CTB-Locker - a new modification of the FileCoder ransomware trojan
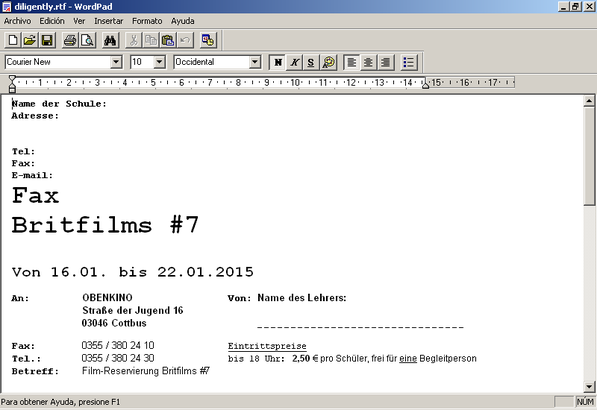
We have already written several times about various families of encryption trojans. We are talking about modifications to the FileCoder malware family, as well as the Win32 / Virlock ransomware . A few days ago, our antivirus lab began receiving messages about a malicious campaign targeting users in Latin America and Eastern Europe. Phishing e-mail messages contained information about the “arrived fax”. The attachments of such messages contained malware that specializes in encrypting user files and demanding a ransom for decryption in bitcoins.

An example of such a malicious message is shown in the screenshot below.

In this post, we will look at a malicious campaign to distribute this malicious program, which has spread in Poland, the Czech Republic, Mexico and many other countries.
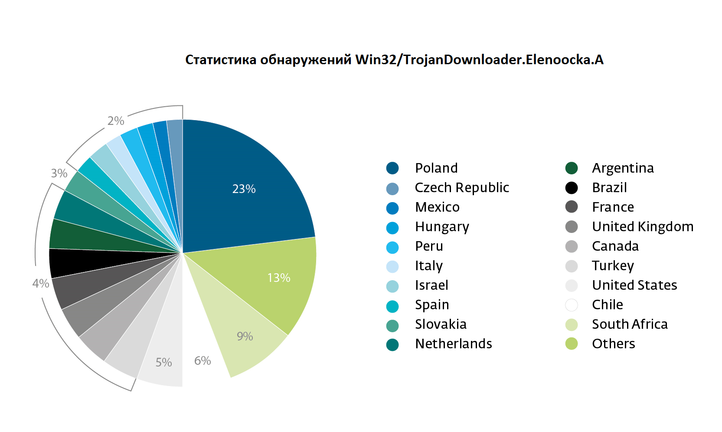
As we mentioned above, the main vector of distribution of CTB-Locker is a phishing email message. The malicious executable file, which is located in the attachment to the message, is detected by ESET AV products as Win32 / TrojanDownloader.Elenoocka.A . This bootloader (or downloader) downloads the above-mentioned FileCoder (CTB-Locker) modification to the user's computer. This modification is detected as Win32 / FileCoder.DA . After starting this malware, the files on the disk are encrypted.
CTB ‑ locker itself is similar to another well-known ransomware calledCryptoLocker . The difference between them is the use of various file encryption algorithms. The result of CTB ‑ locker is similar to CryptoLocker or TorrentLocker , i.e., it encrypts files with the extensions mp4, .pem, .jpg, .doc, .cer, .db. After the file encryption operation is completed, the malware displays a warning message to the user. For this purpose, the CTB ‑ locker can personalize the user's desktop, that is, change the wallpaper there to the following.
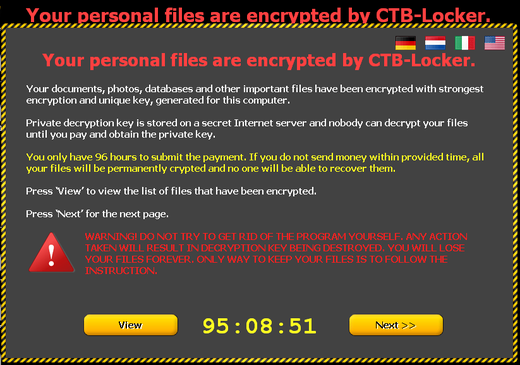
The ransomware supports the display of text in various languages, including German, Dutch, Italian, English. There is no Spanish in the list of supported languages, although we observed infections with this malware in those countries for which this language is the main one.
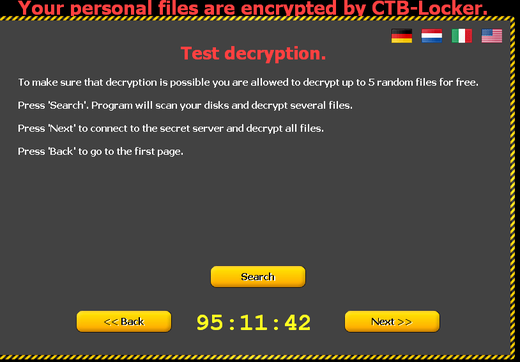
CTB-Locker is distinguished by the fact that attackers use a special method to convince the user to pay the ransom. They demonstrate to him what will happen after his payment, that is, they convince the user that they will not deceive him and decrypt the files.
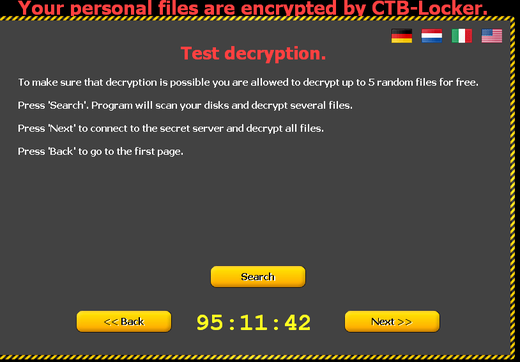
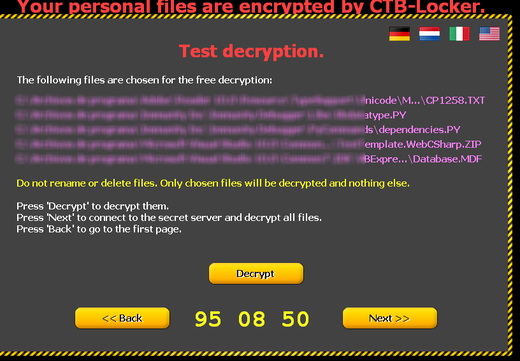
After that, the user will be shown how he can decrypt the files and on what account he will need to transfer bitcoins for this.
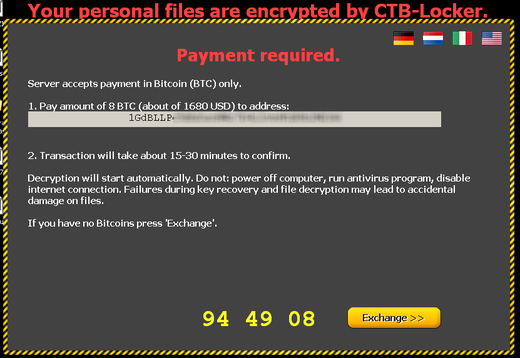
As can be seen above in the screenshot, CTB-Locker can demonstrate the exchange rate of bitcoins based on the currency that corresponds to the location of the locked computer. At the time of the screenshot, eight bitcoins were worth $ 1,680.
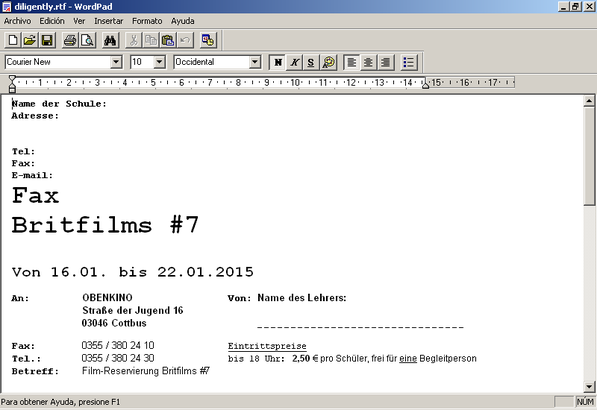
From a technical point of view, the ransomware downloader itself, which is detected as Win32 / TrojanDownloader.Elenoocka.A, is a fairly small in size and simple from a technical point of view malicious program. We have observed the use of this downloader by cybercriminals in other malicious campaigns. One of these campaigns used phishing e-mail messages, which included malicious files with the names invoice_% YEAR_% MONTH_% DAY-1% HOUR_% MIN.scr (e.g. invoice_2015_01_20-15_33 .scr). To mask its launch in the system, the executable file contains a fake Word document in its resources, which will be shown to the user in the background of the execution of the malicious file.
The CTB-Locker malware belongs to the type of ransomware after which it is impossible to decrypt files without a key obtained from cybercriminals. As we have repeatedly emphasized, the use of backup is the main method that can be used to recover data after the activity of such malware, in addition, timely updating of anti-virus databases is also a necessary measure to prevent infection.

An example of such a malicious message is shown in the screenshot below.

In this post, we will look at a malicious campaign to distribute this malicious program, which has spread in Poland, the Czech Republic, Mexico and many other countries.
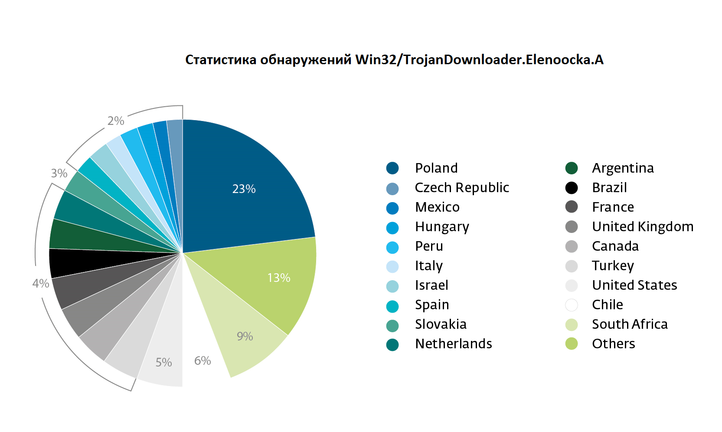
As we mentioned above, the main vector of distribution of CTB-Locker is a phishing email message. The malicious executable file, which is located in the attachment to the message, is detected by ESET AV products as Win32 / TrojanDownloader.Elenoocka.A . This bootloader (or downloader) downloads the above-mentioned FileCoder (CTB-Locker) modification to the user's computer. This modification is detected as Win32 / FileCoder.DA . After starting this malware, the files on the disk are encrypted.
CTB ‑ locker itself is similar to another well-known ransomware calledCryptoLocker . The difference between them is the use of various file encryption algorithms. The result of CTB ‑ locker is similar to CryptoLocker or TorrentLocker , i.e., it encrypts files with the extensions mp4, .pem, .jpg, .doc, .cer, .db. After the file encryption operation is completed, the malware displays a warning message to the user. For this purpose, the CTB ‑ locker can personalize the user's desktop, that is, change the wallpaper there to the following.
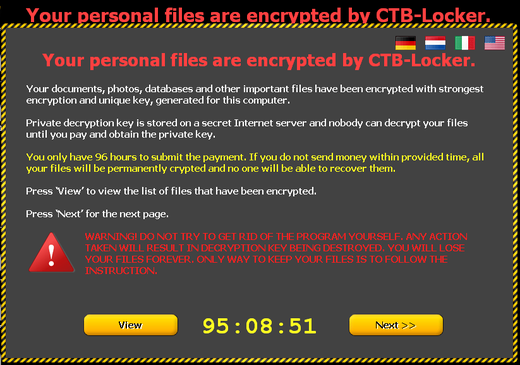
The ransomware supports the display of text in various languages, including German, Dutch, Italian, English. There is no Spanish in the list of supported languages, although we observed infections with this malware in those countries for which this language is the main one.
CTB-Locker is distinguished by the fact that attackers use a special method to convince the user to pay the ransom. They demonstrate to him what will happen after his payment, that is, they convince the user that they will not deceive him and decrypt the files.
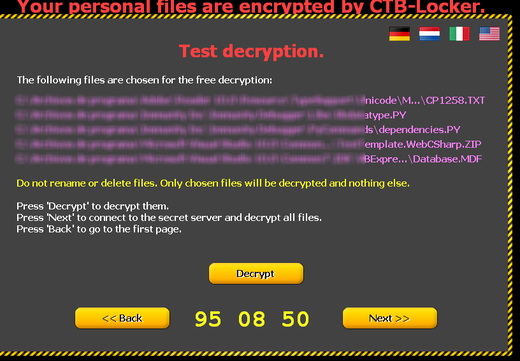
After that, the user will be shown how he can decrypt the files and on what account he will need to transfer bitcoins for this.
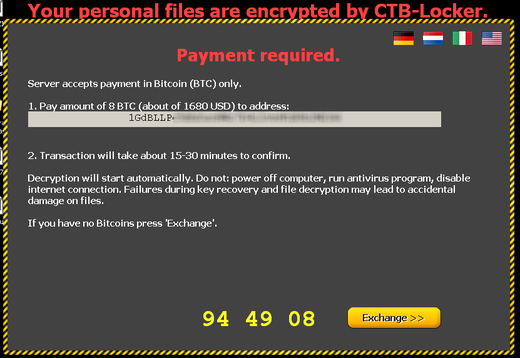
As can be seen above in the screenshot, CTB-Locker can demonstrate the exchange rate of bitcoins based on the currency that corresponds to the location of the locked computer. At the time of the screenshot, eight bitcoins were worth $ 1,680.
From a technical point of view, the ransomware downloader itself, which is detected as Win32 / TrojanDownloader.Elenoocka.A, is a fairly small in size and simple from a technical point of view malicious program. We have observed the use of this downloader by cybercriminals in other malicious campaigns. One of these campaigns used phishing e-mail messages, which included malicious files with the names invoice_% YEAR_% MONTH_% DAY-1% HOUR_% MIN.scr (e.g. invoice_2015_01_20-15_33 .scr). To mask its launch in the system, the executable file contains a fake Word document in its resources, which will be shown to the user in the background of the execution of the malicious file.
The CTB-Locker malware belongs to the type of ransomware after which it is impossible to decrypt files without a key obtained from cybercriminals. As we have repeatedly emphasized, the use of backup is the main method that can be used to recover data after the activity of such malware, in addition, timely updating of anti-virus databases is also a necessary measure to prevent infection.
