News of the week: Autonomous Runet Control Center, $ 8000 bitcoin, vulnerability in Intel processors

In this digest read:
- the rules of the Center for Monitoring and Management of the Autonomous Runet;
- Russian government agencies worked for 9 years under the supervision of the Chinese;
- Bitcoin went up from $ 5,000 to $ 8,000;
- over the year, the number of attacks on sites increased by 60%;
- Intel processors found four critical vulnerabilities;
- another version of the key to the Voynich manuscript.
The principle of operation of the Center for Monitoring and Management of Autonomous Runet
At the beginning of the week, a government decree “On Approving the Rules for the Subsidy from the Federal Budget for the Creation and Operation of a Monitoring and Management Center for a Public Communication Network, as well as the Creation, Operation, and Development of an Information System for Monitoring and Management of a Public Communication Network” was published on the official portal of legal information ".
The document describes the nuances of the Center, as well as sources of funding. The Center will be engaged in the creation and support of information systems for monitoring traffic routes on the Internet, monitoring and managing a public communications network, and filtering Internet traffic when children use sites. In 2019, a subsidy of 100 million rubles is allocated to finance the organization.
Russian structures worked for nine years under the supervision of Chinese cybercriminals
Two companies, Positive Technologies and Kaspersky Lab, announced the discovery of a cyber grouping that successfully attacked more than 30 Russian companies and government agencies over several years. Presumably, the group operates from China .
In most cases, group members used a similar work scenario. The first step was the formation of a specific task in the task scheduler. Then, specialized OS and software teams were launched, which made it possible to penetrate the organization’s network. How cybercriminals used the information received is unclear.
In five days, bitcoin went up from $ 6,000 to $ 8,000
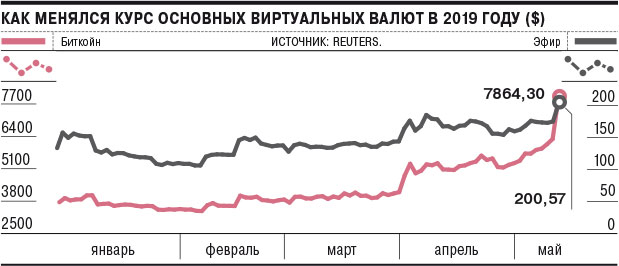
In just a few days, bitcoin grew from $ 6,000 to $ 8,000 , and unexpectedly for many. And this is not a short-term leap, since the value of bitcoin does not fall. The reasons for the growth are still unclear. Perhaps the stimulus for growth was positive news.
The growth of bitcoin is part of a wider cryptocurrency boom. Last Saturday, the price of ether (Ethereum) for the first time in 2019 rose above $ 200. Other cryptocurrencies, including Litecoin, Bitcoin Cash, Monero and Dash, are at or near the highs of 2019.
The number of malicious attacks on websites increased by 60% over the year
Analysts estimate that last year attackers attacked 62 sites per day, the total number of attacks increased by almost 60% compared to 2017. At the same time, infected sites occupy only 1% of all existing sites. In absolute terms, this figure is more impressive - the fact is that malicious activity is detected on 17.6 million resources.
However, webmasters of many resources continue to neglect the basics of security, apparently believing that search engines will warn the owner of the threat. But in fact, this does not always happen.
The most vulnerable are sites with common CMS like WordPress and Drupal. According to analysts, there are serious gaps like XSS or CSRF, vulnerabilities to SQL injection on 20% of WordPress sites and 15% of resources based on CMS Joomla. In the case of Drupal, this figure was only 2%, but in this system there are most kernel vulnerabilities - such problems were found in 34% of Drupal sites.
Critical Vulnerabilities in Intel Processors
Many media reported on four new vulnerabilities in Intel processors . They give attackers the ability to steal user data. It is possible to fix the problem, although it is rather difficult - you need to update the processor microcode, releasing patches for operating systems. In this case, the correction can lead to a drop in PC performance up to 40%.
Official Vulnerability Codes - CVE-2018-12126: Microarchitectural Store Buffer Data Sampling; CVE-2018-12130: Microarchitectural Fill Buffer Data Sampling; CVE-2018-12127: Microarchitectural Load Port Data Sampling; CVE-2019-11091: Microarchitectural Data Sampling Uncacheable Memory The names are given for a reason, they indicate which processor element can be attacked.
Linguist found the key to Voynich manuscript

And again, news about the Voynich manuscript - one of the most mysterious in history. In late April, linguist Gerard Cheshire of the University of Bristol published an article describing the language system of the document . The scientist believes that the language of the manuscript is Protoromanian, listing the characteristic features of the language and individual fragments of the manuscript as evidence.
According to the researcher, the language was distinguished by a complex sound system, had no punctuation marks in their classical form and was subject to strong influence of Latin. The main focus of the article is on the writing system and identifying links with other languages, which should confirm the hypothesis of the Protoromanian origin of the text.
