Attacks on SS7: yesterday for special services, today for everyone
At the end of August, the Washington Post published a booklet of the American company Verint, which offers its customers Skylock service for tracking mobile network subscribers around the world - without the knowledge of the subscribers and operators themselves. Although offers of location services can be found on the Internet for a long time, but the Verint case is perhaps one of the first when such services are offered quite officially and globally.
How is this possible? In response to stories about mobile surveillance, the version about complex technologies that can only be used by intelligence agencies is most often put forward. In practice, everything is simpler. A telecommunication network consists of many subsystems of various technological levels, and the security level of the entire network is often determined by the level of the weakest link.
In particular, the process of establishing voice calls is still based on SS7 technology, which is rooted in the 70s of the last century. In the early 2000s, the SIGTRAN specification was developed , which allows SS7 messages to be transmitted over IP networks. At the same time, all the security flaws of the upper layers of the SS7 protocols were inherited. As a result, attackers have the ability to send, intercept and modify SS7 protocol messages uncontrollably, carrying out various attacks on mobile networks and their subscribers.
One of the first public reports on SS7 vulnerabilities soundedin 2008, at the Chaos Computer Club hacker conference, where German researcher Tobias Engel showed a technique for tracking subscribers of mobile networks. However, in the professional environment, these vulnerabilities have been known before - since 2001 . Even then, the governments of some countries knew about these opportunities. So, in the book by Thomas Porter and Michael Gough “How to Bypass VoIP Security” (How to Cheat at VoIP Security), a quote from a report by one of the US agencies states that “the US Presidential Administration is seriously concerned about the high level of threat of attacks based on SS7” .
A new surge of public concern occurred in 2013, when former CIA officer Edward Snowden revealed to the world the story of total surveillance by the US National Security Agency for citizens. Among Snowden's revelations, SS7 vulnerabilities again surfaced as one of the techniques used by the NSA. After that, it became known about the existence of private companies that offer similar services at the global level, as the already mentioned SkyLock:
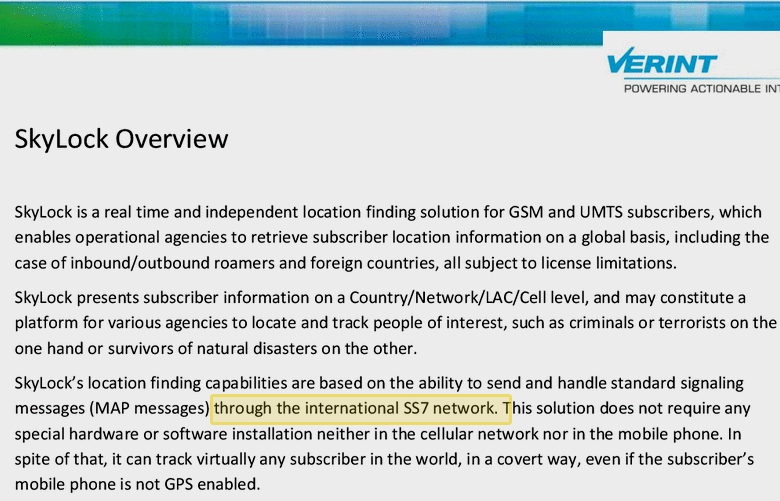
According to the Washington Post, Verint does not use surveillance against American and Israeli citizens, “however, a number of other similar services operating in Switzerland and in Ukraine, they are not subject to such restrictions. ”
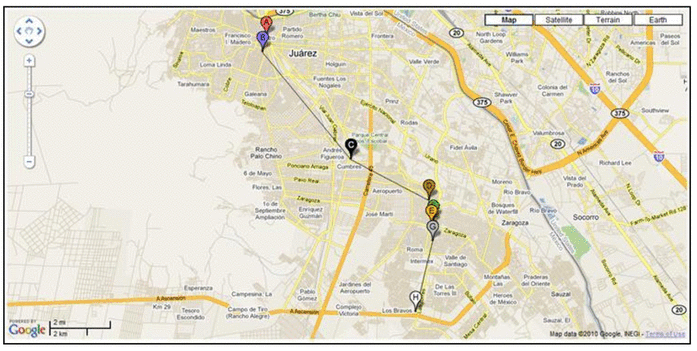
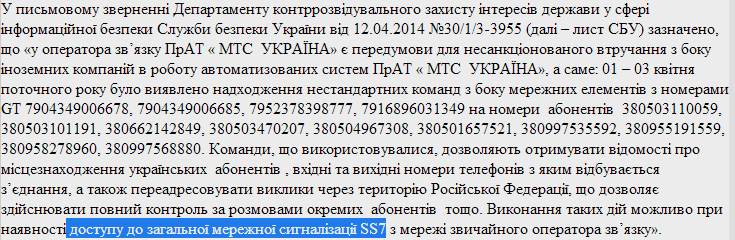
The above quote is one of the possible explanations for a whole wave of scandals related to the publication of records of telephone conversations in Ukraine. In June 2014, the National Communications and Informatics Regulatory Commission of Ukraine reported cases of wiretapping of MTS-Ukraine subscribers through a server allegedly belonging to the Russian “daughter” of Tele2:
According to Positive Technologies experts, the wiretapping algorithm used in this case is a combination of attacks that were discussed at the PHDays IV Practical Safety Conference , as well as in selected publications of our blog. Now all these attacks are compiled and described in more detail in the new study, “Vulnerabilities in Mobile Networks Based on SS7”. See the full study here:www.ptsecurity.ru/lab/analytics The
materials presented in this report were collected in 2013 and 2014 in the course of consulting work on the security analysis of large mobile operators. During this study, Positive Technologies experts were able to implement such attacks as disclosing a subscriber’s location, violating subscriber’s availability, intercepting SMS messages, forging USSD requests and transferring funds with them, forwarding voice calls, eavesdropping on conversations, and disrupting the availability of a mobile switch.
At the same time, it was demonstrated that even telecom operators, members of the top ten world leaders, are not protected from such attacks. And an attacker today does not need sophisticated equipment to carry out these attacks: the study used a node based on a regular computer running Linux family of OS, with the SDK installed to form SS7 packets - these programs are available for free download on the Internet.
Options for solving the problem are proposed in the final chapter of the study . In addition, if you have questions about this study, you can ask the report authors at the webinar, which will be held on October 2 at 14:00 on the company's website.
The webinar is free, but you must first register:
www.ptsecurity.ru/lab/webinars
