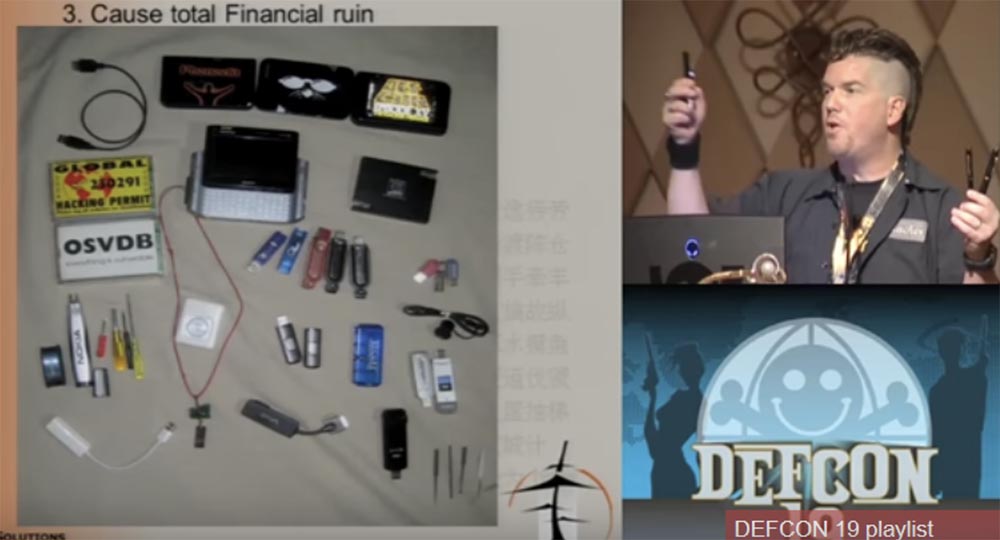
Conference DEFCON 19. "Steal everything, kill everyone, cause a complete financial collapse!" Jason I. Street
- Transfer
I want you to understand why I begin my speech from this slide. I want to say how little you know, if you think that bad always means mean, hateful, and good is always nice and fluffy. I want you to remember this kitten picture when I start telling you really awful things.
My presentation is called “Steal everything, kill everyone, cause a complete financial collapse, or how I entered and misbehaved!” Simply because it tells about the failure of the security system.
The signature on the picture with the kittens reads: “Army of darkness. Milder than you expected. ” The slide with the name of the presentation shows a sign with the inscription “The security guard will return in 5 minutes”.
I'm going to explain to you that physical security issues and everything related to them are our weakest point, because people oppose two-dimensional to three-dimensional and simple to complex, when they approach the entrance doors. You see that Jason I. Street has many more letters after the last name, so let me introduce myself first. I have a day job and a night job. My day job is that I serve as vice president of information security at financial company Stratagem 1 Solutions. I work in an office booth, surrounded by many interesting events. I watch the firewalls, I follow the ID systems, I built our own infrastructure and I find more creative ways to protect it from those people who can “come for us”, and my main job is the “blue team”, that is, protection.
My night job is to serve as the CIO - director of information strategies, and I perform penetration testing about 3 times a year, this is my main job. I speak at such events around the world, I wrote the book “Dissecting the Hack: The F0rb1dd3n Network” in the genre of the documentary detective story, I write articles, and I do all this at night. During the day, I react to incidents, and at night I create incidents for other people, so it is more convenient for both parties.

I love to look at these photos. In this baseball cap and black glasses, I stood for an hour in front of the building of the protected industrial park, on Sunday, in the absence of other traffic, and a guard passed me twice, who did not even ask what I was doing on the sidewalk and why I was inspecting the protected building, and did not record this incident in the report.
In the second photo I’m wearing glasses, I’m just about to apply for a job, here I’m wearing a BlackHat-colored community shirt because I like walking with “warning stickers”. I never got this job because I was not qualified enough, but I managed to get their data. That was my victory.
On the next slide, you see two more photos that I like too.

T-shirt with the inscription, I think the best, because in it I almost stole a car. I was in a hotel on the coast and the parking attendant provided me with a car, but I explained to him that I could not take this car right now, he asked why, and I answered - because I would steal it. Apparently, he bought the inscription on my T-shirt "I am the source of trouble," and decided to give me someone else's car. It took him a while to understand what I mean, so I had to say to him: "You must take her back, because the owner may need it."
The next shirt is my favorite. At one of the most guarded objects I've seen in life, directly opposite Ground Zero, the zero level of the World Trade Center in Manhattan, the SWAT squadron, these K9 with their machine guns, pass through the hall to the main elevator, which is guarded by 8 guards. the upper floors I go to myself in a shirt with the icon "Geek your company." Yes, I like this photo the most, and later I will tell you about this story a little more.
I have a CISSP (information security certificate from a non-profit organization International Information Systems Security Certificates Consortium), and I think that according to the ethical code I should mention that in my presentation I used quotes from the treatise “The Art of War” by Sun Tzu, a Chinese strategist and thinker of the V century.

So, my presentation consists of the following parts:
Introduction;
The fact is one fact that we will encounter when discussing this topic;
Rules - 2 rules that I thought up while doing my job;
Results - we will have as many as 3 results arising from these 2 rules;
Conclusions and / or discussion.
So why this particular topic? I talked about this last year at the 36 CHARGE conference, I talked about the beginning of social engineering, about the things you could do to try to get into a protected building. It was the first part and, to be honest, I received some feedback after that, and I was approached with all sorts of difficult questions.
But I am not an expert in the field of social engineering, I do not know anything about neurolinguistic programming (NLP), I do not know the methods of face recognition or ninja technology. However, I have 100% success in entering buildings, I just go there when I use the skills of this very social engineering. But believe me, I am not strong in it, it is just our modern security.
I think you will not learn anything new from me, so this is rather an educational lecture that will show you the beginning of the path, but I hope that after it you will remember what will force you to look around and take a fresh look at things that seem known to you and improve your perception of the environment.
But now I will not talk about social engineering, so this is all the damage I was able to inflict after your guard allowed me to go through the entrance doors.
So, fact number 1: I sneaked inside! I took this photo as soon as I opened the door and went up to the hall. I saw the door for the staff, this was the door to the protected area, and I just went through it by pressing buttons 1-3-5.

I could press 5-3-1, or 3-1-5, it does not matter, I would still open it, because I pressed the buttons, the surface of which was wiped from frequent use more than others. I returned from there 10 minutes before the start of our meeting, and no one found out that I was there.
Another fun occasion was when I went to get another job. I decided to be a bad guy, and when I signed my name at the reception, I stole a pen from them. Then I asked where their toilet is. This is not because I drink too much dietary cola, I just “get lost” in these large buildings and can wander for hours in search of this toilet, while looking around the entire building.

In search of a toilet, I unexpectedly stumbled upon a protected part of the working area and found an entrance for staff. It looked as if the guard of this object was showing off its security systems worth a million dollars, but when I looked at the door, I saw a little thing, a rod that holds the door latch. If I had a condom, I would adjust it to keep the door from closing. And then I remembered the stolen handle, screwed the cap off it and put it on the rod, and the door did not click. When I returned there 20 minutes after walking through the “forbidden” zone, the cap was still there. No one knew that I was on a guarded object, and it was fun!
So, I am not a locksmith of the highest category, and I do not need to be a master in locks so that people let me through the front door. I don't need to be a super ninja coder to just steal a hard disk with data from your computer. This video shows my hacker skills and a unique master key - the cover of a cardboard folder. I simply insert a sheet of cardboard between the doors of a closed door, take them up and down, and the doors open with such a simple “key”.
Next on the slide is another “key” - a fake email that I put on the iPad. If you just print it, it will look like a fake, they will tell you: “you just printed it yourself!”, But when they see it on the tablet with these blue hyperlinks, they say: “oh, this is magic, it must be true”!

I had to get to a protected facility in New York, because the network administrator noticed that there was a lot of network traffic coming from the computer of the company's deputy CFO. Therefore, such a cool network specialist, like me, had to get on this object and figure out what was happening with the network. Such was the legend, and I spent 2 hours in Google Docs, writing this letter. So, it says here that the new owner of this company was very upset by this sad event and appealed to another company asking it to send its best network specialist, that is, me, to check their main server. Well, the second letter was addressed personally to me as if from the director of information security of the second company, and he wrote that I should give up all my affairs and arrive there by tomorrow. And that I have to do the job as “excellent”, because “many eyes” are looking at this project. In general, I made it so that it sounded urgent and politically, so that no one was particularly surprised by my arrival. I showed this letter to the “network guy”, he took me to the office, we talked to the director of information security for 10 minutes. And then this guy accompanied me on all the desktops with computers, but I could freely insert my flash drives wherever I wanted and do whatever I wanted. So I really loved this letter. And then this guy accompanied me on all the desktops with computers, but I could freely insert my flash drives wherever I wanted and do whatever I wanted. So I really loved this letter. And then this guy accompanied me on all the desktops with computers, but I could freely insert my flash drives wherever I wanted and do whatever I wanted. So I really loved this letter.
So, I don’t care about your credit cards, I don’t care about the Sarbanes-Oxley Act, the ISOs, that Leicester got Linux, I just want to fuck you, spoil your mood in the worst possible way, I want to be the worst may happen to you at the worst possible time. Remember the kittens?
So these are my 2 rules that I took from the Serenity movie: “I want to be out of my mind” and “Let's be the bad guys.”

It's like a red team against a blue one, so don't be offended if I hit you below the belt. It’s like the bankers who are kidnapped and held hostage by their whole family until the robbers open the doors of the bank. This is not funny, it really is still happening. This is one of the things about which people say that there is nothing new in it. The concept of what we are doing is taken from the 1992 film Sneakers. It’s as if people are hiring you to break into places to make sure no one can hack them.
Now this business has become better, but still, the concept is preserved, it is not new, and there are people who understand this better than me.
Another thing we need to understand is that management is a response, not a warning. I will quote the words of Dana Erwin, a security officer at Dow Chemical, in 2008: "The best way to draw management’s attention to a disaster plan is to burn the building across the street."
Greetings to all present - I am this fire! And now we come to the fun part of the speech, in which I will talk about several ways of kindling such lights.
The inscription on the demotivator: “Prostaki. Even ducklings know how to recognize them! ”
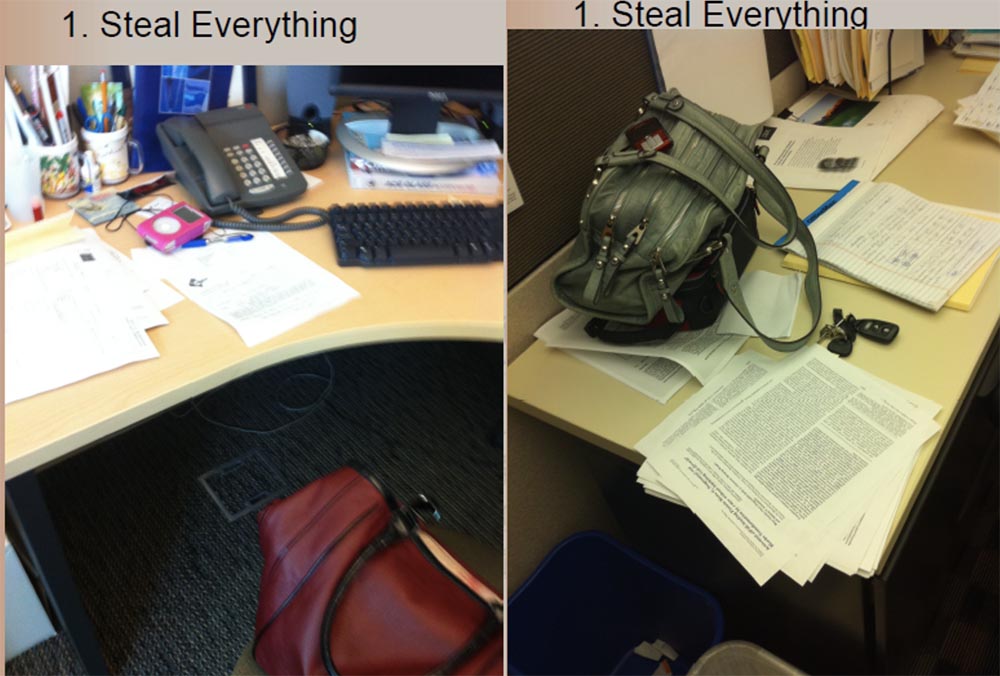
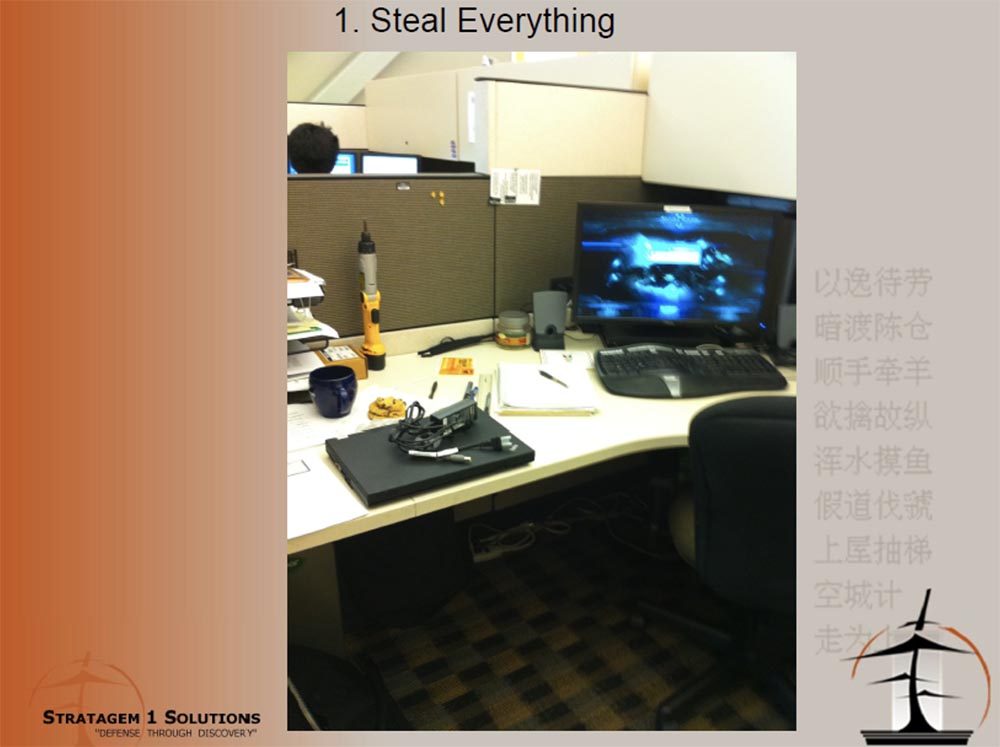
Next on the slides, what I call “use bad facts” is depicted, because I stole this phone, I “raped” this laptop, and 30 laptops in this office did not have anti-theft cables, because the management thought that they were already “ protected. " When I got there, they just equipped laptops with anti-theft cables, and one guy left his laptop with a cable and a screwdriver on the table, probably so that the thief would be convenient to unscrew the cable if it were connected to a laptop. But since I was hungry, I stole only cookies from his table.

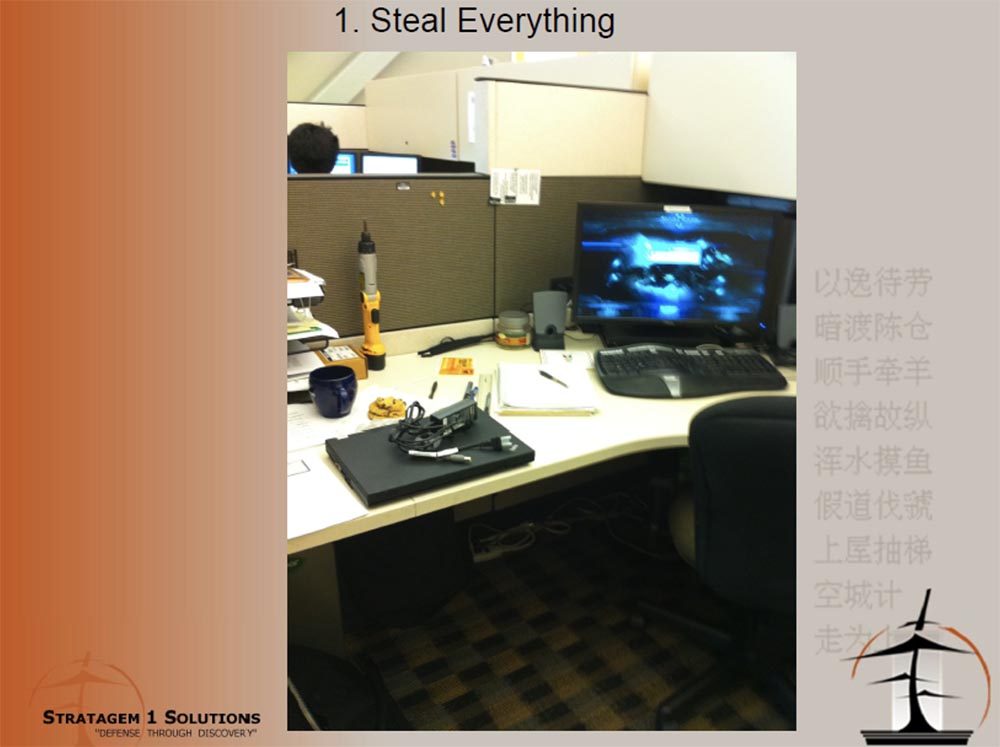
You know, people believe that security should not be so thorough that they use anti-theft cables to protect their laptops. Because you have to attach it to the table, and this is difficult, you need to bend, so let's just run this cable over the table, because no one will pull it. And you know that most of the guards really don’t try to pull this cable to check, but I’m not a guard, I’m a thief, I’ll pull him to try to steal a laptop.

Some guys use a combination lock, but I assure you that if this code is 0-0-0-0, I will try to dial it, if it is 1-1-1-1, I will also try, and I will try to dial even 9-9- 9-9. And if you are so smart that you pick up 0-0-0-7, because people like you like to move only the last or only the first wheel of the lock, I will try this option and still open the lock.

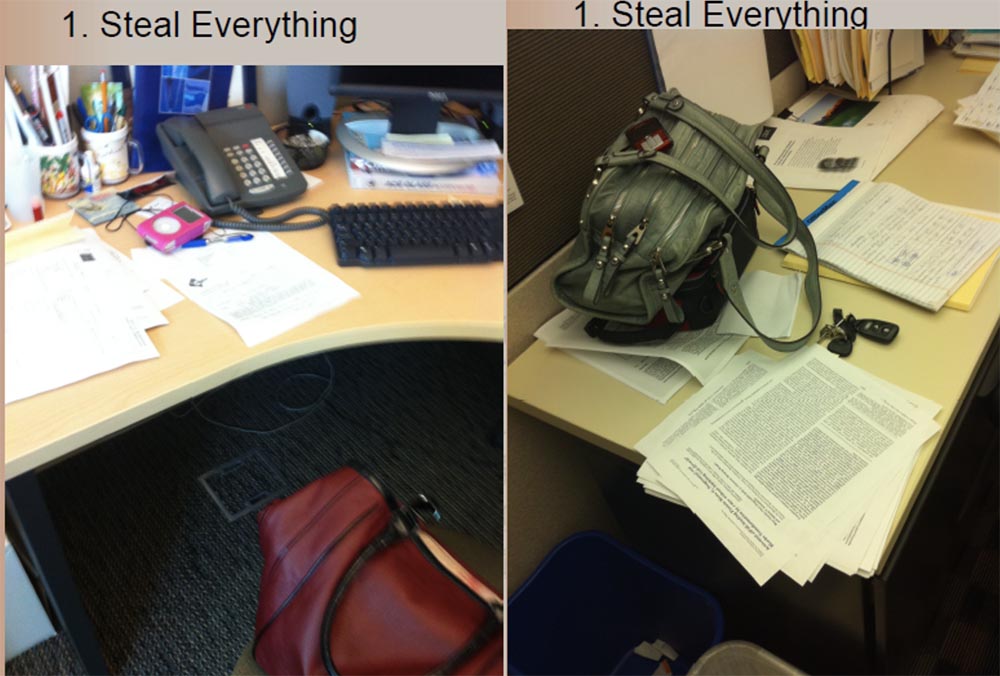
I'm going to go through all the drawers of your desk and all the lockers, and I will look for all sorts of things there. A decent and honest colleague will not look at someone else’s table, what lies there, but I’m not like that. On the slide to the right, you see a laptop of one guy, he fixed the laptop quite correctly, and thought that now that he has such a brilliant cable, his laptop is protected from theft. But then he put the keys in the top drawer of his desk and crossed out all the security.
The next slide shows why I stole this iPod in a retro style, these car keys and driver's license. Because they were lying unattended.
Now imagine that I took her keys, went down to the parking lot, opened the car, and then put the keys in place. And after work, I would have been waiting for her in the back seat of a car with a gun in my hand. From the driver's license, I would have recognized her home address, and could have sent people who would have killed her family if she had not returned to work and stolen the necessary data for me.
Workers should know that their personal belongings belong only to them, but their theft can inflict a serious blow not only on them, but also on the company in which they work. Therefore, they themselves must ensure the safety of their belongings. Let's once again remember the cute kittens from the first slide.
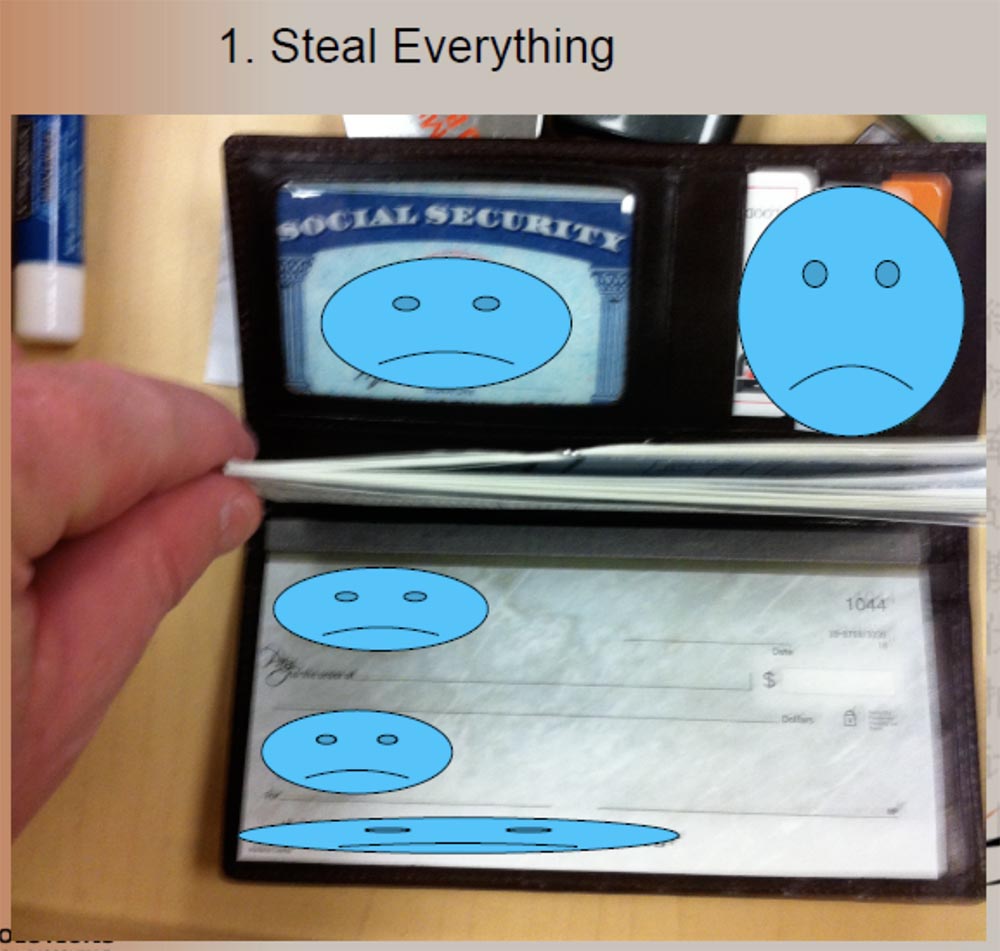
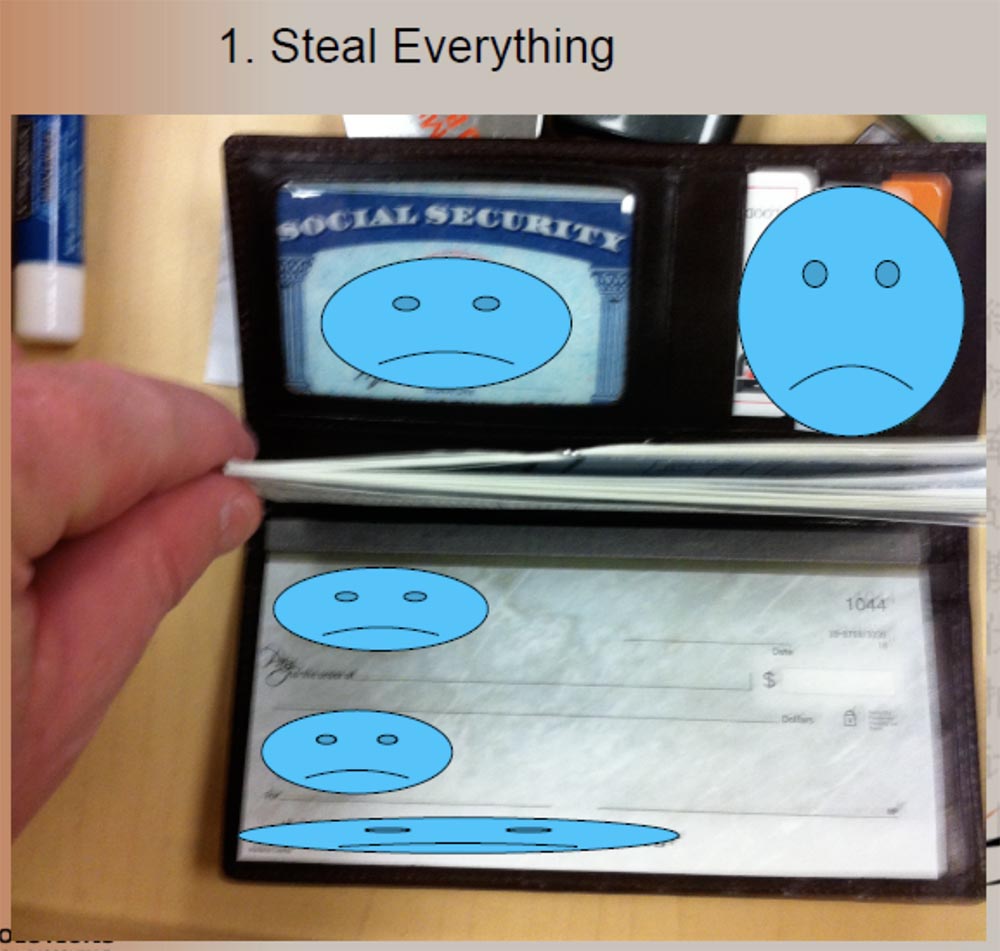
Look at the next slide, do you know why there are so many sad emoticons? Because this is a complete “game over” for the owner of this wallet - there is an empty checkbook, credit cards, an identity card and a social security card with the owner’s signature.
When I was going to steal my first car, there were too many people there, and then I came at 2 am and opened three Mercedes-Benz and one Beamer and it took me less than 60 seconds, like in the movie with Nicholas Cage You should have seen a security manager when I came to him and threw 4 keys from these cars on the table - the expression on his face was simply indescribable.

By the way, I included this slide in the presentation - this picture of the desktop in my home.
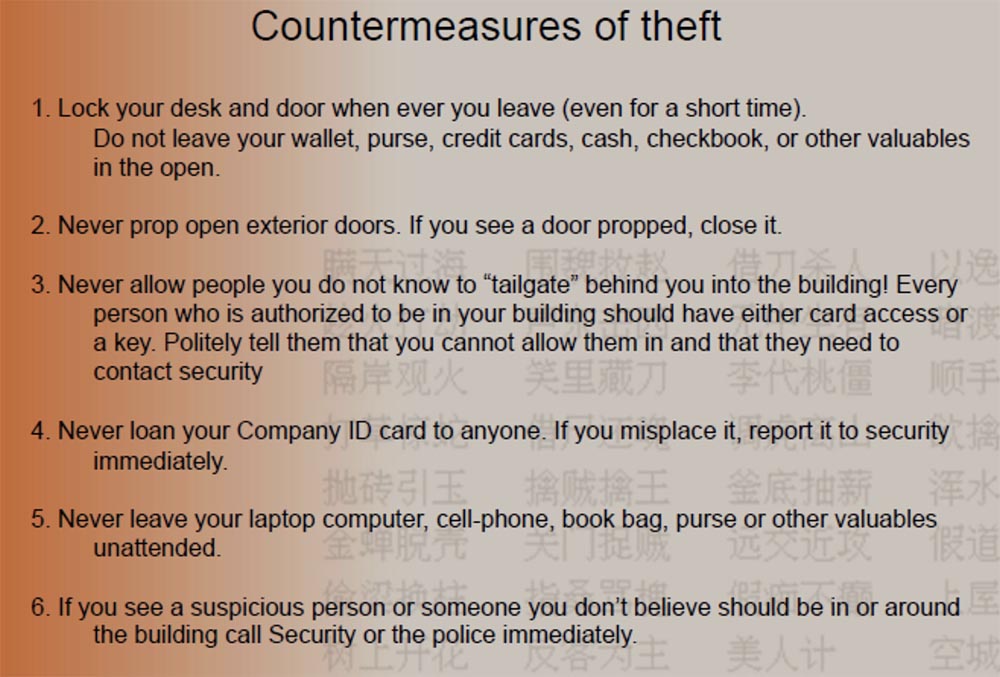
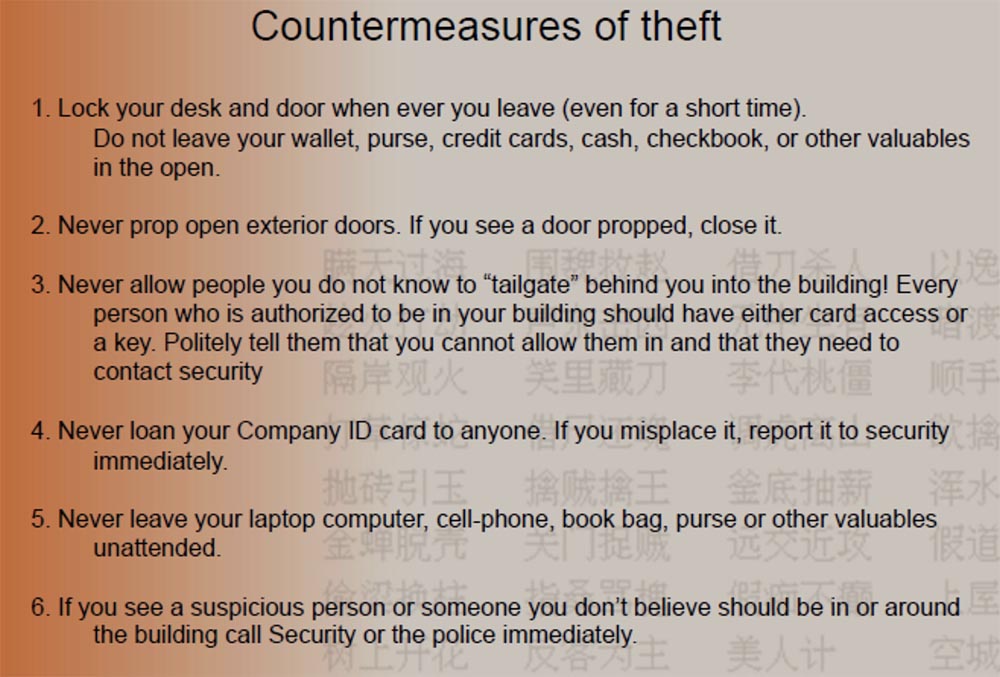
Therefore, I would like employees to take countermeasures against theft, to lock the boxes at work, even if they leave the workplace for a short time, not to leave wallets, credit cards, checkbooks on the tables, to ensure the safety of their property at work and at home, the safety of their property. machines. I want them to understand that it is impossible to pass by the “tail” to two people on one pass and explain to others that this threatens their own security. You can not send anyone a certificate issued by your company, you can not leave your computer, laptop and smartphone unattended. Finally, if you see a suspicious person, or someone who should not be inside or outside the building, immediately inform the security or the police.
Do you know what I did once? I appeared in a wheelchair with 4 books in my hands. “Jason, you are a jerk!”, And I’m all so — yes, I’m trying to rob you, you really think that I’m worried about my inferiority, because I don’t have to be in this wheelchair? I’m evil, I’m really going to do THAT, and you just let me pass inside the protected object with these 4 books.
I want to note that you don’t have to push the handicapped person out of the door yourself, or open the door in front of him if you are embarrassed or afraid to offend him. But if you saw something suspicious - say so. Remember that any employee is part of the company's security system. If you consider something suspicious, do not hesitate to report this to the guards, it is their job to check all suspicious visitors.
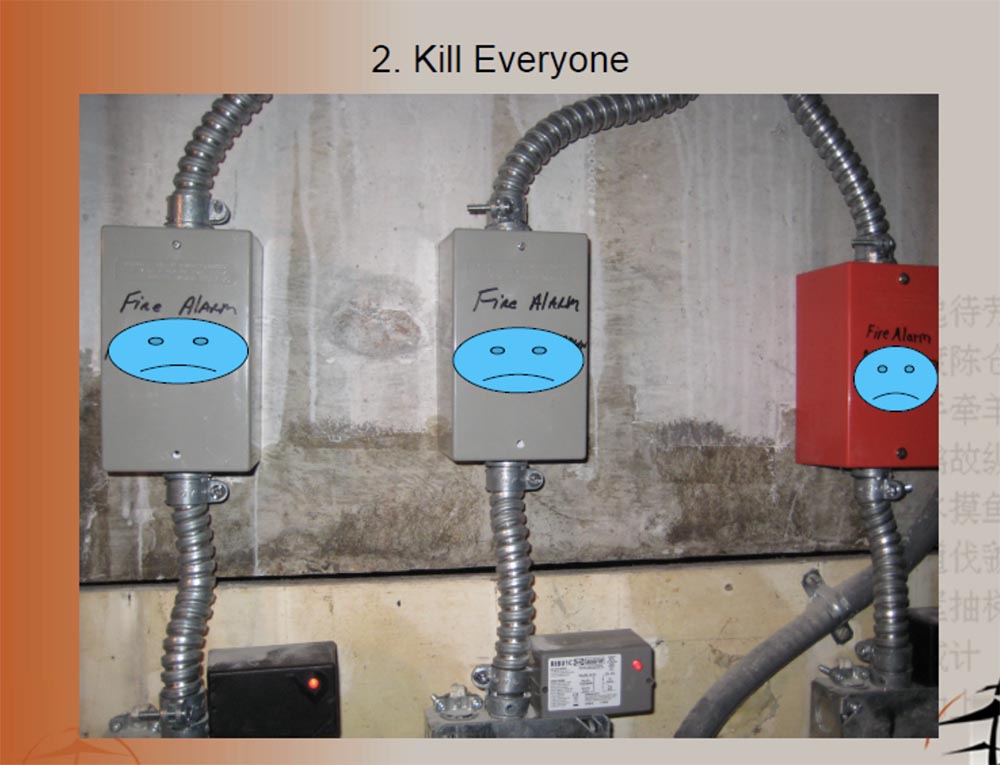
So, we figured out what it means to “steal everything”, so now let's talk on the topic “kill everyone”.
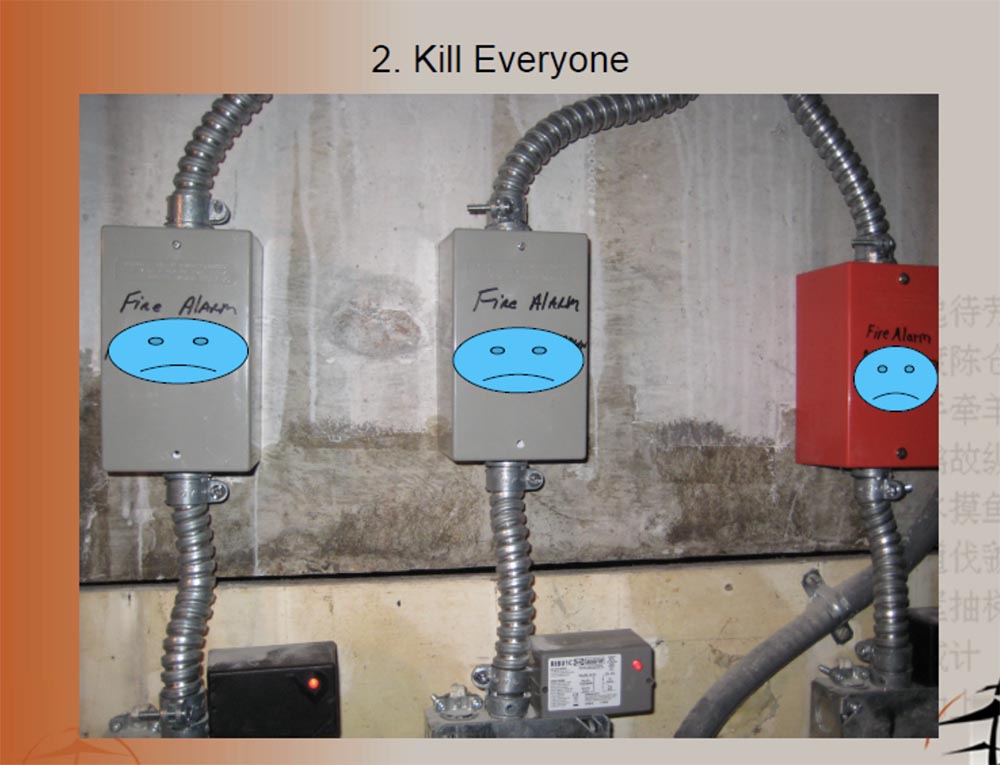
This slide shows a photo taken at 2-30 Sunday night in the hotel’s basement working area, I went there in my pajamas and barefoot because I took off all my clothes in the bathroom of the guest area and thought what I could do here and how It turned out I could do a lot. I entered the room with mechanical equipment and saw that there were no locks on any of the switches.

Imagine that I have something like OBS, obsessive-compulsive disorder, I'm crazy, and if these switches are turned off, I turn them on, if they turn on - I turn them off, if there is a red button, then I press it twice, but do not think that I am a complete moron. If there are any toxic chemicals, they will catch fire, and smoke will go into the ventilation, and a fire alarm may be triggered. But I'm not so awful to bother people at half past two in the morning, who wants to get up in the middle of the night, awakened by these alarm bells, so I will just mute the alarm.
By the way, what the fire alarm system looks like in the same basement are these boxes, and below them are red buttons. But if the alarm calls do not wake you up, the fire prevention system will start sprinkling cold water on your face from the ceiling, and that will be at 2-30 in the morning! This is very cruel! Therefore, I will also shut off the water supply to the fire system with the help of these taps shown in the next slide.
Another place that is great for killing people is the hotel’s kitchen. This guy on the slide asked me what I was doing there, but most people wouldn't ask.

Now I will show you a video that I made at a hotel in Malaysia. I was wearing the same shirt as now, so look what happened there.
The video shows that the shooting is a fast-moving person. He moves along some corridors with open doors, bumps into a bunch of tables. Jason says he already wanted to steal one table, but he noticed a man in the audience and decided not to risk it. The camera moves on and is in front of the door to the guarded premises. Outside the door is a metal lock. There is a sign on the door: “Be careful, dangerous chemicals”!

Jason: “I didn’t enter there with Uzi or AK-47, I didn’t bring C-4 explosives with me, I just came here to this room with poison. Let's see what I can do. ” Next, the camera pulls away from the door, follows the corridor and enters the kitchen.
I decided to look around for what else was around, and suddenly I stumbled upon the kitchen. Right next to this toxic room. There was one man in the kitchen, I said to him: “Hi!”, But he didn’t answer me, you moron. There were refrigerators with food and a cooking place, so if I wanted to deal with all the hotel guests, I would just poison all the products in the kitchen, especially since the poison was in the next room.
Then I went through another door, a corridor, and found myself in a room with mechanical equipment. See, there are 2 guys here, so I use social engineering techniques. I ask them: “How are you?”, They answer: “OK!”, And I just go on. Here's another door, a corridor, and I enter the kitchen again. This hotel is well protected information, all data about the guests are in the computer, and you can not just come up and ask who and where he stayed. But in the kitchen, right on the wall, there are lists with the names and numbers of rooms, and each guest has his own number. Today it is quite non-tech service. Then I used social engineering again, looked into the booth of the main manager and asked if they used the Internet for a Wi-Fi network or cable, I was in my hacker shirt, with an iPad in my hands,
I tell you this: people do not expect bad things to happen until they really happen. The next slide shows measures against workplace violence:
Teach your people to understand one thing at a time what is happening in the workplace, teach them this code word. I always tell people that the code “Oh God, he has a gun, we will all die!” Is not the best code in case of danger. I advise them to use the word Periwinkle (periwinkle) in this combination: “Where is Mr. Perivinkle? Mr. Pereinkl cause! ”And the like. I hope that someday they will create the Periwinkle Institute, because it is a very funny word.
Check the safety of your equipment and your people constantly. When I walked along one object for an hour, I noticed a door that I could easily break. Directly above her was a camera, and two more cameras in the parking lot, poorly tuned. And it would be possible to walk past them diagonally, and no one would have noticed you, especially if you changed the angle of this single camera above the door. I began to talk about this with the head of the security service, he waved his hand, said that it was nonsense, and invited me to his office. There was no security, he showed me the screens of computers and monitors, they were all turned off. He turned them on, and one camera did not work — it was the one camera above the door that only provided competent observation. I looked into his eyes and said: “This is not serious!”. I think that was not the only one who could verify this,
We now turn to the third part of the presentation - the complete financial collapse, and we start with spying. Look at these gloomy smiles on the slide - this means that everything is bad.

Do you know why? Because I am an environmentalist! Do you know how many poor trees die senselessly every day for the printouts you leave near your printer? So know that they do not die in vain, because when I come, I will take them all. I will free these trees! I'll take your printouts and take it with me, just to be sure that you have not forgotten about the poor trees.
You know why this is really sad - because these people still use machines to destroy papers with confidential data. However, all that would have to grind, pass through a shredder, we still put in this big blue bucket.
This is all confidential information, and so it is done in the District of Columbia, and in financial institutions, and in the Department of Defense, in all these protected offices, where room cleaners cannot even enter, because there are top-secret data. And you know what the staff then do? At night, they just take out this blue bucket of paper and put it outside the door! This is really terrible, that is, I want to say terrible for a bad guy like me. Let's go further.

If the attacker does not know where the flash drive of your exchange server is located, simply leave the USB flash drive in the desired USB port. Thereby you will show where you need to download confidential information. What about your financial server, where all the accounts are located? The 25 employees who receive salaries there believe that there is nothing wrong with sticking a piece of paper with the word ACCOUNTING on one of the computers. To the offender did not spend time searching for this server, and immediately put the flash drive where necessary.

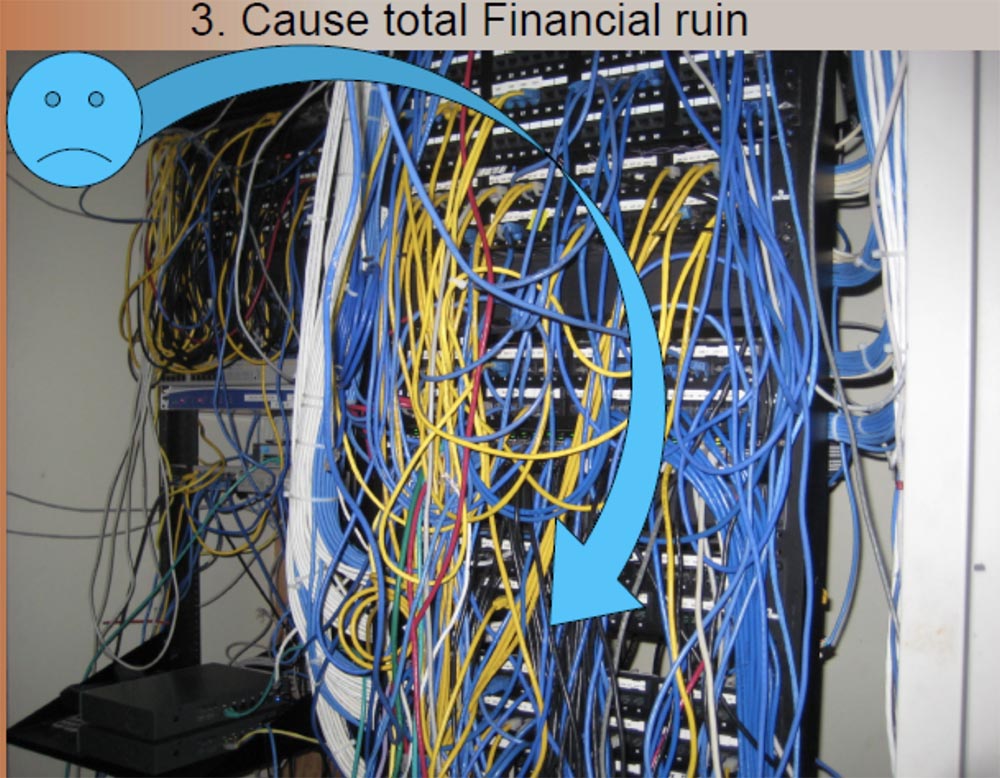
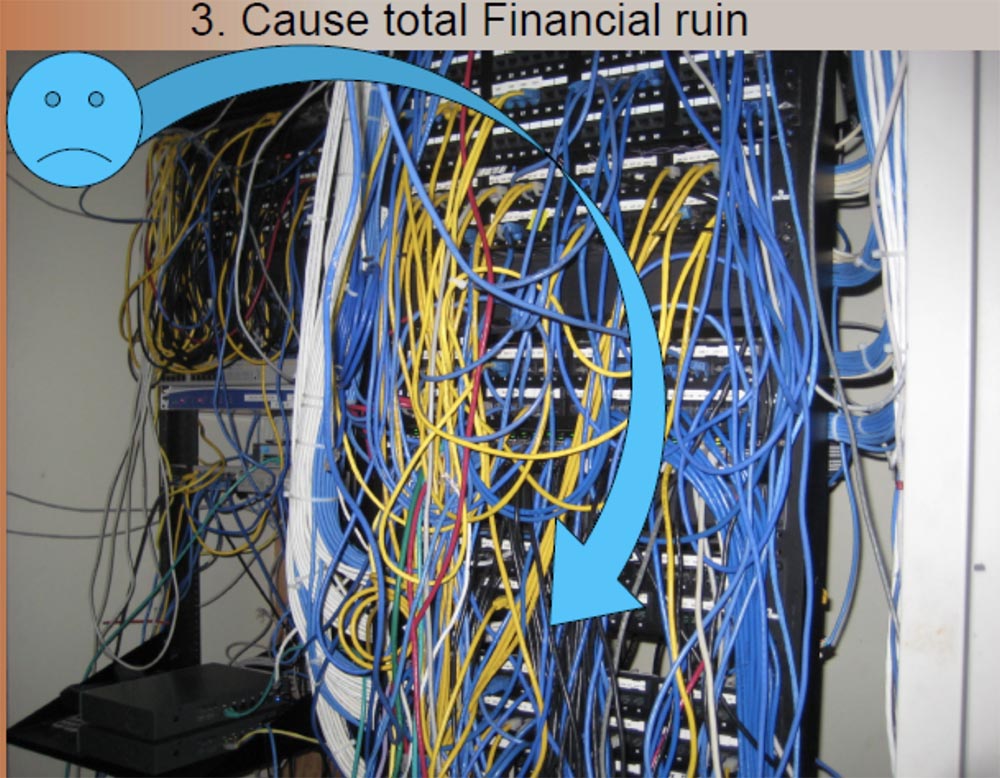
If you want to wiretap, you do not need to look for something special - just go to this mess of wires and use the one you need.
Do you know how hard it is to steal or forge passwords? You need to understand Linux, to be technically savvy, it's not about me. So I’ll just go to this table and read the password on the sticker.
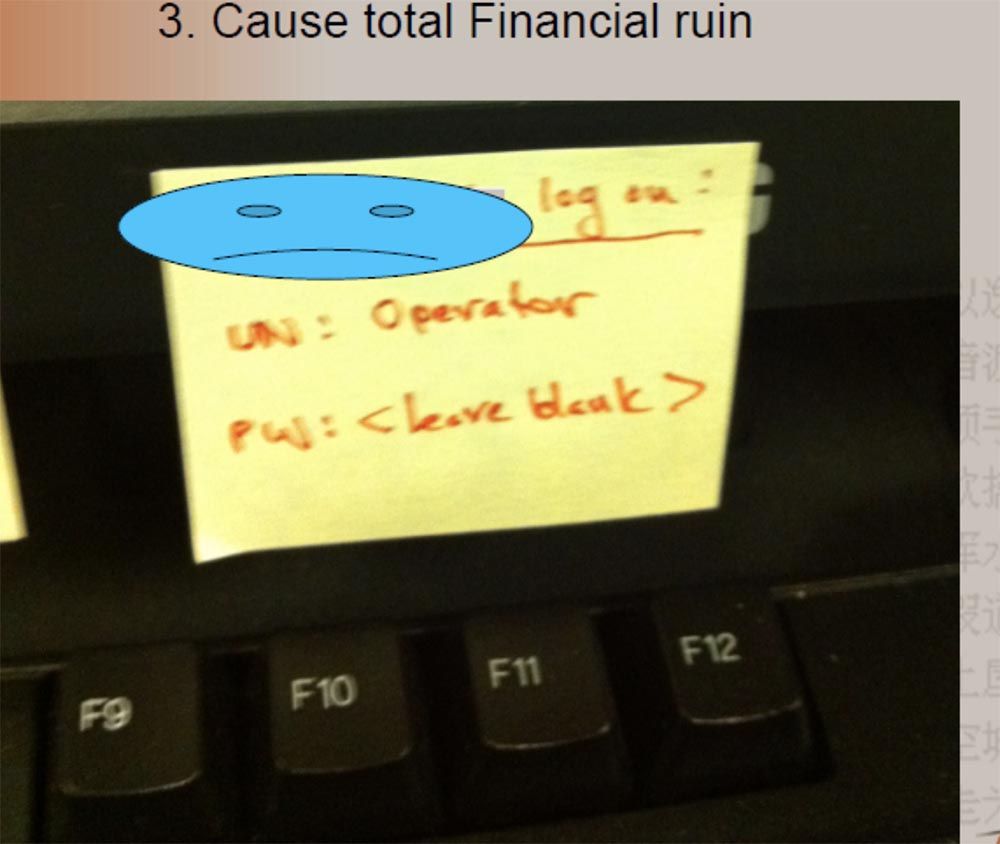
I usually remove the password sticker and leave the clip blank to make them think a little.
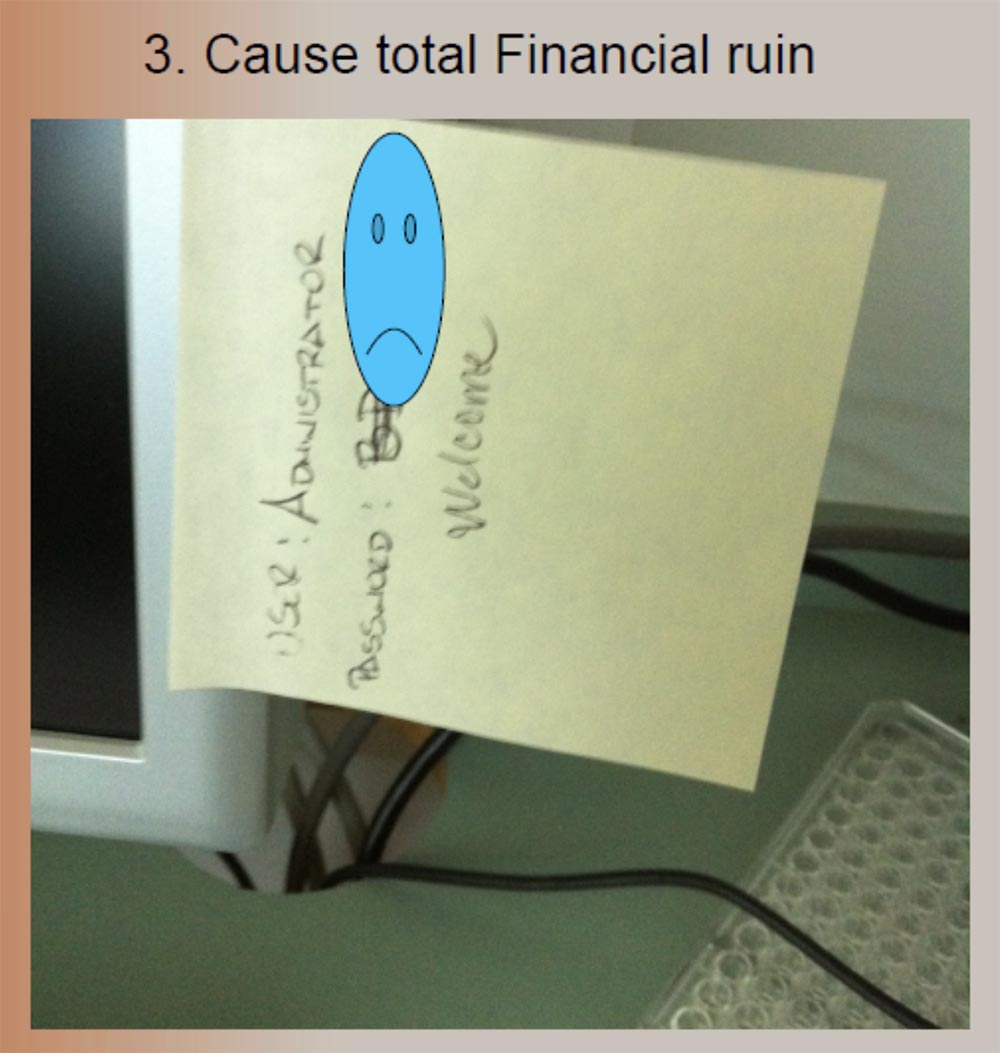
And this picture on the top slide is one of my favorites. This is the office of a pharmaceutical laboratory that performs biochemical research. These are complex things, so let's end the rocket science and write a password easier. And they cross out a special alphanumeric password, which was quite complicated, and replace it with this word Welcome. Indeed, welcome to my computer!
There is a worse thing than to see me in Pepsi pajamas - to see me in a strict suit, because it gives me the opportunity to do really awful things. Because if I'm in this suit, then I want to “throw” you.

Next to him, my favorite clothes are the waistcoat, which I call Wasted Doom, “Mindless Death”, because I think it sounds cool.
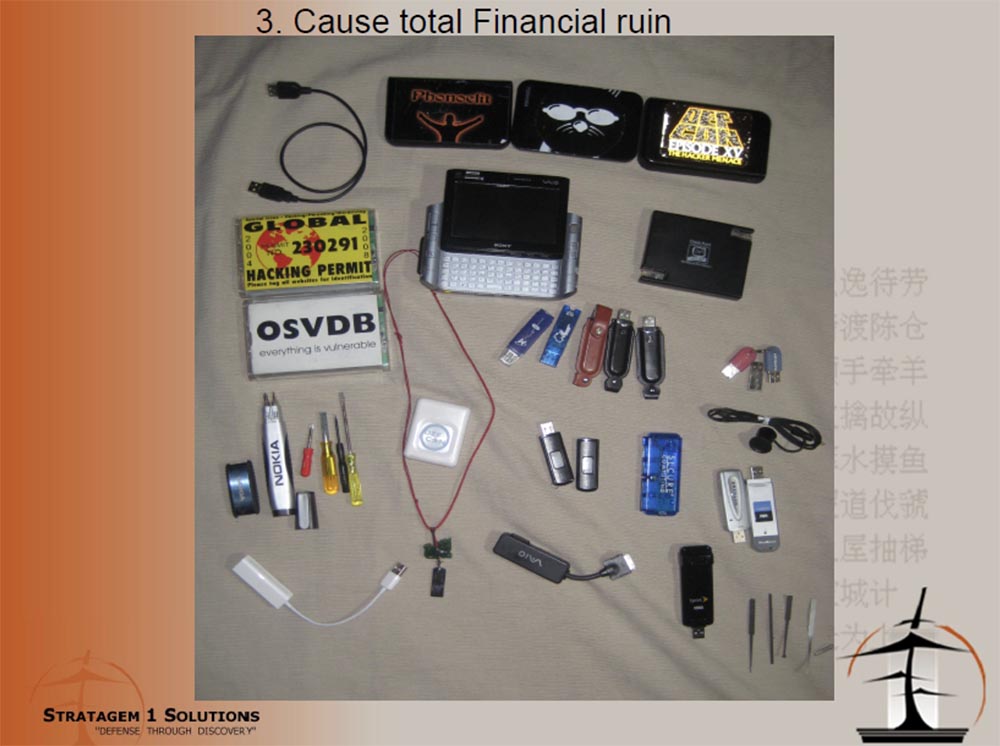
On this slide you see my “toys”, I told about them last year, and now I already have a version of the Wasted Doom 2.0 vest. I use these kind of writing pens with a video camera and USB, I do not leave them in my pocket, but I put it in your little pencil cup and leave, and the built-in video camera will record all your logins, passwords and your conversations.
I have a stunning little flashlight - a video camera with 8 GB of memory and USB, so that I can steal your data with it, besides, a video recorder is also built into my watch. With these devices, I can do whatever I want. They were provided to me by one agency of 3 letters, located in the District of Columbia, and the only condition for the use of this equipment, on the creation of which billions of dollars were spent, was my obligation to never talk about it publicly.
Another device that I carry in my vest looks like a regular USB “flash drive”. This is Spy Keylogger, or a keylogger who can intercept and record all manipulations with a computer keyboard. It is not detected by any antivirus, it is very difficult to detect visually and simply insert into any free connector - there are 2 versions, under USB or PS2 keyboard connector. He writes everything you type on the keyboard. I found it on the Think Geek website.

The following site shows the Risk Matrix.

Vertically, the axis of probability of risk when using spyware, available for purchase on the site of Think Geek, and horizontally - the intensity or degree of impact. Low risk is shown in green, medium - in yellow, and red means a complete disaster. So, interception of keystrokes of a computer keyboard by the CEO, or the chief executive officer, leads to just such consequences.
It is believed that there is a very limited group of people who have access to all the espionage technologies shown here. But imagine, it turns out, anyone can buy them - these are many advertising tools for office espionage that are shown on these flyers. Do you think that only hackers can steal data? Not at all!
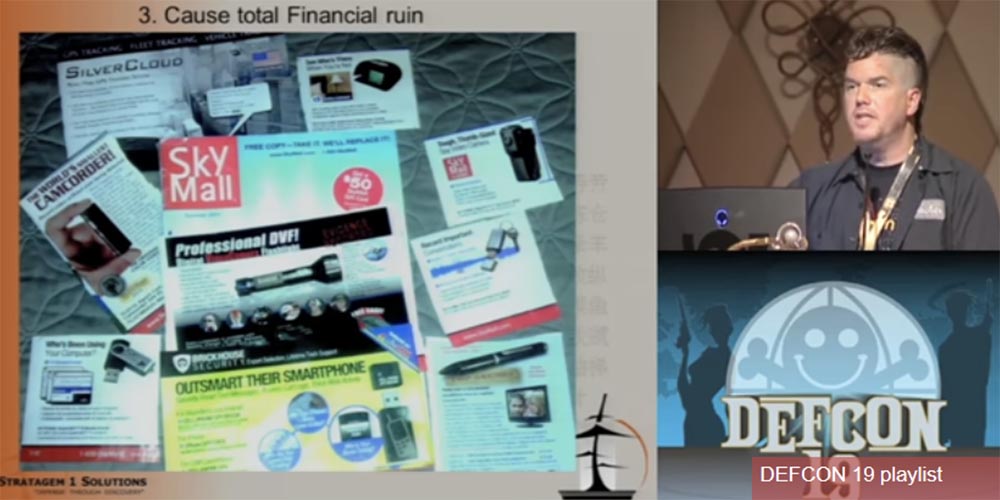
If I really hate my boss, I hate my job, I want to steal a whole bunch of company secrets, what will I do? I will use these flyers, which are thrown into my mailbox, and I see that I can use this keyboard interceptor to steal information from the boss’s computer, I use a video recorder to record secrets and an audio recorder to record confidential talks and meetings. That's not difficult. I always say it is easy to do if you can do it yourself! People are protected from serious threats coming from outside, but do not take into account the risks associated with threats within the company.
The next slide shows the connection of adapters for Pony Express in a branch of one of the banks on the west coast. I had 4 branches, 4 attempts, 4 success. After the 4th try, they finally told me to stop. The reason why I managed to do this, why I was able to penetrate these branches unhindered, was as follows.
I came to them wearing a blue DEFCON jacket, I was wearing working clothes, I had warning stripes on it, and I told them that they had sent me from the main office. I said that we had a voltage drop in the network, and I need to check if it affected your operations, so insert this device into your network so that you can take readings and transfer them to the main office so that they understand , what's happening. And by the way, I need to go in and make sure that all the computers are working properly, they were not affected by power surges, and that the UPSs are in good condition.
I had a fake name, a fake equipment supplier, a fake company phone number, but I got away with it. If I had rushed to them in a mask with a shotgun in their hands, they would know how to act, they were taught this. But they did not foresee the option of such an obsessive as me. They led me through the checkout area, through the back rooms, past the vault of money, past the large safe. Imagine how much damage I could do to them! But all I did was connect my little Pony Express adapter. On the right of the slide you see the UPS where I connected, for this I had to ask the manager to get up from his desk.
Therefore, I want to tell you about countermeasures against internal espionage:
First of all, you need to teach your employees not to click on phishing links in emails, not to go to malicious sites, not to say that this stupid user has gone there, not to call them stupid, but to teach that you can't do that. It’s like I hire an employee who doesn’t have a driver’s license, and then give him the keys to the car and say: “Go, get my Bentley here!”, He drives and breaks the car. But an idiot is not the guy who drove the car, but the one who gave him these keys! If you give employees technology, you should teach them how to use them. You need to teach your employees to understand what they are going to do. You need to strengthen your employees. When I say "strengthen", I do not mean the trade unions, or the fact that they have to arm themselves with baseball bats, although it would be cool.
It is necessary that your employees know that they are part of your company's security team, from the CEO to the courier, so that they understand how much depends on them. They need to know that safety is their job and their duty, that they are required to observe safety.
I have a guy at work who weekly sends me 15 letters from his email that he considers phishing or just weird for me to check for malware. And every time I say “great, thank you” to him, because the 16th letter can be really dangerous and will not be a false alarm. It is necessary to make people notice that someone without a badge is in the wrong place, and stopped him and asked what he was doing here. We need to tell people that they did the right thing. For this to create competition, for the employees to say: “This damn Susanna always gets a loan, because she does such things!”, So the others should do the same, they should catch those who have no badge. This does not mean that they should stop someone by force, for that there is a guard.
You have a huge human potential to ensure safety, so just learn how to use it correctly! And as soon as you stop talking “stupid users” and start saying “my colleagues in the department of information security”, you will win!
Thank you for staying with us. Do you like our articles? Want to see more interesting materials? Support us by placing an order or recommending to friends, 30% discount for Habr's users on a unique analogue of the entry-level servers that we invented for you: The whole truth about VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps from $ 20 or how to share the server? (Options are available with RAID1 and RAID10, up to 24 cores and up to 40GB DDR4).
Dell R730xd 2 times cheaper? Only we have 2 x Intel Dodeca-Core Xeon E5-2650v4 128GB DDR4 6x480GB SSD 1Gbps 100 TV from $ 249 in the Netherlands and the USA! Read about How to build an infrastructure building. class c using servers Dell R730xd E5-2650 v4 worth 9000 euros for a penny?
My presentation is called “Steal everything, kill everyone, cause a complete financial collapse, or how I entered and misbehaved!” Simply because it tells about the failure of the security system.
The signature on the picture with the kittens reads: “Army of darkness. Milder than you expected. ” The slide with the name of the presentation shows a sign with the inscription “The security guard will return in 5 minutes”.
I'm going to explain to you that physical security issues and everything related to them are our weakest point, because people oppose two-dimensional to three-dimensional and simple to complex, when they approach the entrance doors. You see that Jason I. Street has many more letters after the last name, so let me introduce myself first. I have a day job and a night job. My day job is that I serve as vice president of information security at financial company Stratagem 1 Solutions. I work in an office booth, surrounded by many interesting events. I watch the firewalls, I follow the ID systems, I built our own infrastructure and I find more creative ways to protect it from those people who can “come for us”, and my main job is the “blue team”, that is, protection.
My night job is to serve as the CIO - director of information strategies, and I perform penetration testing about 3 times a year, this is my main job. I speak at such events around the world, I wrote the book “Dissecting the Hack: The F0rb1dd3n Network” in the genre of the documentary detective story, I write articles, and I do all this at night. During the day, I react to incidents, and at night I create incidents for other people, so it is more convenient for both parties.

I love to look at these photos. In this baseball cap and black glasses, I stood for an hour in front of the building of the protected industrial park, on Sunday, in the absence of other traffic, and a guard passed me twice, who did not even ask what I was doing on the sidewalk and why I was inspecting the protected building, and did not record this incident in the report.
In the second photo I’m wearing glasses, I’m just about to apply for a job, here I’m wearing a BlackHat-colored community shirt because I like walking with “warning stickers”. I never got this job because I was not qualified enough, but I managed to get their data. That was my victory.
On the next slide, you see two more photos that I like too.

T-shirt with the inscription, I think the best, because in it I almost stole a car. I was in a hotel on the coast and the parking attendant provided me with a car, but I explained to him that I could not take this car right now, he asked why, and I answered - because I would steal it. Apparently, he bought the inscription on my T-shirt "I am the source of trouble," and decided to give me someone else's car. It took him a while to understand what I mean, so I had to say to him: "You must take her back, because the owner may need it."
The next shirt is my favorite. At one of the most guarded objects I've seen in life, directly opposite Ground Zero, the zero level of the World Trade Center in Manhattan, the SWAT squadron, these K9 with their machine guns, pass through the hall to the main elevator, which is guarded by 8 guards. the upper floors I go to myself in a shirt with the icon "Geek your company." Yes, I like this photo the most, and later I will tell you about this story a little more.
I have a CISSP (information security certificate from a non-profit organization International Information Systems Security Certificates Consortium), and I think that according to the ethical code I should mention that in my presentation I used quotes from the treatise “The Art of War” by Sun Tzu, a Chinese strategist and thinker of the V century.

So, my presentation consists of the following parts:
Introduction;
The fact is one fact that we will encounter when discussing this topic;
Rules - 2 rules that I thought up while doing my job;
Results - we will have as many as 3 results arising from these 2 rules;
Conclusions and / or discussion.
So why this particular topic? I talked about this last year at the 36 CHARGE conference, I talked about the beginning of social engineering, about the things you could do to try to get into a protected building. It was the first part and, to be honest, I received some feedback after that, and I was approached with all sorts of difficult questions.
But I am not an expert in the field of social engineering, I do not know anything about neurolinguistic programming (NLP), I do not know the methods of face recognition or ninja technology. However, I have 100% success in entering buildings, I just go there when I use the skills of this very social engineering. But believe me, I am not strong in it, it is just our modern security.
I think you will not learn anything new from me, so this is rather an educational lecture that will show you the beginning of the path, but I hope that after it you will remember what will force you to look around and take a fresh look at things that seem known to you and improve your perception of the environment.
But now I will not talk about social engineering, so this is all the damage I was able to inflict after your guard allowed me to go through the entrance doors.
So, fact number 1: I sneaked inside! I took this photo as soon as I opened the door and went up to the hall. I saw the door for the staff, this was the door to the protected area, and I just went through it by pressing buttons 1-3-5.

I could press 5-3-1, or 3-1-5, it does not matter, I would still open it, because I pressed the buttons, the surface of which was wiped from frequent use more than others. I returned from there 10 minutes before the start of our meeting, and no one found out that I was there.
Another fun occasion was when I went to get another job. I decided to be a bad guy, and when I signed my name at the reception, I stole a pen from them. Then I asked where their toilet is. This is not because I drink too much dietary cola, I just “get lost” in these large buildings and can wander for hours in search of this toilet, while looking around the entire building.

In search of a toilet, I unexpectedly stumbled upon a protected part of the working area and found an entrance for staff. It looked as if the guard of this object was showing off its security systems worth a million dollars, but when I looked at the door, I saw a little thing, a rod that holds the door latch. If I had a condom, I would adjust it to keep the door from closing. And then I remembered the stolen handle, screwed the cap off it and put it on the rod, and the door did not click. When I returned there 20 minutes after walking through the “forbidden” zone, the cap was still there. No one knew that I was on a guarded object, and it was fun!
So, I am not a locksmith of the highest category, and I do not need to be a master in locks so that people let me through the front door. I don't need to be a super ninja coder to just steal a hard disk with data from your computer. This video shows my hacker skills and a unique master key - the cover of a cardboard folder. I simply insert a sheet of cardboard between the doors of a closed door, take them up and down, and the doors open with such a simple “key”.
Next on the slide is another “key” - a fake email that I put on the iPad. If you just print it, it will look like a fake, they will tell you: “you just printed it yourself!”, But when they see it on the tablet with these blue hyperlinks, they say: “oh, this is magic, it must be true”!

I had to get to a protected facility in New York, because the network administrator noticed that there was a lot of network traffic coming from the computer of the company's deputy CFO. Therefore, such a cool network specialist, like me, had to get on this object and figure out what was happening with the network. Such was the legend, and I spent 2 hours in Google Docs, writing this letter. So, it says here that the new owner of this company was very upset by this sad event and appealed to another company asking it to send its best network specialist, that is, me, to check their main server. Well, the second letter was addressed personally to me as if from the director of information security of the second company, and he wrote that I should give up all my affairs and arrive there by tomorrow. And that I have to do the job as “excellent”, because “many eyes” are looking at this project. In general, I made it so that it sounded urgent and politically, so that no one was particularly surprised by my arrival. I showed this letter to the “network guy”, he took me to the office, we talked to the director of information security for 10 minutes. And then this guy accompanied me on all the desktops with computers, but I could freely insert my flash drives wherever I wanted and do whatever I wanted. So I really loved this letter. And then this guy accompanied me on all the desktops with computers, but I could freely insert my flash drives wherever I wanted and do whatever I wanted. So I really loved this letter. And then this guy accompanied me on all the desktops with computers, but I could freely insert my flash drives wherever I wanted and do whatever I wanted. So I really loved this letter.
So, I don’t care about your credit cards, I don’t care about the Sarbanes-Oxley Act, the ISOs, that Leicester got Linux, I just want to fuck you, spoil your mood in the worst possible way, I want to be the worst may happen to you at the worst possible time. Remember the kittens?
So these are my 2 rules that I took from the Serenity movie: “I want to be out of my mind” and “Let's be the bad guys.”

It's like a red team against a blue one, so don't be offended if I hit you below the belt. It’s like the bankers who are kidnapped and held hostage by their whole family until the robbers open the doors of the bank. This is not funny, it really is still happening. This is one of the things about which people say that there is nothing new in it. The concept of what we are doing is taken from the 1992 film Sneakers. It’s as if people are hiring you to break into places to make sure no one can hack them.
Now this business has become better, but still, the concept is preserved, it is not new, and there are people who understand this better than me.
Another thing we need to understand is that management is a response, not a warning. I will quote the words of Dana Erwin, a security officer at Dow Chemical, in 2008: "The best way to draw management’s attention to a disaster plan is to burn the building across the street."
Greetings to all present - I am this fire! And now we come to the fun part of the speech, in which I will talk about several ways of kindling such lights.
The inscription on the demotivator: “Prostaki. Even ducklings know how to recognize them! ”
Next on the slides, what I call “use bad facts” is depicted, because I stole this phone, I “raped” this laptop, and 30 laptops in this office did not have anti-theft cables, because the management thought that they were already “ protected. " When I got there, they just equipped laptops with anti-theft cables, and one guy left his laptop with a cable and a screwdriver on the table, probably so that the thief would be convenient to unscrew the cable if it were connected to a laptop. But since I was hungry, I stole only cookies from his table.

You know, people believe that security should not be so thorough that they use anti-theft cables to protect their laptops. Because you have to attach it to the table, and this is difficult, you need to bend, so let's just run this cable over the table, because no one will pull it. And you know that most of the guards really don’t try to pull this cable to check, but I’m not a guard, I’m a thief, I’ll pull him to try to steal a laptop.

Some guys use a combination lock, but I assure you that if this code is 0-0-0-0, I will try to dial it, if it is 1-1-1-1, I will also try, and I will try to dial even 9-9- 9-9. And if you are so smart that you pick up 0-0-0-7, because people like you like to move only the last or only the first wheel of the lock, I will try this option and still open the lock.

I'm going to go through all the drawers of your desk and all the lockers, and I will look for all sorts of things there. A decent and honest colleague will not look at someone else’s table, what lies there, but I’m not like that. On the slide to the right, you see a laptop of one guy, he fixed the laptop quite correctly, and thought that now that he has such a brilliant cable, his laptop is protected from theft. But then he put the keys in the top drawer of his desk and crossed out all the security.
The next slide shows why I stole this iPod in a retro style, these car keys and driver's license. Because they were lying unattended.
Now imagine that I took her keys, went down to the parking lot, opened the car, and then put the keys in place. And after work, I would have been waiting for her in the back seat of a car with a gun in my hand. From the driver's license, I would have recognized her home address, and could have sent people who would have killed her family if she had not returned to work and stolen the necessary data for me.
Workers should know that their personal belongings belong only to them, but their theft can inflict a serious blow not only on them, but also on the company in which they work. Therefore, they themselves must ensure the safety of their belongings. Let's once again remember the cute kittens from the first slide.
Look at the next slide, do you know why there are so many sad emoticons? Because this is a complete “game over” for the owner of this wallet - there is an empty checkbook, credit cards, an identity card and a social security card with the owner’s signature.
When I was going to steal my first car, there were too many people there, and then I came at 2 am and opened three Mercedes-Benz and one Beamer and it took me less than 60 seconds, like in the movie with Nicholas Cage You should have seen a security manager when I came to him and threw 4 keys from these cars on the table - the expression on his face was simply indescribable.

By the way, I included this slide in the presentation - this picture of the desktop in my home.
Therefore, I would like employees to take countermeasures against theft, to lock the boxes at work, even if they leave the workplace for a short time, not to leave wallets, credit cards, checkbooks on the tables, to ensure the safety of their property at work and at home, the safety of their property. machines. I want them to understand that it is impossible to pass by the “tail” to two people on one pass and explain to others that this threatens their own security. You can not send anyone a certificate issued by your company, you can not leave your computer, laptop and smartphone unattended. Finally, if you see a suspicious person, or someone who should not be inside or outside the building, immediately inform the security or the police.
Do you know what I did once? I appeared in a wheelchair with 4 books in my hands. “Jason, you are a jerk!”, And I’m all so — yes, I’m trying to rob you, you really think that I’m worried about my inferiority, because I don’t have to be in this wheelchair? I’m evil, I’m really going to do THAT, and you just let me pass inside the protected object with these 4 books.
I want to note that you don’t have to push the handicapped person out of the door yourself, or open the door in front of him if you are embarrassed or afraid to offend him. But if you saw something suspicious - say so. Remember that any employee is part of the company's security system. If you consider something suspicious, do not hesitate to report this to the guards, it is their job to check all suspicious visitors.
So, we figured out what it means to “steal everything”, so now let's talk on the topic “kill everyone”.
This slide shows a photo taken at 2-30 Sunday night in the hotel’s basement working area, I went there in my pajamas and barefoot because I took off all my clothes in the bathroom of the guest area and thought what I could do here and how It turned out I could do a lot. I entered the room with mechanical equipment and saw that there were no locks on any of the switches.

Imagine that I have something like OBS, obsessive-compulsive disorder, I'm crazy, and if these switches are turned off, I turn them on, if they turn on - I turn them off, if there is a red button, then I press it twice, but do not think that I am a complete moron. If there are any toxic chemicals, they will catch fire, and smoke will go into the ventilation, and a fire alarm may be triggered. But I'm not so awful to bother people at half past two in the morning, who wants to get up in the middle of the night, awakened by these alarm bells, so I will just mute the alarm.
By the way, what the fire alarm system looks like in the same basement are these boxes, and below them are red buttons. But if the alarm calls do not wake you up, the fire prevention system will start sprinkling cold water on your face from the ceiling, and that will be at 2-30 in the morning! This is very cruel! Therefore, I will also shut off the water supply to the fire system with the help of these taps shown in the next slide.
Another place that is great for killing people is the hotel’s kitchen. This guy on the slide asked me what I was doing there, but most people wouldn't ask.

Now I will show you a video that I made at a hotel in Malaysia. I was wearing the same shirt as now, so look what happened there.
The video shows that the shooting is a fast-moving person. He moves along some corridors with open doors, bumps into a bunch of tables. Jason says he already wanted to steal one table, but he noticed a man in the audience and decided not to risk it. The camera moves on and is in front of the door to the guarded premises. Outside the door is a metal lock. There is a sign on the door: “Be careful, dangerous chemicals”!

Jason: “I didn’t enter there with Uzi or AK-47, I didn’t bring C-4 explosives with me, I just came here to this room with poison. Let's see what I can do. ” Next, the camera pulls away from the door, follows the corridor and enters the kitchen.
I decided to look around for what else was around, and suddenly I stumbled upon the kitchen. Right next to this toxic room. There was one man in the kitchen, I said to him: “Hi!”, But he didn’t answer me, you moron. There were refrigerators with food and a cooking place, so if I wanted to deal with all the hotel guests, I would just poison all the products in the kitchen, especially since the poison was in the next room.
Then I went through another door, a corridor, and found myself in a room with mechanical equipment. See, there are 2 guys here, so I use social engineering techniques. I ask them: “How are you?”, They answer: “OK!”, And I just go on. Here's another door, a corridor, and I enter the kitchen again. This hotel is well protected information, all data about the guests are in the computer, and you can not just come up and ask who and where he stayed. But in the kitchen, right on the wall, there are lists with the names and numbers of rooms, and each guest has his own number. Today it is quite non-tech service. Then I used social engineering again, looked into the booth of the main manager and asked if they used the Internet for a Wi-Fi network or cable, I was in my hacker shirt, with an iPad in my hands,
I tell you this: people do not expect bad things to happen until they really happen. The next slide shows measures against workplace violence:
- train management and staff to recognize dangerous signs of violence in the workplace;
- when faced with a threat, hire additional security and provide employees with sufficient instructions and instructions;
- make sure all employees / victims know that if they report workplace violence, harassment, and / or threats, this will not affect their job status;
- create a code word that administrators at the reception can use to alert colleagues about a potentially dangerous person who has arrived at the reception area;
- conduct regular trainings to train managers and supervisors to recognize signs of violence and minimize potentially violent situations in the workplace;
- conduct scheduled security checks and maintain the functionality of workplaces, including emergency exits, alarms, lighting, surveillance cameras, metal detectors.
Teach your people to understand one thing at a time what is happening in the workplace, teach them this code word. I always tell people that the code “Oh God, he has a gun, we will all die!” Is not the best code in case of danger. I advise them to use the word Periwinkle (periwinkle) in this combination: “Where is Mr. Perivinkle? Mr. Pereinkl cause! ”And the like. I hope that someday they will create the Periwinkle Institute, because it is a very funny word.
Check the safety of your equipment and your people constantly. When I walked along one object for an hour, I noticed a door that I could easily break. Directly above her was a camera, and two more cameras in the parking lot, poorly tuned. And it would be possible to walk past them diagonally, and no one would have noticed you, especially if you changed the angle of this single camera above the door. I began to talk about this with the head of the security service, he waved his hand, said that it was nonsense, and invited me to his office. There was no security, he showed me the screens of computers and monitors, they were all turned off. He turned them on, and one camera did not work — it was the one camera above the door that only provided competent observation. I looked into his eyes and said: “This is not serious!”. I think that was not the only one who could verify this,
We now turn to the third part of the presentation - the complete financial collapse, and we start with spying. Look at these gloomy smiles on the slide - this means that everything is bad.

Do you know why? Because I am an environmentalist! Do you know how many poor trees die senselessly every day for the printouts you leave near your printer? So know that they do not die in vain, because when I come, I will take them all. I will free these trees! I'll take your printouts and take it with me, just to be sure that you have not forgotten about the poor trees.
You know why this is really sad - because these people still use machines to destroy papers with confidential data. However, all that would have to grind, pass through a shredder, we still put in this big blue bucket.
This is all confidential information, and so it is done in the District of Columbia, and in financial institutions, and in the Department of Defense, in all these protected offices, where room cleaners cannot even enter, because there are top-secret data. And you know what the staff then do? At night, they just take out this blue bucket of paper and put it outside the door! This is really terrible, that is, I want to say terrible for a bad guy like me. Let's go further.

If the attacker does not know where the flash drive of your exchange server is located, simply leave the USB flash drive in the desired USB port. Thereby you will show where you need to download confidential information. What about your financial server, where all the accounts are located? The 25 employees who receive salaries there believe that there is nothing wrong with sticking a piece of paper with the word ACCOUNTING on one of the computers. To the offender did not spend time searching for this server, and immediately put the flash drive where necessary.

If you want to wiretap, you do not need to look for something special - just go to this mess of wires and use the one you need.
Do you know how hard it is to steal or forge passwords? You need to understand Linux, to be technically savvy, it's not about me. So I’ll just go to this table and read the password on the sticker.
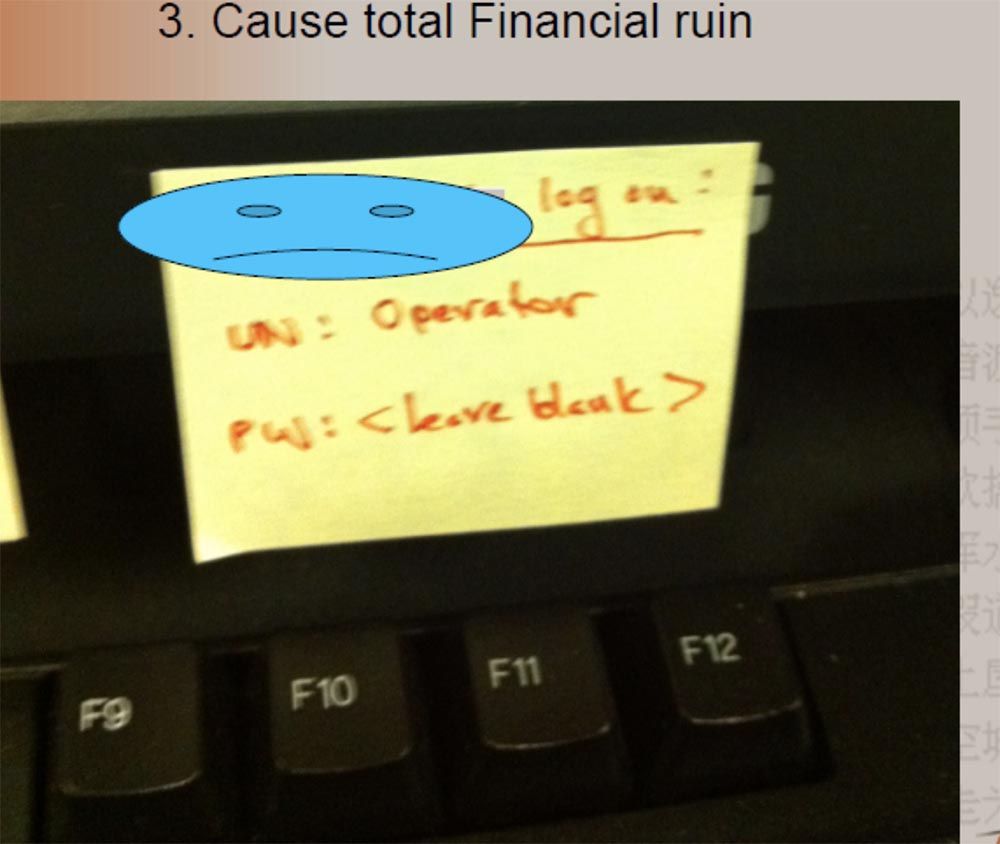
I usually remove the password sticker and leave the clip blank to make them think a little.
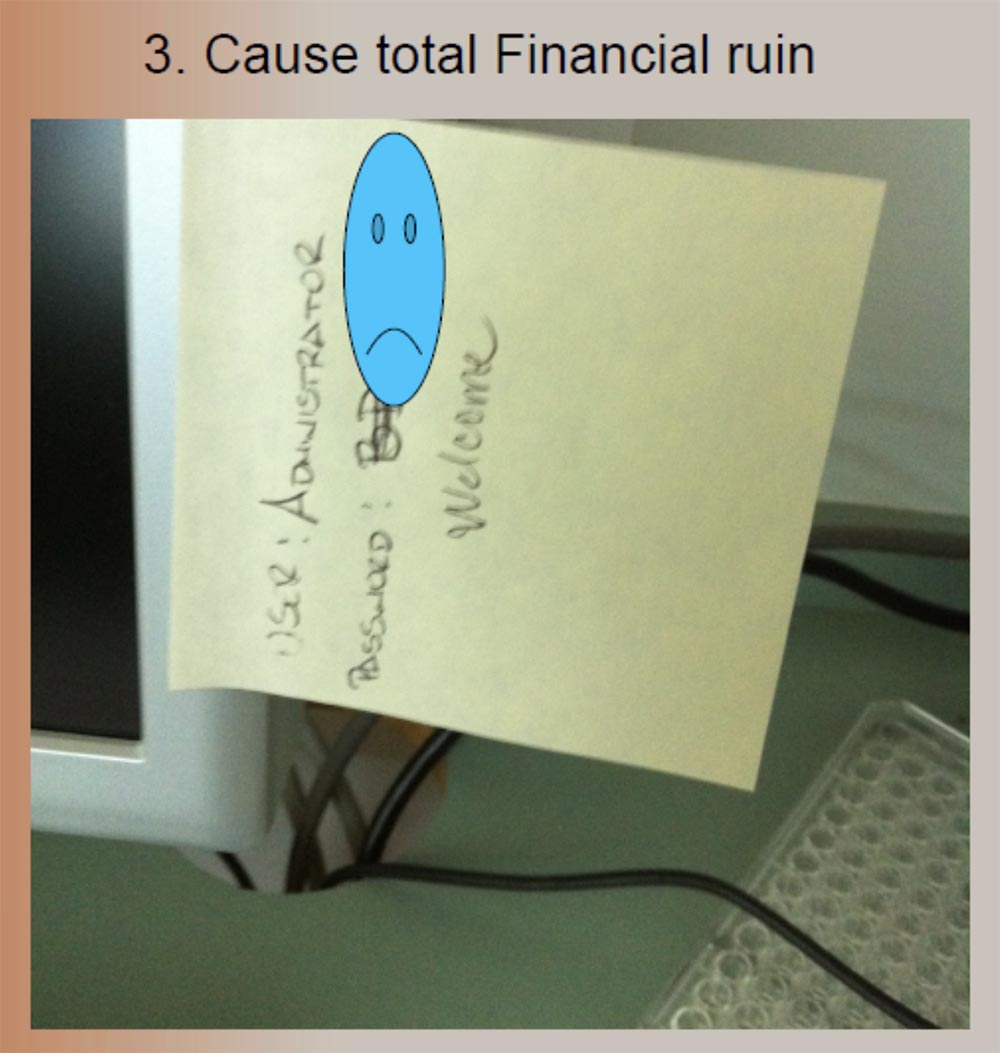
And this picture on the top slide is one of my favorites. This is the office of a pharmaceutical laboratory that performs biochemical research. These are complex things, so let's end the rocket science and write a password easier. And they cross out a special alphanumeric password, which was quite complicated, and replace it with this word Welcome. Indeed, welcome to my computer!
There is a worse thing than to see me in Pepsi pajamas - to see me in a strict suit, because it gives me the opportunity to do really awful things. Because if I'm in this suit, then I want to “throw” you.

Next to him, my favorite clothes are the waistcoat, which I call Wasted Doom, “Mindless Death”, because I think it sounds cool.
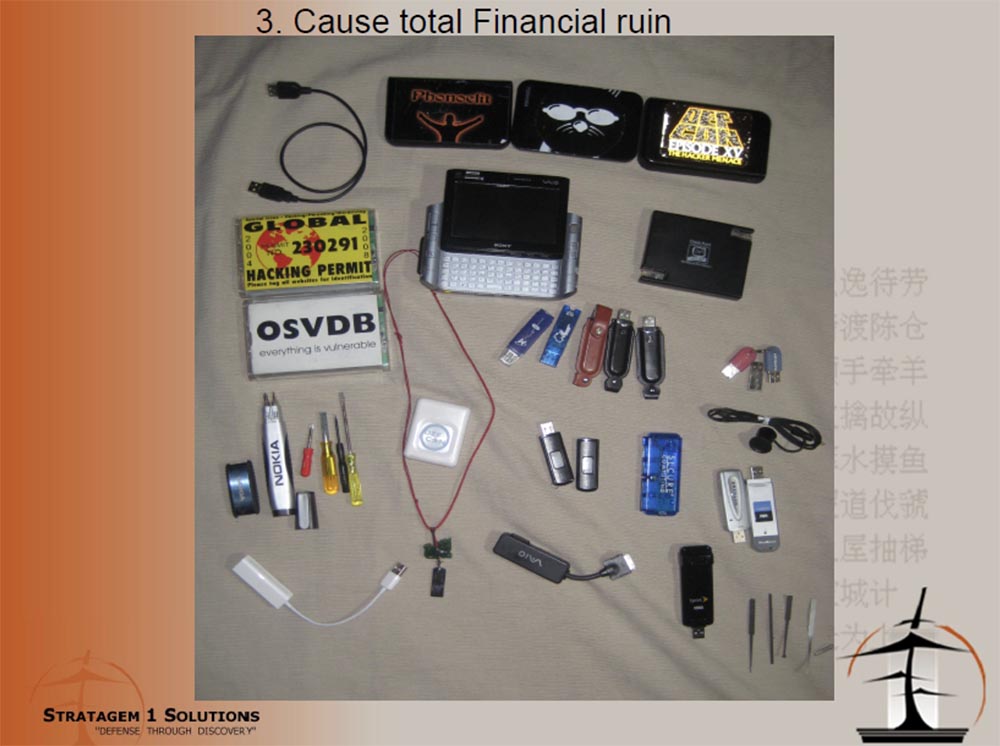
On this slide you see my “toys”, I told about them last year, and now I already have a version of the Wasted Doom 2.0 vest. I use these kind of writing pens with a video camera and USB, I do not leave them in my pocket, but I put it in your little pencil cup and leave, and the built-in video camera will record all your logins, passwords and your conversations.
I have a stunning little flashlight - a video camera with 8 GB of memory and USB, so that I can steal your data with it, besides, a video recorder is also built into my watch. With these devices, I can do whatever I want. They were provided to me by one agency of 3 letters, located in the District of Columbia, and the only condition for the use of this equipment, on the creation of which billions of dollars were spent, was my obligation to never talk about it publicly.
Another device that I carry in my vest looks like a regular USB “flash drive”. This is Spy Keylogger, or a keylogger who can intercept and record all manipulations with a computer keyboard. It is not detected by any antivirus, it is very difficult to detect visually and simply insert into any free connector - there are 2 versions, under USB or PS2 keyboard connector. He writes everything you type on the keyboard. I found it on the Think Geek website.

The following site shows the Risk Matrix.

Vertically, the axis of probability of risk when using spyware, available for purchase on the site of Think Geek, and horizontally - the intensity or degree of impact. Low risk is shown in green, medium - in yellow, and red means a complete disaster. So, interception of keystrokes of a computer keyboard by the CEO, or the chief executive officer, leads to just such consequences.
It is believed that there is a very limited group of people who have access to all the espionage technologies shown here. But imagine, it turns out, anyone can buy them - these are many advertising tools for office espionage that are shown on these flyers. Do you think that only hackers can steal data? Not at all!
If I really hate my boss, I hate my job, I want to steal a whole bunch of company secrets, what will I do? I will use these flyers, which are thrown into my mailbox, and I see that I can use this keyboard interceptor to steal information from the boss’s computer, I use a video recorder to record secrets and an audio recorder to record confidential talks and meetings. That's not difficult. I always say it is easy to do if you can do it yourself! People are protected from serious threats coming from outside, but do not take into account the risks associated with threats within the company.
The next slide shows the connection of adapters for Pony Express in a branch of one of the banks on the west coast. I had 4 branches, 4 attempts, 4 success. After the 4th try, they finally told me to stop. The reason why I managed to do this, why I was able to penetrate these branches unhindered, was as follows.
I came to them wearing a blue DEFCON jacket, I was wearing working clothes, I had warning stripes on it, and I told them that they had sent me from the main office. I said that we had a voltage drop in the network, and I need to check if it affected your operations, so insert this device into your network so that you can take readings and transfer them to the main office so that they understand , what's happening. And by the way, I need to go in and make sure that all the computers are working properly, they were not affected by power surges, and that the UPSs are in good condition.
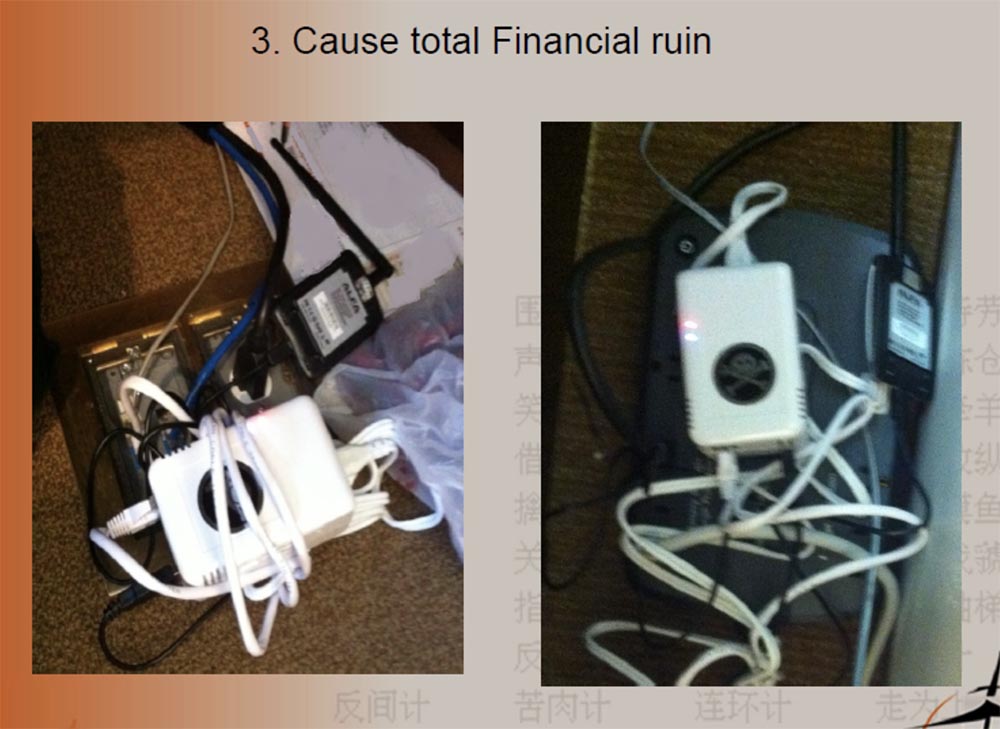
I had a fake name, a fake equipment supplier, a fake company phone number, but I got away with it. If I had rushed to them in a mask with a shotgun in their hands, they would know how to act, they were taught this. But they did not foresee the option of such an obsessive as me. They led me through the checkout area, through the back rooms, past the vault of money, past the large safe. Imagine how much damage I could do to them! But all I did was connect my little Pony Express adapter. On the right of the slide you see the UPS where I connected, for this I had to ask the manager to get up from his desk.
Therefore, I want to tell you about countermeasures against internal espionage:
- Since most of the information is stored on paper, companies must destroy all documents in the shredder before they are thrown away.
- Do not print important information unnecessarily. After printing, place it in a secure envelope or place it in a place inaccessible to third parties.
- Information freely lying on a table can be copied, photographed, or stolen.
- Keep all important documents in locked cabinets. Lock the locker when not in use.
- Companies must invest in technology that prevents the copying of sensitive information.
- Companies can set access control to the software with the indication of authorized persons who are allowed to print specific pages of certain documents. This will prevent the negligent attitude to printing documents, exposing the company to unnecessary risks.
- Print encryption is another method to protect company confidential information. When printing a document, confidential information is hidden in special fields where encryption occurs. Only persons authorized to view such information can see the encrypted information.
First of all, you need to teach your employees not to click on phishing links in emails, not to go to malicious sites, not to say that this stupid user has gone there, not to call them stupid, but to teach that you can't do that. It’s like I hire an employee who doesn’t have a driver’s license, and then give him the keys to the car and say: “Go, get my Bentley here!”, He drives and breaks the car. But an idiot is not the guy who drove the car, but the one who gave him these keys! If you give employees technology, you should teach them how to use them. You need to teach your employees to understand what they are going to do. You need to strengthen your employees. When I say "strengthen", I do not mean the trade unions, or the fact that they have to arm themselves with baseball bats, although it would be cool.
It is necessary that your employees know that they are part of your company's security team, from the CEO to the courier, so that they understand how much depends on them. They need to know that safety is their job and their duty, that they are required to observe safety.
I have a guy at work who weekly sends me 15 letters from his email that he considers phishing or just weird for me to check for malware. And every time I say “great, thank you” to him, because the 16th letter can be really dangerous and will not be a false alarm. It is necessary to make people notice that someone without a badge is in the wrong place, and stopped him and asked what he was doing here. We need to tell people that they did the right thing. For this to create competition, for the employees to say: “This damn Susanna always gets a loan, because she does such things!”, So the others should do the same, they should catch those who have no badge. This does not mean that they should stop someone by force, for that there is a guard.
You have a huge human potential to ensure safety, so just learn how to use it correctly! And as soon as you stop talking “stupid users” and start saying “my colleagues in the department of information security”, you will win!
Thank you for staying with us. Do you like our articles? Want to see more interesting materials? Support us by placing an order or recommending to friends, 30% discount for Habr's users on a unique analogue of the entry-level servers that we invented for you: The whole truth about VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps from $ 20 or how to share the server? (Options are available with RAID1 and RAID10, up to 24 cores and up to 40GB DDR4).
Dell R730xd 2 times cheaper? Only we have 2 x Intel Dodeca-Core Xeon E5-2650v4 128GB DDR4 6x480GB SSD 1Gbps 100 TV from $ 249 in the Netherlands and the USA! Read about How to build an infrastructure building. class c using servers Dell R730xd E5-2650 v4 worth 9000 euros for a penny?
