Artificial Intelligence, Import Substitution, and Other Application Security Features

The security of Russian information systems is falling every year: in 2014, 77% of critical applications of large companies and state-owned enterprises contained dangerous vulnerabilities. The course on import substitution complicates the situation even more: it is necessary to build systems from “raw” domestic software. To meet these security challenges, a new generation of protective solutions is needed that combines a serious scientific approach and a high degree of automation for early detection of threats. Positive Technologies experts shared these and other observations with reporters at a press conference on application security.
Despite 15 years of experience in the information security market, the company rarely holds such public presentations for the media. One of the reasons for the “disclosure” was a recent IDC study, according to which Positive Technologies took third place in the security software market in Russia. After the publication of this report, it became clear that for some journalists, “security software” is a synonym for “antivirus”, since they are much less familiar with other security technologies - including security analysis systems, compliance control standards, code analyzers, application protection systems.
Experts decided to tell reporters about these technologies. Moreover, there was another reason: Positive Technologies recently released a new line of products for protecting applications in a wide variety of industries, including Internet banking and ERP systems, government services portals and telecom web services. It is possible that these developments will seriously change the information security market - both Russian and world.
They started, however, from afar. The first to speak was Boris Simis, PT's Deputy General Director for Business Development. He spoke about the history of the company, which set the task of collecting the best hackers and the largest vulnerability database for analyzing the security of large companies. “Our guys can hack everything that moves! The main thing is to direct this energy into a peaceful direction, ”said Boris.

Currently, the main offices of researchers and developers of Positive are located in Moscow and St. Petersburg, and the regional sales and support network covers the USA, Great Britain, Europe, India, South Korea, North Africa and the Persian Gulf countries.
At the same time, according to the observations of Boris Simis, the development of information security business abroad is taking place more actively due to the good awareness of customers: they already know what threats exist and what means of protection are available, and in fact they speak the same language with software manufacturers. In Russia, the management of enterprises has a much worse idea of information security; protective products are often implemented formally, without understanding the situation.
The topic of awareness was continued in her report by the head of the analytics department of the company Evgenia Potseluevskaya, who said that now such a term has appeared - “sellers of fear”. This is what some IB analysts are called, accusing them of artificially escalating panic. However, Positive Technologies is different in that it collects its data in the course of real penetration tests. And in relation to real vulnerabilities, the situation in 2014 deteriorated quite naturally - companies are more active on the Internet and use more applications, but they are not in a hurry to investigate the security of these applications. Here's what the top vulnerabilities look like this year:

A full 2014 vulnerability study, the data of which were presented at a press conference, will be published a little later; 2013 studies can be foundon the company website . Evgeniya Potseluevskaya also presented the vulnerability statistics of popular open source systems. There is a myth that the very fact of using the open source model makes products “more secure”, but in practice this is not always the case.
The speech of Sergey Gordeychik, Positive Technologies Deputy Director General for Technology Development, consisted of two parts. In the first part, Sergey told why modern application protection tools cannot cope with new threats. And in the second - about what is import substitution in the Russian IT industry in terms of security.
According to the expert, it will not be possible to replace the hardware base and system software for a long time, so they become “untrusted products”, which may contain bookmarks of a foreign manufacturer. And the replacement of high-level software will occur with the help of domestic products created in a hurry, not passed enough testing and often use third-party code. As a result, a high-risk situation is created, or “H6 intruder model” (when the intruder is already in the system, but has not yet begun active actions).
Such a situation will require modern security approaches. Sergey Gordeychik presented the following trends, the development of which can change the AppSec market:
- code security control at all stages, through the automation of secure development (SSDL);
- combination of approaches, in particular a combination of various methods of code analysis;
- Automation of vulnerability checks, for example, by generating exploits — special requests that show how this vulnerability is “included”;
- behavioral analysis and self-training, that is, the creation of a model of the “correct” system operation, followed by analysis of deviations;
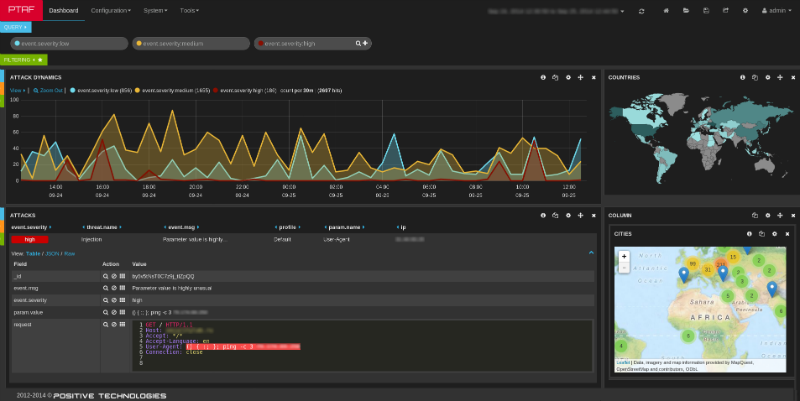
- Intelligent threat processing, including a grouping and visualization of events that will allow information security experts to receive the most important messages (for example, attack chains) instead of a complete list of thousands of operations;
- closing gaps before correcting the code using virtual patch at the firewall level;
- integration of security tools into a common ecosystem, including the interaction of a firewall with code analyzers, antiviruses, DLP systems and other security tools.

Then, Denis Baranov, director of application security at the company's research center, spoke about the practical implementation of the above protection principles in two new products. The PT Application Inspector system, whose abbreviation (AI) does not coincide with the abbreviation “artificial intelligence”, combines static (SAST), dynamic (DAST) and interactive (IAST) methods for analyzing application security. And the result of the analyzer is exploits that show developers exactly how to fix the code.
The same exploits can eliminate the threat before the code is fixed: they are transferred to another company product - the PT Application Firewall, which uses them for virtual patching. In addition, PT AF uses behavioral traffic analysis to identify new attacks for which there are no signatures yet. Denis showed how the firewall, even in its basic configuration zadetektiroval attack ShellShosk . As the last speech at the press conference, a video review of the client was shown: the leading specialist of the information security department of MegaFon OJSC Sergey Khimanych spoke about the use of Positive Technologies to protect the web services of one of the largest Russian telecom operators.
“We studied the products of various companies, including leaders of the foreign market, but preferred the Russian solution PT Application Firewall,” a representative of MegaFon said. “Thanks to this system, we can monitor and block attacks on our applications in real time, while maintaining a high level of security for millions of subscribers.”
During the Q&A session, the journalists were most interested in further plans of the company, as well as the ways in which the company attracted hackers “to the bright side”. Boris Simis and Sergey Gordeychik believe that the main thing in this matter is the sooner the better. They spoke, in particular, about the Positive Education program.thanks to which students from 50 leading Russian universities can use the company's training materials when studying practical safety.
On the way to the buffet, company experts arranged a tour for their journalists at the office. There was a hacked ATM, a supercomputer for selecting encryption keys, and many other amazing things. Want to see? - Come to the next “Positive” press conference!

