Snort signature for CVE-2017-9805 in Apache Struts
Friends, good afternoon!
On September 7–8, reports about the hacking of one of the largest Equifax credit history bureaus began to appear in the media and blogs. Representatives of the American company said that the data "leaked" 143 million people: names, addresses, social security numbers and, in some cases, credit card numbers. Those who know how many services in the USA work with these identifiers can suggest the potential scale of future identity thefts.
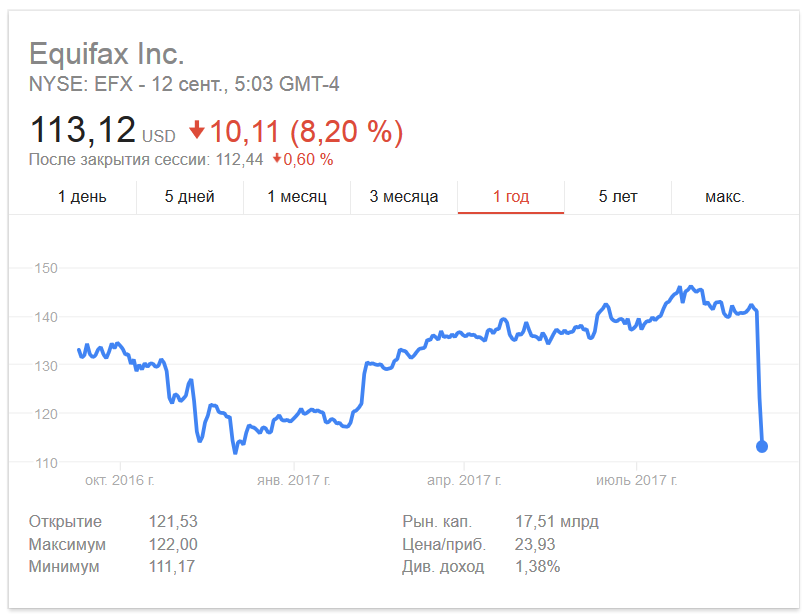
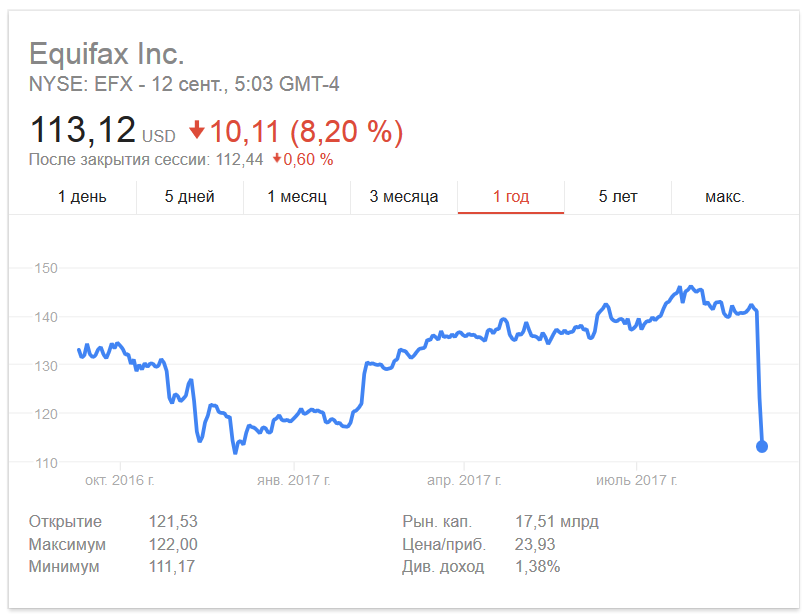
The leak itself occurred in May 2017, it became known about it only at the end of June. And for more than a month, the fact of the leak was not made public. Because of this and because of the strange behavior of top management (they may have leaked their stakes in the company a few days before the problems were announced), Equifax did this:
On September 5, the blog lgtm.com, sponsored by Semmle Inc., introduced the entry Using QL to find a remote code execution vulnerability in Apache Struts . The vulnerability received the identifier CVE-2017-9805 and CVSS Score from 7.5 to 10. That is, everything is very serious and many may have problems.
Therefore, as with the last time with WannaCry , we post the Snort signature to detect attempts to exploit this vulnerability:
What else to read to analyze the situation:
On September 7–8, reports about the hacking of one of the largest Equifax credit history bureaus began to appear in the media and blogs. Representatives of the American company said that the data "leaked" 143 million people: names, addresses, social security numbers and, in some cases, credit card numbers. Those who know how many services in the USA work with these identifiers can suggest the potential scale of future identity thefts.
The leak itself occurred in May 2017, it became known about it only at the end of June. And for more than a month, the fact of the leak was not made public. Because of this and because of the strange behavior of top management (they may have leaked their stakes in the company a few days before the problems were announced), Equifax did this:
On September 5, the blog lgtm.com, sponsored by Semmle Inc., introduced the entry Using QL to find a remote code execution vulnerability in Apache Struts . The vulnerability received the identifier CVE-2017-9805 and CVSS Score from 7.5 to 10. That is, everything is very serious and many may have problems.
Therefore, as with the last time with WannaCry , we post the Snort signature to detect attempts to exploit this vulnerability:
alert tcp $EXTERNAL_NET any -> $HOME_NET $HTTP_PORTS (msg:"AM Exploit Apache Struts 2.5 - REST Plugin XStream Possible Remote Code Execution"; flow:to_server,established; content:"POST"; http_method; nocase; content:"/bin/sh"; nocase; content:"java.lang"; nocase; content:"0"; content:"InputStream"; nocase; content:"jdk.nashorn.internal.objects.NativeString"; nocase; content:"ProcessBuilder"; nocase; content:"javax.imageio.ImageIO"; nocase; content:"/struts2-rest-showcase/"; http_uri; reference:cve,2017-9805; reference:url,lgtm.com/blog/apache_struts_CVE-2017-9805; reference:url,exploit-db.com/exploits/42627/; classtype:client-side-exploit; sid:5300590; rev:1) What else to read to analyze the situation:
- Vulnerability in Apache Struts allows remote code execution.
- A data leak of 143 million Equifax clients could have occurred due to a vulnerability in Apache Struts.
- Unknowns hacked into Equifax credit bureaus and stole the data of 143 million people.
- Equifax credit bureaus could hack through a bug in Apache Struts.
