And again the wolf in sheep's clothing
A phishing site should look believable enough to match any of the cybercriminals' legends. Often, something related to security is chosen as a legend, such resources arouse more trust among potential victims. And here is a fresh example of this approach: sbersecure.ru .
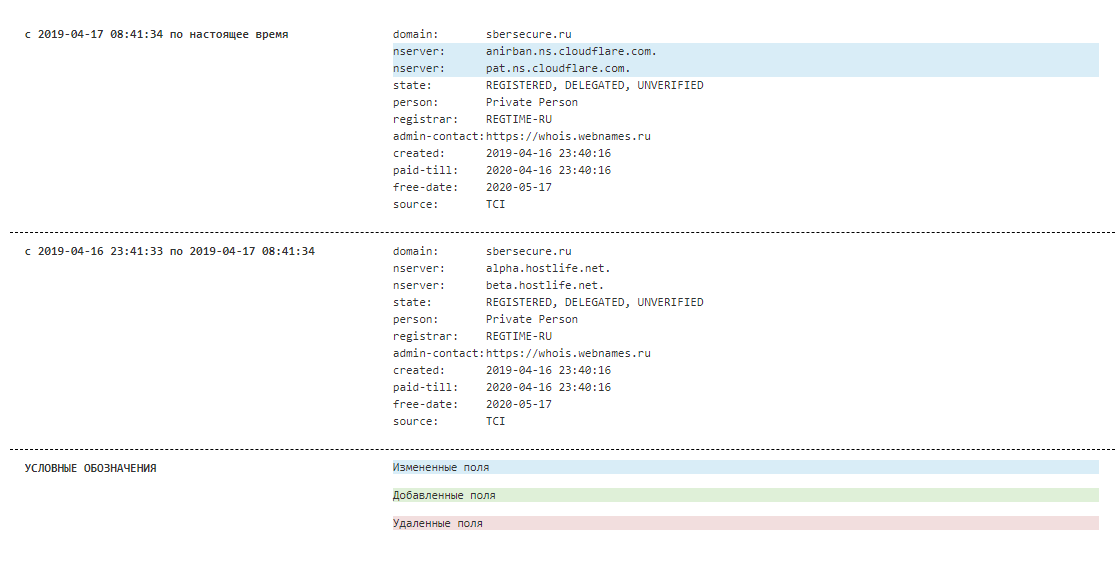
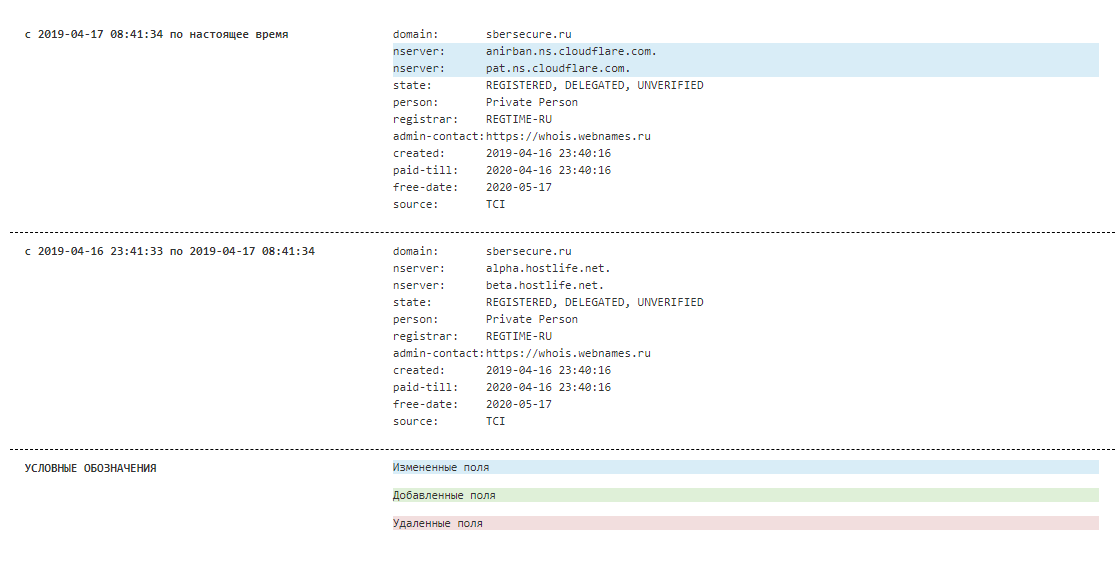
Events around the site developed rapidly. The domain name was registered in the evening of April 16, and the next day a phishing site appeared on it. Initially, the servers of the Russian Hostlife hoster were specified as DNS, however, after only 9 hours, the addresses of CloudFlare, a company that does not need to be presented, appeared in NS records. April 17 at 15 hours Moscow time, the resource acquired an encryption certificate issued by the same CloudFlare.
Take a closer look at the phishing site.
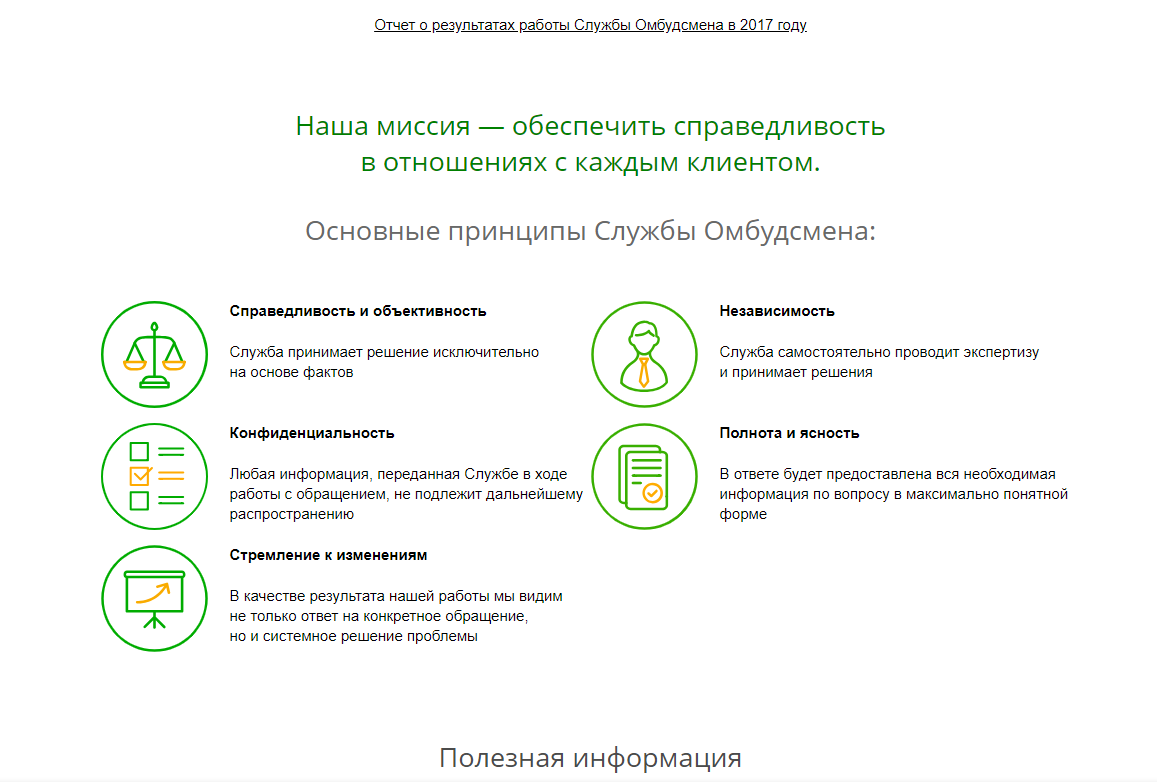
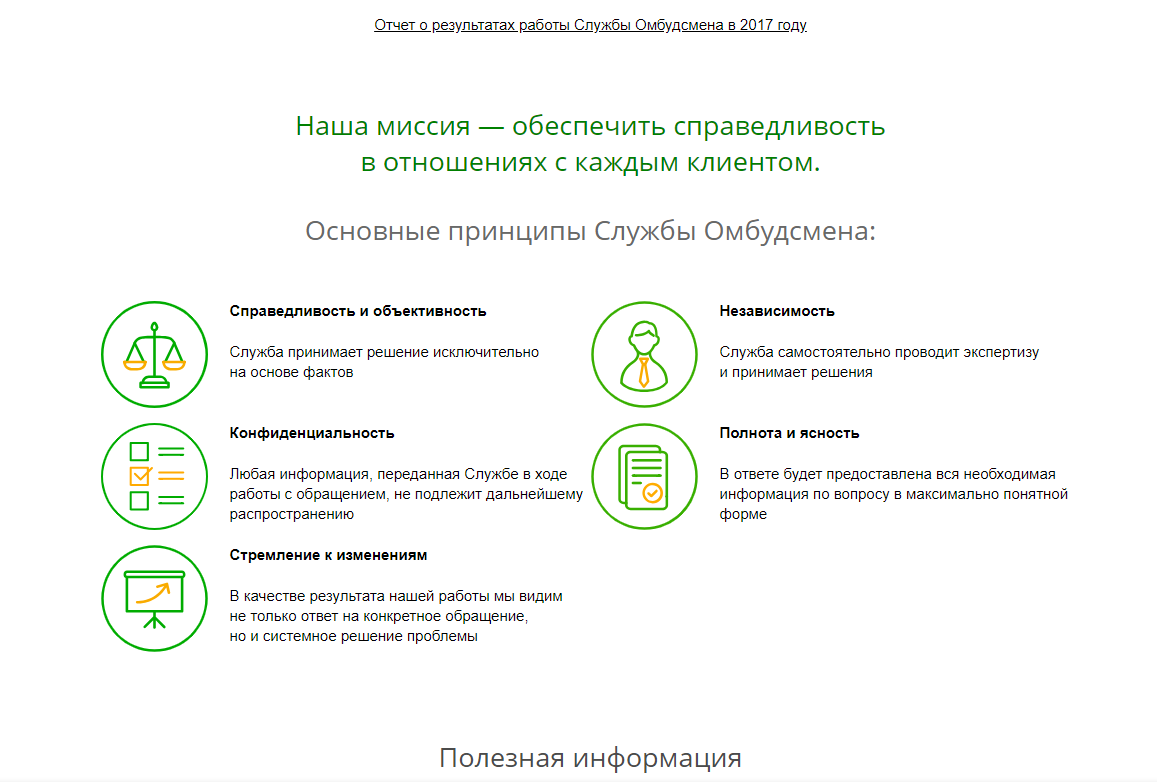
To create the resource, a fairly popular method of partial copying of the original site was used. In this case, the attackers took the Bank’s Ombudsman’s Service page as a basis, changing the words “Ombudsman’s Service” to “Customer Security Service”.
Here is the original Ombudsman Service page.
And here is a phishing site.
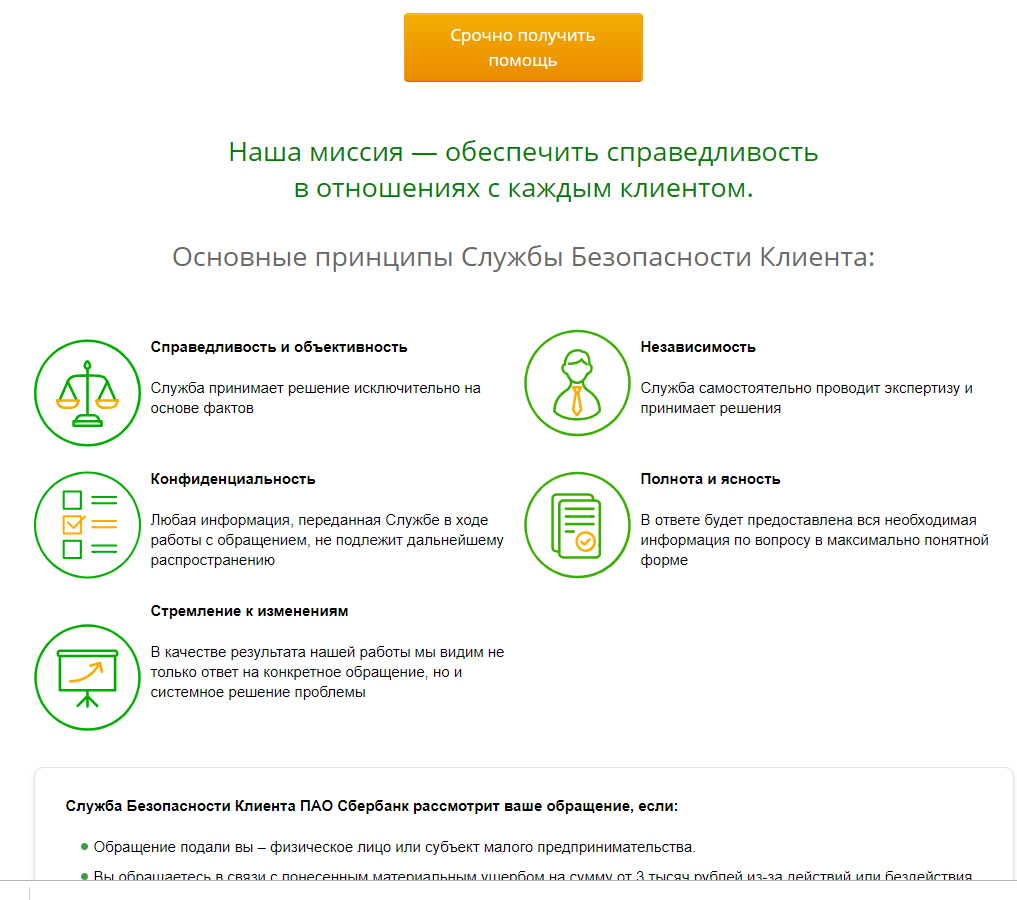
At the same time, the changes affected only the central part of the site, the header, context menus and footer completely repeat the original design. All links, including a link to the authorization page in the Sberbank.Online service, lead to the real site of Sberbank.
General view of a phishing site.

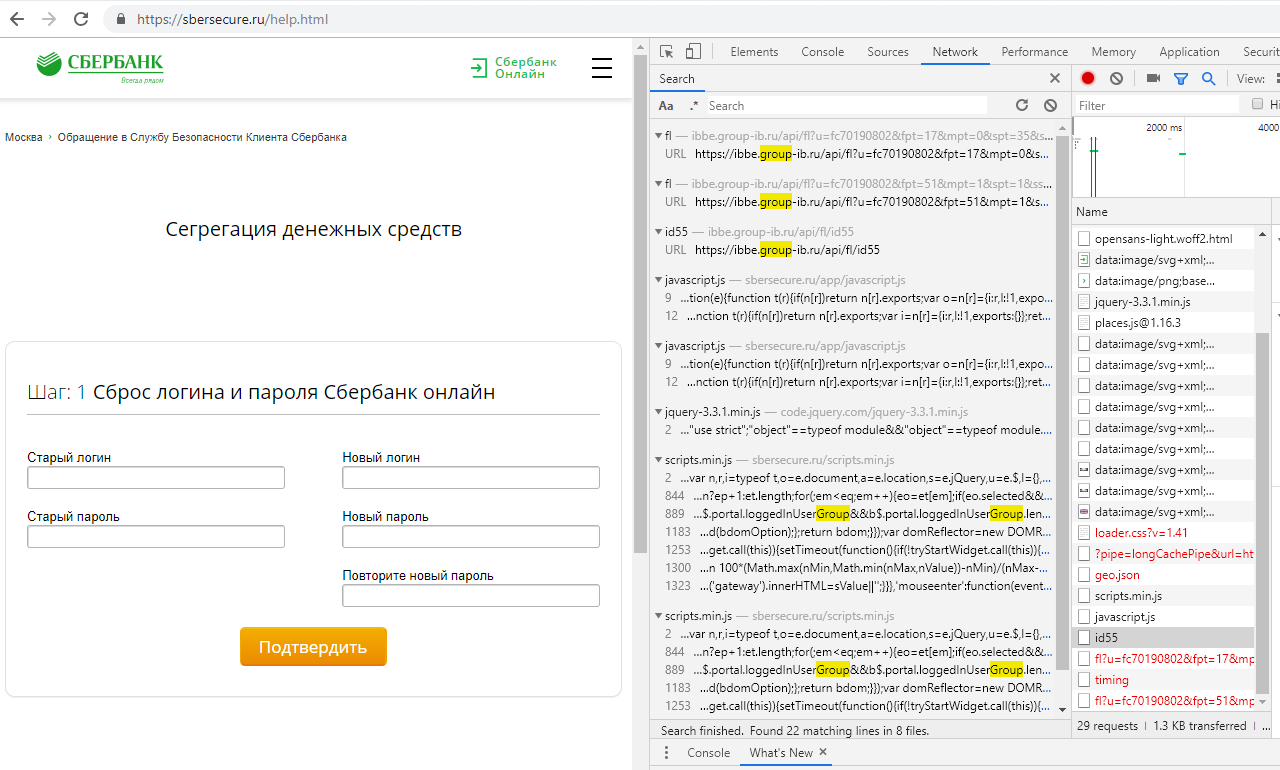
A key element of a phishing resource is a button that says “Get help urgently.” Clicking on it redirects us to the page sbersecure.ru/help.html . In parallel, a whole bunch of java scripts are launched, most of which do not work. Curiously, one of the scripts accesses the ibbe.group-ib.ru resource . Apparently, this is a script of the Secure Bank service from Group-IB, inherited from the phishing resource from this bank’s website.
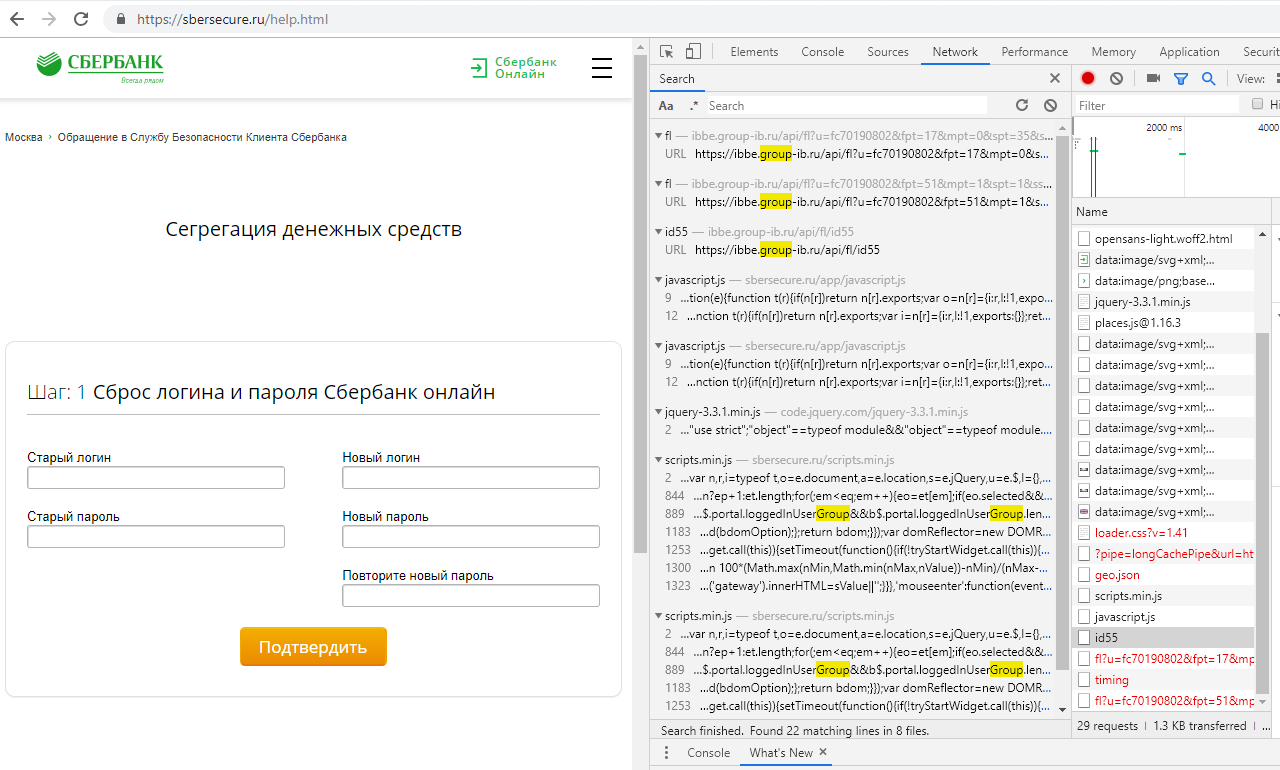
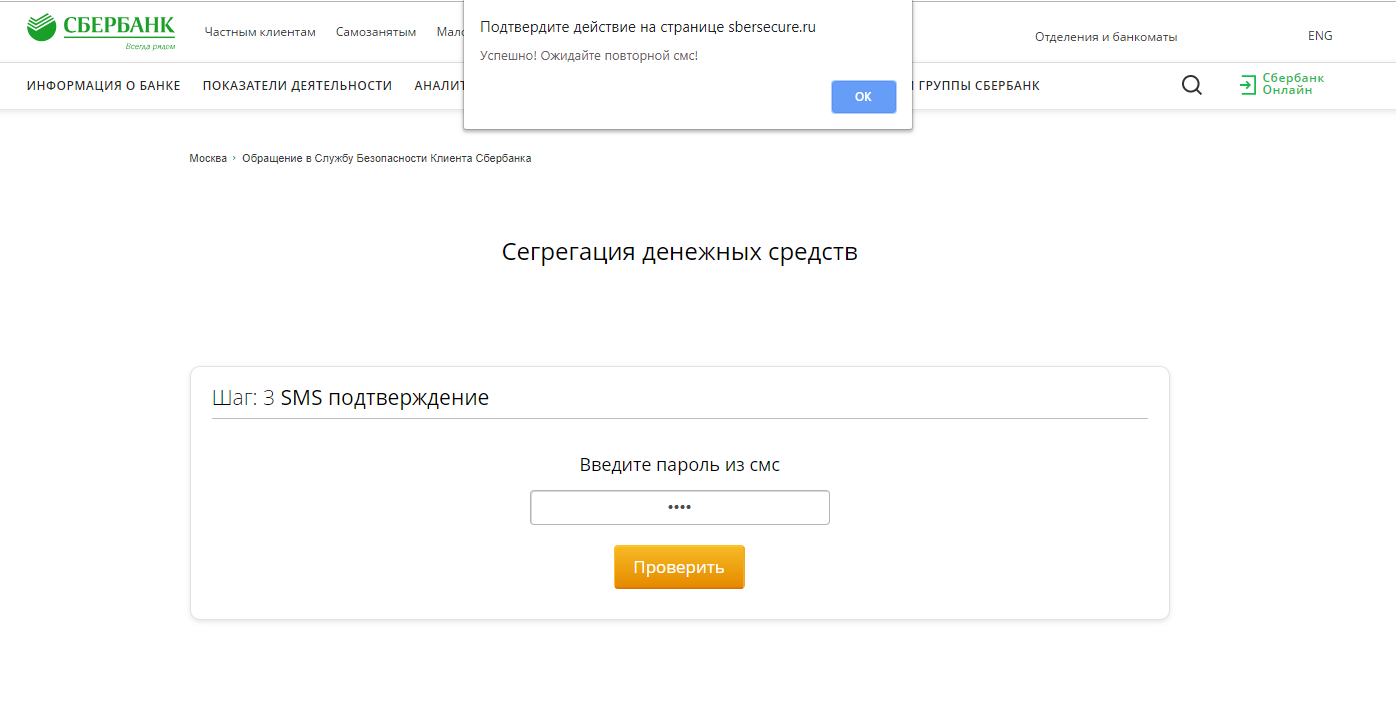
The second page of the resource is called “Segregation of funds”. On April 18, when this site came into view, it looked like this.
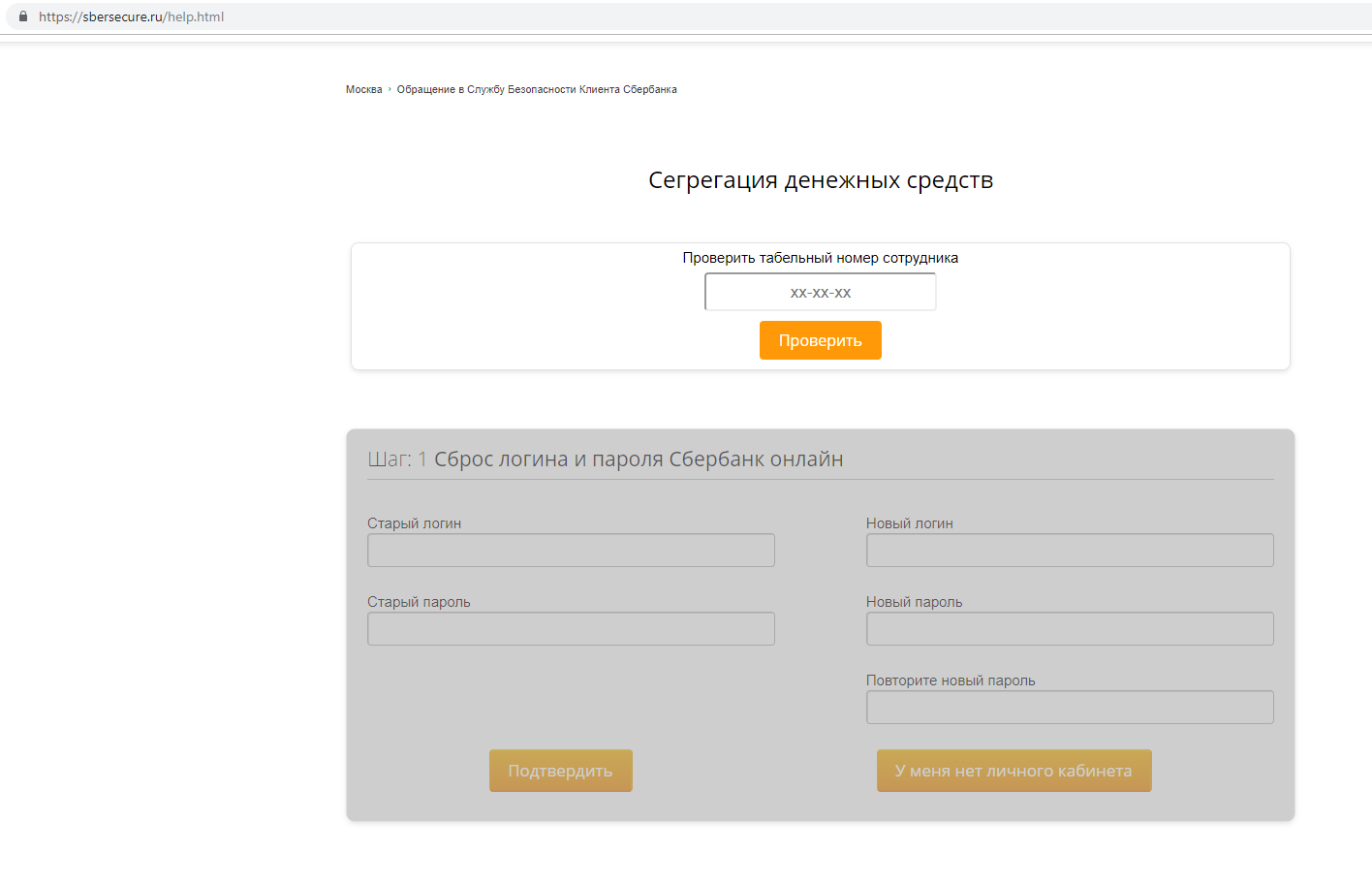
Attempts to enter an arbitrary personnel number for the employee did not lead to anything, the second part - “Resetting the login and password of Sberbank online” was inactive.
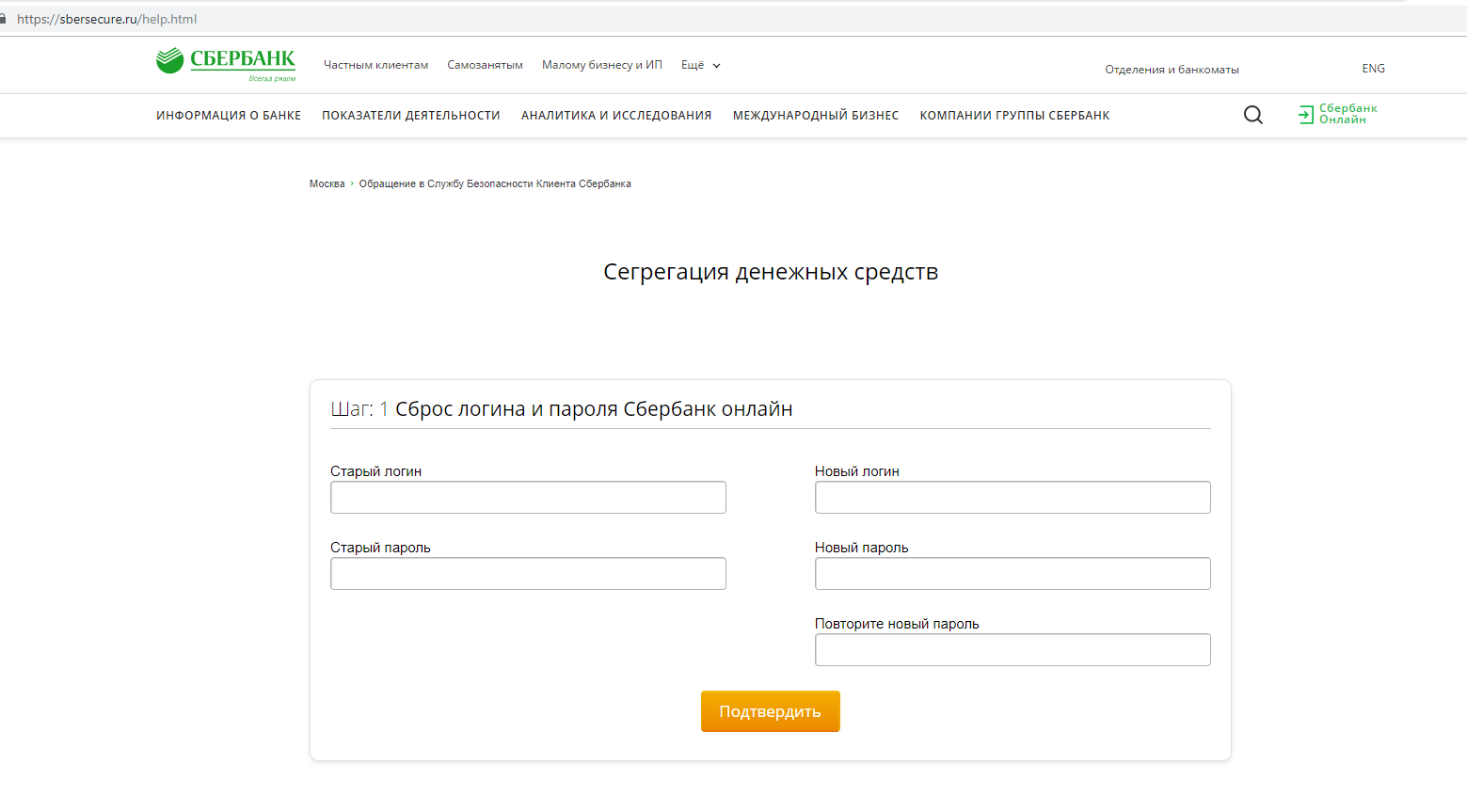
The page has changed over the weekend. The form for entering the personnel number has disappeared, but a form has been made available for changing the login and password from the personal account of the online bank. This clarifies the possible uses of a phishing resource.
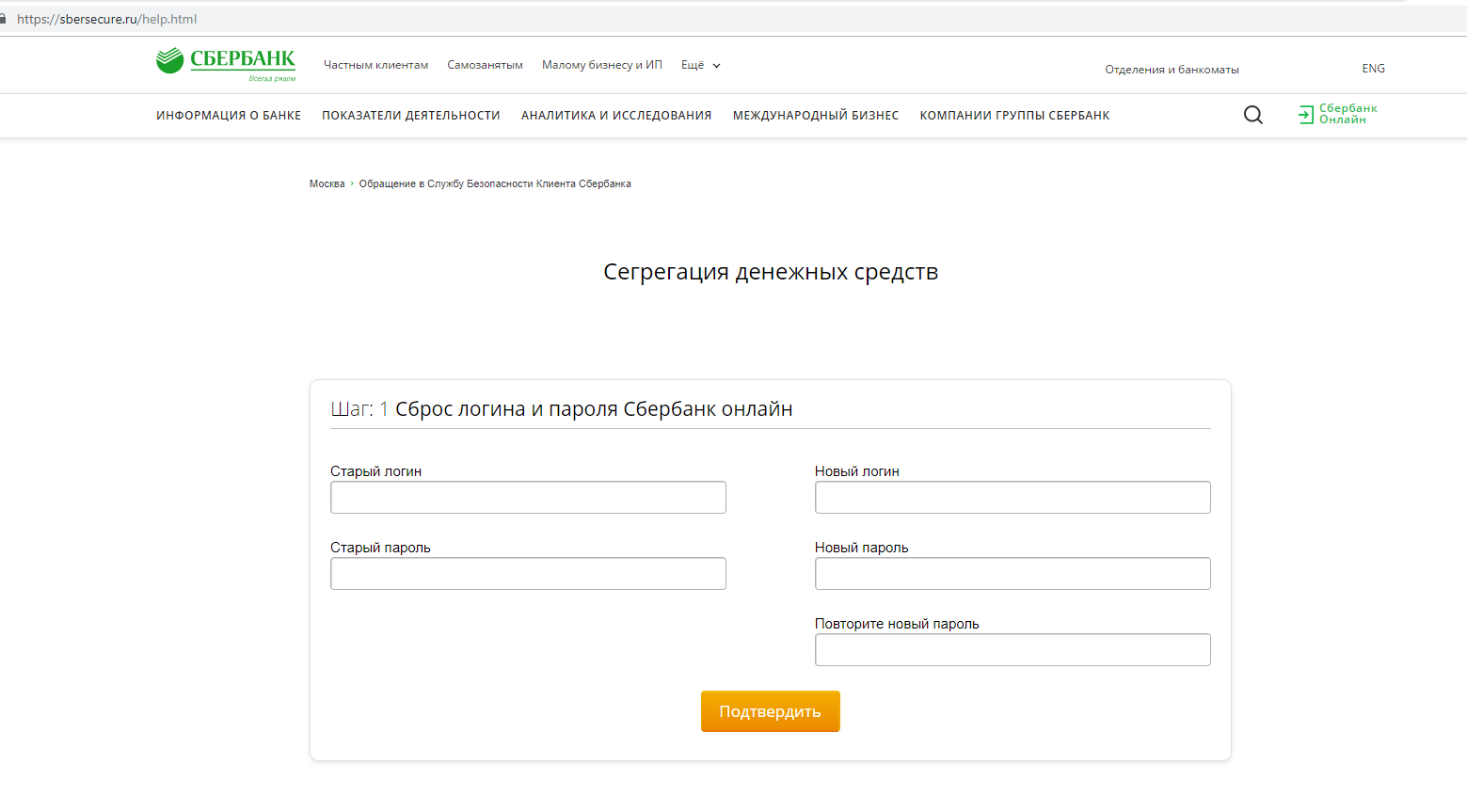
It would be foolish not to see what happens to the data sent, so we fill out the form with arbitrary words and click on the “Confirm” button.
Clicking on the button in plain text transfers the following data to the sbersecure.ru/php/add_login_bank.php script : username and password from the Sberbank.Online service, information about the region of residence and IP address. Information from the fields for entering a new login and new password is ignored for obvious reasons. After that, redirects to the page sbersecure.ru/get_info.html, on which we are prompted to enter the name, surname, phone number, as well as card details, including number, CVV and its validity.
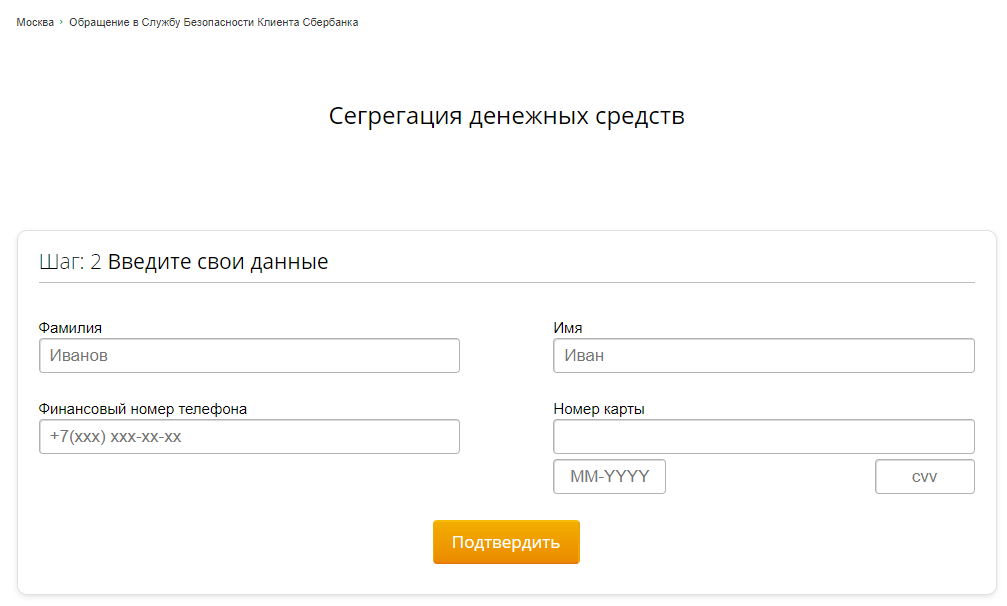
Not bad, is it? But we are, as it were, on the page of the bank’s security service ... We enter fictitious data (the site does not check card numbers for validity) and a real phone number. The entered data flies to sbersecure.ru/php/input_user_data.php , and we find ourselves on the next page.
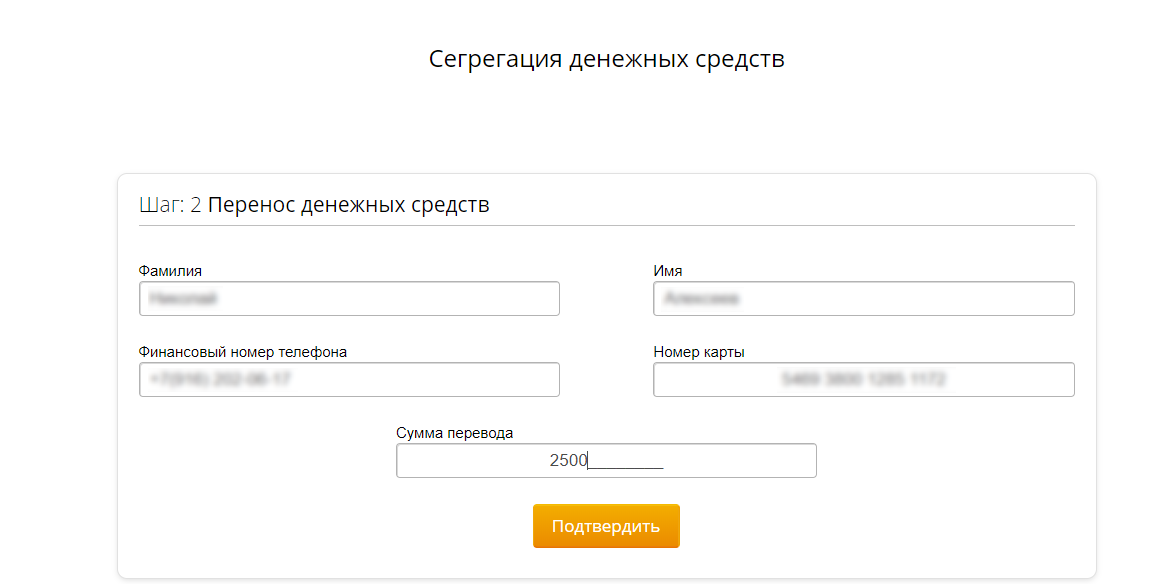
The logic is not entirely clear, perhaps, since we are talking about segregation of funds, here the victim would have to enter the data of his second bank card. Again, fill in the fields with believable garbage, while indicating the existing phone number. The entered data is transmitted to sbersecure.ru/php/input_frand.php. Honestly, I don’t know what frand can mean, but I suspect that this is a distorted friend.
Voila!
Predictably enough, we find ourselves on the page for entering the code from an SMS message. At the same time, SMS from Yandex arrives on the phone. It seems that someone is trying to make a transfer using the Yandex.Money service. We enter the code, data on the phone number and the entered characters go to sbersecure.ru/php/input_sms_2.php , and returns to the previous page.
Following this, another SMS arrives at the indicated number. You can continue this cycle almost endlessly.
Of course, if we talk about the details of the money transfer scheme, then this is largely an assumption. For the purity of the experiment, you should enter the data of a valid, albeit a virtual bank card, try to track the movements of finances, and so on, but even now it’s clear that with the help of this site attackers receive at least
With such information at your disposal, you can easily steal money from bank accounts in a variety of ways.
Naturally, my colleagues and I could not calmly pass by such a resource, so back in the evening of April 18 we sent information about it to Sberbank using the feedback form on the official website. After 2 days, on April 20, we received a letter stating that our appeal was registered.
Later, we repeated the appeal, using the special form for sending messages about fraudulent resources, which was very difficult to find without Google: www.sberbank.ru/ru/person/dist_services/warning/form
Let's hope that the bank will quickly respond to the message, and the phishing site will disappear from the network as quickly as it appeared.
Events around the site developed rapidly. The domain name was registered in the evening of April 16, and the next day a phishing site appeared on it. Initially, the servers of the Russian Hostlife hoster were specified as DNS, however, after only 9 hours, the addresses of CloudFlare, a company that does not need to be presented, appeared in NS records. April 17 at 15 hours Moscow time, the resource acquired an encryption certificate issued by the same CloudFlare.
Take a closer look at the phishing site.
To create the resource, a fairly popular method of partial copying of the original site was used. In this case, the attackers took the Bank’s Ombudsman’s Service page as a basis, changing the words “Ombudsman’s Service” to “Customer Security Service”.
Here is the original Ombudsman Service page.
And here is a phishing site.
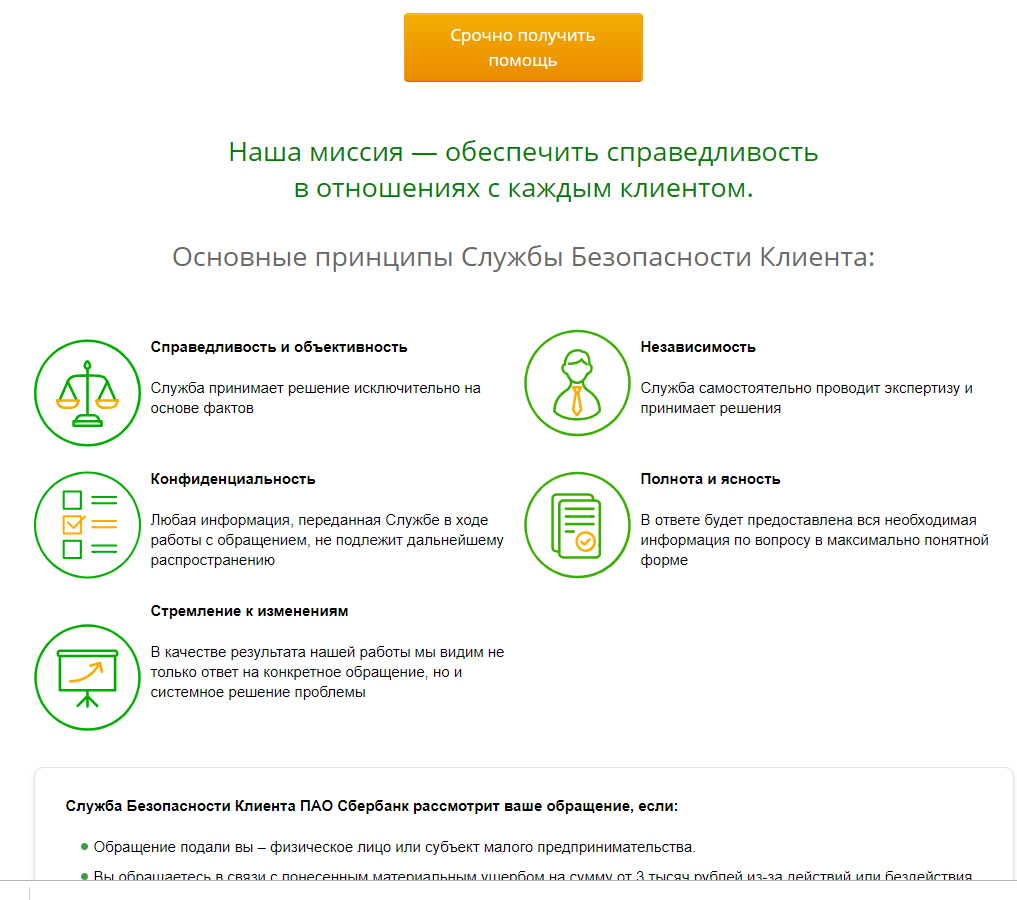
At the same time, the changes affected only the central part of the site, the header, context menus and footer completely repeat the original design. All links, including a link to the authorization page in the Sberbank.Online service, lead to the real site of Sberbank.
General view of a phishing site.

A key element of a phishing resource is a button that says “Get help urgently.” Clicking on it redirects us to the page sbersecure.ru/help.html . In parallel, a whole bunch of java scripts are launched, most of which do not work. Curiously, one of the scripts accesses the ibbe.group-ib.ru resource . Apparently, this is a script of the Secure Bank service from Group-IB, inherited from the phishing resource from this bank’s website.
The second page of the resource is called “Segregation of funds”. On April 18, when this site came into view, it looked like this.
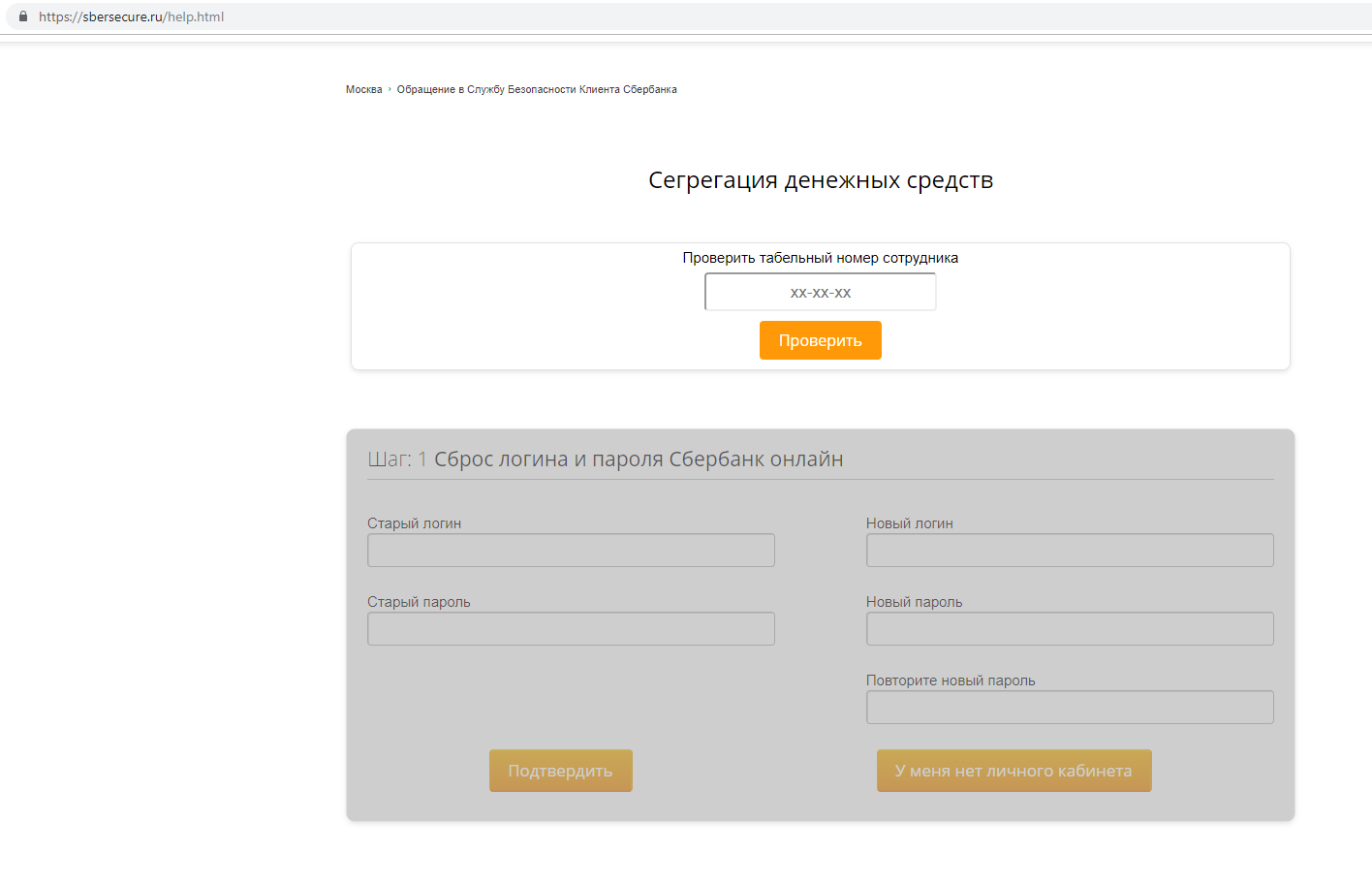
Attempts to enter an arbitrary personnel number for the employee did not lead to anything, the second part - “Resetting the login and password of Sberbank online” was inactive.
The page has changed over the weekend. The form for entering the personnel number has disappeared, but a form has been made available for changing the login and password from the personal account of the online bank. This clarifies the possible uses of a phishing resource.
It would be foolish not to see what happens to the data sent, so we fill out the form with arbitrary words and click on the “Confirm” button.
Clicking on the button in plain text transfers the following data to the sbersecure.ru/php/add_login_bank.php script : username and password from the Sberbank.Online service, information about the region of residence and IP address. Information from the fields for entering a new login and new password is ignored for obvious reasons. After that, redirects to the page sbersecure.ru/get_info.html, on which we are prompted to enter the name, surname, phone number, as well as card details, including number, CVV and its validity.
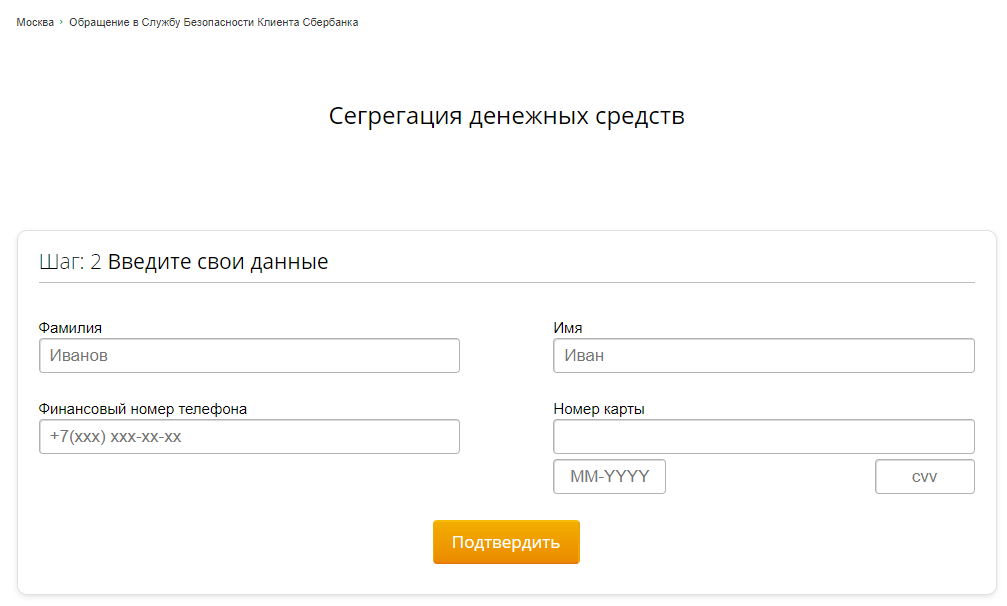
Not bad, is it? But we are, as it were, on the page of the bank’s security service ... We enter fictitious data (the site does not check card numbers for validity) and a real phone number. The entered data flies to sbersecure.ru/php/input_user_data.php , and we find ourselves on the next page.
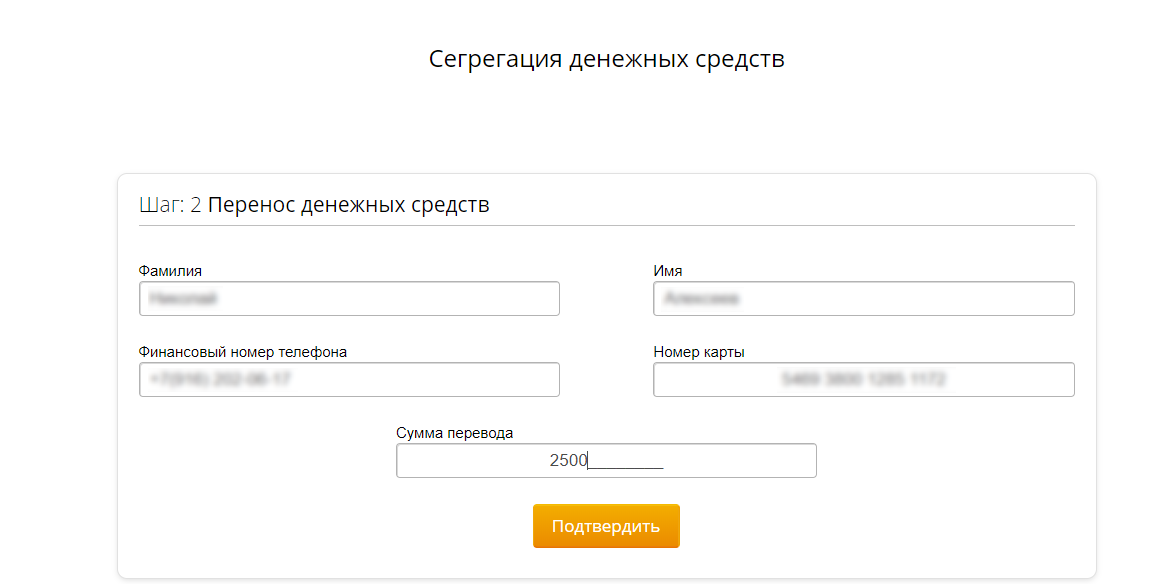
The logic is not entirely clear, perhaps, since we are talking about segregation of funds, here the victim would have to enter the data of his second bank card. Again, fill in the fields with believable garbage, while indicating the existing phone number. The entered data is transmitted to sbersecure.ru/php/input_frand.php. Honestly, I don’t know what frand can mean, but I suspect that this is a distorted friend.
Voila!
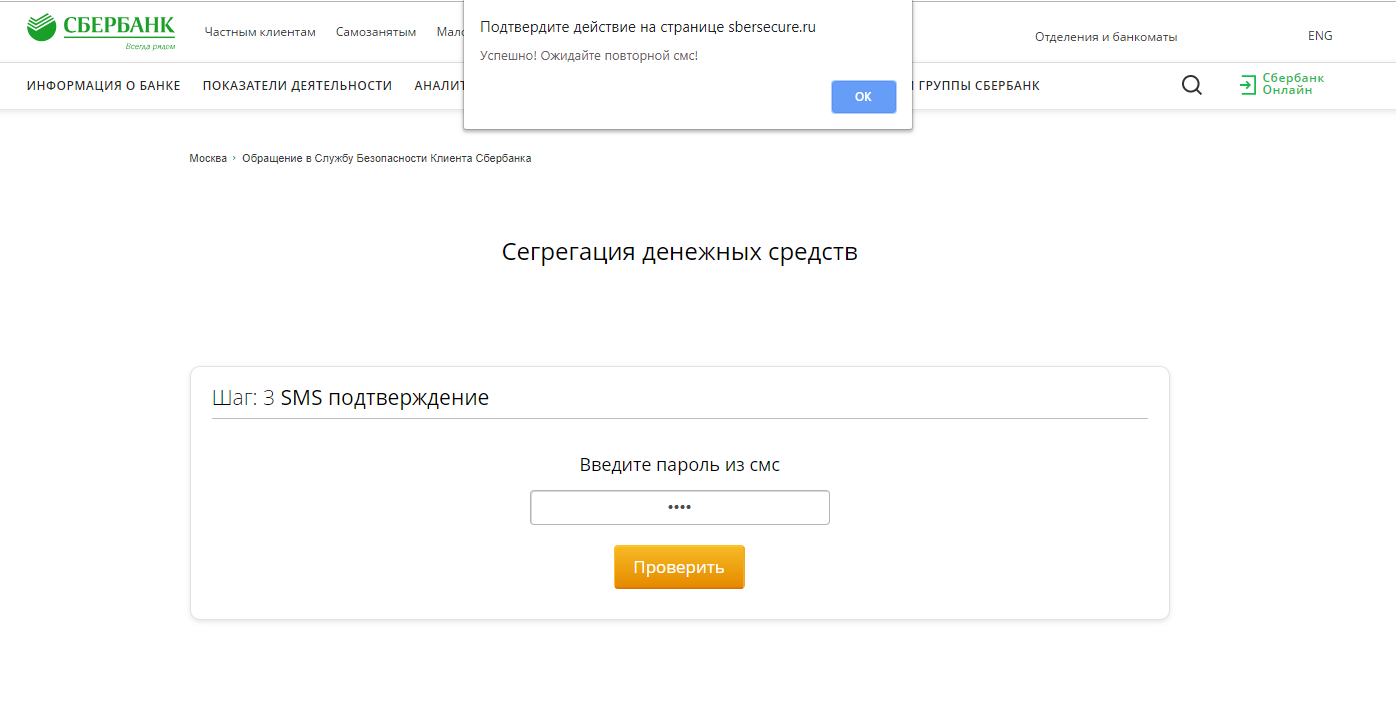
Predictably enough, we find ourselves on the page for entering the code from an SMS message. At the same time, SMS from Yandex arrives on the phone. It seems that someone is trying to make a transfer using the Yandex.Money service. We enter the code, data on the phone number and the entered characters go to sbersecure.ru/php/input_sms_2.php , and returns to the previous page.
Following this, another SMS arrives at the indicated number. You can continue this cycle almost endlessly.
Of course, if we talk about the details of the money transfer scheme, then this is largely an assumption. For the purity of the experiment, you should enter the data of a valid, albeit a virtual bank card, try to track the movements of finances, and so on, but even now it’s clear that with the help of this site attackers receive at least
- Surname
- Name
- Full credit card details
- Phone number
- Login and password for entering the Sberbank.Online service
With such information at your disposal, you can easily steal money from bank accounts in a variety of ways.
Naturally, my colleagues and I could not calmly pass by such a resource, so back in the evening of April 18 we sent information about it to Sberbank using the feedback form on the official website. After 2 days, on April 20, we received a letter stating that our appeal was registered.
Later, we repeated the appeal, using the special form for sending messages about fraudulent resources, which was very difficult to find without Google: www.sberbank.ru/ru/person/dist_services/warning/form
Let's hope that the bank will quickly respond to the message, and the phishing site will disappear from the network as quickly as it appeared.
