How to Obtain Superuser Status Using DRAM: Rowhammer Technique
- Transfer
Researchers Information Security from Google created an exploit which exploits the physical weakness of the DDR-memory chips of certain types, to improve the rights of non-trusted users on Intel-based computers running under Linux.
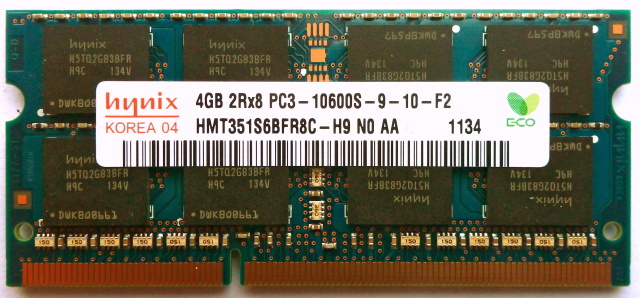
In a blog post on the Project Zero project, Google experts described a vulnerability exploitation technique that involves changing the values of individual data bits (bit flipping) stored in DDR3 chip modules called DIMMs. Last year, researchers provedthat such a substitution of bits can be carried out by affecting small sections of memory, which leads to a change in the data stored there. Google representatives have shown how all this can be used for a real attack.
“What is most impressive here is the fact that we are witnessing how a completely analogous problem at the level of the manufacturer of iron can be used to attack software. [...] Simply put, an exploit simply jumps over several levels of the stack, ”says David Kanter, editor-in-chief of Microprocessor Report.
How it works
DDR memory is an array of rows and columns that are divided into blocks used by various applications and the operating system. To ensure the security and integrity of the entire system, there is a “sandbox” in each large area of memory, access to which is available only for a specific application or process of the operating system.
A hacker can run a program that will, thousands of times in a split second, access specific rows of such areas in the memory module, as if “hammering them” until electromagnetic radiation penetrates into the adjacent memory area, which can lead to to change the values of bits in it from zeros to ones and vice versa. This technique is called Rowhammer .
The ability to influence the content of “forbidden” areas of memory can have far-reaching consequences. For example, in this way, users or applications with limited system privileges can increase them up to the unauthorized gain of administrative control.
And this, in turn, will allow an attacker to run malicious code or intercept the actions of users or programs. The consequences of such an attack, for example, on servers in a data center serving thousands of users can lead to significant damage.
It's not so bad
The vulnerability is present only in newer types of DDR3 memory, since the DRAM cells in them are located more compactly, which facilitates the electromagnetic effect of one cell on another. The attack will not work in the case of new DDR4, which have the ability to correct the error code ( ECC ).
In addition, according to Irene Abezgauz, an expert at Dyadic Security, for a number of reasons, the attack developed by Google at the moment is more theoretical than practical.
Firstly, it can be implemented only locally, and not remotely - this is a limitation that seriously reduces the possibility of using this technique by “ordinary” hackers. Secondly, to implement the Rowhammer technique, more than 540 thousand memory accesses must be completed in 64 milliseconds, which complicates the hacking.
Google researchers in their publication do not name the manufacturers of computers or memory whose products can be hacked using the developed exploit, or details about the percentage of successful attacks. However, the post contains a table listing anonymous 29 memory modules and laptop models. Of these 29, only 15 were subject to a change in bit values. In addition, only 13% of the implemented bit changes led to the possibility of exploiting the vulnerability.
Nevertheless, the ability to exploit the physical weaknesses of hardware is a new type of computer attack, which is quite difficult to counter.
Microprocessor Report's David Kanter describes the problem as follows:
This is not about software where you can create a patch and distribute it through a system update in a couple of weeks to most users. Here, in order to truly cope with the problem, you need to replace billions of dollars of DRAM modules. From a practical point of view, this is not feasible.
