Wardriving in MAC OS X
- Tutorial

The de facto standard in wardriving is usually considered the Linux system (modified drivers, Kismet in conjunction with aircrack-ng ). But few people know that the poppy has powerful tools for
UPD: The tools described in the article are outdated today. Using Linux Recommended.
For a general understanding of wardriving, it is recommended that you read this Kismac article
.- A powerful all-in-one program. A big advantage over Linux is that wi-fi card drivers are integrated directly into the program and you do not need to install additional modules. All actions for network scanning, traffic collection and analysis (in Linux, airdump, airmon, airplay commands) are performed in one place from the graphical interface, which greatly simplifies the process.
Features of the program:
- passive scanner / sniffer
- packet injection
dump in the standard PCAP format, which is understandable for all packet analyzers (for example, Wireshrak ) - in the presence of a GPS module, it can mark the found networks on the map
- sound indication of signal strength (like a metal detector)
- dump recording from kismet drone server
Kismac also has tools for decrypting WEP / WPA algorithms, but the authors of the program say that they have not been developed for a long time and recommend using the latest version of aircrack-ng, which can be installed from source or using the fink port system .
Equipment selection
The Airport Extreme card integrated into the MacBook is not suitable for wardriving. It is impossible to inject packets, and due to the low sensitivity of the receiver, traffic collection for analysis must be carried out in the immediate vicinity of the signal source. The only reason it is suitable is an initial inspection of networks: you can find out the type of encryption used, the presence of clients at points, etc.
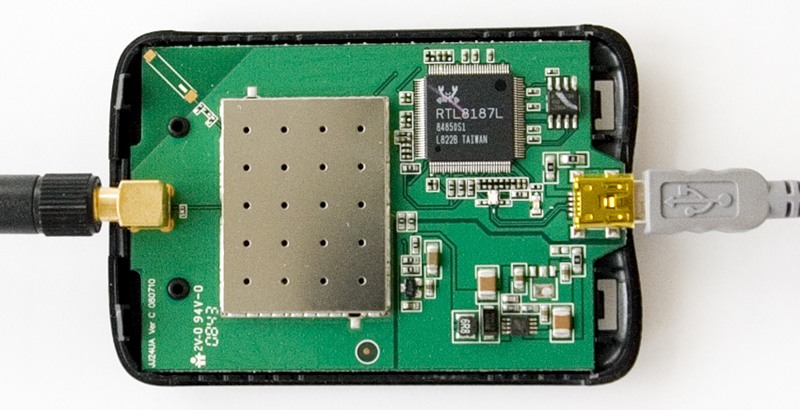
For a deeper study, you need a card that supports packet injection (see the list of devices ). The best choice would be an Alfa AWUS036H cardon the RTL8187L chipset. It is recommended by the developers of kismac and aircrack-ng. It is supported by all wardriver programs in all operating systems, it has a very sensitive receiver. Transmission power 500 milliwatts. Equipped with an RP-SMA connector for connecting external antennas.
The Chinese make these cards under different names, for example G-SKY or IDU-2850UG-8G or Kinmax .
In principle, you can choose any of the supported cards, but this one has the best characteristics, it is cheap and easy to find.
To start working, you need to select the driver for your device:
KisMac => Preferences ... => Driver
To get acquainted with the program and for lack of other cards, select Airport Extreme Passive mode.
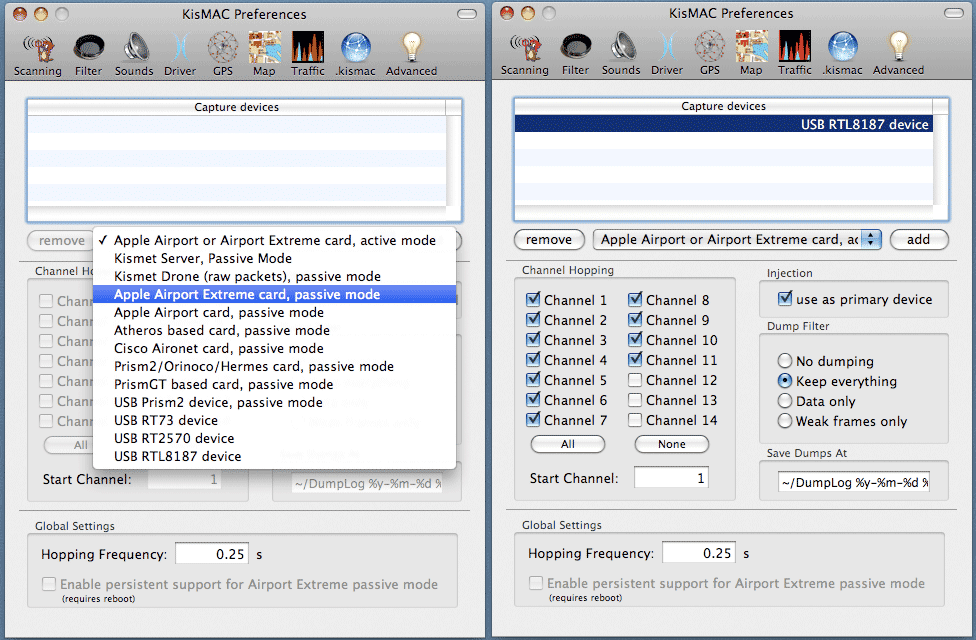
Channel Hopping - select all European channels 1-11.
Use as primary device - to activate the package injection function (not possible in Airport)
Dump Filter - which data to write to the dump file, select “Keep everything”.
Save Dumps At - path and name of the dump file.
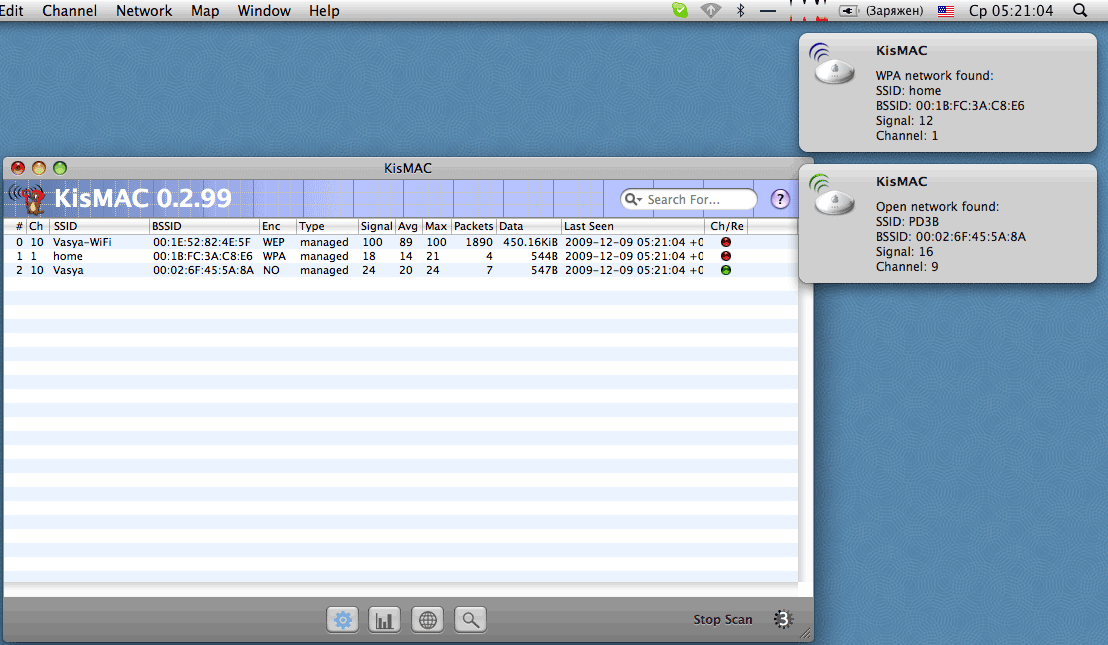
Now you can start scanning. The program will report on all found networks. The changing numbers in the lower right corner mean that the device is in Channel Hopping mode, jumping in frequencies to find networks working on all channels. It is also necessary to keep in mind that the card jumps through the channels very quickly (the speed is adjusted when choosing a driver), so there is a possibility that some networks may not be detected. To eliminate this, you can go through each channel separately. When you have chosen the network of interest, you must stop Channel hopping and set the channel on which the selected network works.
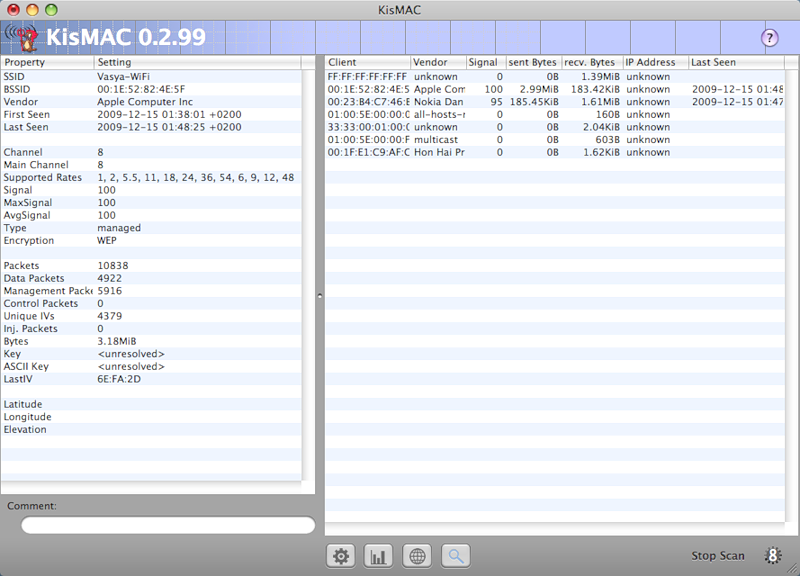
Double-clicking on the selected network will show detailed information.
On the left is technical information, on the right is a list of clients connected to the point. Really connected clients are set to Last Seen.
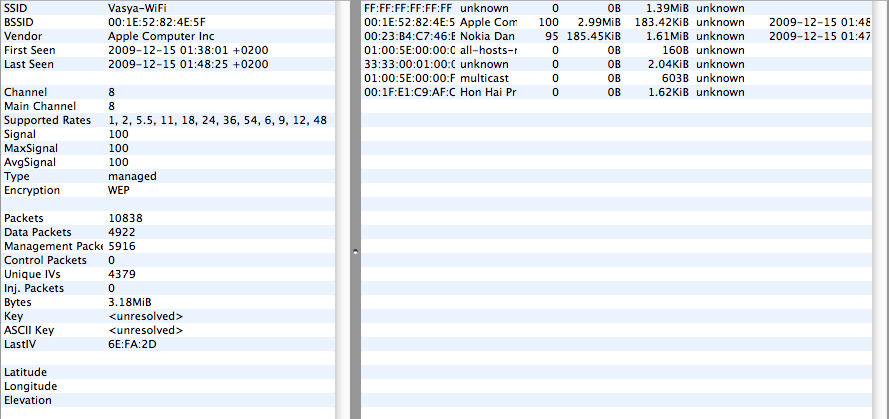
An important factor is the signal strength.
Signal - signal strength
AvgSignal - signal quality (useful signal including interference)
MaxSignal - maximum fixed signal level
For successful packet injection, the point signal and client signal should not be lower than 40-50. It is necessary to find the optimal antenna position at which the signal will be maximum. Sometimes a change in position even by one centimeter can significantly affect the signal level. You can also turn on the sound indication of signal strength in the menu "Network => Monitor Signal Strenght", depending on the signal level, the tonality of the sound will change.
Open Network Sniffing
In networks without encryption, all traffic can be freely viewed. To do this, just configure the card to listen to the frequency at which the network is operating (Main channel), and collect all the traffic in a file. Then the dump can be viewed by the packet analyzer.
For example, at the next table in the cafe Vasya! * SuPeR-ViP *! Pupkin logged in to contact:
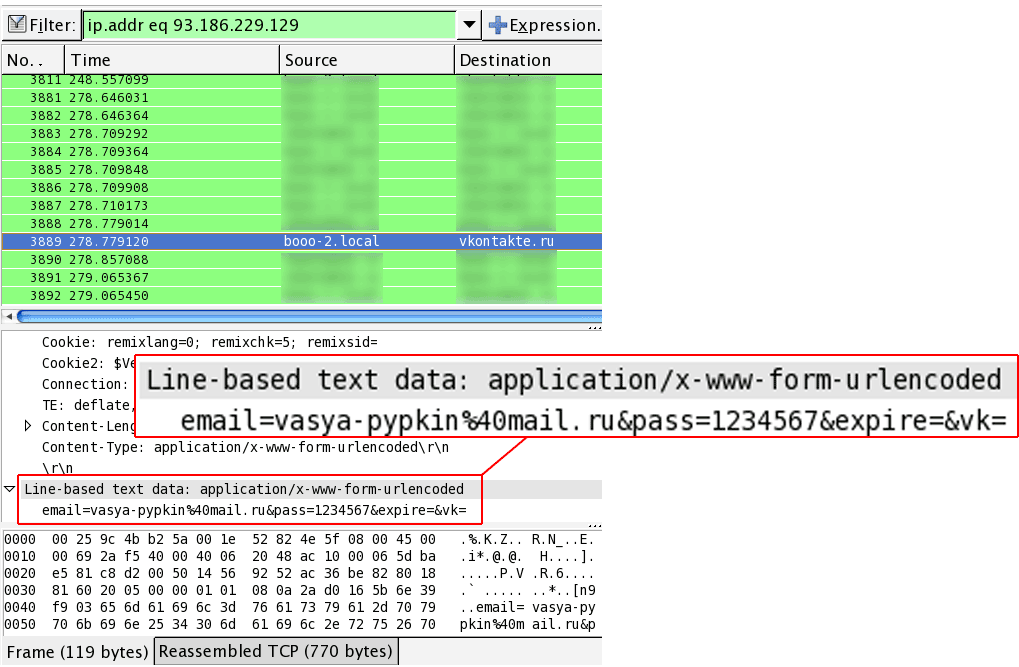
In loaded networks, dumps fill up very quickly, and filters can be applied to speed up the opening of a wireshark dump. For example, select only by protocol or IP. You can also disable address resolution.
Hacking WEP
The bottom line is to collect a large number of service packages containing the Initial Vector, and from them to decrypt the network key. Initialization vectors are transmitted to control the connection of the point with the client, respectively, the attack is feasible only when there are connections to the point.
To successfully find the key, you need to collect more than 70 thousand packages (in practice, 20 thousand are enough). It is not possible to collect such an amount by passively listening to the broadcast. To speed up the process, there is a packet injection method to force hosts to generate a large number of IV packets. To start the injection, you need to have a certain amount of Initial Vectors, so you can just wait or catch the traffic with an authorization flood: Network => Authentication Flood (Similar to a DoS attack. Be careful with this option, the access point may hang). After that, you can start the injection: Network => Reinject Packets .
If the injection attempt was successful, the number of packages we need (Unique IV's) will begin to increase dramatically.
Run the decryption of the key in parallel using the aircrack-ng program.
In the terminal, enter:
aircrack-ng /path/to_dump.file
If you do not specify the mac address of the attacked access point, the program prompts you to select from all the points found in the dump. You can specify the mac address with the -b option:
aircrack-ng -b 00: 00: 00: 00: 00: 00 /path/to_dump.file
Hacking WPA / WPA2
Today, the WPA algorithm is quite reliable. The only hacking option is brute force (dictionary search).
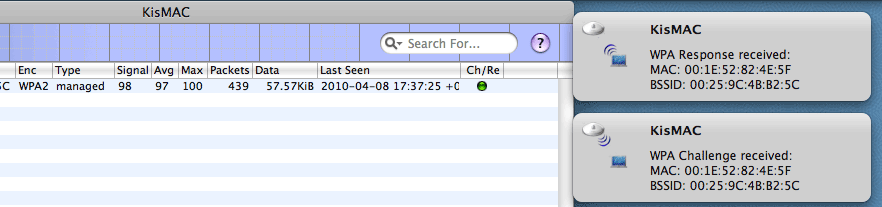
The task is to intercept the “handshake” (handshake) at the time of client authorization at the access point and the subsequent enumeration of passwords in the dictionary. To do this, we need to either wait until the client comes in to log in or try to disconnect existing connections in order to provoke reconnection:
Network => Deauthenticate
It is important to catch both parts of the handshake: Challenge and “Response. If successful, the red Ch / Re dot will turn green.
It often happens that you can only catch the answer of the point (Challenge), but the response of a low-power client (for example, a mobile phone) fails. In this case, you need to find the position of the antenna at which the client signal will be maximum. The
key search looks like this:
aircrack-ng -w keys.txt -b 00: 00: 00: 00: 00: 00 dump.file
where keys.txt is the path to dictionary, 00: 00: 00: 00: 00: 00 - the mac address of the attacked point, dump.file - the path to the file with the handshake.
Having an encryption key, you can listen to all traffic passing on the network. To do this, use a dump descriptor:
for WEP encryption, the key is specified with the -w option:
airdecap-ng -w 12345678 /path/to/wep.dump.file
for WPA / WPA2 with the -e network_name -p network_key option:
airdecap-ng -e 'Cool -WiFi '-p 12345678 /path/to/wpa.dump.file
As a result, a decrypted dump file will be created which can already be viewed by the packet analyzer.
