LNKpokalipsis or new bagofic from MS (CVE-2010-2568)
On a habr already wrote about Win32 / Stuxnet and the vulnerability revealed with it . But for some reason little attention is paid to the vulnerability itself, basically all the noise around Win32 / Stuxnet and the valid certificates used to sign the components of this malware. Meanwhile, this vulnerability has already appeared in the public domain. First in the form of PoC , and then in the form of a module for Metasploit. MS, as in other things and usually, does not care about the criticality of this vulnerability and it is most likely to release a patch no earlier than August 10. And for WinXP SP2 there will be no patch at all, although it is not strange that there are still users on it and they are not as few as we would like. Symantec window threat distribution confirms thiswhere exactly WinXP SP2 has a large share of recorded incidents.

As vectors for exploiting this vulnerability, not only USB storage devices can be stored, but also network resources. For example, in Metasploit, exploitation takes place via WebDAV.
The vulnerability works something like this:
This is not about a banal overflow or an unnamed pointer, everything is much worse, because vulnerability by design, so to speak (all versions of Windows are vulnerable). Those. the developers slammed their ears that attackers could use this path to install all kinds of malware. Although it can be much worse and is it just another backdoor left in the system at the request of the NSA? I'm afraid of the truth, we will never know. Now let's talk directly about the technical details of how this vulnerability works.
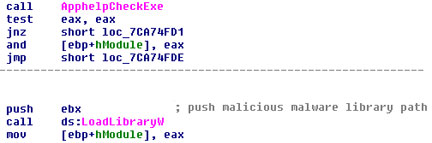
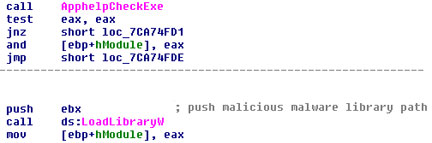
CVE-2010-2568 - the vulnerability is in the LNK file handler, more precisely it is related to the process of displaying the Control Panel shortcuts when they are loaded into memory by the Explorer.exe process. The shell32.dll library in which incorrect processing occurs is vulnerable. The following diagram illustrates the data flows between the called functions during the exploit (see here ). A successful exploit is loading a third-party dynamic library using the WinAPI function LoadLibraryW .

The sequence of calls looks like this: Actually, the code below makes the malicious DLL execute, this code is in the _LoadCPLModule function , which is called from
CPL_LoadCPLModule .
A Metasploit exploit for exploiting a vulnerability generates a URL like " {webdav} {exploit_base} \\ {exploit_dll} ", this approach to exploiting this vulnerability greatly expands the scope of its exploitation beyond USB drives. What to do and how to protect yourself from this vulnerability can be read here . More on countering this vulnerability can be found on the blog of the independent researcher Didier Stevens. Two methods are described there:
1) Prohibition of autorun and execution of executable modules from external media. But this will not save you from the possibility of infection with a network balloon and WebDAV links.
2) Installation Software Restriction Policies (SRP)

As vectors for exploiting this vulnerability, not only USB storage devices can be stored, but also network resources. For example, in Metasploit, exploitation takes place via WebDAV.
The vulnerability works something like this:
This is not about a banal overflow or an unnamed pointer, everything is much worse, because vulnerability by design, so to speak (all versions of Windows are vulnerable). Those. the developers slammed their ears that attackers could use this path to install all kinds of malware. Although it can be much worse and is it just another backdoor left in the system at the request of the NSA? I'm afraid of the truth, we will never know. Now let's talk directly about the technical details of how this vulnerability works.
CVE-2010-2568 - the vulnerability is in the LNK file handler, more precisely it is related to the process of displaying the Control Panel shortcuts when they are loaded into memory by the Explorer.exe process. The shell32.dll library in which incorrect processing occurs is vulnerable. The following diagram illustrates the data flows between the called functions during the exploit (see here ). A successful exploit is loading a third-party dynamic library using the WinAPI function LoadLibraryW .

The sequence of calls looks like this: Actually, the code below makes the malicious DLL execute, this code is in the _LoadCPLModule function , which is called from
SHELL32!CRunnableTask::Run
SHELL32!CGetIconTask::RunInitRT
SHELL32!SHGetIconFromPIDL
SHELL32!CFSFolder::GetIconOf
SHELL32!SHGetIconFromPIDL
SHELL32!_GetILIndexGivenPXIcon
SHELL32!CShellLink::GetIconLocation
SHELL32!CExtractIconBase::GetIconLocation
SHELL32!CCtrlExtIconBase::_GetIconLocationW
SHELL32!CPL_FindCPLInfo
SHELL32!CPL_LoadAndFindApplet
SHELL32!_LoadCPLModule
SHELL32!_imp__LoadLibraryW
CPL_LoadCPLModule .
A Metasploit exploit for exploiting a vulnerability generates a URL like " {webdav} {exploit_base} \\ {exploit_dll} ", this approach to exploiting this vulnerability greatly expands the scope of its exploitation beyond USB drives. What to do and how to protect yourself from this vulnerability can be read here . More on countering this vulnerability can be found on the blog of the independent researcher Didier Stevens. Two methods are described there:
1) Prohibition of autorun and execution of executable modules from external media. But this will not save you from the possibility of infection with a network balloon and WebDAV links.
2) Installation Software Restriction Policies (SRP)
