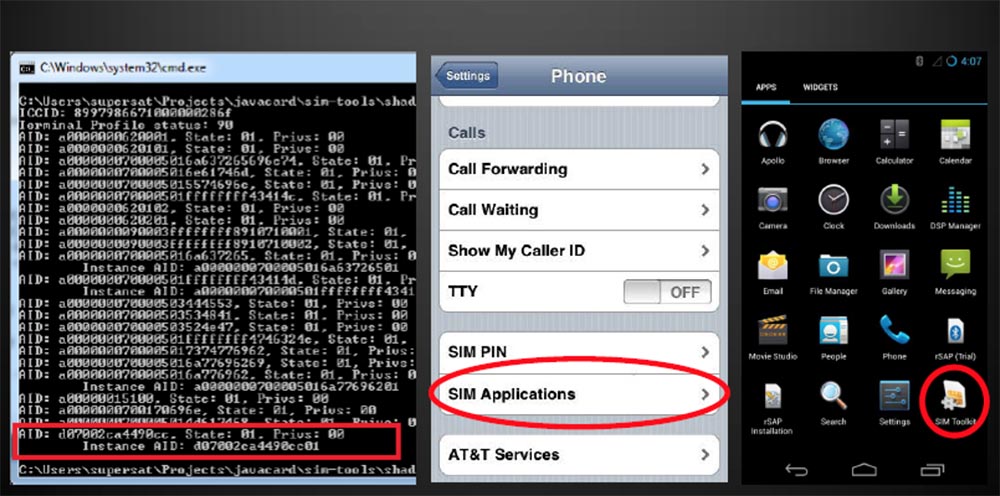
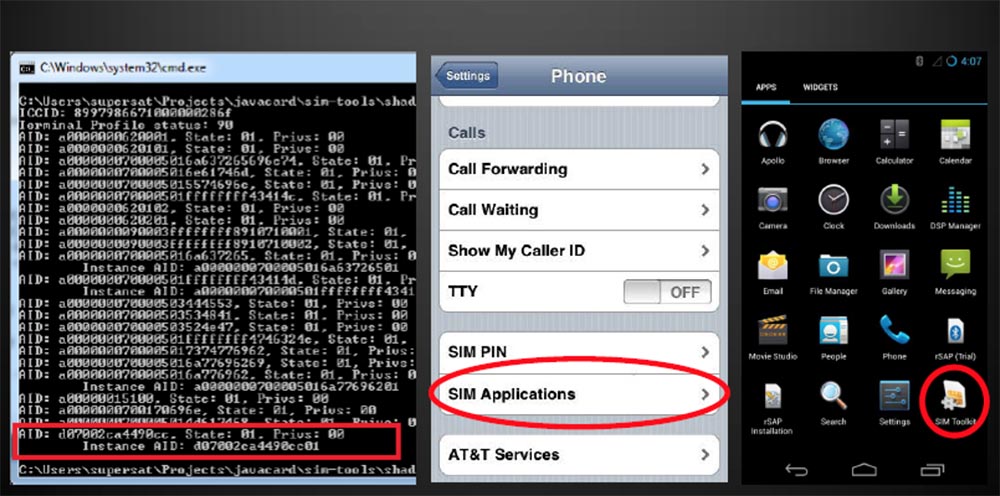
The next slide shows what a working application looks like. On the left is a screen shot showing the operation of the program in Python, in the middle is the iPhone settings menu with the SIM Applications item and the icon of our program on the Applications tab for smartphones running Android.
Karl told you how hard programming was, but testing was not a bit easier. In order to check whether our program works, it was necessary to do the following:
If the code does not work, the whole procedure must be repeated. How can this procedure be accelerated and facilitated?
To do this, you can use the Android emulator for SIM cards. There is an open source SEEK, which is an SDK for Android. It includes patches for accessing a SIM card or SD card via a USB PCSC card reader and prevents SIM card incompatibility conflict when connected to a computer and phone. You run the Android emulator on your computer and test your card without using a smartphone.
Can I use a smartphone as a card reader? Karl will answer this question.
The fact is that most radio interfaces do not allow direct communication with a SIM card. You can solve this problem using the Remote SIM Access Protocol. This method exists in Europe under the name "remote access to the SIM card via Bluetooth." This is a profile with built-in authentication. He needs to write an application that can send and receive APDUs. However, this method in some cases is able to turn your smartphone into a "brick", so you should not install this profile on all smartphones in a row.
I want to introduce you to the future directions of our developments. The STK is a great tool, but it has limitations in use. This begs the question, is it possible to create an SMS botnet? After all, SIM cards are designed for communication through a cellular network and do not need operating systems for the exchange of information, so there is the opportunity to combine them into a common network.
The integration of Android applications with SIM card applets also opens up great opportunities, for example, storing secure SSH private keys for authorization on a SIM card and secure operations with electronic currency BitCoin. We have an idea to use Android applications for OTA technology - “updating programs by air”, using SMS packages for this.
Another area is the improvement of NFS functions, Eric will tell you about it.
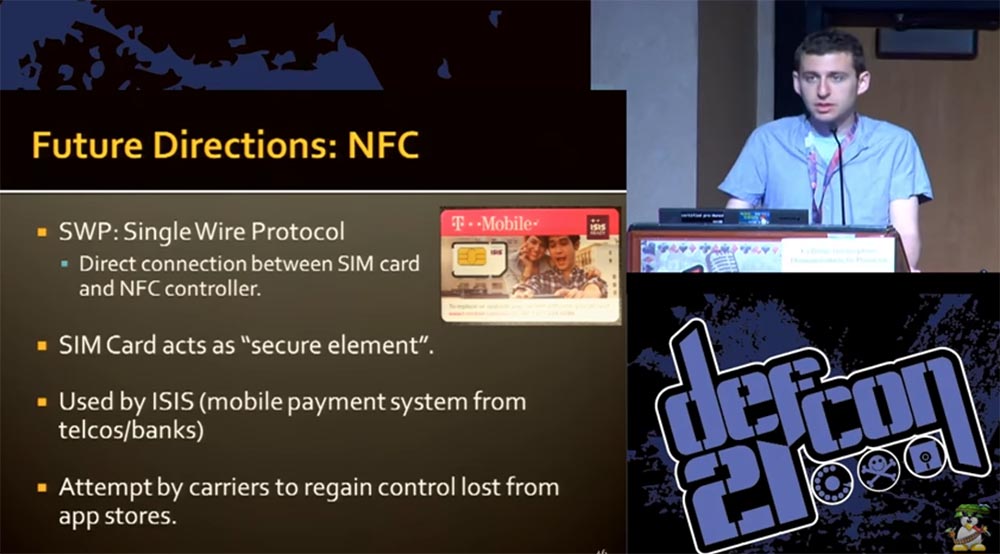
For example, using the single-wire SWP protocol, it will be possible to establish a direct connection between a SIM card and an NFS controller. This means that your SIM card can work without the help of the phone’s operating system directly, just like VISA or MasterCard bank cards work.
The SIM card can work as a security element or be used in ISIS mobile payment systems. This is an American system that is being introduced very slowly, it combines mobile banking and Telcos mobile communications, and our idea may be useful to them.
A SIM card can also serve to restore lost control over a mobile app store. Using SIM cards as an element of security is possible due to the following properties:
Therefore, I think that manufacturers of SIM cards should think about their potential capabilities and develop their functions in the areas we have described.
If you wish, you can download our application on the site , for its operation you will need certain devices worth no more than $ 20, for example, a card reader. There you can find slides of this presentation, scripts for applets, Makefiles for Java Card, patches for Android emulator and many more useful things.
Thank you for staying with us. Do you like our articles? Want to see more interesting materials? Support us by placing an order or recommending it to your friends, a 30% discount for Habr users on a unique analogue of entry-level servers that we invented for you: The whole truth about VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps from $ 20 or how to divide the server? (options are available with RAID1 and RAID10, up to 24 cores and up to 40GB DDR4).
Dell R730xd 2 times cheaper? Only we have 2 x Intel Dodeca-Core Xeon E5-2650v4 128GB DDR4 6x480GB SSD 1Gbps 100 TV from $ 249 in the Netherlands and the USA! Read about How to Build Infrastructure Bldg. class using Dell R730xd E5-2650 v4 servers costing 9,000 euros for a penny?
I did not know anything about what SIM cards are, so I had to study the issue and find out the following:
- SIM, or Subscriber Identification Module, is a mobile subscriber identity module;
- on the SIM card there is an IMSI identification key and a symmetric key Ki;
- it has a built-in security module that allows you to neither extract nor clone keys;
- they are used by GSM operators, and currently LTE (Verizon 4G network);
- may also launch applications.
The last point surprised me because I had never heard before that SIM cards can work with applications. It turns out, a long time ago, when there were no “iPhones” or “androids”, the applications were located on a SIM card. The phone was a simple dialer - you could remove the SIM card from it and rearrange it to another phone along with all your contacts, programs, and so on. Some operators, for example, Telcom, were the owners of SIM cards, controlling the applications installed on them.
After a decade, everything changed radically. Today, the SIM card is a tiny handheld computer that you cannot control. However, many of the principles of the mid-90s have been preserved to this day, and I tried to understand how this all works. I had a great opportunity to play with SIM cards in the camp, and I thought it would be nice to get cards that run applications.
This was not an easy task, because there are many operators who want to sell about 500 thousand of these cards, but we only needed 500 pieces. Most of the operators are forcing us to sign an agreement on the non-disclosure of confidential information of the NDA, which we did not want to do, because we were going to tell everything that we would know when studying such cards.
Some of the cards that we found supported the work of applications, but did not support GSM, and this did not suit us. In addition, there was too little documentation on how to program them. It took us a long time to summarize all the information found, but we learned a lot of interesting things about the technology of programmable SIM cards.
The SIM cards that we finally managed to get had such characteristics.
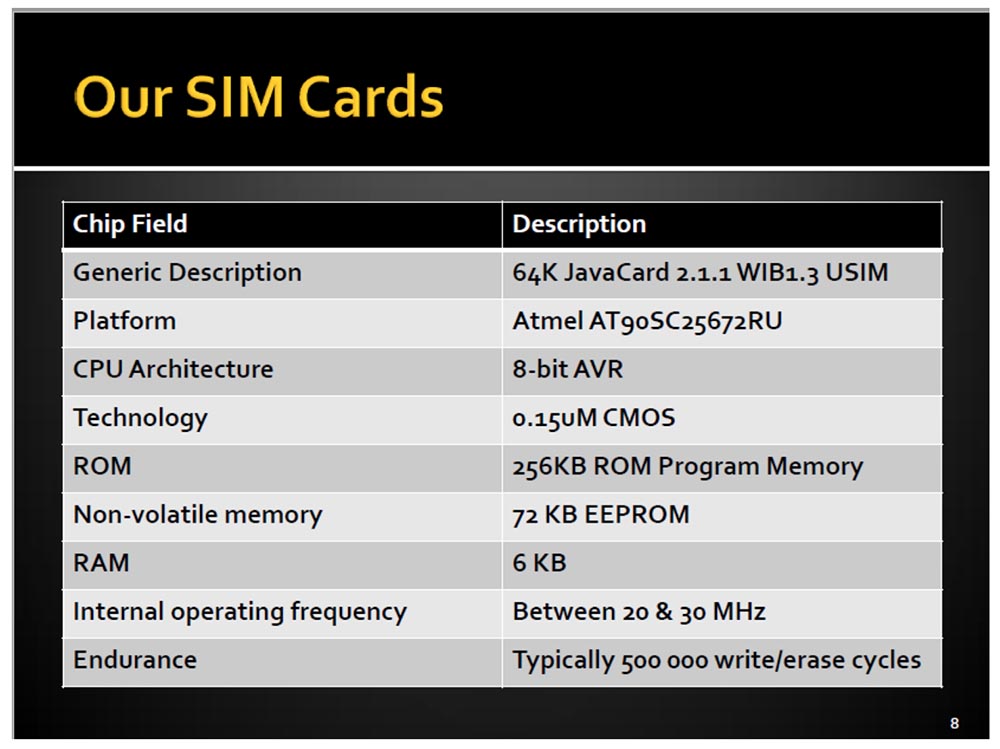
They had their own AVR processor, not the same as the Arduino, with 64 KB of memory and a tiny 6 KB of RAM. They were called JavaCards and ran from 20 to 30 MHz, so these mini-computers had their limitations.
Based on these SIM cards, we came up with our own cellular network for our camp. I wanted people who come to the camp to choose their tent, go through registration and receive a schedule, receive our SIM cards at the entrance for use in a common internal network called Shadytel.
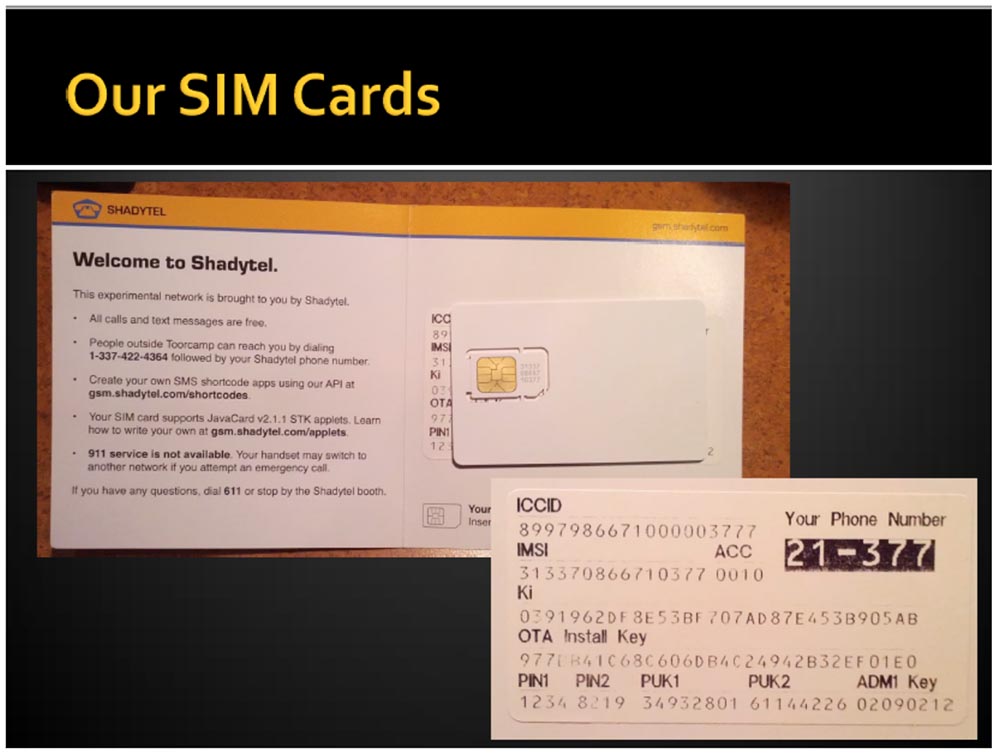
So we gave out more than 400 of our 500 cards, and each received his own mobile number. Our experimental network had the following capabilities:
- all calls and text messages were free;
- people outside the camp could call you on their mobile phone using the prefix 1-337-422-4364 in front of your number;
- You could create your own SMS encoder using our API located on the site ;
- SIM card supported JavaCard v.2.1.1 software. and STK applets, and you could learn about creating your own applets on the same site;
- To call the 911 service, it was necessary to use a different network, since our Shadytel did not support such a call.
We handed the guests not only a SIM card, but also all the private information necessary for its use, similar to that which goes to a regular SIM card, as well as open codes, which are usually encrypted on the operator’s cards. In addition, our network provided the opportunity to call anywhere for free, so that you could freely call even your mom to Australia. Our network was very functional and not at all expensive, we even had a license from the Federal Communications Commission (FCC), so our network worked quite legally.
Consider what the applications or applets that we programmed on the SIM cards allowed.
They were run on the processor of the SIM card, regardless of the phone, so that it did not even “see” what was happening, and depending on the operating system used, they directly connected to BaseBand (in the case of the iPhone). Applications could be remotely installed on the card in the "silent installation" mode using the media. What is a "carrier", I will explain a little later. Today, most SIM card carriers support such applications.
Our cards supported the operation of several applications that were selected using AID and controlled by the standard Card Manager card selection application.
In essence, GSM SIM support is simply an application on a physical card with an integrated circuit (UICC).
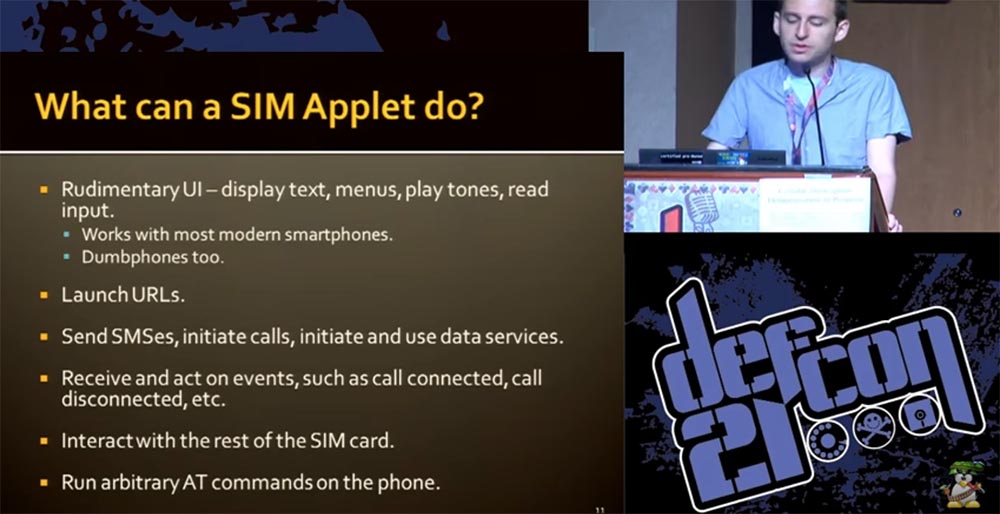
Here is what our applets were able to do:
- perform the usual functions of cell phones using the OS software interface - show text, menus, play ringtones, read incoming messages;
- work with modern smart phones (and with stupid ones too);
- Download URL
- send SMS, initiate calls and data exchange services;
- receive and carry out events such as connecting and disconnecting calls, and carry out about 200 more functions available for regular SIM cards;
- interact with other SIM cards;
- execute arbitrary AT commands on the phone to control the GSM modem.
I will show you some examples of how the screen of smartphones looks when using our cards. Here are the features of mobile banking, not particularly common in the United States, but widely used throughout the world.
And now Karl will tell you how our applications work.

We used the following technologies:
- SmartCard - the physical connection between the SIM card and the phone, the same as using any smart cards;
- Java Card - Java programming for smart cards, which is the easiest way to write applications; it appeared back in the early 90s;
- SIM Toolkit (STK) API - an interaction interface between applications and the smartphone operating system interface, which allows the card to "talk" to the phone, receiving from it and transmitting events to it;
- GlobalPlatform is a standard for downloading and managing applications on a SIM card developed by the creators of the VISA system.
The design of the smart card is designed to ensure the safety of data storage and processing, and communication is carried out using packages called APDUs.
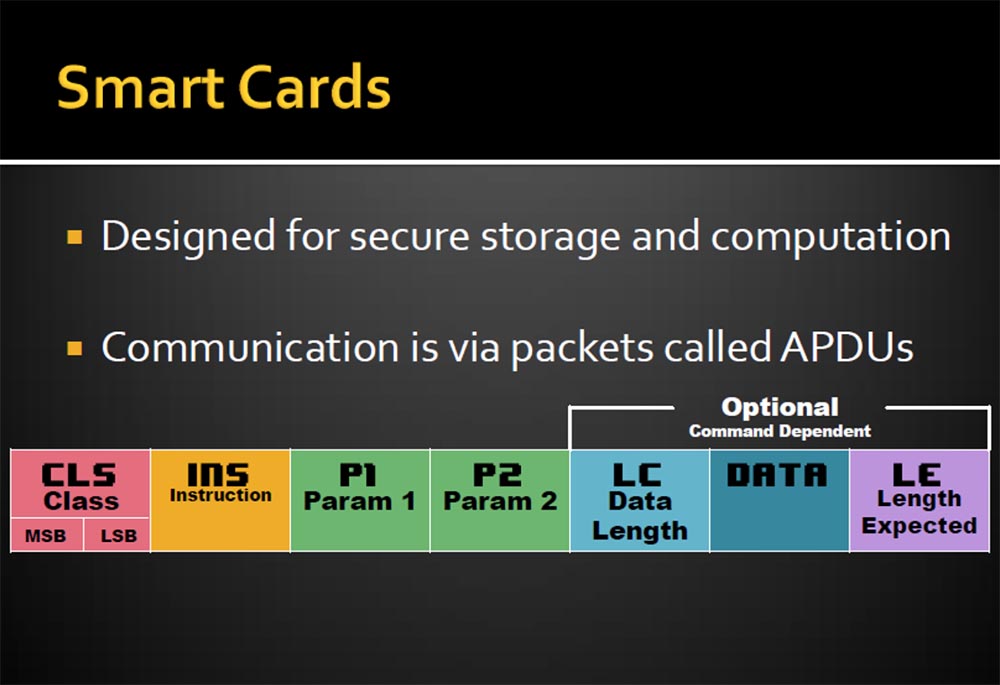
A feature of smart cards is the non-removability of keys and the encryption-decryption procedure, so you can use such personal data as passwords and logins to access the banking system, digital signatures, and access to satellite television. The CLS parameter is responsible for this. The following are instructions for processing INS information. APDUs are a stream of bytes that are described by parameters P1 and P2, and additional records, such as the length of the LC data transmission, the data itself, and the extension of the length of the LE.
On the next slide, you see JavaCard. This is Java and at the same time not entirely Java, because there is no garbage, no letters, strings, multidimensional arrays. If you are lucky, you can find several integer int data types. The structure of these cards is extremely simple. It goes without saying that there are no standard APIs, such as files or themes, you can get rid of verification, but there are some exceptions. Samples and classes of variables are stored in EEPROM memory, which has a limited number of write cycles, approximately 500 thousand. Therefore, depending on the type of map, you may have problems updating these variables.
I will tell you how we created our smart card applications. There are several specialized commercial IDE development environments, but you can do without them, because firstly, we wanted to make our applications as open as possible for everyone, and secondly, these commercial tools cost about $ 3000.
From Oracle, we downloaded the free Java Card Development Kit editor. If you use Eclipse, you must remove the standard JRE library system (Java Runtime) from the card and add the Java Card library to help describe classes and the like. In addition, we ourselves have written several programs to facilitate the work.
The STK application operates as follows:
- the application is downloaded to the map;
- The application registers itself using the SIM Toolkit API;
- the phone informs STK about its capabilities, and STK informs the phone about the registered application.
Thus, after downloading the phone, the application can use all 200 available functions, selecting an application from the menu triggers the corresponding event, after which the application sends UI requests back to the phone.
This is what our code looks like.

Java allows you to set a card class using two standard methods: creating and registering a class using the Java Runtime and installing the class using the SIM toolkit. The latter method is used when some event needs to be transferred to the card from the phone.
The next slide shows what the app we created for Tourcamp looks like. By activating the card, you can select one of the available networks. When you restart and connect to our network, you will be asked if you want to enable encryption, and this is another interesting feature of our application. It allows you to save prompts on a protected device so that they cannot be removed from there. In addition, we have introduced markers of unwanted interference, which allow you to find out whether these hints were viewed by someone, and allow you to view content remotely, which I will discuss later.
I warn you that the program code of our application looks pretty ugly. If you remember, there are no lines or groups here, so we are forced to create arrays of individual bytes with individual letters. This is a rather painful process, but we withstood it.
Next, we programmatically described the procedure for self-registration of the application using the SIM Toolkit, the process of selecting a program in the phone menu, displaying prompts on the screen and other functionality. We tried to prescribe everything to the maximum as we could, it looks awful, but it works. A full description of the program is given on our website, so you do not need to memorize what is shown on these slides. Now our report will continue Eric.

The easiest way is to use the old version of Java 1.1 encoding and the code compatibility version 1.3. After you have created the class files, you must transcode them for the Java Card. To do this, use the converter available in our SDK. You will also need some ID applications (most literally for one minute), an API export directory, and so on. These files must be understandable by the phone OS, so they are made in .jar format.
We also developed a special Makefiles program, which is available on the site . The converter produces a CAP file, which is a Zip archive of CAP components (Java Card code).
One of the important questions that had to be answered before starting work on the project was the question of how to interact with a SIM card. We needed a card reader. They are of two types: for connection to the PCSC port (PC / Smart Card API) and connected to the serial port Serial. The first ones are usually universal, so you need to have an adapter for working with a standard size SIM card, and the second ones are much smaller and are used specifically for SIM cards.
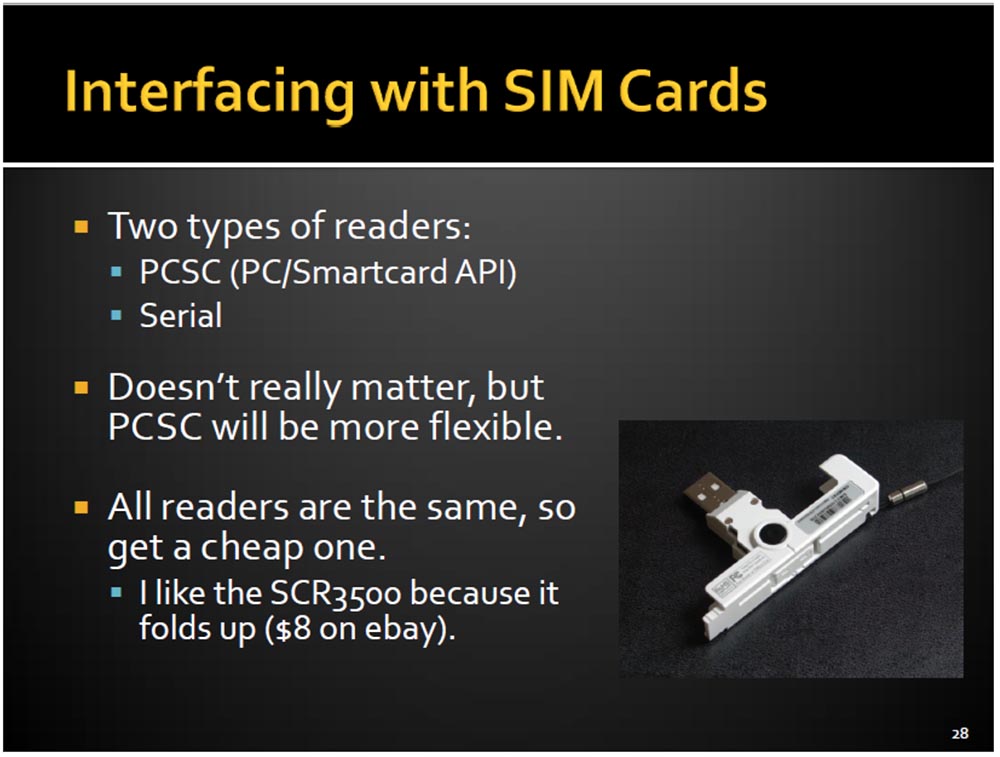
Functionally, there is no difference, but the PCSC option is more convenient to use. It uses official software designed specifically for the API and makes working with a computer easier. In addition, there are many open applications for working with SIM cards, which are easier to use with the PCSC option. All card readers are the same, so I used the cheapest SCR3500, bought on eBay for $ 8.
So, we wrote this awful looking code, then processed it with a Java compiler and converted it into a CAP file. Next, we tried to place it on a SIM card, for which we used the popular GPShell Tool, but we did not succeed. The seller of SIM cards advised us of another program with a simple and convenient interface that could not be found anywhere, and then promised to sell it for $ 600, although he did not have this program either.
Therefore, we used a program called SIM Alliance Loader, the slide below shows its window. We used the first version of this program, but now the second version is already available. SIM Alliance is a group that develops software for working with SIM cards. SIM Alliance Loader is an adaptation of Java applications for Windows and is designed for experts who understand what they are doing.

But if you understand the matter, transferring the application to the SIM card will take just a couple of minutes. However, given that we had about a thousand cards that we wanted to prepare for Tourcamp, such a recording technology would take too much time, so we decided to use something more productive. Therefore, we turned to Global Platform, the standard for downloading, installing, and managing Java Card applications. Depending on the application, this software allows the use of protocols and commands, as well as encryption and authentication. It also allows you to perform some external procedures without the participation of a SIM card, for example, verify the binary codes of our applets.
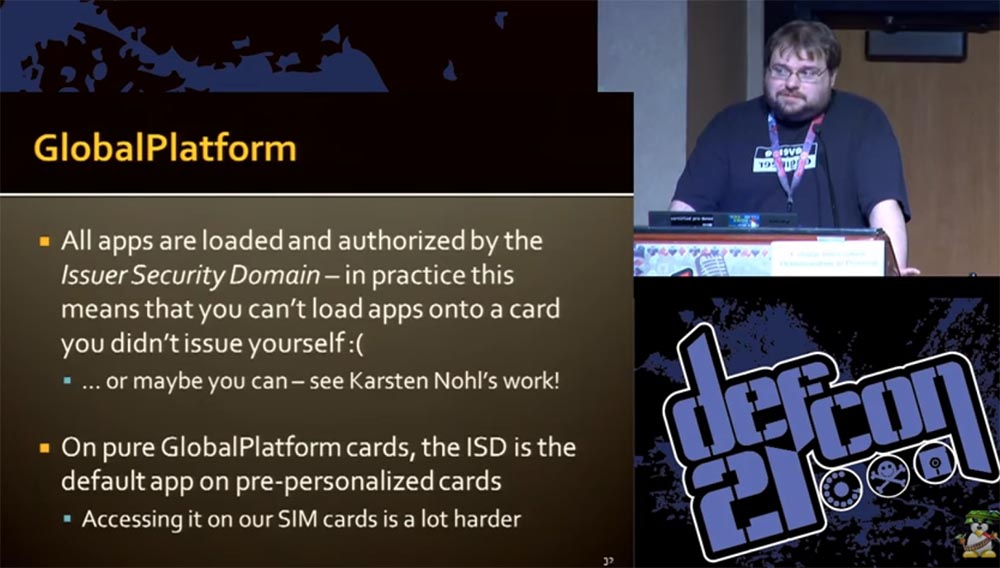
In the process, it turned out that all applications are downloaded and authenticated in the Issuer Security Domain (ISD) application, the Global Platform authentication system. In practice, this means that you cannot download the application to the map if you have not developed it yourself, but there are exceptions described in the work of Carsten Knowle.
On clean Global Platform SIM cards, the ISD application is available by default, access to it is much more difficult for our cards, because the GSM application is installed on them by default and there is not even an opportunity to access the Global Platform application. I will briefly describe the procedure for installing our application on a SIM card.
The process consists of two stages: the DOWNLOAD command (loading an array of binary codes) and the INSTALL command (creating an instance of the application on the SIM card). Single CAP components are combined together and sent to the card in blocks using the DOWNLOAD command. There are three types of Application IDs (AIDs) involved in this process:
- AID applications associated with the boot file;
- modular AIDs associated with the main card class;
- single AIDs used to select a specific parameter.
As a result, the CAP file is unzipped, data is extracted and written to the SIM card. The only way to “communicate” the Global Platform application with our SIM card is through the air, ie via SMS messages. In fact, we did not send traditional SMS, but simply generated commands on the map using SMS packets.
It was a long and rather laborious process. For the GSM 03.48 standard, it consisted of using the CAT shell (AoC2), which allows us to perform the necessary actions with the card. At the first stage of the process, it includes the SMS PP (D1) download, which, in turn, consists of the device identification and the SMS TPDU transport protocol data packet.

SMS TPDU includes header and user data. User data also includes a header, a command package, a subtitle (security settings, application selection). He, in turn, uses a TAR ID of 3 bytes (I wonder how PowerPoint withstood such nonsense). On this, the limit of internal data is exhausted, and at the very end of the list there is the very APDU that our Global Platform so needs. Thus, all this bulky mechanism serves to transfer a tiny array of data.
In case you do not want to do this, there is another mechanism for remotely sending APDUs to a SIM card. It requires the use of cellular communication to send SMS with installation commands, which requires authentication on the network. However, Karsten Knowle describes a method where encryption errors allow brute-force keys to obtain keys of a symmetric DES encryption algorithm, that is, without network authentication.
The Shadysim boot script is written in Python and runs on OSX, Linux, and Windows. The next slide shows how it looks. Downloading is done using a PC to which a card reader with a SIM card is connected.

The next slide shows the parameters that must be set to install the application on the card.
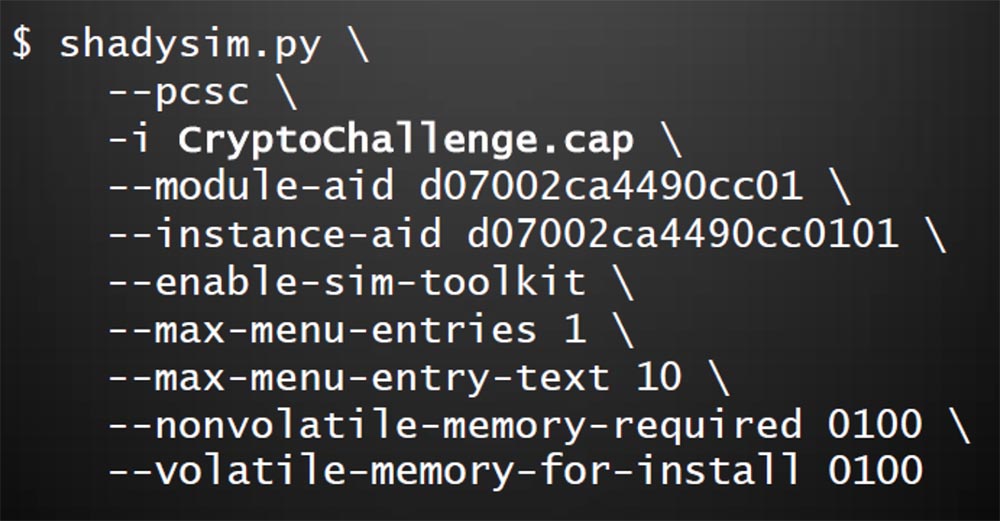
Here the main class of the map is set, the physical and RAM memory is reserved, the size of the text menu that will be displayed on the smartphone screen is determined, the command for launching the Toolkit is recorded, and so on. You can enter any other parameters using the hex code. Finally, a list of applications is introduced with the - t parameter, which allows you to update the phone book.
How do we know that our application is working? Eric will tell you about this.
The next slide shows what a working application looks like. On the left is a screen shot showing the operation of the program in Python, in the middle is the iPhone settings menu with the SIM Applications item and the icon of our program on the Applications tab for smartphones running Android.
Karl told you how hard programming was, but testing was not a bit easier. In order to check whether our program works, it was necessary to do the following:
- turn off the phone;
- remove the SIM card, and it is better to remove the battery;
- insert a SIM card into a card reader;
- Upload new code
- remove the card from the card reader;
- insert it back into the phone and insert the battery;
- wait for the phone to boot;
- check the operation of the code.
If the code does not work, the whole procedure must be repeated. How can this procedure be accelerated and facilitated?
To do this, you can use the Android emulator for SIM cards. There is an open source SEEK, which is an SDK for Android. It includes patches for accessing a SIM card or SD card via a USB PCSC card reader and prevents SIM card incompatibility conflict when connected to a computer and phone. You run the Android emulator on your computer and test your card without using a smartphone.
Can I use a smartphone as a card reader? Karl will answer this question.
The fact is that most radio interfaces do not allow direct communication with a SIM card. You can solve this problem using the Remote SIM Access Protocol. This method exists in Europe under the name "remote access to the SIM card via Bluetooth." This is a profile with built-in authentication. He needs to write an application that can send and receive APDUs. However, this method in some cases is able to turn your smartphone into a "brick", so you should not install this profile on all smartphones in a row.
I want to introduce you to the future directions of our developments. The STK is a great tool, but it has limitations in use. This begs the question, is it possible to create an SMS botnet? After all, SIM cards are designed for communication through a cellular network and do not need operating systems for the exchange of information, so there is the opportunity to combine them into a common network.
The integration of Android applications with SIM card applets also opens up great opportunities, for example, storing secure SSH private keys for authorization on a SIM card and secure operations with electronic currency BitCoin. We have an idea to use Android applications for OTA technology - “updating programs by air”, using SMS packages for this.
Another area is the improvement of NFS functions, Eric will tell you about it.
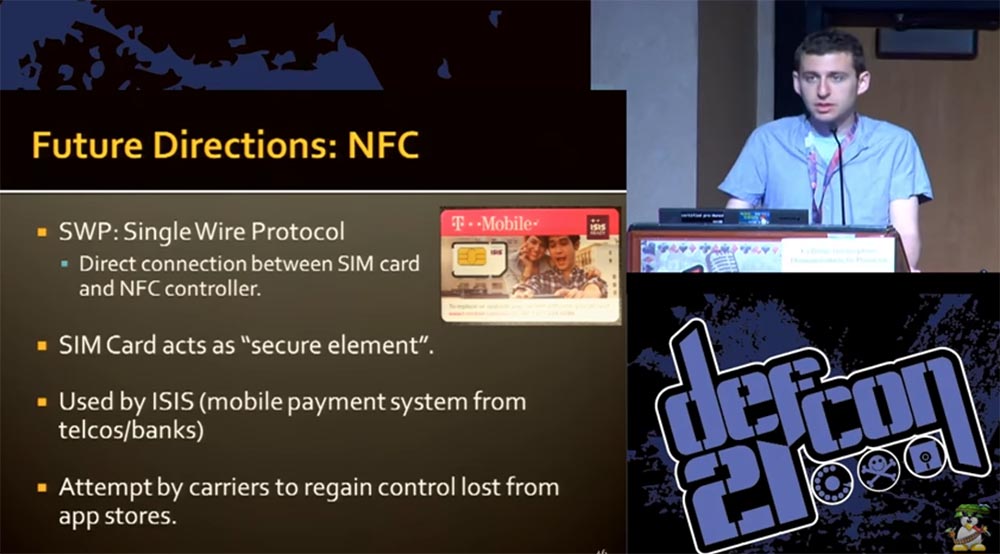
For example, using the single-wire SWP protocol, it will be possible to establish a direct connection between a SIM card and an NFS controller. This means that your SIM card can work without the help of the phone’s operating system directly, just like VISA or MasterCard bank cards work.
The SIM card can work as a security element or be used in ISIS mobile payment systems. This is an American system that is being introduced very slowly, it combines mobile banking and Telcos mobile communications, and our idea may be useful to them.
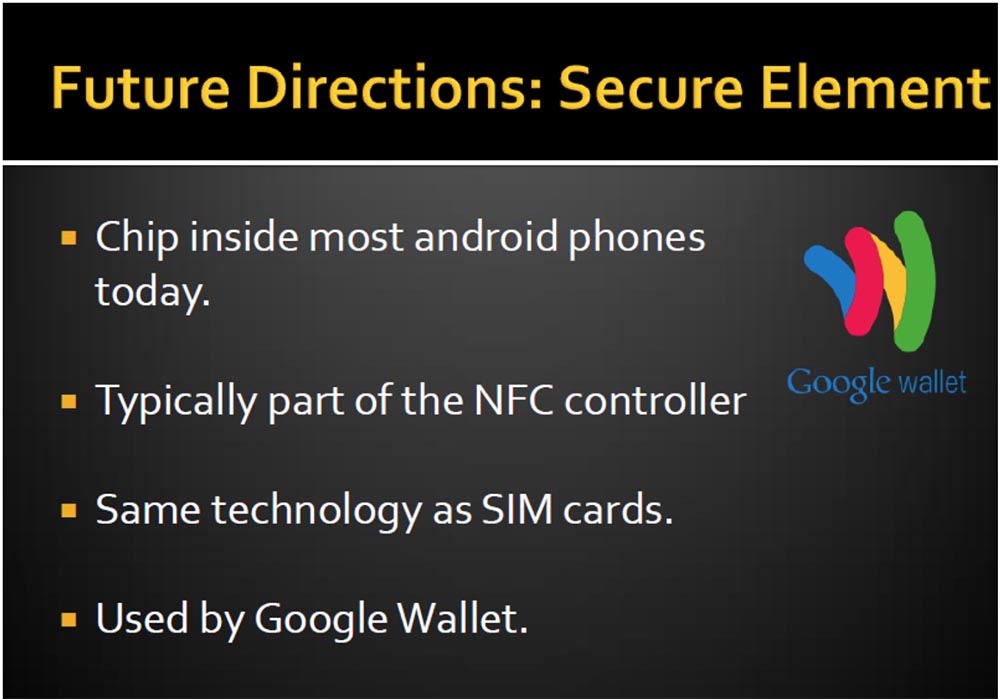
A SIM card can also serve to restore lost control over a mobile app store. Using SIM cards as an element of security is possible due to the following properties:
- Today, the SIM card processor is located inside most Android mobile devices;
- a SIM card is usually part of an NFS controller;
- the security element uses the same technology as the SIM card;
- SIM card can be used by Google Wallet e-wallet.
Therefore, I think that manufacturers of SIM cards should think about their potential capabilities and develop their functions in the areas we have described.
If you wish, you can download our application on the site , for its operation you will need certain devices worth no more than $ 20, for example, a card reader. There you can find slides of this presentation, scripts for applets, Makefiles for Java Card, patches for Android emulator and many more useful things.
Thank you for staying with us. Do you like our articles? Want to see more interesting materials? Support us by placing an order or recommending it to your friends, a 30% discount for Habr users on a unique analogue of entry-level servers that we invented for you: The whole truth about VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps from $ 20 or how to divide the server? (options are available with RAID1 and RAID10, up to 24 cores and up to 40GB DDR4).
Dell R730xd 2 times cheaper? Only we have 2 x Intel Dodeca-Core Xeon E5-2650v4 128GB DDR4 6x480GB SSD 1Gbps 100 TV from $ 249 in the Netherlands and the USA! Read about How to Build Infrastructure Bldg. class using Dell R730xd E5-2650 v4 servers costing 9,000 euros for a penny?
