Change your password: testing web services password policies

Back in 2015, we already tested the password policies of the largest web services, the results of which were presented here . And now, after 4 years, we decided to update and expand this study. In the 2019 study, we checked 157 services, divided into 14 categories depending on their purpose. If you are interested in how large resources are suitable for password policies such as Gmail, Facebook, eBay, PayPal, Steam, coinbase, DropBox, GitHub and many others, welcome to the cat!
So that users could not confine themselves to the simplest passwords in the process of registering an account and, therefore, did not put themselves under attack, there are password policies. They define the requirements for the length of passwords, the types of characters allowed and mandatory for use, the degree of complexity, etc. During the study, we found out what password policies are used on various web services.
It should be noted right away that you should not completely rely on the requirements of web resources when choosing your password. The study showed that even if you follow all the recommendations, the service may allow you to use some of the most common dictionary passwords.
Research methodology
For the analysis, we determined a set of rules presented in Table 1 - a compilation of recommendations from many services that are not very popular.

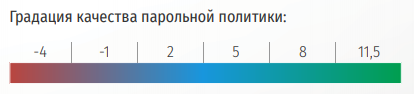
The next step was to evaluate the proposed resource requirements using points. For each defect that could eventually lead to a "weakening" of the password, points were deducted. And, on the contrary, services with optimal recommendations earned deserved points. The more points, the better the password policy of the service, respectively.
Of course, worst of all, if the rules for creating passwords are not at all, and a small number of points here does not require explanation. However, the approach in which the service requires creating a combination no longer than 20 characters or prohibiting the use of special characters also “weakens” the passwords. Therefore, in this case, the subtraction of points is fully justified.
In addition to these rules, 0.5 points added the presence of two-factor authentication from the service.
We also formed a small list of passwords (see Table 2), which to some extent satisfy these rules, but they are also dictionary and often used. If the service allowed you to register with the proposed combinations, he lost points.

A dictionary attack significantly speeds up password cracking and increases the chances of a brute force attack. To test the ability to set simple passwords, passwords were selected from several well-known dictionaries:
- Top 100 Worst Passwords
- Top 10,000 Worst Passwords
- The RockYou dictionary is one of the most popular brute force dictionaries. It includes passwords stolen from the hacked site of the company RockYou - a developer of applications for social networks.
For clarity, we have added a number of "achievements" for the shortcomings of the password policy.
Testing Web Services Password Policies
As a result of testing, 157 resources of various purposes were analyzed. The list of selected categories has been expanded, the old ones have been added:
- Hosting
- Password Managers
- News Services
- Entertainment resources
- Blogs and forums
- Internet banking
Full research can be read on the link .
We will immediately look at the results. In the table below you can find the leaders and outsiders of each group of services, compare the number of achievements obtained, but the most important thing is to find out who is more concerned about the security of their users' accounts.

Even the largest services do not always pay enough attention to protecting against the creation of simple passwords and, therefore, the security of user accounts. Only a few of the most popular Internet resources place serious demands on authentication.
Social networks
We show how we considered points on the example of social networks. The score distribution table is the following.


The final results in this group of services.

Most of the investigated services impose a minimum of password requirements. Basically, restrictions are imposed only on the minimum length. Compared with the previous study, this time the passwords are “grown up”, at least 6-8 characters. However, there is still no verification of vocabulary passwords. Social networks still don't care what password you will use. Thus, we evaluated all 14 service groups. What has changed in the last couple of years?
In the overall standings, postal services still lead, which is quite logical and reasonable, but social networks left their second position and moved to the middle of the list. E-commerce services are in the rankings even lower than before.
Mail Services
Like 4 years ago, the Pobox resource was an outsider among mail services. It was joined by the ProtonMail mail service, which does not use any password policies and puts all the responsibility for password security on the shoulders of the user.

Cryptocurrency services
In the group of cryptocurrency services, the CEX.IO and BitPay services, which were previously lagging behind in terms of security, strengthened their policies and now took middle positions.
Internet banking
Only on the third line of the ranking were Internet banking services. It would be logical to assume that the services of this category will accurately be more attentive to the security of the accounts of their users. In reality, everything turned out to be somewhat different. It turned out that not all services implemented password matching with login or mail. It also turned out to use most of the vocabulary passwords. Of course, one-time SMS verification codes are good, but only as long as the phone is in your hands. In general, the quality level of password policies in the services studied is comparable with password managers or cryptocurrency services.
Payment Services
In the group of WebMoney payment services over the past few years, it moved from the leading position to the bottom of the list. Almost every service gives a large number of recommendations for choosing a password. Of course, they block the simplest passwords, but still this level of security is unacceptable in the context of such services.

Gaming services
Game services began to take better care of password policies. True, this does not prevent the fact that player accounts constantly appear in the databases of the leaked data. An interesting condition appeared on the PlayStation Network page - the prohibition of duplicate and also located one after another on the keyboard characters. But a couple of vocabulary passwords still managed to be installed.

Cloud File Storage
These services are useful for providing access to data from anywhere in the world where there is access to the network. However, safety is usually sacrificed to comfort. There is also a tendency to allow the user to choose the password.

Hosting
Cases in terms of password policies of the hosts are, unfortunately, not at all rosy. Of all the services studied, only two had requirements for a user password. In addition, only DigitalOcean and Vscale filter vocabulary passwords.
Entertainment resources
Entertainment password policies are also not credible. Only one service "overcame the poverty line" in our scoring system. All the other services studied allowed using dictionary passwords and did not apply any checks to the passwords to be set. Despite all this, it was nice to learn about the possibility of using two-factor authentication on some resources.

Blogs and forums
Blogs and forums are not far away - they made unreasonably few requirements for user passwords and did not check them. This state of affairs in the services under study can be justified by the desire not to scare users away with a large set of rules. In pursuit of popularity, security is relegated to the background. And we did not avoid Habr - we honestly checked his password policies, the results were not at all impressive: there is no check for matching passwords with login or dictionary passwords, no recommendations on the symbols used.
findings
The picture remains the same: the use of a strong password is still a private initiative. Only a few of the most popular Internet resources place serious demands on authentication. Such an attitude to secure authentication can be explained by the pursuit of services for the audience. Here it is necessary to choose the “golden mean”: too complex rules will force you to spend significantly more time on registration, which can frighten the user away. On the other hand, the complete absence of policies will necessarily entail the occurrence of security incidents.
However, no matter how hard the service developers try, if the user doesn’t care about his protection, no one will help him. The full text of the study can be found here .
