Tor releases obfuscated proxy to mask traffic in Iran
Judging by reports from Iranian users, from Thursday January 9, some Internet service providers in the country began filtering Internet traffic by signature ( deep packet inspection ), blocking almost all SSL / TLS packets. Thus, HTTPS services, including Gmail, Google search, and websites of other Internet companies, stopped working for users. SSH tunneling on the Iranian Internet has been blocked a few months ago.
Tor experts analyzed how local authorities block HTTPS, apparently, this is done in three ways:
- deep packet inspection for SSL
- selective blocking of combinations of IP addresses and TCP ports
- keyword filtering
SSL blocking is not complete and nationwide. Until now, most users have HTTPS. In other places, apparently, the system recognizes packets at the beginning of the “handshake” of SSL and simply stops the procedure for setting up a secure connection.
Judging by the statistics of direct connections from Iranian IPs , so far the HTTPS blocking is not particularly applied, although there is some decrease in traffic. However, Tor experts believe that in the near future filtration will spread to all of Iran. Therefore, they offer such a solution .
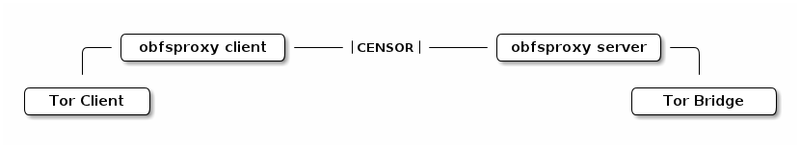
Private network bridges operators are invited to install a special obfuscated bridge that will mask HTTPS traffic - especially for Iran. See the instructions for installing such a bridge here . On the other hand, users will also need to install the obfsproxy program to obfuscate traffic.
Private bridges are not listed in the general Tor node catalog, but are reported only upon request from a specific network segment . Thus, users from Iran will be able to use your network bridge, if necessary. Obfuscating traffic, theoretically, will bypass the blocking of signatures by the Iranian authorities.
