Cellular Interception FAQ: What are IMSI Interceptors / SCATs and Can I Protect Against Them?
Наверное, даже домохозяйки знают, что публичные точки Wi-Fi небезопасны. Что не мешает рядовым юзерам вовсю ими пользоваться — ведь если нельзя, но скучно и очень хочется, то можно! И без всякого VPN — хотя функцию VPN теперь внедряют даже в комплексные антивирусные продукты. Здоровой альтернативой Wi-Fi всегда считалось обычное мобильное подключение, тем более что с каждым годом оно становится все дешевле, а скорость его все выше. Но так ли оно безопасно, как нам кажется?
- What is an IMSI interceptor?
- When did the first IMSI interceptors appear?
- How do IMSI interceptors monopolize access to a mobile phone?
- Are there handicrafts?
- Can I become a victim of “accidental interception”?
- How can an IMSI interceptor track my movements?
- Can they listen to my calls?
- Can they install software on my mobile phone?
- We all know about the dangers of open (and not only) Wi-Fi points. Can I become a victim of interception if I sit everywhere strictly through LTE?
- And if I am a cool banker and they may really, really want to sniff me?
- What data can I lose if you consider the fact that I have HTTPS and two-factor authentication everywhere?
- How are they protected from interception?
- Can ESD Overwatch provide 100 percent protection?
- Will IMSI interceptors continue to listen to me if I change my SIM card?
“And if I'm on CDMA, will I be safe from the IMSI interceptor?”
- Why are bad guys using IMSI interceptors?
- How common are IMSI interceptors today?
- In general, how promising is the IMSI interception technique? Maybe there are some more effective alternatives?
- What is the attitude of the special services to pirates-interceptors? What happens if I walk past the Lubyanka with an IMSI suitcase?

Note: Please note that among the hyperlinks listed in the article there are links to US Department of Defense materials. Going through them from a normal browser does not work - use the TOR browser, or its equivalent.
We are now on the eve of an era where almost everyone can listen to telephone conversations. Our time is similar to the dashing 90s, when using cheap Soviet analog scanners you could listen to mobile conversations in the USA and Europe. Only today, not analog scanners, but digital IMSI interceptors rule the show.
What is an IMSI interceptor?
This is such a device (the size of a suitcase or even just a mobile phone) that uses the design feature of mobile phones - to give preference to the cell tower whose signal is the strongest (to maximize signal quality and minimize its own power consumption). In addition, in GSM (2G) networks, only the mobile phone must pass the authentication procedure. This is not required from the cell tower. Therefore, the mobile phone is easy to mislead, including to disable data encryption on it. UMTS (3G) universal mobile communication system, on the other hand, requires two-way authentication; however, it can be bypassed using the GSM compatibility mode present in most networks. 2G networks are still widespread - network operators use GSM as a backup network in places where UMTS is not available. So this is background information about IMSI interceptors. Deeper technical details of IMSI interception availablein the report of the SBA Research Center. Another meaningful description, which is the desktop document of modern cyber-counterintelligence agents, is the article “Your Secret Skat, No More Secret at all,” published in the fall of 2014 in the Harvard Journal of Law & Technology.
When did the first IMSI interceptors appear?
The first IMSI interceptors appeared back in 1993, and were large, heavy, expensive. "Long live domestic microcircuits - with fourteen legs ... and four handles." The manufacturers of such interceptors could be counted on the fingers, and their high cost limited the circle of users to government agencies only. However, now they are becoming cheaper and less cumbersome. For example, Chris Page built his IMSI interceptor for just $ 1,500 and introduced itat the DEFCON conference, back in 2010. Its version consists of programmable radio and free open source software: GNU Radio, OpenBTS, Asterisk. All the information the developer needs is in the public domain. And in mid-2016, the Evilsocket hacker offered his version of the portable IMSI sniffer for just $ 600.
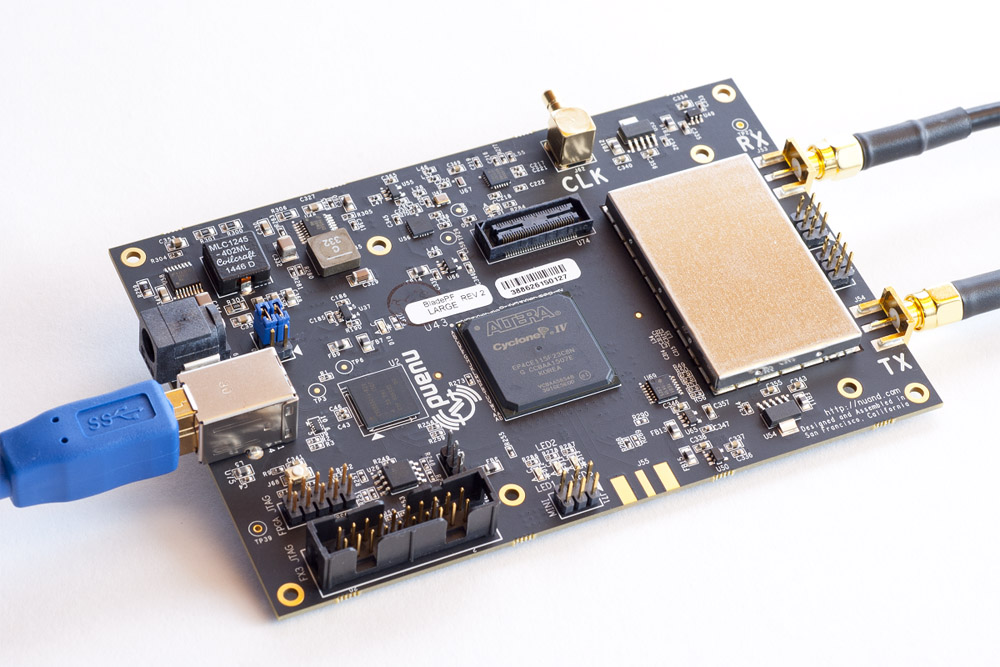 The heart of modern IMSI interceptor
The heart of modern IMSI interceptor
How do IMSI interceptors monopolize access to a mobile phone?
- They cheat on your mobile phone, making it think that this is the only connection available.
- Configured in such a way that without the mediation of an IMSI interceptor, you could not make a call.
- Read more about monopolization in the publication of the SBA Research: IMSI-Catch Me If You Can: IMSI-Catcher-Catchers .
Are there handicrafts?
- Since 2017, enterprising technical specialists have been manufacturing IMSI interceptors using high-tech boxed components available on the open market and a powerful radio antenna - while spending no more than $ 600 (see the version of the IMSI interceptor from the Evilsocket hacker). This is for stable IMSI interceptors. But there are experimental, cheaper ones that work unstably. For example, in 2013 at the Black Hat conference a version of the unstable IMSI interceptor was presented , the total cost of hardware components of which amounted to $ 250. Today, such an implementation would be even cheaper.
- If we take into account that modern Western high-tech military equipment has an open hardware architecture and open software code (this is a prerequisite for compatibility of software and hardware systems developed for military needs), developers who are interested in manufacturing IMSI interceptors have everything necessary trump cards for this. You can read about this current trend in military high-tech in the Leading Edge magazine (see the article “The Benefits of SoS Integration” published in the February 2013 issue of the magazine). Not to mention the fact that a couple of years ago, the U.S. Department of Defense expressed its willingness to pay $ 25 million to a contractor who will develop an effective system for radio identification (see April issuemonthly magazine “Military Aerospace”, 2017). One of the basic requirements for this system is the openness of its architecture; and the openness of the components of which it will consist. T.O. open architecture is today a prerequisite for the compatibility of hardware and software systems developed for military needs.
- Therefore, manufacturers of IMSI interceptors do not even need to have great technical qualifications - you only need to be able to pick up a combination of existing solutions and place them in one box.
- In addition, modern microelectronics, which is getting cheaper at an exorbitant pace, allows you to place your artisanal crafts not only in one box, but even (!) On one chip (see the description of the SoC concept ) and even more, configure an intra- chip wireless network (see the description of the concept NoC via the same link), which replaces the traditional data bus. What can I say about IMSI-interceptors, when in the public domain today you can even find technical details about the hardware and software components of the ultra-modern American F-35 fighter.
Can I be the victim of an "accidental interception"?
Without a doubt! Imitating a cell tower, IMSI interceptors listen to all local traffic - where, among other things, conversations of innocent passers-by also fall (read “The Revelations of Big Brother's Big Sister” ). And this fact is a favorite argument of "privacy advocates" opposing the use of IMSI interceptors by law enforcement agencies that use this high-tech equipment to track down criminals.
How can an IMSI interceptor track my movements?
- Most often, IMSI interceptors used by local law enforcement agencies are used for tracing.
- Knowing the IMSI of the target mobile, the operator can program the IMSI interceptor to communicate with the target mobile when it is within reach.
- After connecting, the operator uses the process of mapping radio frequencies to determine the direction of the target.
Can they listen to my calls?
- It depends on the IMSI interceptor used. Interceptors with basic functionality simply record: "in such and such a place is such and such a mobile phone."
- To listen to conversations, the IMSI interceptor requires an additional set of functions that manufacturers integrate for an additional fee.
- 2G calls are tapped easily. IMSI interceptors have been available to them for over 10 years.
- The cost of an IMSI interceptor depends on the number of channels, the operating range, the type of encryption, the encoding / decoding speed of the signal, and what radio interfaces should be covered.
Can they install software on my mobile phone?
- The IMSI interceptor collects IMSI and IMEI from your device. T.O. its operator knows which model of mobile phone you are using, and also sometimes knows where you bought it. Knowing the model number, it’s easier for him to promote a firmware update - specially designed for this mobile phone.
- In addition, your SIM card is already a computer in itself. She is able to perform simple programs without even interacting with your mobile phone. At the same time, without even knowing what kind of model your mobile phone is and what operating system it has.
- Cellular operators can update the SIM card software remotely, and moreover, “in silent mode”. Accordingly, if the IMSI interceptor is pretending to be a mobile operator, it can do the same. The SIM card computer can do the following: receive and transmit data, go to URLs, send SMS, answer and receive calls, connect and use information services, receive and process events such as “connection is established”, “connection is disconnected” etc.; run AT-commands of the mobile phone.
- At the same time, the SIM card computer can do all this “in silent mode” - so that the phone will not give a single sign of life. You can learn more about the personal life of your SIM card from Eric Butler 's presentation at the DEFCON21 conference (in 2013).
 Computer Specifications for Your SIM Card
Computer Specifications for Your SIM Card
We all know about the dangers of open (and not only) Wi-Fi points. Can I become a victim of interception if I sit everywhere strictly through LTE?
- Firstly, even if your mobile phone is configured for LTE, and shows that it works in LTE mode - it’s far from the fact that it works in this mode. With the skillful configuration of an IMSI interceptor, your mobile phone will show a regular cellular connection - 3G or 4G, and at the same time it will have to return to weaker 2G encryption.
- Some mobile phones, even in LTE mode, execute commands without preliminary authentication, although the LTE standard requires this (see the report from SBA Research already mentioned at the beginning of the article).
- In addition, since the LTE interface was not developed “from scratch”, but as a modernization of the UMTS interface (which in turn is an upgraded GSM interface), its structure is not as perfect as we would like. In addition, despite the widespread adoption of 3G and 4G networks, 2G networks still provide backup access if 3G and 4G become unavailable.
- Of course, you can set up your mobile phone so that it only connects to a 4G network, but this network is not available everywhere, and therefore the coverage area for your mobile phone will significantly narrow.
And if I am a cool banker and they may really, really want to sniff me?
- The universal mobile communication system (UMTS, 3G) and the standard for the long-term development of cellular communications (LTE, 4G) require mutual two-way authentication, but even they are not protected from IMSI interceptors. Although, of course, devices for intercepting them are much more expensive. Among others, VME Dominator from the American manufacturer Meganet Corporation claims to play this role .
- At the DEFCON 22 conference (in 2014), the hacker Justin Case carried out a demonstrative hacking of the most secure smartphone in the world - “Blackphone”. It took him only five minutes to do this ( see the slides of his speech).
- In addition, there is a system for intercepting LTE traffic, which "does not look for workarounds," but deals with a full LTE connection. This system was introduced by Tobias Engel in 2014 at the annual congress of the Chaos IT club, which was held under the heading New Dawn.
- Finally, if a "very, very strong desire to sleep" is supported by a budget of $ 100,000, then you will definitely not be able to defend yourself. Because all the most advanced technological components are available on the open market. This situation is also facilitated by the fact that the US Department of Defense even stimulates such openness - so that technology manufacturers compete among themselves for the high quality.
What data can I lose if you consider the fact that I have HTTPS and two-factor authentication everywhere?
- HTTPS is not a panacea. You won’t hide from the special services. It is enough for them to request SSL-keys from the service provider, and so they will be able to access all your data transmitted over the network. Therefore, if you are a bad guy, then you certainly will not succeed in hiding.
- In 2017, WikiLeaks published 6 documents of the Hive project - lotions for unauthorized access to encrypted HTTPS traffic, which until recently were used only by CIA officers. T.O. Today these lotions are available to the general public.
- Given the scale of the ambitions of the international intelligence services (google information about Snowden’s revelations), as well as the fact that the CIA’s hi-tech treasure has been opened wide since Snowden and WikiLeaks have submitted, anyone can be interested in your data: government intelligence agencies, commercial corporations, hooligan youth. In addition, since the average age of a cybercriminal is gradually decreasing (in 2015, the average age bar went down to 17 years), it can be expected that this hooligan youth will increasingly be behind the hacks - unpredictable and desperate.
How are they protected from interception?
- As the availability of IMSI interceptors increases, there is also a demand for protection from them. There are only software and hardware-software solutions.
- As for software solutions, there are many Android applications on the market: AIMSICD (interacts with the radio subsystem of a mobile phone, trying to track anomalies there), Femto Catcher (has functionality similar to AIMSICD, but is optimized for Verizon femtocells). You can also note: “GSM Spy Finder” , “SnoopSnitch” , “Net Change Detector” , “Android IMSI-Catcher Detector” , etc. Most of them are of poor quality. In addition, a number of applications available on the market lead to many false positives due to insufficient technical qualifications of their developers.
- In order to work efficiently, the application must have access to the base frequency range of the mobile phone and the radio stack; and also have first-class heuristics - to be able to distinguish an IMSI interceptor from a poorly tuned cell tower.
- As for hardware and software solutions, four devices can be noted: 1) Cryptophone CP500 . Sells for $ 3,500 apiece. At the time of 2014, more than 30,000 cryptophones were sold in the United States; and more than 300,000 were sold in other parts of the world. 2) ESD Overwatch . A device with a three-component analyzer (see the description below). 3) Pwn Pro . An instrument with an integrated 4G module, announced at the RSA conference in 2015; Its price is $ 2675. 4) Bastille Networks . A device that displays a list of nearby wireless devices that interact with the radio (in the range from 100 KHz to 6 GHz).
 What interceptors are on sale?
What interceptors are on sale?
Can ESD Overwatch provide 100 percent protection?
- ESD Overwatch in its basic functionality is equipped with a three-component analyzer that tracks the next three “bells”. 1) The first call is when the phone moves from a more secure 3G and 4G to a less secure 2G. 2) The second bell is when the telephone connection cuts off encryption, which makes interception much easier. 3) When the cell tower does not provide a list of other cell towers available nearby (this list allows the phone to easily switch between neighboring towers); IMSI interceptors usually do not leave alternatives, as they seek to gain exclusive access to the mobile phone.
- However, it should be understood that even such a three-component approach does not provide 100 percent protection. By the way, there is a free application (available on Google Play) that claims the same role as Cryptophone with ESD Overwatch: “Darshak” . In addition, although rare, there are cases when even with all three of the above “calls”, there is no actual IMSI interception. And naturally, the developers of IMSI-interceptors, having heard about this three-component counter-interception system, will not slow down with a retaliatory step in this “arms race”.
- Even the military cannot provide absolute protection for themselves, although they use the most advanced (at the time of 2016) IQ-Software system and hardware from PacStar. "IQ-Software" is a promising wireless tactical system for exchanging classified information with smartphones and laptops via Wi-Fi and cellular radio stations. I hope it’s not a secret for you that in modern military operations - and not only as a means of communication - the same smartphone that is in your pocket is used (more about this in the article “Safe smartphones are getting ready for deployment” ).
- For example, the US Air Force in the summer of 2013 published the announcement of “B-52 CONECT: Transition to the Digital Age” . “Combat Network Communications Technology,” or CONECT, will help the B-52 strategic ultra-long-range bomber integrate into a modern cyber infrastructure by converting this analog plane into a digital platform that can be commanded from a regular smartphone.
- It is for such purposes that the military is very interested in safe communications, but even they cannot provide absolute protection for themselves.
Can IMSI interceptors continue to listen to me if I change my SIM card?
- An IMSI interceptor captures your IMSI from your SIM card and your IMEI from your mobile phone. Then both of these parameters are stored in a centralized database. Thus, changing SIM cards and changing mobile phones will not help.
- Of course, if you take a new mobile phone and a new SIM card, then there will be no record of them in the centralized database of the IMSI interceptor. However, the people you contact will also need to purchase new mobile phones and new SIM cards. Otherwise, thanks to the cross-references of the centralized database, you will again find yourself in the list of IMSI interceptors.
- In addition, the IMSI interceptor can locate mobile devices located in a specific geolocation.
And if I'm on CDMA, will I be safe from the IMSI interceptor?
No, because the same manufacturers who make GSM IMSI interceptors also make CDMA versions; and some even make versions for Iridium (a global satellite service provider) and Thuraya (a regional satellite phone service provider that operates in Europe, Central Asia, Australia and Africa). Among them: the Israeli laboratory "Ability" and the Thai "Jackson Electronics" .
Why do bad guys use IMSI interceptors?
- To terrorize others with threatening text messages.
- Keep track of law enforcement investigations.
- Government, commercial and household espionage.
- Steal the personal information transmitted by mobile phone.
- To deprive the mobile phone user of the opportunity to contact emergency services.
How common are IMSI interceptors today?
- Aaron Turner, director of the Integricell Mobile Security Research Center , conducted his independent investigation. Over a two-day drive with a cryptophone (which tracks suspicious mobile activity), he came across 18 IMSI interceptors. Mainly near specialized government agencies and military bases.
- At the same time, Turner does not undertake to say whose IMSI interceptors they are: they are being monitored by special services, or someone is watching special services. This was back in 2014 stated «The Washington Post».
- In the same year, the results of another sensational investigation were published on the Popular Science news site , during which another 17 IMSI interceptors were discovered during the month of traveling around the USA.
- In addition, if you recall that already at the time of 2014, more than 300,000 cryptophones were sold around the world that solve the opposite task of IMSI interceptors, you can also get some idea of the prevalence of the latter. After all, it would be reasonable to assume that a significant part of these buyers also use IMSI interceptors. So your chances of running into an IMSI interceptor are very real.
In general, how promising is the IMSI interception technique? Maybe there are some more effective alternatives?
Well, since you asked ... There is Wi-Fi radio mapping, which combines the old analog school with modern digital power. This approach works at a lower level, and therefore more flexible. After all, with its help you can even follow those people who do not carry any equipment with them. Take for example WiSee , which recognizes human gestures; WiVe , which sees moving objects behind the wall; WiTrack , which tracks the three-dimensional movement of a person; and finally WiHear , which is able to read lips. But since these are fundamentally different technologies - more about them another time.
How do the security services treat pirates-interceptors? What happens if I walk past the Lubyanka with an IMSI suitcase?
- If you are impressed by the film “Who Am I” and want to play with the special services, then you have good advice: refrain. Especially when it comes to Russian special services, and especially the FSB. Serious people work there, you can’t beat them. Do not flatter yourself.
- In addition, our law enforcement agencies deserve respect. It’s not enough in which country you can calmly walk along the street, especially in the dark. And with us - it is possible. Remember this! And on occasion, thank the security forces for this.
- As the topic of cybersecurity is becoming increasingly relevant, intelligence agencies (whether Russian or foreign) are interested in qualified technical specialists. So, you can be invited to a conversation - to understand what you are. And in case you are worth something, they might even give you work. The truth is most likely without formal employment.
- So for example, as I wrote this FAQ, I had to google relevant topics. And a couple of hours after that, targeted advertising invited me to become a “communications officer” by inviting the Siberian State University of Telecommunications and Informatics to the Military Training Center .
- However ... It’s better not to pull the tiger with a mustache.
Tell me what targeting ads show you and I’ll tell you who you are!
PS Excessively active actions in the radio frequency spectrum require special approval and licensing; ignoring this fact, you automatically fall into the category of "bad guys" details - here .
