Researcher Demonstrates Interception of Aircraft Control Using Android Application
- Transfer
Today at the Hack In The Box conference in Amsterdam, a report was made by Hugo Teso, a security consultant at n.runs AG, about a completely reliable scenario of hijacking an airplane using a simple Android application.
Teso has been working in the IT industry for the past 11 years, but even more time he is a commercial pilot, which allowed him to combine his two professions and study the state of affairs with the security of aviation computer systems and communication protocols.

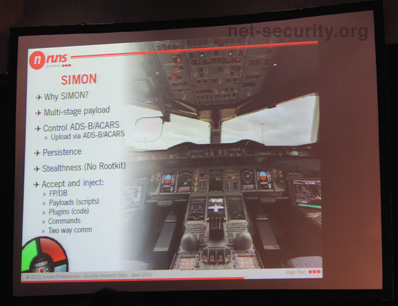
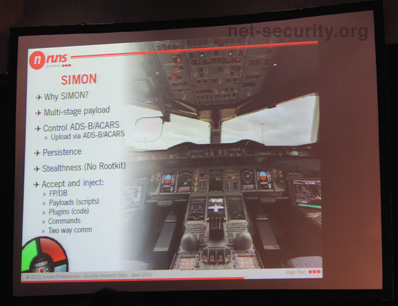
Taking advantage of two new aviation systems for vulnerability detection, information collection and exploitation, creating a framework (SIMON) and an Android application (PlaneSploit) that deliver an attacking message to the flight management system of the aircraft (Flight Management Systems), he demonstrated the ability to gain complete control over the aircraft making the virtual plane "dance to its own tune."
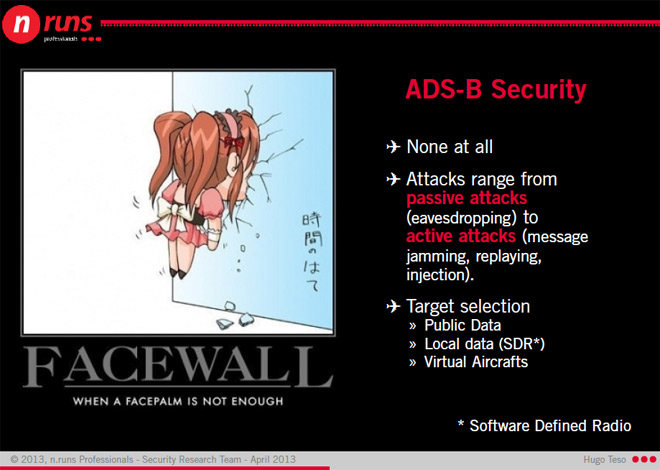
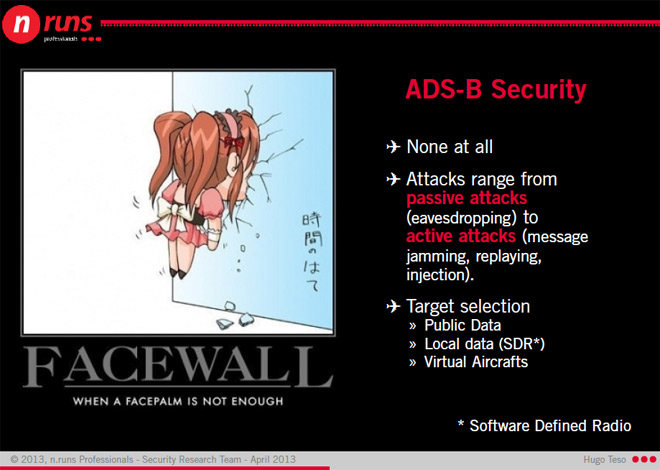
One of the two technologies that he abused is Automatic Dependent Surveillance-Broadcast (ADS-B). It sends information about each aircraft (identifier, current position, altitude, etc.) through the on-board transmitter to the air traffic controller, allowing airplanes equipped with this system to receive flight and weather information about all other vessels currently in the air in the current area .
The second is the Aircraft Communications Addressing and Reporting System (ACARS), which is used to exchange messages between the aircraft and the dispatcher by radio or satellite, and also to automatically deliver information about each phase of the flight to the center.
Both of these technologies are extremely unsafe and susceptible to a number of passive and active attacks. Teso used ADS-B to select a target, and ACARS to collect information about the on-board computer, as well as to crack its vulnerabilities by sending a fake malicious message.
Based on his own research, Teso developed the SIMON framework, which he intentionally made working only in a virtual environment, so it cannot be used on real airplanes. His test lab consists of a set of software and hardware, but the means of connection and communication, as well as hacking methods, are exactly the same that could be used in real life.
Since it is almost impossible to detect the framework in the Flight Management System, there is no need to disguise it as a rootkit. Using SIMON, an attacker can download certain malicious code to a remote FSM, download flight plans, detailed commands, or even their own plugins that can be developed for the framework.
To make it even more interesting - or simple - Tesco showed an Android app that uses SIMON to remotely control an airplane in motion. The application, intricately named PlaneSploit, has a simple interface packed with various features. And this is a worthy example of technological evolution - ten years ago we did not have phones with color screens, and today we are cracking planes from smartphones.
PlaneSploit uses the Flightradar24 tracker and you can tap on any aircraft in the area. In a virtual environment, the distance of the aircraft does not matter, but in the real world everything will depend on the antenna used (if we are talking directly about the aircraft) or the system (if you use ACARS, such as SITA or ARINC).
The user interface of the application is divided into functions: detection, information collection, operation and post-operation. The attacker can click on any active aircraft and get its identifier, current position and end point of the flight. If the aircraft system is hackable (the researcher indicated a number of attack vectors, but did not particularly discuss methods), the application warns the user with a message or push notification. The payload can be downloaded with a simple tap, and from that moment the flight control system is remotely controlled by a hacker. Hacking other FMS related systems is also possible.
Teso at the conference showed some functionality of his application:
Teso, for obvious reasons, did not disclose many details about the tools that he used to attack, and vulnerabilities that have yet to be fixed. However, he notes that he was pleasantly surprised by the industry’s reaction to his research, which did not deny its existence, but promised to help him in his research.

He notes that old systems that originate in the 70s will be difficult, if at all possible, to fix, but new ones just patch with new firmware and changes in programs.
The solution for pilots to regain control of the aircraft is still simple - an attack of this kind only works when autopilot is on, so it just needs to be turned off, after which it landed on “analog instruments”.
The bad news is that there are not so many new planes, and pilots must understand that the computer is hacked in order to carry out maneuvers.
Teso has been working in the IT industry for the past 11 years, but even more time he is a commercial pilot, which allowed him to combine his two professions and study the state of affairs with the security of aviation computer systems and communication protocols.

Taking advantage of two new aviation systems for vulnerability detection, information collection and exploitation, creating a framework (SIMON) and an Android application (PlaneSploit) that deliver an attacking message to the flight management system of the aircraft (Flight Management Systems), he demonstrated the ability to gain complete control over the aircraft making the virtual plane "dance to its own tune."
One of the two technologies that he abused is Automatic Dependent Surveillance-Broadcast (ADS-B). It sends information about each aircraft (identifier, current position, altitude, etc.) through the on-board transmitter to the air traffic controller, allowing airplanes equipped with this system to receive flight and weather information about all other vessels currently in the air in the current area .
The second is the Aircraft Communications Addressing and Reporting System (ACARS), which is used to exchange messages between the aircraft and the dispatcher by radio or satellite, and also to automatically deliver information about each phase of the flight to the center.
Both of these technologies are extremely unsafe and susceptible to a number of passive and active attacks. Teso used ADS-B to select a target, and ACARS to collect information about the on-board computer, as well as to crack its vulnerabilities by sending a fake malicious message.
Based on his own research, Teso developed the SIMON framework, which he intentionally made working only in a virtual environment, so it cannot be used on real airplanes. His test lab consists of a set of software and hardware, but the means of connection and communication, as well as hacking methods, are exactly the same that could be used in real life.
Since it is almost impossible to detect the framework in the Flight Management System, there is no need to disguise it as a rootkit. Using SIMON, an attacker can download certain malicious code to a remote FSM, download flight plans, detailed commands, or even their own plugins that can be developed for the framework.
To make it even more interesting - or simple - Tesco showed an Android app that uses SIMON to remotely control an airplane in motion. The application, intricately named PlaneSploit, has a simple interface packed with various features. And this is a worthy example of technological evolution - ten years ago we did not have phones with color screens, and today we are cracking planes from smartphones.
PlaneSploit uses the Flightradar24 tracker and you can tap on any aircraft in the area. In a virtual environment, the distance of the aircraft does not matter, but in the real world everything will depend on the antenna used (if we are talking directly about the aircraft) or the system (if you use ACARS, such as SITA or ARINC).
The user interface of the application is divided into functions: detection, information collection, operation and post-operation. The attacker can click on any active aircraft and get its identifier, current position and end point of the flight. If the aircraft system is hackable (the researcher indicated a number of attack vectors, but did not particularly discuss methods), the application warns the user with a message or push notification. The payload can be downloaded with a simple tap, and from that moment the flight control system is remotely controlled by a hacker. Hacking other FMS related systems is also possible.
Teso at the conference showed some functionality of his application:
- flight to the point set by the hacker;
- the task of filters - points in space, when approaching which the plane will do something;
- meeting with the earth;
- warning pilots about problems.
Teso, for obvious reasons, did not disclose many details about the tools that he used to attack, and vulnerabilities that have yet to be fixed. However, he notes that he was pleasantly surprised by the industry’s reaction to his research, which did not deny its existence, but promised to help him in his research.

He notes that old systems that originate in the 70s will be difficult, if at all possible, to fix, but new ones just patch with new firmware and changes in programs.
The solution for pilots to regain control of the aircraft is still simple - an attack of this kind only works when autopilot is on, so it just needs to be turned off, after which it landed on “analog instruments”.
The bad news is that there are not so many new planes, and pilots must understand that the computer is hacked in order to carry out maneuvers.
