Transparent encryption: advantages and disadvantages
This article will talk about transparent encryption implemented using the CyberSafe Top Secret program. In addition to the CyberSafe Top Secret program itself, it will show how to decrypt files encrypted using EFS.

Earlier in our articles, we showed how to use CyberSafe Top Secret to encrypt physical disks and create virtual encrypted disks. However, such encryption is not always convenient.
Firstly, it is not always possible to encrypt the entire physical disk. Secondly, if you use virtual disks, then container files, as a rule, occupy hundreds of megabytes of disk space and it is very easy for an attacker to detect them. Yes, there are methods of hiding data, but human laziness wins. Thirdly, the encrypted folder can constantly grow, and the size of the cryptodisk is limited to the size specified when it was created.
Everyone wants to work with files conveniently, and so that the files are reliably protected. There is such a compromise - this is transparent file encryption, when files are encrypted and decrypted "on the fly" - in the process of working with them. Files remain encrypted, and you work with them as with regular files. For example, if you encrypted the C: \ Documents folder and placed your documents in it, then when you open the document from this folder, Word or Excel starts and they do not even suspect that they are encrypted. You work with encrypted files, as with the most ordinary ones, completely without thinking about encryption, mount, virtual disks, etc.
In addition to ease of use, transparent encryption has another significant advantage. As a rule, a large number of files are stored on virtual encrypted disks. To work even with one of them, you need to connect the entire cryptodisk. As a result, all other files become vulnerable. Of course, you can create many small cryptodisks, assign each a separate password, but this is not very convenient.
In the case of transparent encryption, you can create as many encrypted folders as you need and put in each of them different groups of files - documents, personal photos, etc. In this case, only those files that are accessed are decrypted, and not all cryptodisk files at once.
In Windows (starting from Windows 2000 and in addition to Home releases), an encrypted file system - EFS (Encrypting File System) is traditionally used to organize transparent encryption.
EFS is designed to prevent one user from accessing files (encrypted) by another user. Why did you need to create EFS if NTFS supports access control? Although NTFS is a fairly safe file system, various utilities have appeared over time (one of the first was NTFSDOS, which allows reading files located on an NTFS partition from a DOS environment) that ignore NTFS permissions. There was a need for additional protection. Such protection was supposed to be EFS.
Essentially, EFS is an add-on for NTFS. EFS is convenient because it is part of Windows and you do not need any additional software to encrypt files - everything you need is already in Windows. To begin encrypting files, you do not need to perform any preliminary steps, since the first encryption of a file automatically creates an encryption certificate and a private key for the user.
Another advantage of EFS is that when you move a file from an encrypted folder to any other, it remains encrypted, and when you copy a file to an encrypted folder, it is automatically encrypted. There is no need to perform any additional actions.
This approach, of course, is very convenient, and it seems to the user that EFS is only one benefit. But this is not so. On the one hand, under unfavorable circumstances, the user may lose access to encrypted files altogether. This can happen in the following cases:
When users (especially beginners) start using EFS, few people think about it. But, on the other hand, there is special software (and it will be demonstrated later on) that allows you to access data even if the system was reinstalled and some keys were lost. And I don’t even know the advantages or disadvantages of this fact - this software allows you to restore access to data, but at the same time it can be used by an attacker to gain unauthorized access to encrypted files.
It would seem that data using EFS is encrypted very reliable. After all, files on a disk are encrypted using the FEK (File Encryption Key), which is stored in the file attributes. FEK itself is encrypted with a master key, which, in turn, is encrypted with the keys of system users who have access to this file. User keys are encrypted with password hashes of these users, and password hashes are also encrypted with SYSKEY.
It would seem that such an encryption chain was supposed to provide reliable data protection, but it all comes down to a username and password. Once the user resets the password or reinstalls the system, they will no longer be able to access the encrypted data.
EFS developers have reinsured themselves and implemented EFS Recovery Agents, that is, users who can decrypt data encrypted by other users. However, using the EFS RA concept is not very convenient and even difficult, especially for novice users. As a result, these very novice users know how to encrypt files using EFS, but they don’t know what to do in an emergency. It is good that there is special software that can help in this situation, but this same software can also be used for unauthorized access to data, as already noted.
The disadvantages of EFS include the impossibility of network encryption (if you need it, then you need to use other data encryption protocols, for example, IPSec) and the lack of support for other file systems. If you copy the encrypted file to a file system that does not support encryption, for example, to FAT / FAT32, the file will be decrypted and it can be viewed by anyone. There is nothing surprising in this; EFS is just an add-on for NTFS.
It turns out that EFS is more harmful than good. But, in order not to be unfounded, I will give an example of using the Advanced EFS Data Recovery programto access encrypted data. The scenario will be the simplest: first I will log in as a different user and try to access the encrypted file that the other user has encrypted. Then I will simulate the real situation when the certificate of the user who encrypted the file was deleted (this can happen, for example, in the case of reinstalling Windows). As you will see, the program will cope with this situation without too much trouble.
Let's see how you can decrypt files encrypted using EFS. First of all, you need to enable encryption for one of the folders. For demonstration, I specially created the EFS-Crypted folder. To enable EFS encryption for a folder, you just need to enable the corresponding attribute in its properties (Fig. 1).
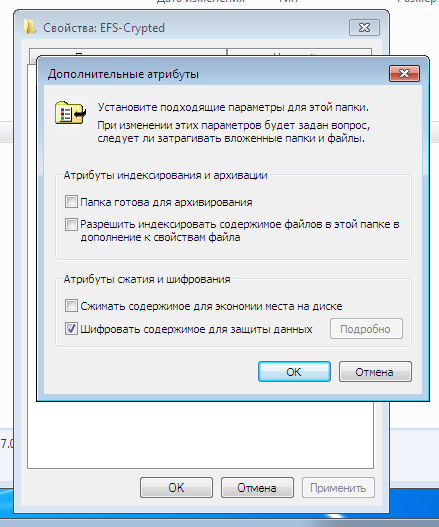
Fig. 1. Enabling encryption for the folder
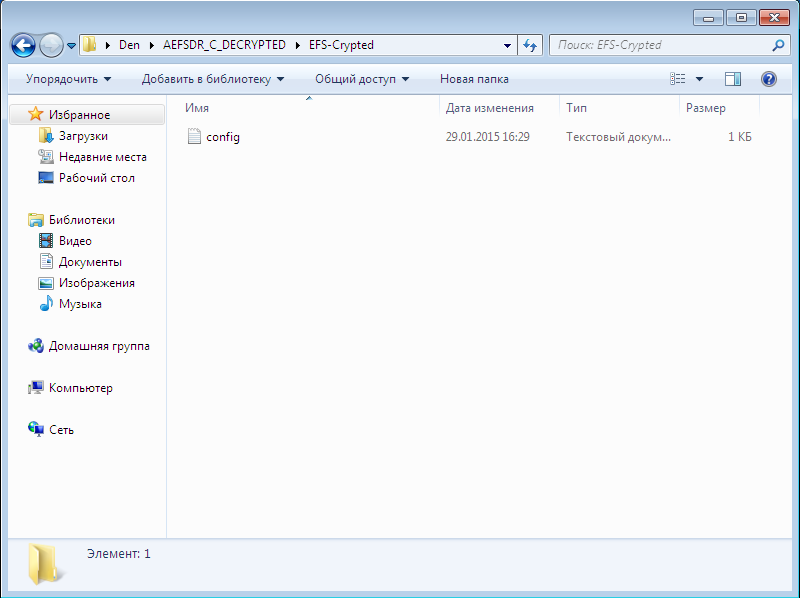
The name of the encrypted folder and all files placed in it (which will be automatically encrypted) in Explorer is displayed in green. As shown in fig. 2, I added the text file config.txt to the encrypted folder, the contents of which we will try to view by logging in as a different user. For the test, another user was created with administrator rights (such rights are needed by ElcomSoft Advanced EFS Data Recovery (AEFSDR)), see fig. 3.

Fig. 2. The contents of the encrypted folder

Fig. 3. A new user has been created.
Naturally, if you log in as another user and try to read the config.txt file, you will not succeed (Fig. 4).

Fig. 4. Access is denied
But it doesn’t matter - we start the Advanced EFS Data Recovery program and go directly to Expert mode (you can, of course, use the wizard that opens when you first start it (Fig. 5)), but I like the expert mode more.

Fig. 5. The wizard when starting Advanced EFS Data Recovery
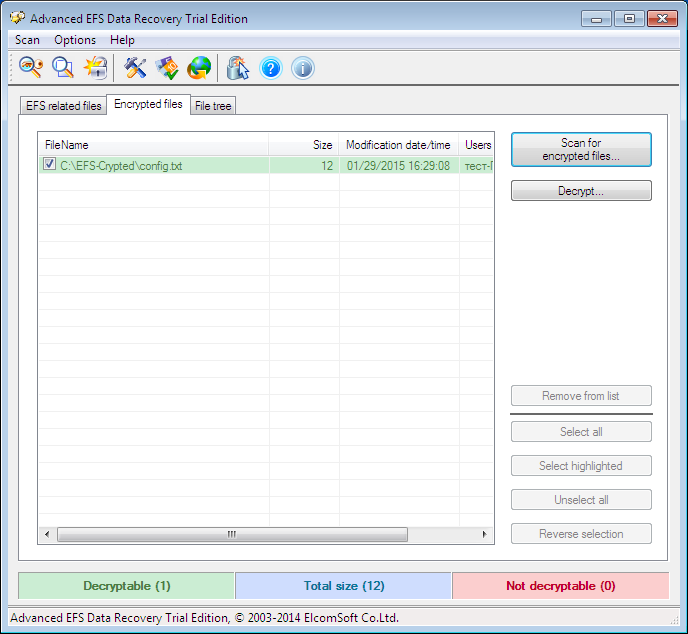
Fig. 6. Expert mode Advanced EFS Data Recovery
So, go to the Encrypted files tab and click the Scan for encrypted files button. In fig. Figure 6 already shows the scan result - our only encrypted file C: \ EFS-Crypted \ config.txt was found. Highlight it and click the Decrypt button . The program will prompt you to select the directory in which you want to decrypt the files (Fig. 7).
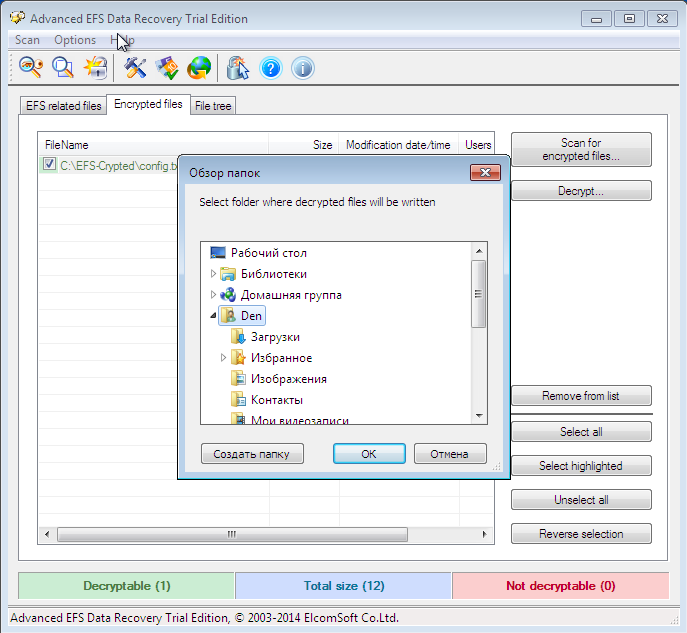
Fig. 7. Select the directory where the files will be decrypted.
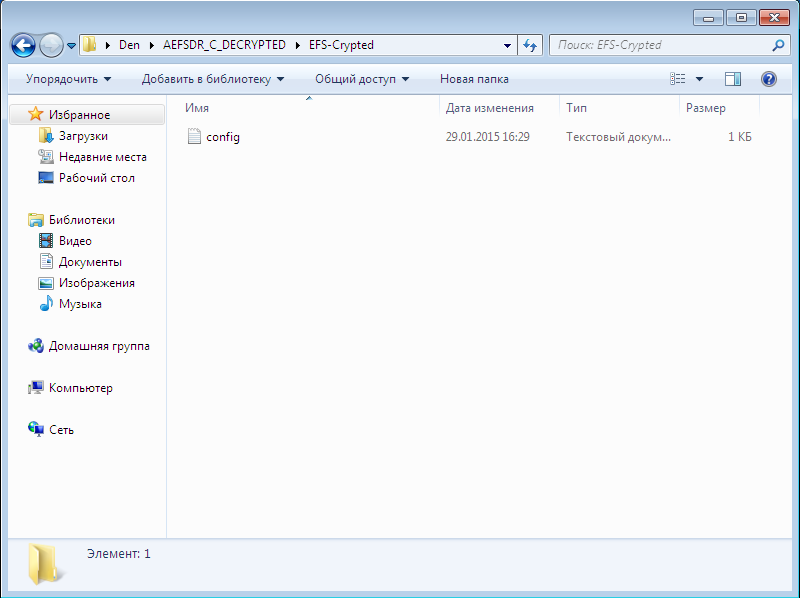
Since I have a trial version of the program, click Continue to continue (Fig. 8). The decrypted files are placed in the subfolder AEFS_ <drive_name> _DECRYPTED (Fig. 9). Please note that our config.txt file is no longer highlighted in green and we can view its contents (Fig. 10).
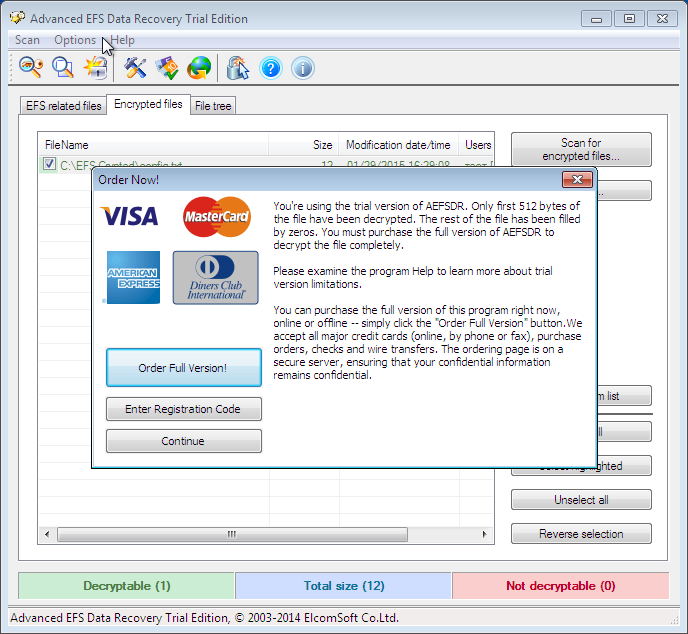
Fig. 8. Click the Continue button
. Fig. 9. Decrypted files
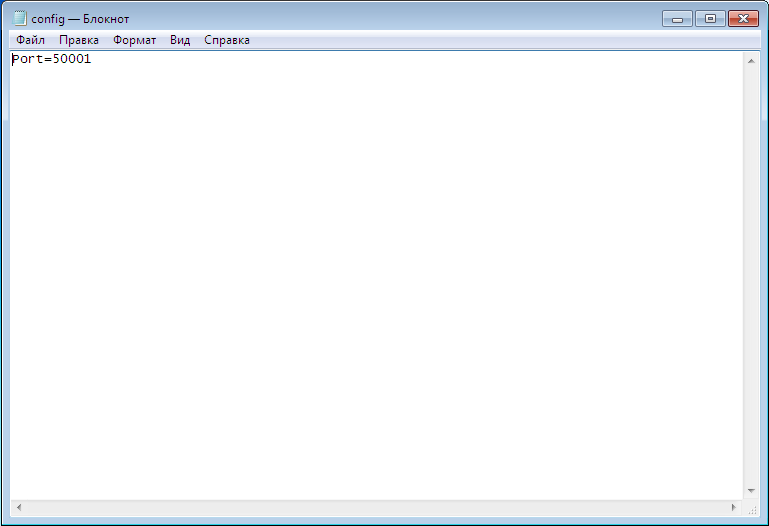
Fig. 10. The contents of the config.txt file
Now let's complicate the task to the Advanced EFS Data Recovery program , namely, delete the personal certificate. Log in as the user who created the encrypted folder and start the mmc console, select the menu command File, Add or Remove Snap-in . Next, select the Certificates snap-in and click the Add button (Figure 11). In the window that appears, select my user account (Fig. 12).

Fig. 11. Adding snap-in

Fig. 12. Equipment of the certificate manager.
Next, click OK and in the window that appears, go to Certificates, Personal, Certificates. You will see the created certificates for the current user (Fig. 13). In my case, the user is called a test . Right-click on its certificate and select Delete to remove the certificate. You will see a warning that decrypting data encrypted with this certificate will no longer be possible. Well, we'll check it out soon.
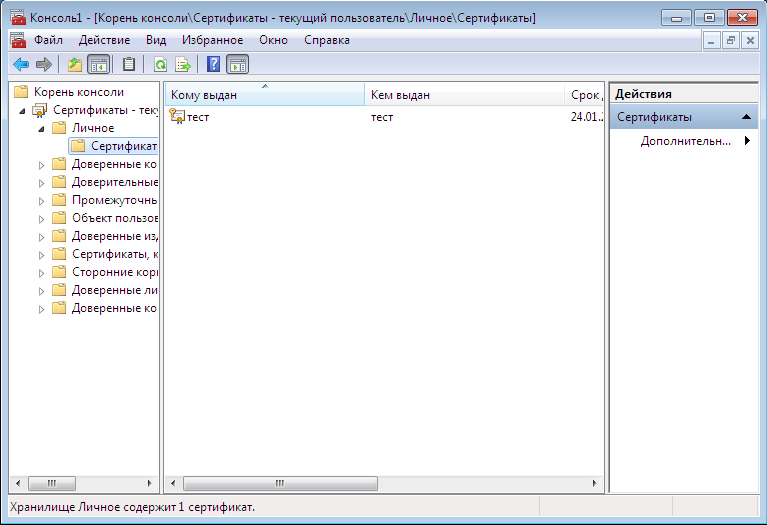
Fig. 13. Personal certificates

Fig. 14. Warning when deleting a certificate
Next, follow these steps:

Fig. 15. Search for keys
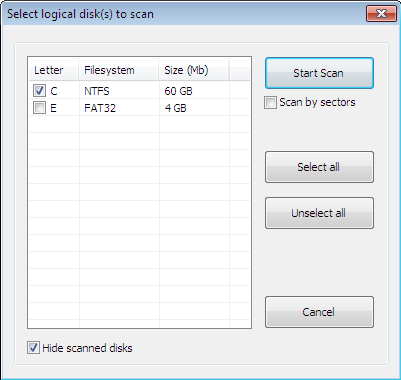
Fig. 16. Scan window
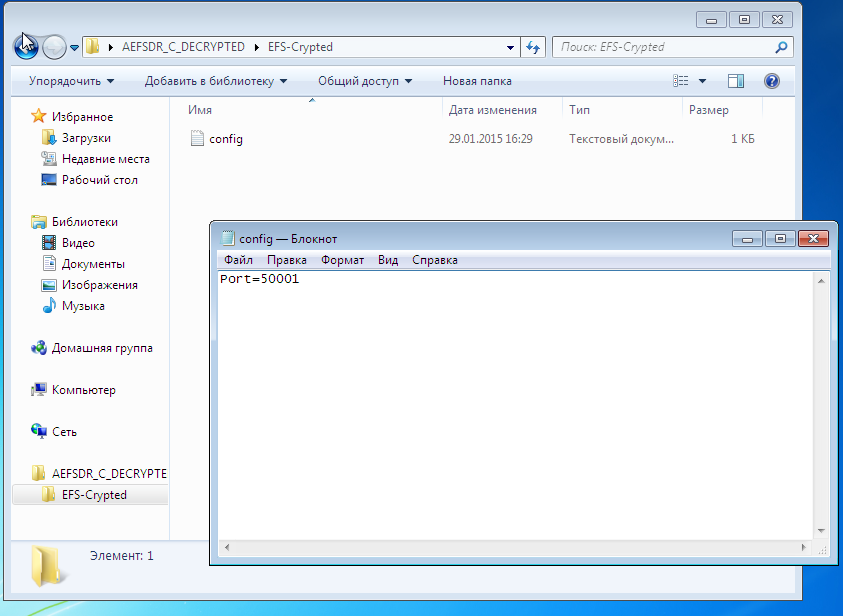
Fig. 17. The file is again decrypted.
To the shame of EFS or to the honor of Advanced EFS Data Recovery, in both cases the file was decrypted. At the same time, as you see, I did not need any special knowledge or skills. It is enough to run a program that will do all the work for you. You can read about how the program works on the developers website (http://www.elcomsoft.ru/), we won’t discuss the principle of its operation in this article, since AEFSDR is not the subject of the article.
In fairness, I must say that specialists can configure the system so that Advanced EFS Data Recovery will be powerless. However, we looked at the most common use of EFS for the vast majority of users.
Let's see how transparent encryption is implemented in CyberSafe. For transparent encryption, the Alfa Transparent File Encryptor driver (http://www.alfasp.com/products.html) is used, which encrypts files using the AES-256 algorithm or GOST 28147-89 algorithm (when using Crypto-Pro).
The encryption rule (file mask, allowed / forbidden processes, etc.), as well as the encryption key, is transmitted to the driver. The encryption key itself is stored in the ADS folder (Alternate Data Streams, eb.by/Z598 ) and encrypted using OpenSSL (RSA algorithm) or GOST R 34.10-2001 - certificates are used for this.
The logic is as follows: add a folder, CyberSafe creates a key for the driver, encrypts it with selected public certificates (they must be previously created or imported into CyberSafe). When someone tries to access a folder, CyberSafe opens the ADS folder and reads the encrypted key. If this user has a private certificate key (he can have one or several of his certificates), which was used to encrypt the key, he can open this folder and read the files. It should be noted that the driver decrypts only what is needed, and not all files when providing access to the file. For example, if a user opens a large Word document, then only the part that is now loaded into the editor is decrypted, the rest is loaded as necessary. If the file is small,
If the folder is network shared, then the files in it remain encrypted, the client driver decrypts only the file or part of the file in memory, although this is also true for the local folder. When editing a file, the driver encrypts the changes in memory and writes to the file. In other words, even when the folder is on (it will be shown later what it is), the data on the disk always remains encrypted.
It is time to consider the practical use of CyberSafe Top Secret. To encrypt a folder, go to the Transparent Encryption program section ( File Encryption tab ), see fig. 18. Then, from the Explorer, drag the folders you want to encrypt into the workspace of the program. You can also use the Add button . folder . I added one folder - C: \ CS-Crypted.
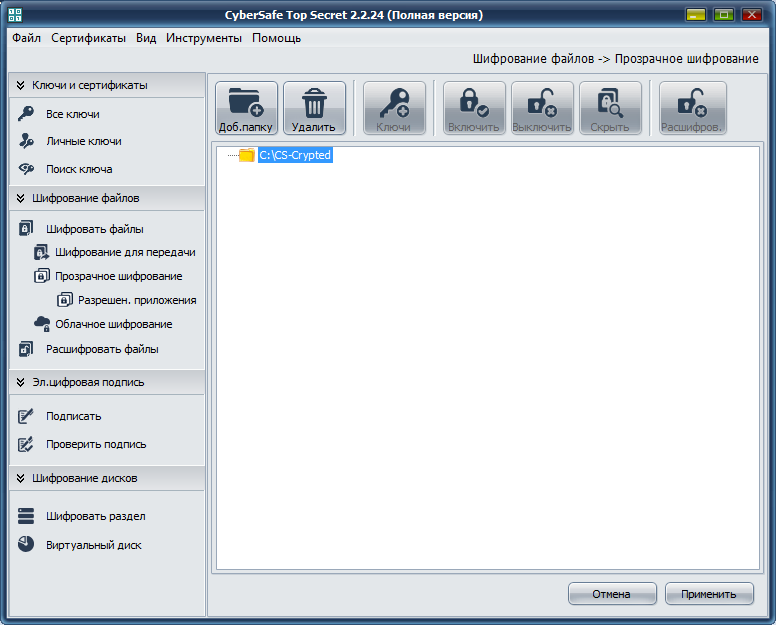
Fig. 18. CyberSafe Top Secret
Click Apply . In the window that appears (Fig. 19), click Yes or Yes for allx (if you are trying to encrypt multiple folders at a time). Next, you will see a window for selecting certificates whose keys will be used for transparent encryption of the folder (Fig. 20). As a rule, certificates are created immediately after installing the program. If you have not already done so, you will have to return to the Private Keys section and click the Create button .

Fig. 19. Click Yes

. Fig. 20. Choosing certificates for transparent encryption.
The next question for the program is whether to install an administrator key for this folder (Fig. 21). Without an administrator key, you cannot make changes to the folder, so click Yes .
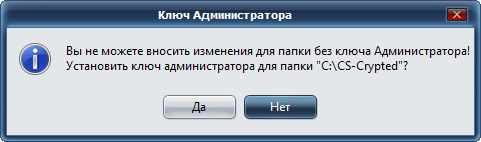
Fig. 21. Again click Yes
After that, you will return to the main program window. Before you start working with an encrypted folder, you need to select it and click the Enable button . The program will ask for the password of the certificate (Fig. 22) specified for encryption of this folder. After that, working with an encrypted folder will not differ from working with a regular folder. In the CyberSafe window, the folder will be marked as open, and a lock icon will appear to the left of the folder icon (Fig. 23).
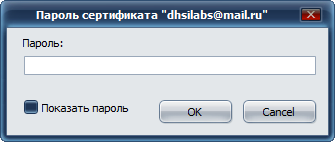
Fig. 22. Enter the certificate password
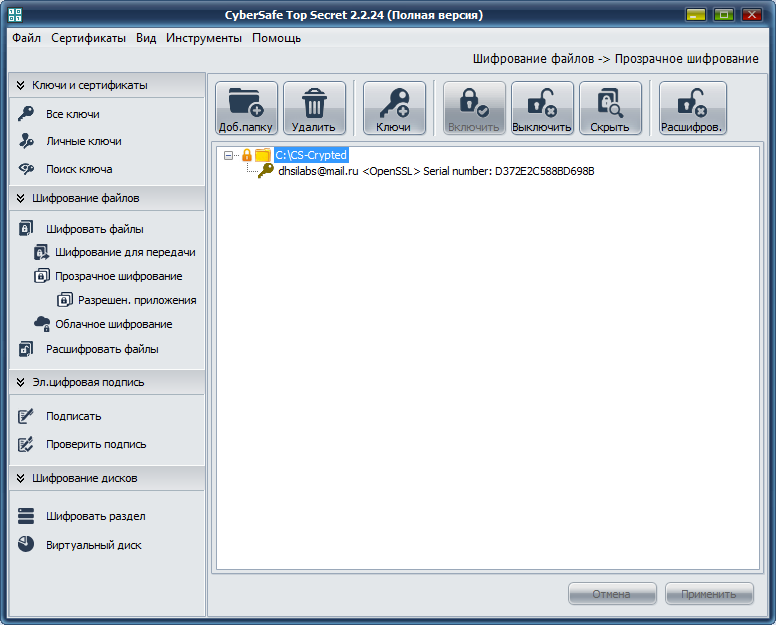
Fig. 23. An encrypted folder is connected.
In Explorer, neither an encrypted folder nor encrypted files are marked in any way. Outwardly, they look the same as other folders and files (unlike EFS, where the names of encrypted files / folders are highlighted in green), see fig. 24.
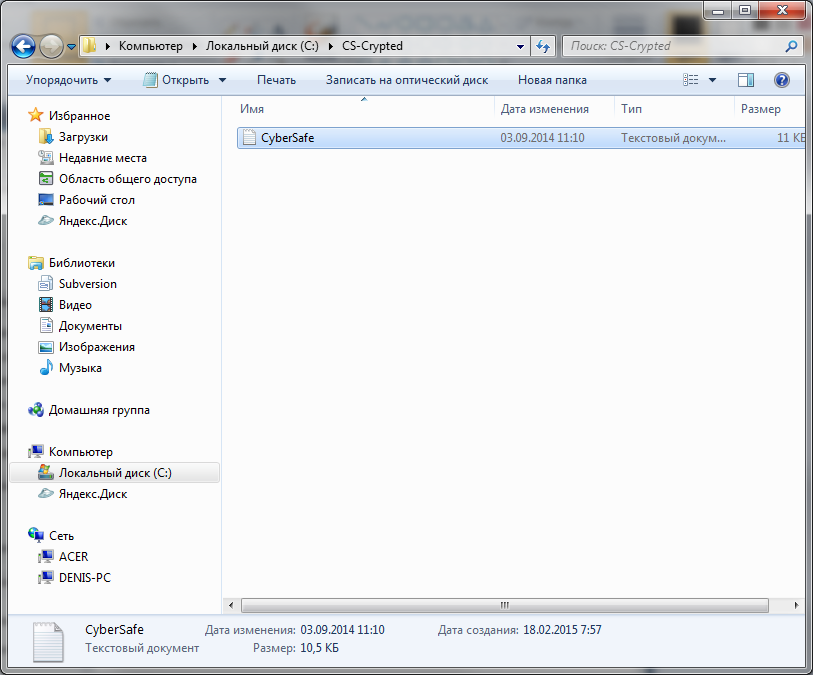
Fig. 24. The encrypted CS-Crypted folder in Explorer
It should be noted that in the same way you can encrypt the network folder. In this case, the CyberSafe program should be located only on the users computer, and not on the file server. All encryption is performed on the client, and already encrypted files are transferred to the server. This decision is more than justified. Firstly, already encrypted data is transmitted over the network. Secondly, even if the server administrator wants to access the files, nothing will come of it, since only users whose certificates were specified during encryption can decrypt the files. But the administrator, if necessary, can back up encrypted files.
When the encrypted folder is no longer needed, you need to go to the CyberSafe program, select the folder and click the Off button. This solution may not seem to you as convenient as EFS - you need to press the on / off buttons. But this is only at first glance. Firstly, the user has a clear understanding that the folder is encrypted and he will not forget about this fact when he reinstalls Windows. Secondly, when using EFS, if you need to leave the computer, you need to log out, because during your absence, anyone can go to the computer and access your files. All he will need to do is copy your files to a device that does not support encryption, for example, to a FAT32 flash drive. Then he will be able to view files outside your computer. With CyberSafe, everything is a little more convenient. Yes, you need to take an additional action (“turn off” the folder) and all encrypted files will become inaccessible.
However, each product has its own characteristics. CyberSafe is no exception. Imagine that you encrypted the C: \ CS-Crypted folder and put the report.txt file there. When the folder is turned off, of course, you cannot read the file. When the folder is turned on , you can access the file and, accordingly, copy it to any other, unencrypted folder. But after copying the file to an unencrypted folder, he continues to live his own life. On the one hand, it is not as convenient as in the case of EFS, on the other hand, knowing such a feature of the program, the user will be more disciplined and will only keep his secret files in encrypted folders.
Now let's try to find out which is faster - EFS or CyberSafe Top Secret. All tests are carried out on a real machine - no virtual machines. The configuration of the laptop is as follows - Intel 1000M (1.8 GHz) / 4 GB RAM / WD WD5000LPVT (500 GB, SATA-300, 5400 RPM, 8 MB / Windows 7 64-bit buffer). The car is not very powerful, but what it is.
The test will be extremely simple. We will copy the files to each of the folders and see how long it takes to copy. To find out which transparent encryption tool is faster, the following simple scenario will help us:
You don't need to be a programming guru to figure out what this script does. It's no secret that we often work with relatively small files with sizes ranging from several tens to several hundred kilobytes. This script copies the distribution of Joomla! 3.3.6, in which there are 5580 such small files, first to the folder encrypted by EFS, and then to the folder encrypted by CyberSoft. Let's see who will be the winner.
The robocopy command is used to recursively copy files, including empty files (/ E option), and its output is deliberately redirected to a text file (if you wish, you can see what was copied and what wasn’t) so as not to clog the script output.
The results of the second test are shown in Fig. 25. As you can see, EFS completed this task in 74 seconds, and CyberSoft in just 32 seconds. Given that in most cases, users work with many small files, CyberSafe will be more than twice as fast as EFS .

Fig. 25. Test results
Now a little summary. The advantages of transparent encryption CyberSafe include the following facts:
The last two benefits deserve special attention. To protect against access to the user's private keys, you can protect the CyberSafe program itself. To do this, execute the Tools, Settings command (Fig. 26). In the Settings window on the Authentication tab, you can enable either password authentication or two-factor authentication. Details on how to do this, please read the manual for CyberSafe Program on page 119.
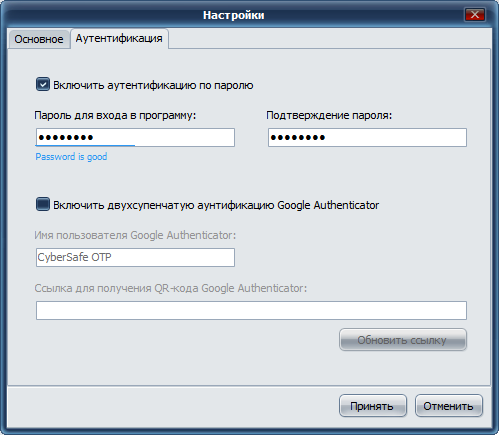
Fig. 26. Protection of the CyberSafe program itself
On the Allowed tab . applicationsYou can identify trusted applications that are allowed to work with encrypted files. By default, all applications are trusted. But for greater security, you can specify applications that are allowed to work with encrypted files. In fig. 27 I have indicated as trusted applications MS Word and MS Excel. If some other program tries to access the encrypted folder, it will be denied access. You can find more information in the article “Transparent file encryption on the local computer using CyberSafe Files Encryption” (http://habrahabr.ru/company/cybersafe/blog/210458/).

Fig. 27. Trusted applications
That's all. We recommend that you read the following articles:
Transparent encryption of files on the local computer using CyberSafe Files Encryption
Transparent encryption of network folders in the corporate space
Methods of information hiding
Encryption of cloud services in companies and organizations

A few words about transparent encryption
Earlier in our articles, we showed how to use CyberSafe Top Secret to encrypt physical disks and create virtual encrypted disks. However, such encryption is not always convenient.
Firstly, it is not always possible to encrypt the entire physical disk. Secondly, if you use virtual disks, then container files, as a rule, occupy hundreds of megabytes of disk space and it is very easy for an attacker to detect them. Yes, there are methods of hiding data, but human laziness wins. Thirdly, the encrypted folder can constantly grow, and the size of the cryptodisk is limited to the size specified when it was created.
Everyone wants to work with files conveniently, and so that the files are reliably protected. There is such a compromise - this is transparent file encryption, when files are encrypted and decrypted "on the fly" - in the process of working with them. Files remain encrypted, and you work with them as with regular files. For example, if you encrypted the C: \ Documents folder and placed your documents in it, then when you open the document from this folder, Word or Excel starts and they do not even suspect that they are encrypted. You work with encrypted files, as with the most ordinary ones, completely without thinking about encryption, mount, virtual disks, etc.
In addition to ease of use, transparent encryption has another significant advantage. As a rule, a large number of files are stored on virtual encrypted disks. To work even with one of them, you need to connect the entire cryptodisk. As a result, all other files become vulnerable. Of course, you can create many small cryptodisks, assign each a separate password, but this is not very convenient.
In the case of transparent encryption, you can create as many encrypted folders as you need and put in each of them different groups of files - documents, personal photos, etc. In this case, only those files that are accessed are decrypted, and not all cryptodisk files at once.
Advantages and disadvantages of EFS
In Windows (starting from Windows 2000 and in addition to Home releases), an encrypted file system - EFS (Encrypting File System) is traditionally used to organize transparent encryption.
EFS is designed to prevent one user from accessing files (encrypted) by another user. Why did you need to create EFS if NTFS supports access control? Although NTFS is a fairly safe file system, various utilities have appeared over time (one of the first was NTFSDOS, which allows reading files located on an NTFS partition from a DOS environment) that ignore NTFS permissions. There was a need for additional protection. Such protection was supposed to be EFS.
Essentially, EFS is an add-on for NTFS. EFS is convenient because it is part of Windows and you do not need any additional software to encrypt files - everything you need is already in Windows. To begin encrypting files, you do not need to perform any preliminary steps, since the first encryption of a file automatically creates an encryption certificate and a private key for the user.
Another advantage of EFS is that when you move a file from an encrypted folder to any other, it remains encrypted, and when you copy a file to an encrypted folder, it is automatically encrypted. There is no need to perform any additional actions.
This approach, of course, is very convenient, and it seems to the user that EFS is only one benefit. But this is not so. On the one hand, under unfavorable circumstances, the user may lose access to encrypted files altogether. This can happen in the following cases:
- Hardware problems, for example, the motherboard is out of order, the bootloader is corrupted, system files are damaged due to a hard disk failure (bad sectors). As a result, the hard drive can be connected to another computer to copy files from it, but if they are encrypted with EFS, nothing will work.
- The system is reinstalled. Windows can be reinstalled for a variety of reasons. In this case, access to encrypted data, of course, will be lost.
- Deleted user profile. Even if you create a user with the same name, he will be assigned a different ID, and decrypt the data will still fail.
- The system administrator or the user himself has reset the password. After that, access to EFS data will also be lost.
- Incorrect user transfer to another domain. If the user transfer is not performed correctly, he will not be able to access his encrypted files.
When users (especially beginners) start using EFS, few people think about it. But, on the other hand, there is special software (and it will be demonstrated later on) that allows you to access data even if the system was reinstalled and some keys were lost. And I don’t even know the advantages or disadvantages of this fact - this software allows you to restore access to data, but at the same time it can be used by an attacker to gain unauthorized access to encrypted files.
It would seem that data using EFS is encrypted very reliable. After all, files on a disk are encrypted using the FEK (File Encryption Key), which is stored in the file attributes. FEK itself is encrypted with a master key, which, in turn, is encrypted with the keys of system users who have access to this file. User keys are encrypted with password hashes of these users, and password hashes are also encrypted with SYSKEY.
It would seem that such an encryption chain was supposed to provide reliable data protection, but it all comes down to a username and password. Once the user resets the password or reinstalls the system, they will no longer be able to access the encrypted data.
EFS developers have reinsured themselves and implemented EFS Recovery Agents, that is, users who can decrypt data encrypted by other users. However, using the EFS RA concept is not very convenient and even difficult, especially for novice users. As a result, these very novice users know how to encrypt files using EFS, but they don’t know what to do in an emergency. It is good that there is special software that can help in this situation, but this same software can also be used for unauthorized access to data, as already noted.
The disadvantages of EFS include the impossibility of network encryption (if you need it, then you need to use other data encryption protocols, for example, IPSec) and the lack of support for other file systems. If you copy the encrypted file to a file system that does not support encryption, for example, to FAT / FAT32, the file will be decrypted and it can be viewed by anyone. There is nothing surprising in this; EFS is just an add-on for NTFS.
It turns out that EFS is more harmful than good. But, in order not to be unfounded, I will give an example of using the Advanced EFS Data Recovery programto access encrypted data. The scenario will be the simplest: first I will log in as a different user and try to access the encrypted file that the other user has encrypted. Then I will simulate the real situation when the certificate of the user who encrypted the file was deleted (this can happen, for example, in the case of reinstalling Windows). As you will see, the program will cope with this situation without too much trouble.
Using Advanced EFS Data Recovery to decrypt encrypted EFS files
Let's see how you can decrypt files encrypted using EFS. First of all, you need to enable encryption for one of the folders. For demonstration, I specially created the EFS-Crypted folder. To enable EFS encryption for a folder, you just need to enable the corresponding attribute in its properties (Fig. 1).
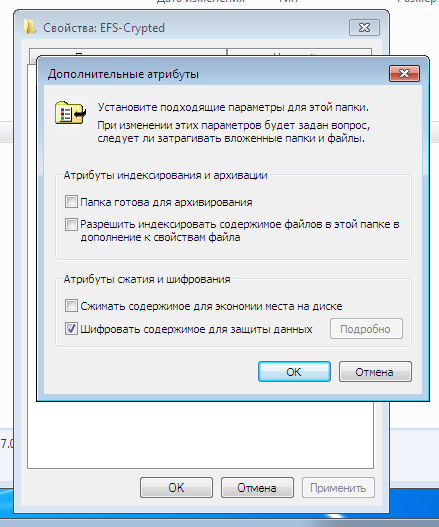
Fig. 1. Enabling encryption for the folder
The name of the encrypted folder and all files placed in it (which will be automatically encrypted) in Explorer is displayed in green. As shown in fig. 2, I added the text file config.txt to the encrypted folder, the contents of which we will try to view by logging in as a different user. For the test, another user was created with administrator rights (such rights are needed by ElcomSoft Advanced EFS Data Recovery (AEFSDR)), see fig. 3.

Fig. 2. The contents of the encrypted folder

Fig. 3. A new user has been created.
Naturally, if you log in as another user and try to read the config.txt file, you will not succeed (Fig. 4).

Fig. 4. Access is denied
But it doesn’t matter - we start the Advanced EFS Data Recovery program and go directly to Expert mode (you can, of course, use the wizard that opens when you first start it (Fig. 5)), but I like the expert mode more.

Fig. 5. The wizard when starting Advanced EFS Data Recovery
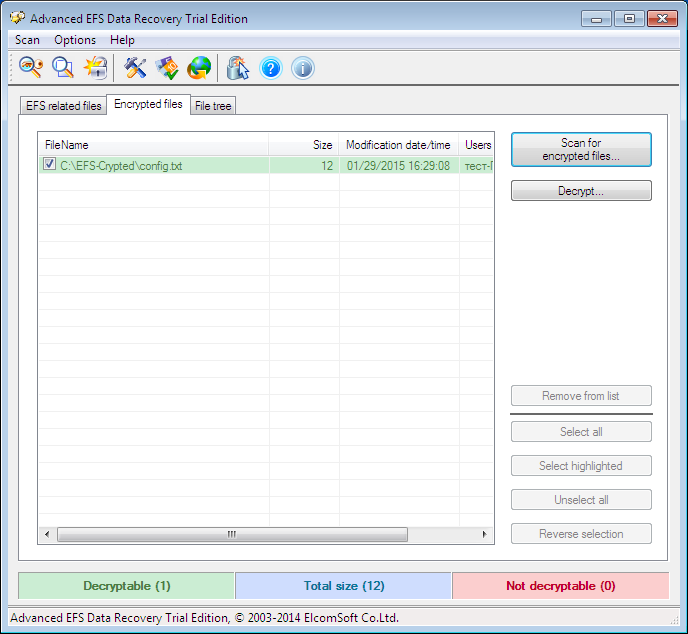
Fig. 6. Expert mode Advanced EFS Data Recovery
So, go to the Encrypted files tab and click the Scan for encrypted files button. In fig. Figure 6 already shows the scan result - our only encrypted file C: \ EFS-Crypted \ config.txt was found. Highlight it and click the Decrypt button . The program will prompt you to select the directory in which you want to decrypt the files (Fig. 7).
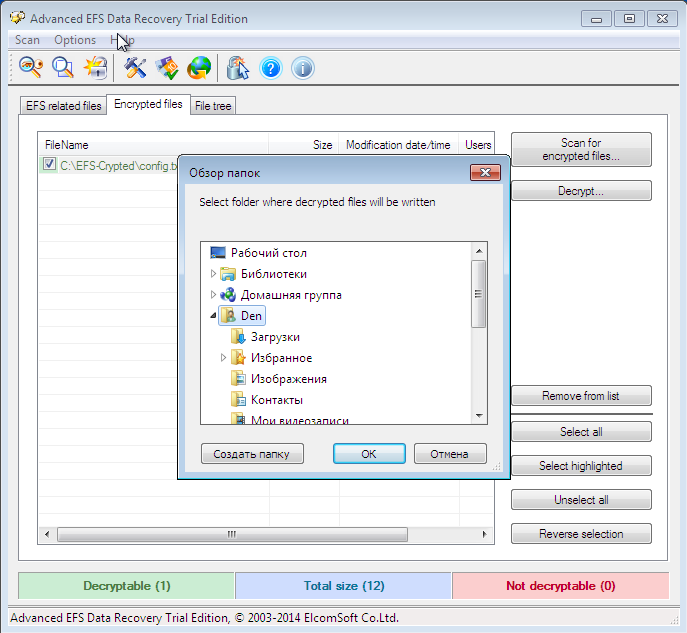
Fig. 7. Select the directory where the files will be decrypted.
Since I have a trial version of the program, click Continue to continue (Fig. 8). The decrypted files are placed in the subfolder AEFS_ <drive_name> _DECRYPTED (Fig. 9). Please note that our config.txt file is no longer highlighted in green and we can view its contents (Fig. 10).
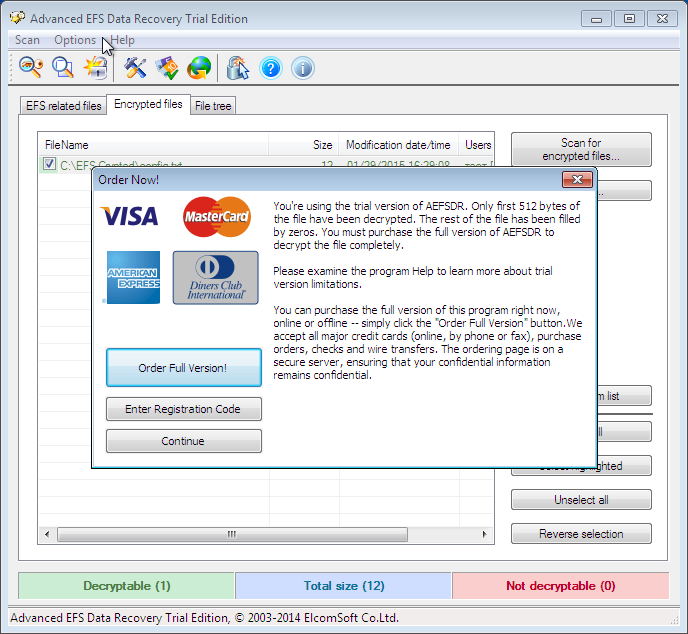
Fig. 8. Click the Continue button
. Fig. 9. Decrypted files
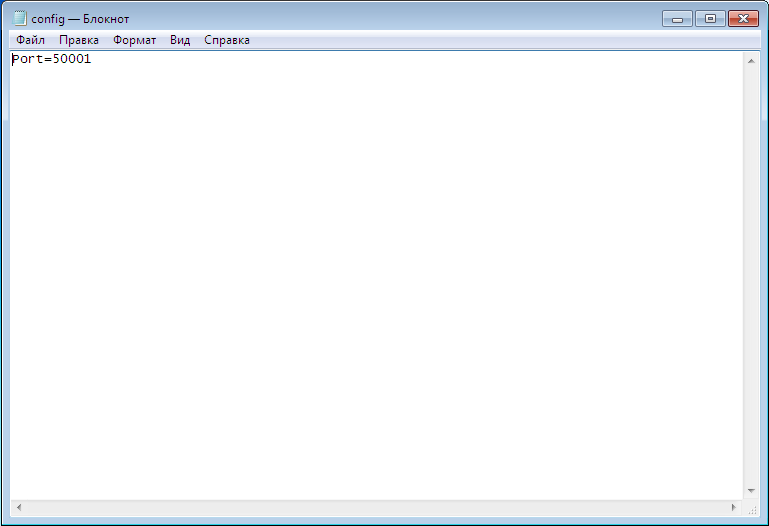
Fig. 10. The contents of the config.txt file
Now let's complicate the task to the Advanced EFS Data Recovery program , namely, delete the personal certificate. Log in as the user who created the encrypted folder and start the mmc console, select the menu command File, Add or Remove Snap-in . Next, select the Certificates snap-in and click the Add button (Figure 11). In the window that appears, select my user account (Fig. 12).

Fig. 11. Adding snap-in

Fig. 12. Equipment of the certificate manager.
Next, click OK and in the window that appears, go to Certificates, Personal, Certificates. You will see the created certificates for the current user (Fig. 13). In my case, the user is called a test . Right-click on its certificate and select Delete to remove the certificate. You will see a warning that decrypting data encrypted with this certificate will no longer be possible. Well, we'll check it out soon.
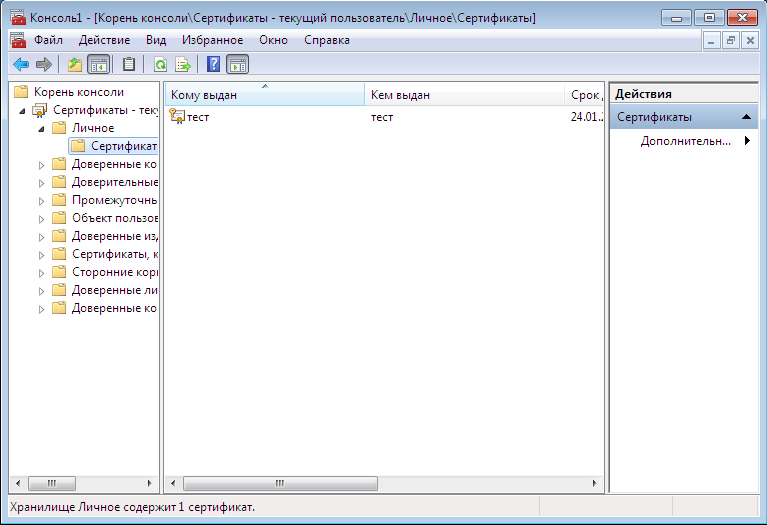
Fig. 13. Personal certificates

Fig. 14. Warning when deleting a certificate
Next, follow these steps:
- Close the snap-in and try to access the encrypted file. Nothing will work out for you, despite the fact that you encrypted this file. After all, the certificate is then deleted.
- Change user, run the Advanced EFS Data Recovery program. Try decrypting the file as shown earlier. First, the program will report that the certificate was not found. Therefore, you need to go to the EFS related files tab and click the Scan for keys button . After a while, the program will tell you that it found the keys, but probably not all (Fig. 15). The program recommends that you scan the keys again, but this time with the Scan by sectors option turned on (Fig. 16), but I did not do this and immediately switched to the Encrypted files tab . The program successfully found and decrypted the file. In fig. Figure 17 shows that I already saved the decrypted file to the desktop.

Fig. 15. Search for keys
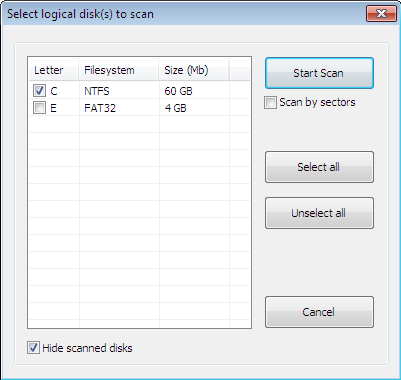
Fig. 16. Scan window
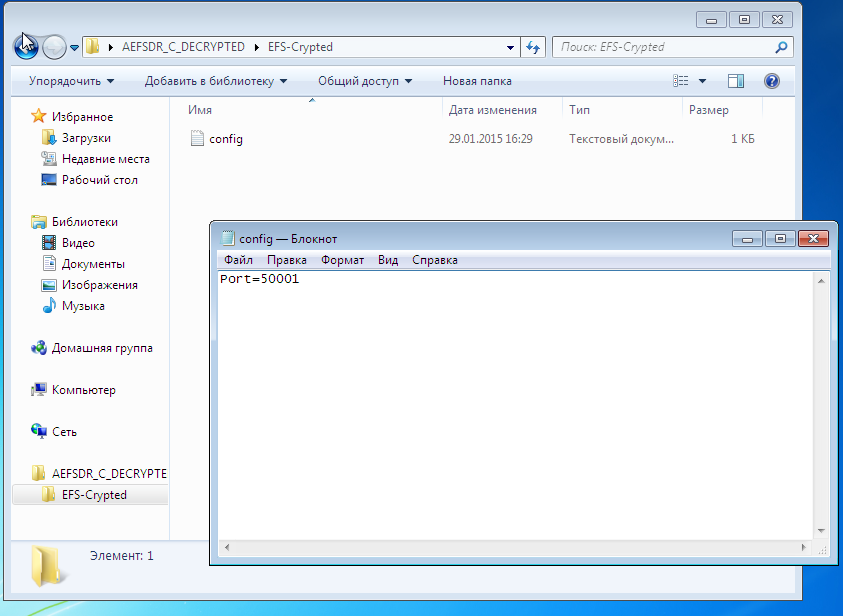
Fig. 17. The file is again decrypted.
To the shame of EFS or to the honor of Advanced EFS Data Recovery, in both cases the file was decrypted. At the same time, as you see, I did not need any special knowledge or skills. It is enough to run a program that will do all the work for you. You can read about how the program works on the developers website (http://www.elcomsoft.ru/), we won’t discuss the principle of its operation in this article, since AEFSDR is not the subject of the article.
In fairness, I must say that specialists can configure the system so that Advanced EFS Data Recovery will be powerless. However, we looked at the most common use of EFS for the vast majority of users.
Transparent encryption system implemented in CyberSafe Top Secret
Let's see how transparent encryption is implemented in CyberSafe. For transparent encryption, the Alfa Transparent File Encryptor driver (http://www.alfasp.com/products.html) is used, which encrypts files using the AES-256 algorithm or GOST 28147-89 algorithm (when using Crypto-Pro).
The encryption rule (file mask, allowed / forbidden processes, etc.), as well as the encryption key, is transmitted to the driver. The encryption key itself is stored in the ADS folder (Alternate Data Streams, eb.by/Z598 ) and encrypted using OpenSSL (RSA algorithm) or GOST R 34.10-2001 - certificates are used for this.
The logic is as follows: add a folder, CyberSafe creates a key for the driver, encrypts it with selected public certificates (they must be previously created or imported into CyberSafe). When someone tries to access a folder, CyberSafe opens the ADS folder and reads the encrypted key. If this user has a private certificate key (he can have one or several of his certificates), which was used to encrypt the key, he can open this folder and read the files. It should be noted that the driver decrypts only what is needed, and not all files when providing access to the file. For example, if a user opens a large Word document, then only the part that is now loaded into the editor is decrypted, the rest is loaded as necessary. If the file is small,
If the folder is network shared, then the files in it remain encrypted, the client driver decrypts only the file or part of the file in memory, although this is also true for the local folder. When editing a file, the driver encrypts the changes in memory and writes to the file. In other words, even when the folder is on (it will be shown later what it is), the data on the disk always remains encrypted.
Using CyberSafe Top Secret to transparently encrypt files and folders
It is time to consider the practical use of CyberSafe Top Secret. To encrypt a folder, go to the Transparent Encryption program section ( File Encryption tab ), see fig. 18. Then, from the Explorer, drag the folders you want to encrypt into the workspace of the program. You can also use the Add button . folder . I added one folder - C: \ CS-Crypted.
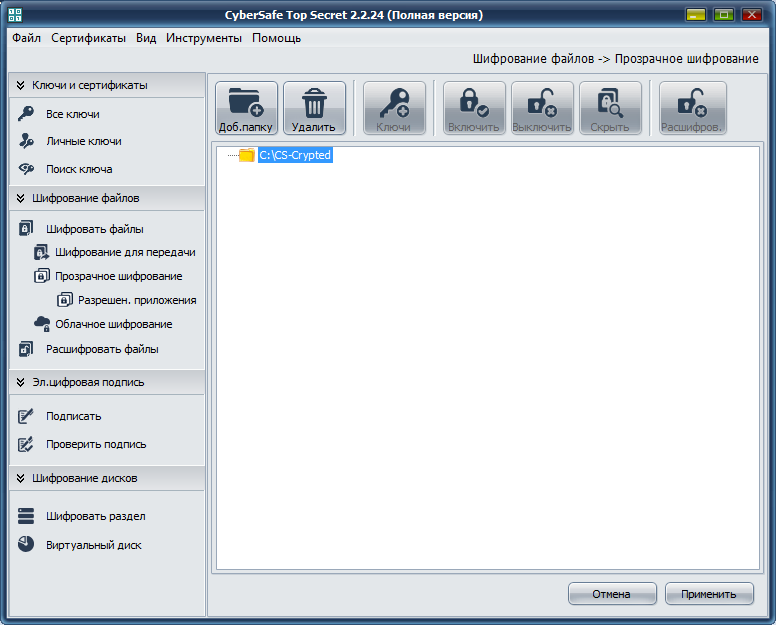
Fig. 18. CyberSafe Top Secret
Click Apply . In the window that appears (Fig. 19), click Yes or Yes for allx (if you are trying to encrypt multiple folders at a time). Next, you will see a window for selecting certificates whose keys will be used for transparent encryption of the folder (Fig. 20). As a rule, certificates are created immediately after installing the program. If you have not already done so, you will have to return to the Private Keys section and click the Create button .

Fig. 19. Click Yes

. Fig. 20. Choosing certificates for transparent encryption.
The next question for the program is whether to install an administrator key for this folder (Fig. 21). Without an administrator key, you cannot make changes to the folder, so click Yes .
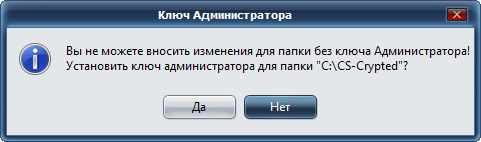
Fig. 21. Again click Yes
After that, you will return to the main program window. Before you start working with an encrypted folder, you need to select it and click the Enable button . The program will ask for the password of the certificate (Fig. 22) specified for encryption of this folder. After that, working with an encrypted folder will not differ from working with a regular folder. In the CyberSafe window, the folder will be marked as open, and a lock icon will appear to the left of the folder icon (Fig. 23).
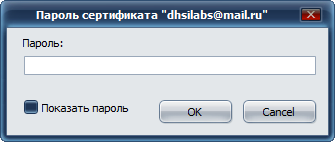
Fig. 22. Enter the certificate password
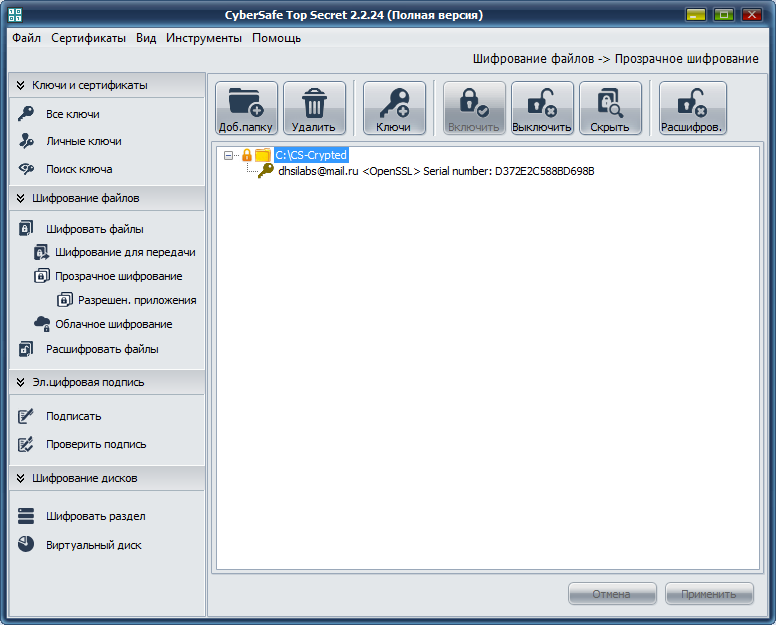
Fig. 23. An encrypted folder is connected.
In Explorer, neither an encrypted folder nor encrypted files are marked in any way. Outwardly, they look the same as other folders and files (unlike EFS, where the names of encrypted files / folders are highlighted in green), see fig. 24.
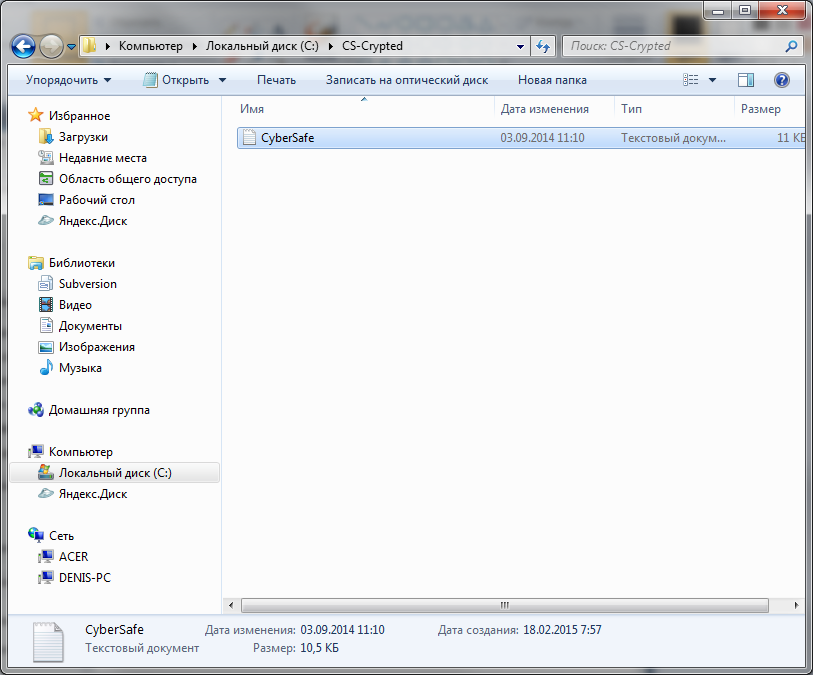
Fig. 24. The encrypted CS-Crypted folder in Explorer
It should be noted that in the same way you can encrypt the network folder. In this case, the CyberSafe program should be located only on the users computer, and not on the file server. All encryption is performed on the client, and already encrypted files are transferred to the server. This decision is more than justified. Firstly, already encrypted data is transmitted over the network. Secondly, even if the server administrator wants to access the files, nothing will come of it, since only users whose certificates were specified during encryption can decrypt the files. But the administrator, if necessary, can back up encrypted files.
When the encrypted folder is no longer needed, you need to go to the CyberSafe program, select the folder and click the Off button. This solution may not seem to you as convenient as EFS - you need to press the on / off buttons. But this is only at first glance. Firstly, the user has a clear understanding that the folder is encrypted and he will not forget about this fact when he reinstalls Windows. Secondly, when using EFS, if you need to leave the computer, you need to log out, because during your absence, anyone can go to the computer and access your files. All he will need to do is copy your files to a device that does not support encryption, for example, to a FAT32 flash drive. Then he will be able to view files outside your computer. With CyberSafe, everything is a little more convenient. Yes, you need to take an additional action (“turn off” the folder) and all encrypted files will become inaccessible.
However, each product has its own characteristics. CyberSafe is no exception. Imagine that you encrypted the C: \ CS-Crypted folder and put the report.txt file there. When the folder is turned off, of course, you cannot read the file. When the folder is turned on , you can access the file and, accordingly, copy it to any other, unencrypted folder. But after copying the file to an unencrypted folder, he continues to live his own life. On the one hand, it is not as convenient as in the case of EFS, on the other hand, knowing such a feature of the program, the user will be more disciplined and will only keep his secret files in encrypted folders.
Performance
Now let's try to find out which is faster - EFS or CyberSafe Top Secret. All tests are carried out on a real machine - no virtual machines. The configuration of the laptop is as follows - Intel 1000M (1.8 GHz) / 4 GB RAM / WD WD5000LPVT (500 GB, SATA-300, 5400 RPM, 8 MB / Windows 7 64-bit buffer). The car is not very powerful, but what it is.
The test will be extremely simple. We will copy the files to each of the folders and see how long it takes to copy. To find out which transparent encryption tool is faster, the following simple scenario will help us:
@echo off
echo "Копирование 5580 файлов в EFS-Crypted"
echo %time%
robocopy c:\Joomla c:\EFS-Crypted /E > log1
echo %time%
echo "Копирование 5580 файлов в CS-Crypted"
echo %time%
robocopy c:\Joomla c:\CS-Crypted /E > log2
echo %time%
You don't need to be a programming guru to figure out what this script does. It's no secret that we often work with relatively small files with sizes ranging from several tens to several hundred kilobytes. This script copies the distribution of Joomla! 3.3.6, in which there are 5580 such small files, first to the folder encrypted by EFS, and then to the folder encrypted by CyberSoft. Let's see who will be the winner.
The robocopy command is used to recursively copy files, including empty files (/ E option), and its output is deliberately redirected to a text file (if you wish, you can see what was copied and what wasn’t) so as not to clog the script output.
The results of the second test are shown in Fig. 25. As you can see, EFS completed this task in 74 seconds, and CyberSoft in just 32 seconds. Given that in most cases, users work with many small files, CyberSafe will be more than twice as fast as EFS .

Fig. 25. Test results
Benefits of CyberSafe Transparent Encryption
Now a little summary. The advantages of transparent encryption CyberSafe include the following facts:
- When you turn off the folder, files can be copied in encrypted form anywhere, which allows you to organize cloud encryption .
- The CyberSafe driver allows you to work over the network, which makes it possible to organize corporate encryption .
- To decrypt a folder, not only do you need to know the password, you must have the appropriate certificates. When using Crypto-Pro, the key can be transferred to the token.
- The CyberSafe application supports the AES-NI instruction set, which positively affects the performance of the program (it was proved by tests above).
- You can protect yourself from unauthorized access to private keys using two-factor authentication.
- Trusted Application Support
The last two benefits deserve special attention. To protect against access to the user's private keys, you can protect the CyberSafe program itself. To do this, execute the Tools, Settings command (Fig. 26). In the Settings window on the Authentication tab, you can enable either password authentication or two-factor authentication. Details on how to do this, please read the manual for CyberSafe Program on page 119.
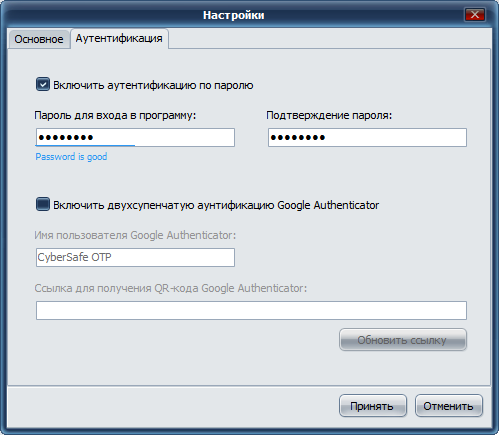
Fig. 26. Protection of the CyberSafe program itself
On the Allowed tab . applicationsYou can identify trusted applications that are allowed to work with encrypted files. By default, all applications are trusted. But for greater security, you can specify applications that are allowed to work with encrypted files. In fig. 27 I have indicated as trusted applications MS Word and MS Excel. If some other program tries to access the encrypted folder, it will be denied access. You can find more information in the article “Transparent file encryption on the local computer using CyberSafe Files Encryption” (http://habrahabr.ru/company/cybersafe/blog/210458/).

Fig. 27. Trusted applications
That's all. We recommend that you read the following articles:
Transparent encryption of files on the local computer using CyberSafe Files Encryption
Transparent encryption of network folders in the corporate space
Methods of information hiding
Encryption of cloud services in companies and organizations
