See the data? Not. So I do not see, but they are. We destroy data on SSD-drives, and even restore speed
Each of us was faced with a situation where it was necessary to restore data, whether it was something not very important or, conversely, critically necessary to achieve certain goals. But few users asked themselves the question: “What if someone restores my personal data on my drive?” - and the right question! Today we’ll talk about Secure Erase data deletion method and learn about its advantages and disadvantages.

But, for starters, let's clarify the situation. This material is aimed at ordinary (no matter - beginners or advanced) users who, for one reason or another, decided to permanently delete data from it or try to restore the drive’s high-speed performance if it began to drop significantly lower than stated (at the same time , SLC caching and other “official” reasons for speed reduction in this case we do not consider, since these are already the hardware features of the drives). The essence of the problem that Secure Erase can solve can also be that the drive began to work slowly - writing and reading data. There can be a lot of reasons, and some of them are related to the hardware component, and some to the software component. SSDs are very different in service from classic HDDs, therefore, simply deleting the data or formatting the drive does not really mean resetting the cell - it needs to be cleared before recording, which slows down the process of writing new data. In theory, there shouldn’t be such problems, because there is TRIM - a command to clear the data marked for deletion in cells during a system outage, so that we don’t notice this. This command only works with 2.5 ”and M.2 SATA drives. For drives connected to the PCIe bus (M.2 or PCIe on the motherboard) there is an analogue - Deallocate. But it happens that these functions are disabled for some reason - an OS error, a user error in setting up a disk through third-party software, the use of non-standard OS assemblies with unknown software components. And soon the disc will start to work noticeably slower,
And a few words for those who find this material an instruction for actions within organizations where data deletion is necessary as a class. In order to protect information that is critical, both for serious organizations that are concerned about the safety of data and for public sector enterprises working with information classified as state secrets, as a rule, protection systems (software and / or hardware), built on cryptographic data protection using domestic GOST 28147-89, satisfying regulatory and regulatory documents of regulators. The thing is that in Russia at the moment there is no really effective algorithm for the complete removal of data from solid-state drives, and GOST P50739-95 is focused on HDD (common HDD) for this is not quite suitable. Let's be patient - about our and not our standards a bit later. It was necessary to tell this, but with terrible formulations in this material we tie. Well, or almost :)

Any of us once thought, and perhaps even thinks now, that by clicking the "Delete" button and then "Empty the trash", the selected files will be deleted. But in reality this is not entirely true and now we will explain why. The HDD operation algorithms are designed in such a way that when you delete a file, the operating system actually removes the link to it from the file system table. It's like removing a shortcut from the desktop - in this case, the program or game remains in place and you can still access it. Still, once at the request of parents removed the label CS or another favorite game with the phrase "everything, the game is deleted"? So here - the file physically remains on the medium, but until a new one is written in its place. Although, even after this, information can be restored by studying the magnetic fields on the surface of the disk, but this is a completely different story ... As you may have guessed, safe erasing of the HDD was very simple - absolutely every sector of the hard disk was overwritten with zeros and ones, as well as their combinations many times. Moreover, the more the better! This procedure takes a lot of time. A lot of time. That is why this method is not suitable for instant and irrevocable data deletion, if suddenly a capture group visits you. Here we need radical methods like instant physical destruction ... Not the point, the conversation is not about that. That is why this method is not suitable for instant and irrevocable data deletion, if suddenly a capture group visits you. Here we need radical methods like instant physical destruction ... Not the point, the conversation is not about that. That is why this method is not suitable for instant and irrevocable data deletion, if suddenly a capture group visits you. Here we need radical methods like instant physical destruction ... Not the point, the conversation is not about that.
With SSD, everything is completely different. Unlike HDDs, SSDs have more complex data distribution algorithms. One example of how data remains intact is related to managing it in an SSD. This is done so that the wear of the memory cells is at least approximately uniform, because they have a limited "life time". When you edit a document and save changes, they do not overwrite the original data. Instead, SSDs write new content to an empty data block and then update the logical map to indicate a new location. This leaves a place in which the source data on the SSD is marked as free, but the actual data remains untouched. Over time, data marked as free can be deleted, but until then it can be restored. Actually this is also the reason for the slowdown of consumer drives, which was mentioned a little higher. The way the flash controller controls the distribution of data does not guarantee to a large extent that the method used in erasing the HDD will completely overwrite all SSD memory locations.
Secure Erase is recognized by the US National Institute of Standards and Technology (NIST) as an efficient and secure way to meet legal data sanitation requirements.
ATA Secure Erase is part of the ANSI ATA specification. In cases of its correct implementation, it erases the entire contents of the disk at the hardware level, and not using software.
ATA Secure Erase (SE) is designed for controllers in SSDs. The SSD controller resets all memory cells, leaving them empty. In fact, this method restores the SSD to its factory state, not only deleting data, but also returning the original performance. When implemented correctly, this standard will process all memory, including service areas and secure sectors.
DomesticGOST P50739-95 recommends erasing information by completely rewriting sectors. At the same time, it does not specify how many times it is required to do this and, as we have already said, this method is not entirely effective, because data can be restored with special equipment. Yes, and it is relevant again for the HDD - what to do, if they do not keep pace with new technologies abroad, then with us - even more so. True, questions of such importance, in fact, are not quickly resolved - those who worked with the FSB or, at least, the FSTEC, are well aware of what this is about. And it’s not a matter of bureaucracy or someone’s reluctance, but that it is necessary to achieve the most useful result, which is very, very difficult. And expensive.
NAVSO P-5239-26 Wipe Method- The most common worldwide recycling standard hails from the US Department of Defense. The execution algorithm is as follows:
- first pass - the specified character is recorded (for example, zero);
- second pass - reverse data is recorded (zero is replaced by one);
- third pass - recording a random sequence.
This method minimizes the residual magnetization and makes it possible to restore special. means extremely problematic. Yeah, it's not about SSDs anymore, right?
German standard VSITR . The execution algorithm runs in 7 complete rewrite cycles:
- write 0;
- write 1;
- write 0;
- write 1;
- write 0;
- write 1;
- record random data.
It turns out that at the moment of time specifically for solid state drives, normative documents do not exist or they are inaccessible to the public.

It would seem that SSD drives have a non-trivial system of work, therefore, the scheme for the complete destruction of data should also not be the easiest. But in reality, this is not so at all. Any SSD has a controller that is the “brain” of the drive. He not only tells the system where to write data, but also skillfully encrypts the information passing through it, and stores the key with himself. If you delete (or rather, replace) a given key, then all the information will turn into a random set of ones and zeros - it will be impossible to decrypt it in any way (at least until such computing power and tools that allow you to select this key are created ) Just one simple enough action on the part of the user can solve the problem of safe data erasure. This method is the fastest and most effective.
If you combine the two methods (replacing the key and resetting the cells), you get the perfect algorithm for obtaining an absolutely sterile disk in the state of its maximum performance. This, firstly, solves the problem that we raised at the very beginning of the article, and, secondly, it can help us answer the question about the degree of wear of the drive. It is important to note that some drives with built-in encryption can receive only one algorithm upon receipt of a safe erase command - this depends on the controller settings by the manufacturer. If you “reset” your SSD and compare the actual performance with the declared one, then you will get the answer to this question. This procedure does not affect disk wear, which is very important. Note that these actions are designed specifically to analyze the state of the disk, but a long-term increase in read / write speed cannot be achieved due to the peculiarities of the operation of SSD disks - the situation may depend on both the drive model and the controller firmware. And it must be noted that not all drives support encryption. In this case, the controller simply resets the cells.
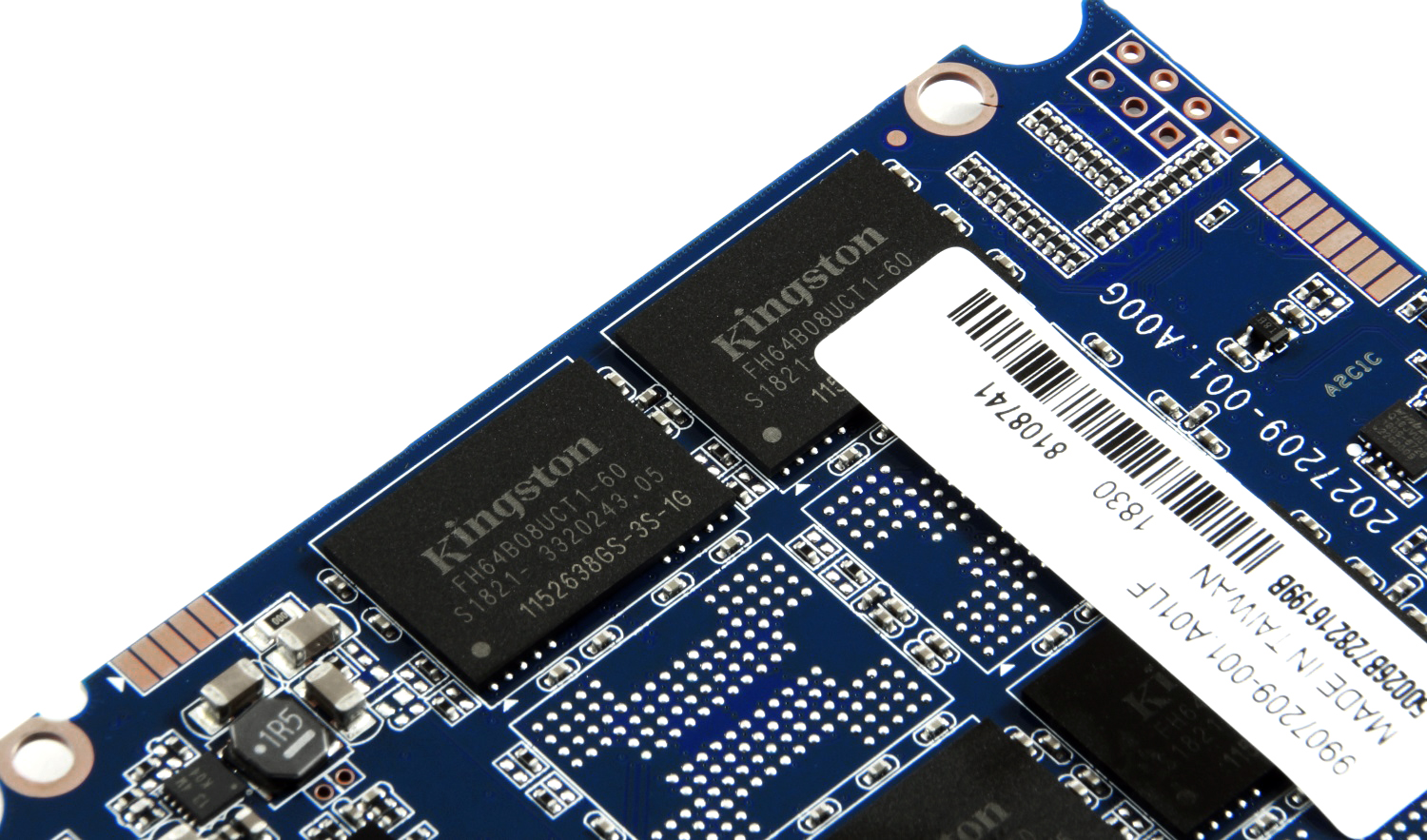
All of the above information described work with magnetic disks based on ATA / SATA interfaces, as well as SSDs based on SATA - 2.5 ”or M.2 devices, which are most common on the market now. But the modern high-speed interface of NVMe is something else. SSDs with this interface can be made in the form of M.2 cards and PCI-Express cards (similar to small video or sound cards - as you like). The NVM Express Interface (NVMe) is the specification of the logical device interface for accessing non-volatile memory connected via the PCI Express bus. NVM acts as an initializer for non-volatile memory, which is usually flash memory in the form of SSDs. NVM Express, as a logical device interface, was designed from the ground up, to maximize the benefits of low latency and internal parallelism of flash-based storage devices, reflecting the parallelism of modern processors, platforms, and applications. Disks of this type do not support standard commands, but since, as mentioned earlier, the problem is not new, the developers took this into account when designing such drives, so all (or almost all) SSDs have in their arsenal a command to run Secure Erase algorithms.
By the way, the latest NVMe specification adds new commands that can clear every nanometer of a disk (bus cache, etc.). The only problem remains software, which should be able to work with disks of this type.
Specifications, algorithms, complex names, this, of course, is very interesting. But we want to erase our disk! What do I need to do?
Let's start with the sad. Sad for Mac OS users. The problem is that for the most part none of the utilities produced by SSD manufacturers that support Secure Erase Unit or Format NVM does not work on a Mac, so you will need to connect your drive to a system running Windows, Linux or DOS
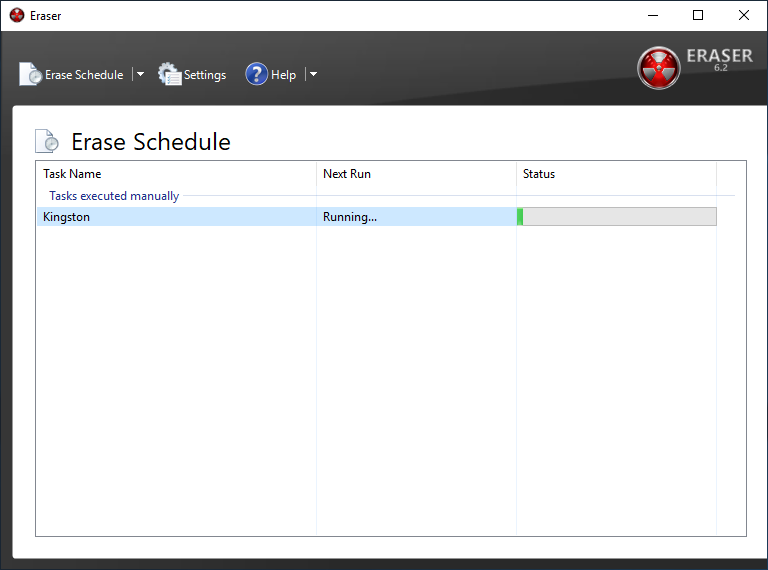
All major manufacturers of SSDs provide utilities for working with their solutions, and you can find them on official sites. You can also use free and paid solutions, which are also suitable for data deletion, but operate on the basis of the standards mentioned above, since no one except the SSD developers knows the hardware component so that it works correctly, and also create a universal tool for all existing SSDs . For an example, we will take Kingston UV500 and A1000 drives with SATA and NVMe interfaces, respectively.
First, we add that cleaning the drive from the operating system operating on it will not work. Actually, it’s logical and nothing surprising. But you never know ...
To demonstrate the processes of data deletion and recovery, we will prepare test A1000. We will drop a set of photos, videos and various software on it both in archives and in the form of executable files.
What do users usually do when they want to “delete” data from disk? For example, before selling it. That's right, format it with the default settings.
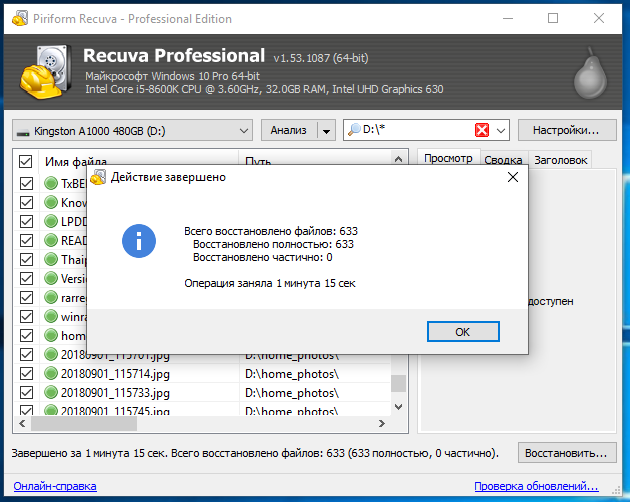
And what can a new drive owner do? Again it’s true - check your purchase for all sorts of interesting things. As you can see, the data is in excellent condition!

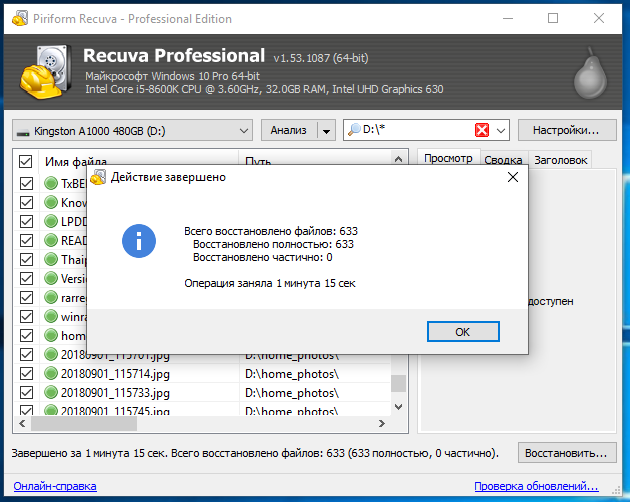
And it took very little time to restore them (if both drives are fast):
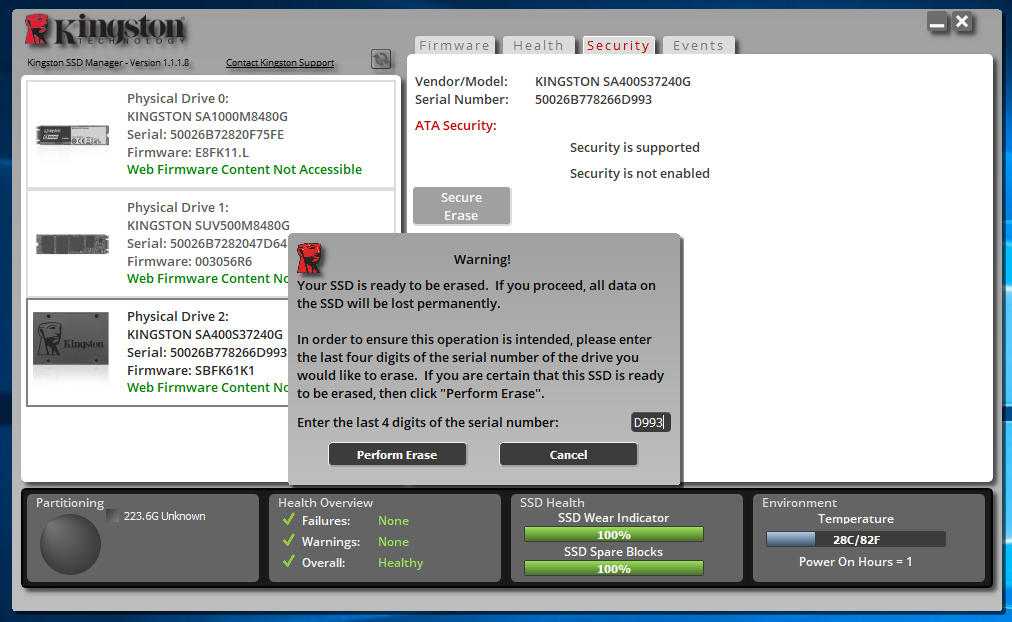
Now many people know that you need to delete data correctly. There are several ways to do this, but there are some limitations. For example, in Windows 8 and later, SSDs operate in such a mode that Secure Erase will not work just like that. If you can still struggle with 2.5 ”drives (to remove the“ lock ”, it is necessary to disconnect the power cable from the drive and turn it on after a switched on system with a loaded operating system), then this will not work with M.2 solutions. Similarly with the NVMe M.2 SSD. Kingston has an SSD Manager program that has all the necessary functionality to monitor the status of drives or their maintenance, including Secure Erase. Actually, when used in Windows 10, the program tells us what to do,

You can use a system with Windows 7 - everything should work correctly in it, unless, of course, you use an incomprehensible "assembly" from craftsmen with unknown how working SATA drivers for the motherboard controller are. Another option if the Secure Erase feature in Kingston SSD Manager is not available regardless of your actions is to use a USB dock to connect your drive. Then immediately no problems - the function is available without any problems. The drive is visible in the system.
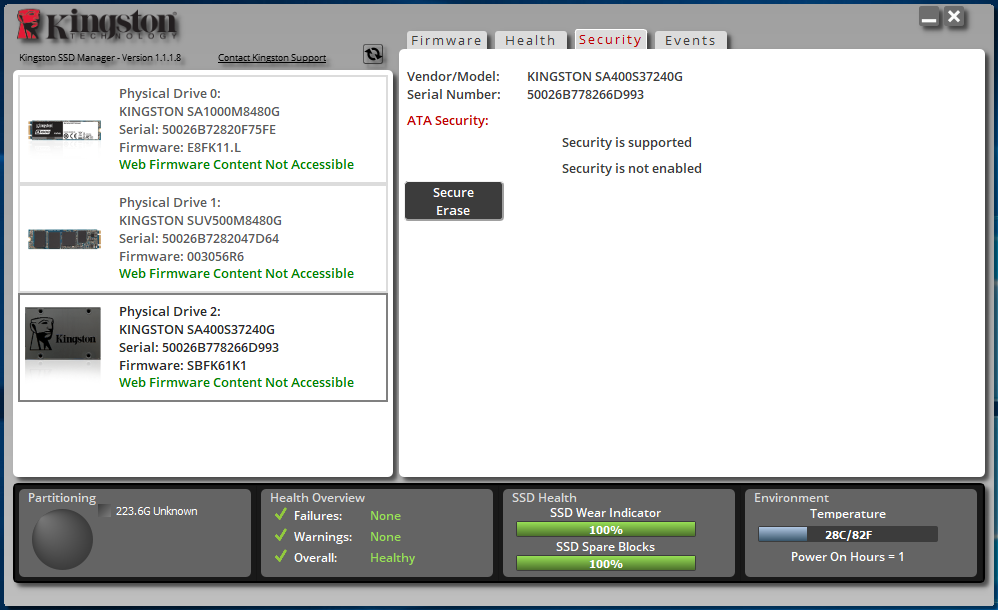
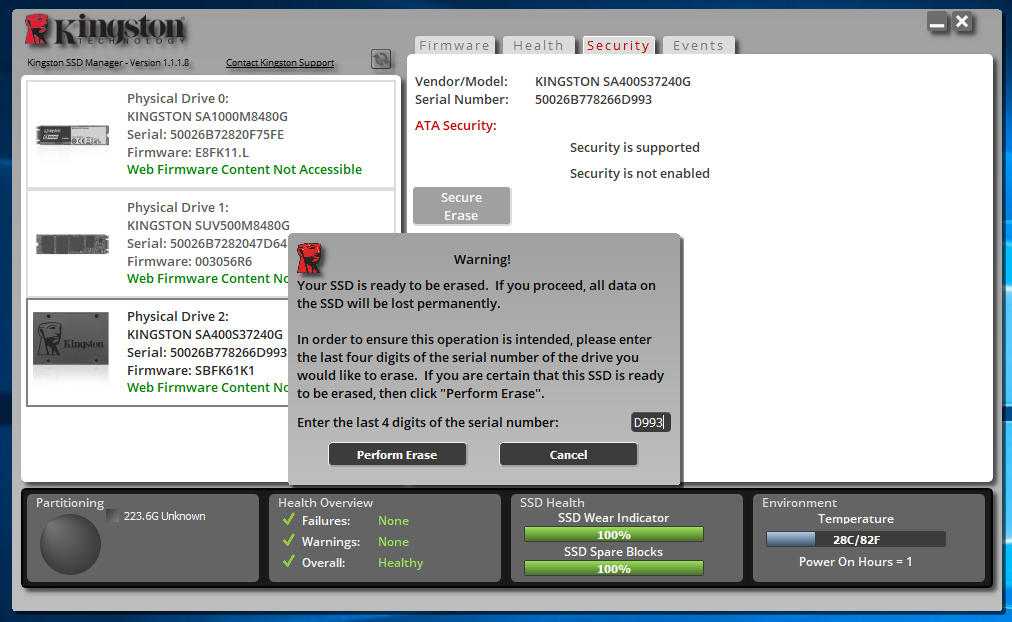
Here we need to select the connected drive, click the Secure Erase button and enter the last 4 characters of the serial number of our drive.
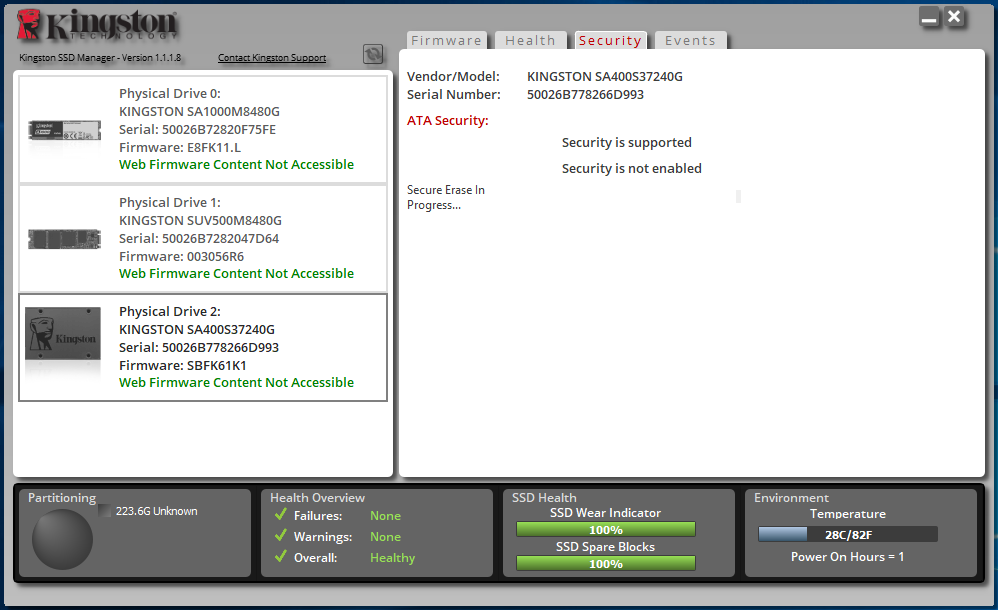
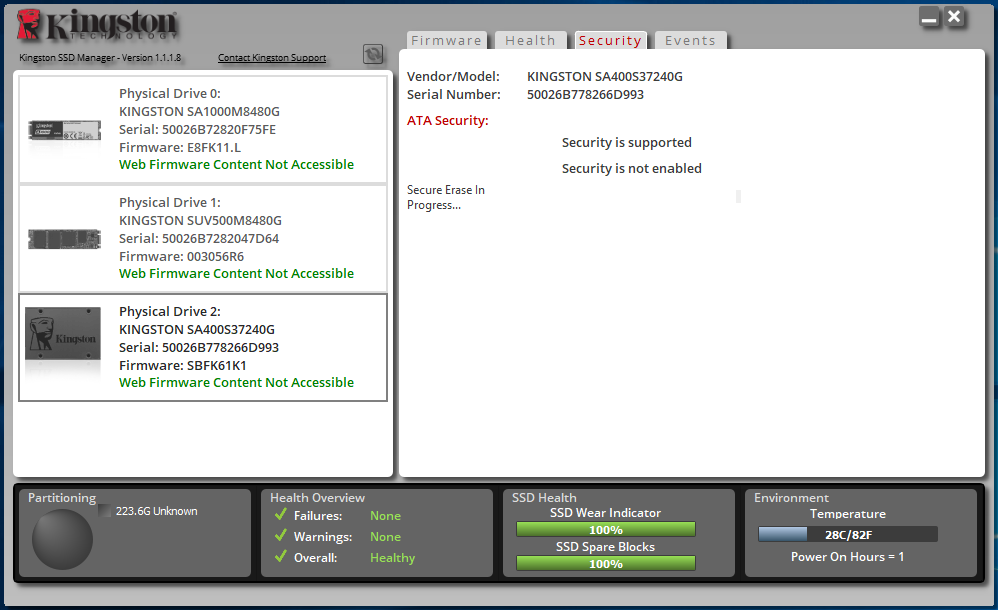
The process does not take much time, so you can soon start using the disk again.
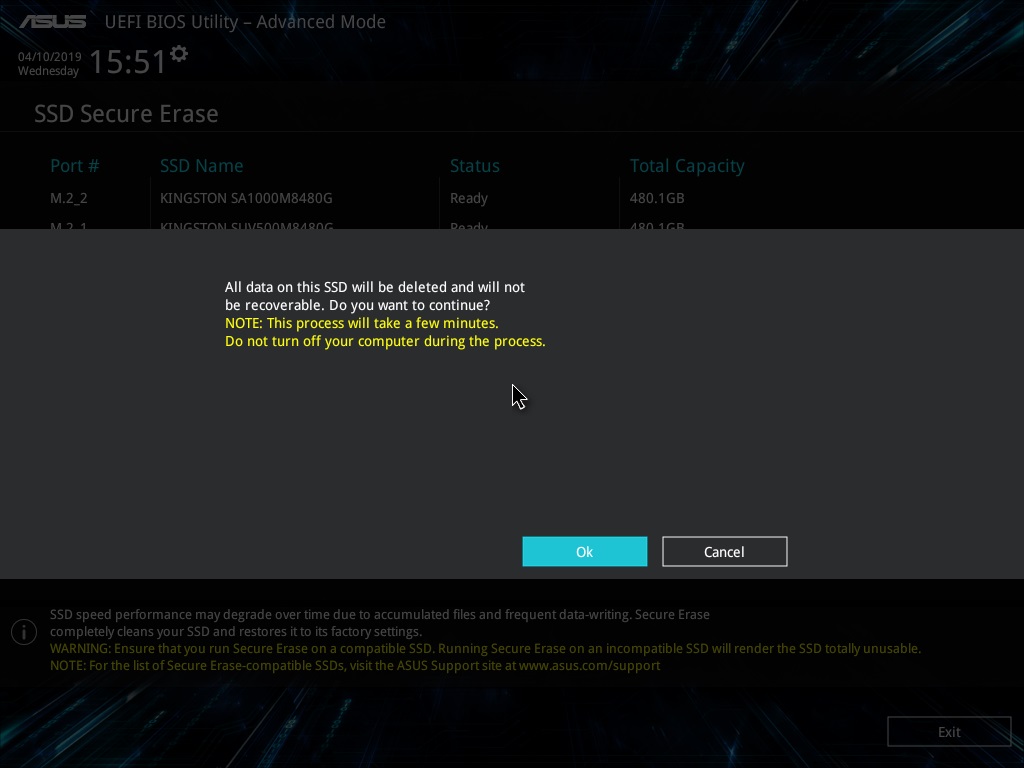
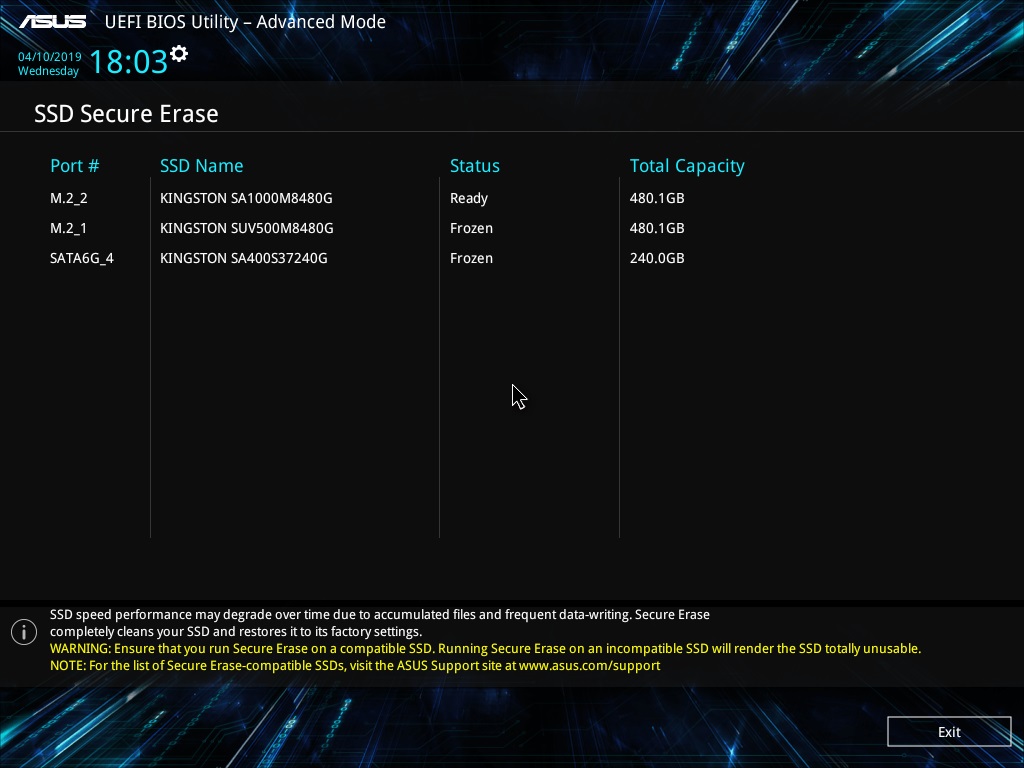
Another option to run Secure Erase is from the motherboard BIOS, if such functionality is implemented by their manufacturer. Usually, the program is in the appropriate section. For example, some models of boards do not have such an opportunity.

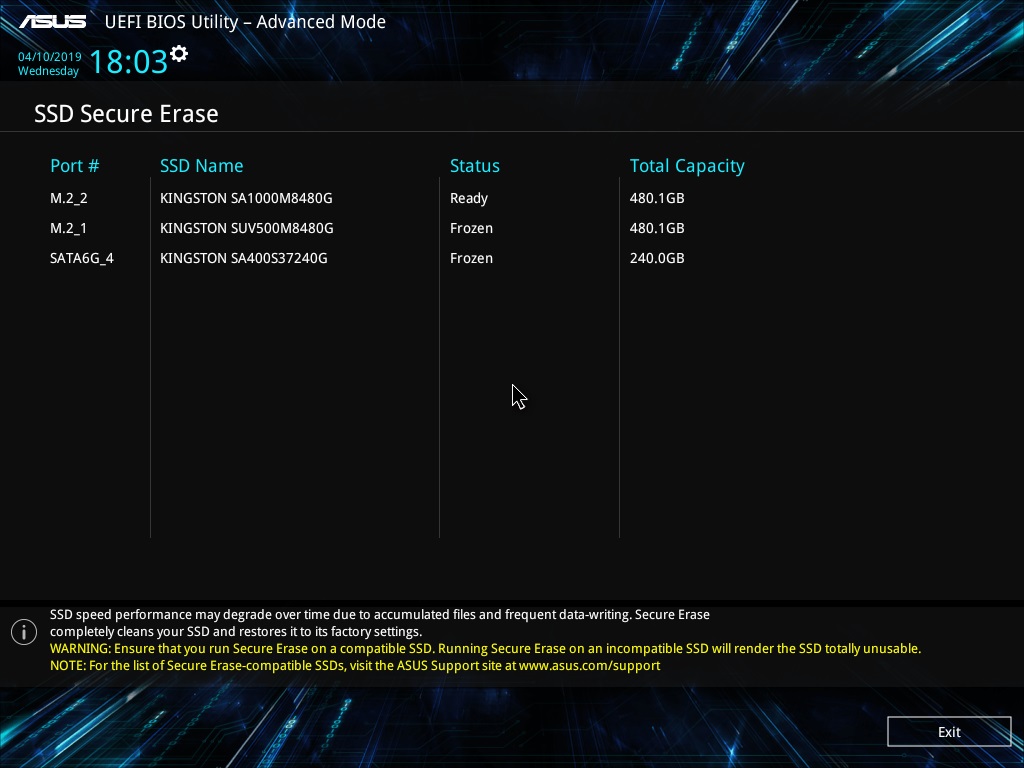
But in a considerable number of models the program is ready to help you:

In it we see a list of mapped drives and their statuses.
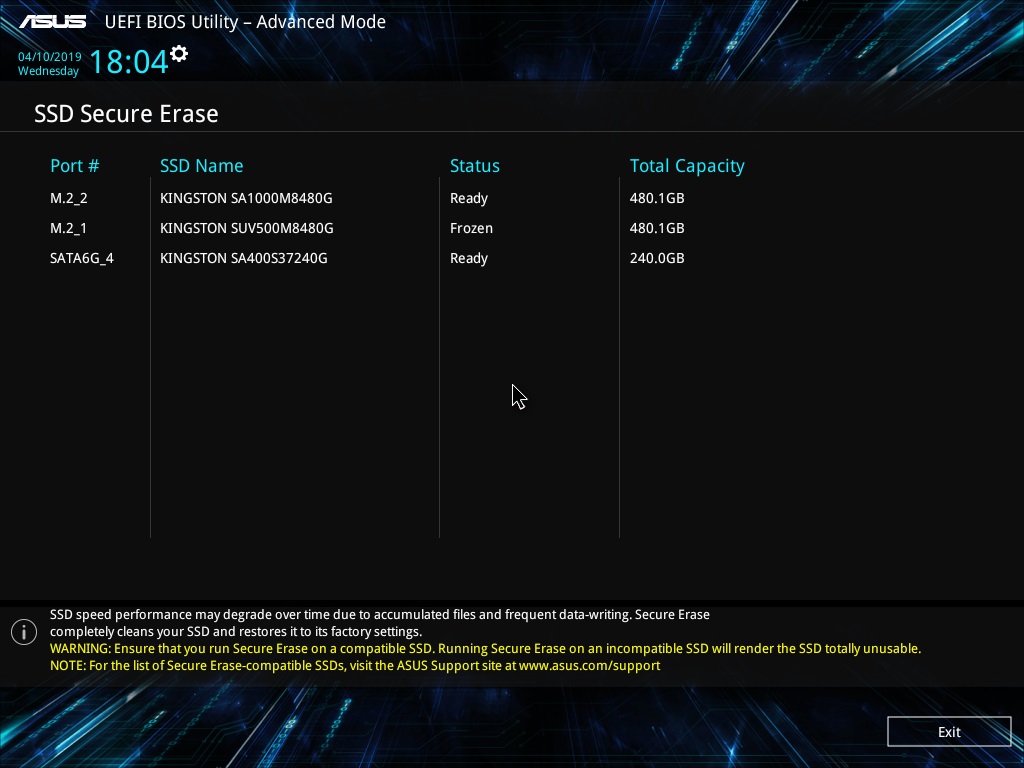
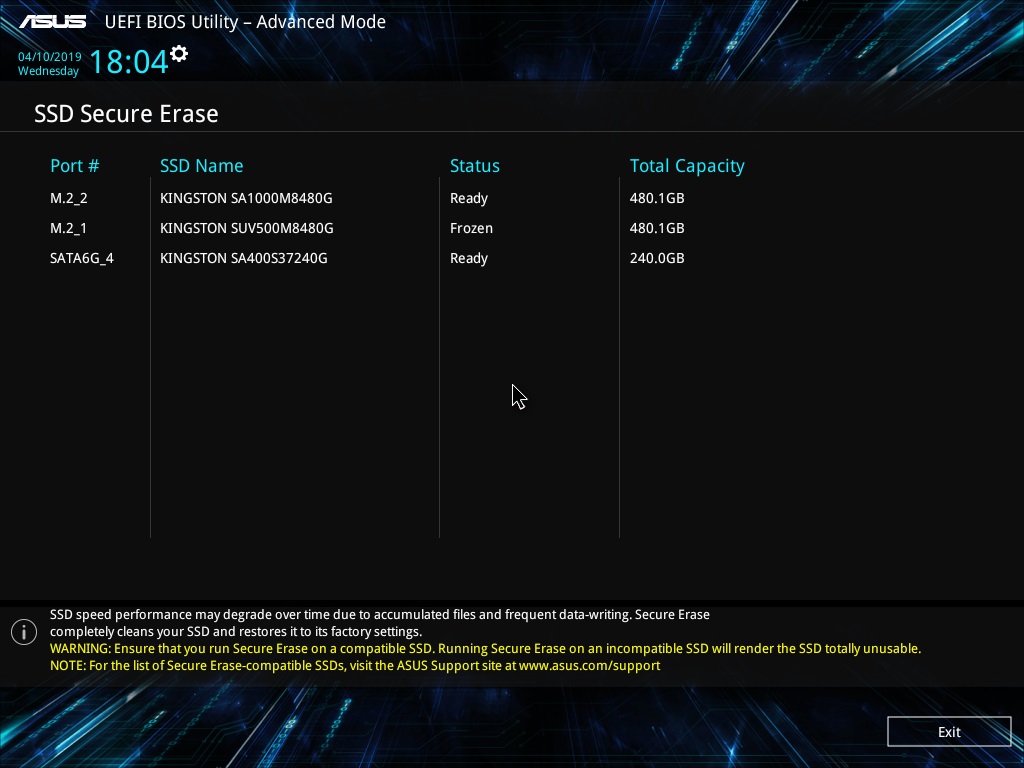
To get Ready status for SATA drives, you need to disconnect and connect their power without turning off the general power of the system, as we said a little earlier. Then you need to restart the SSD Secure Erase utility. We see that the status has changed to Ready.
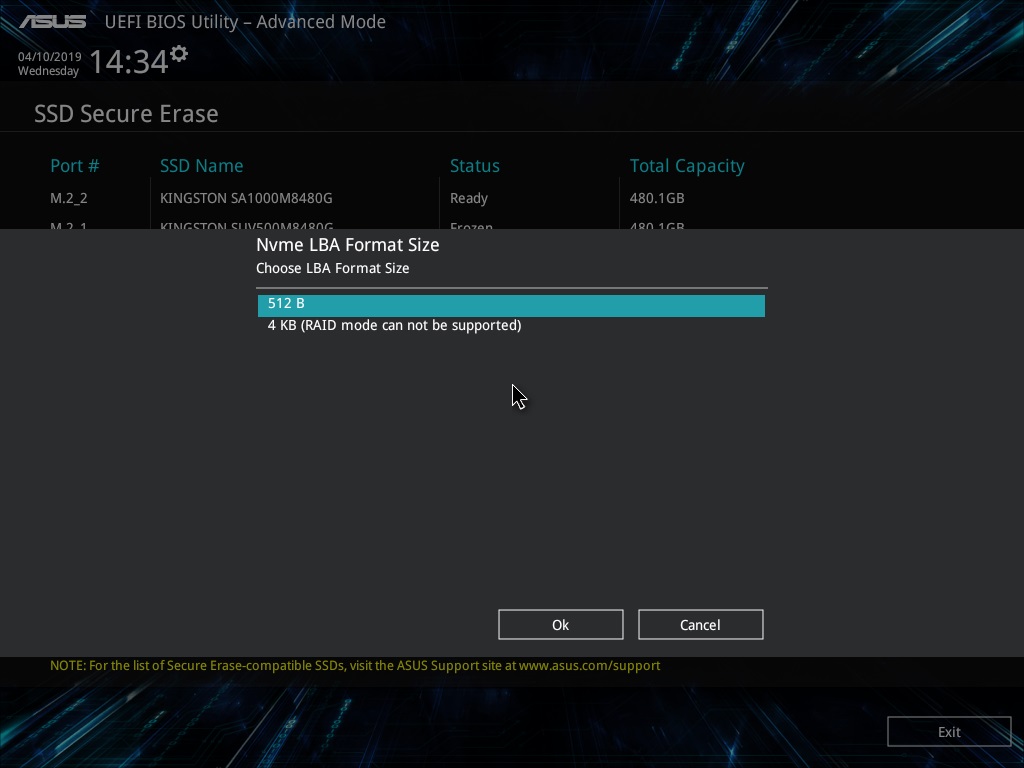
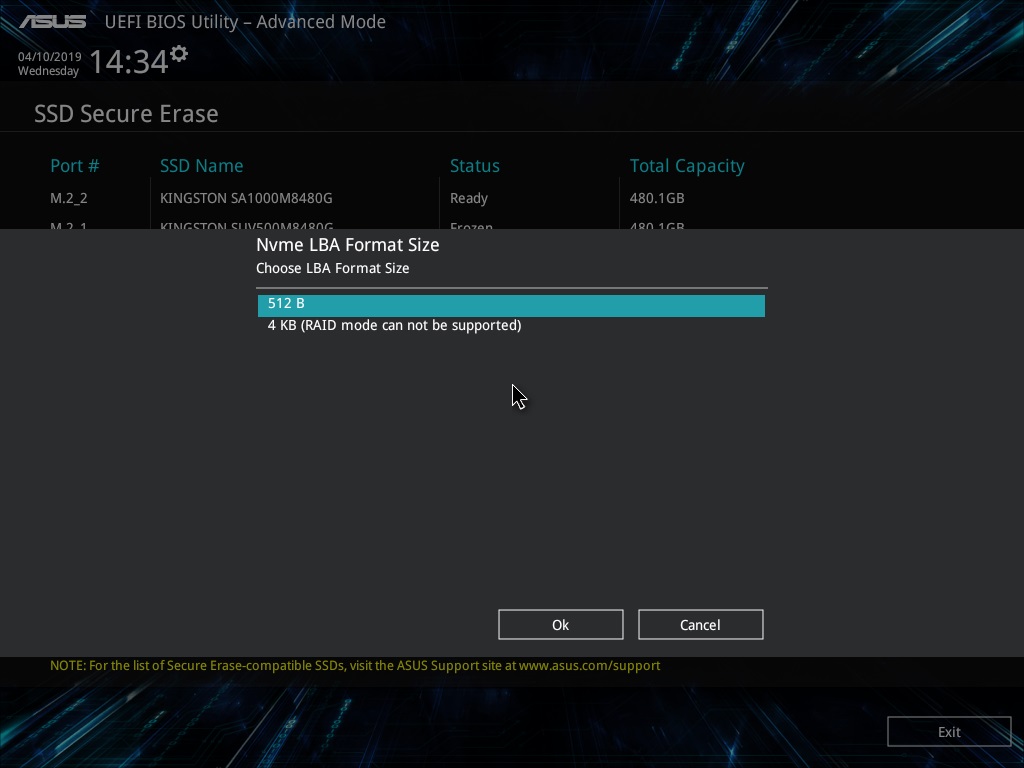
For NVMe disks, you must select the sector size before performing the cleanup.
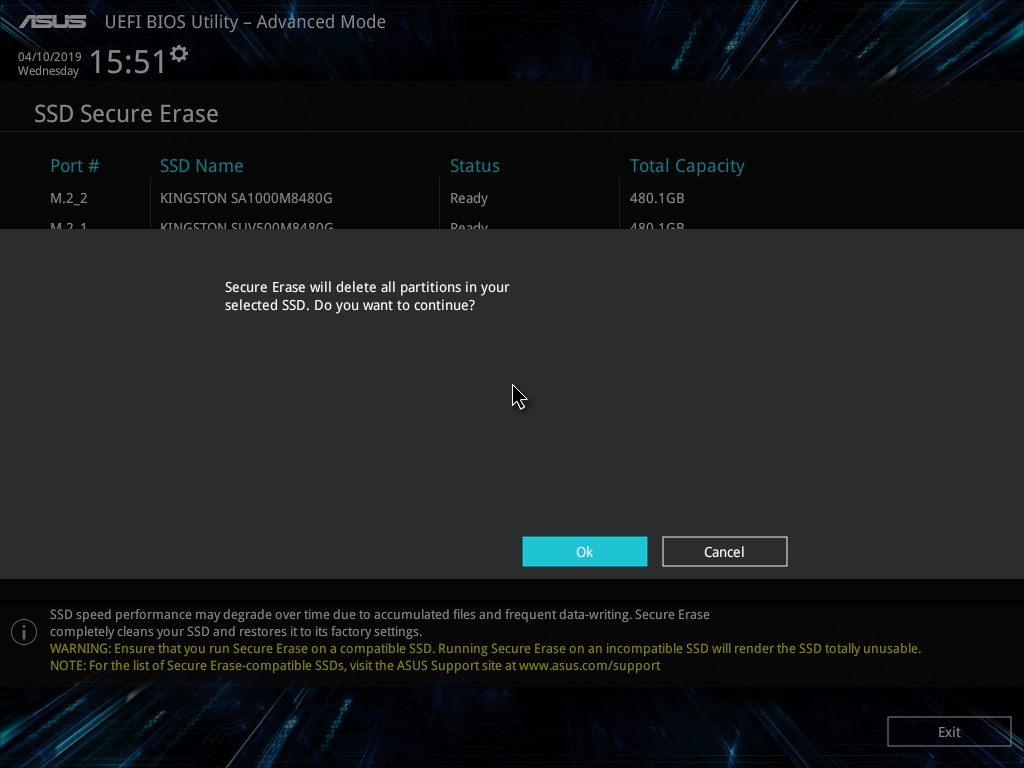
And then we will be asked if we want to clean the drive.
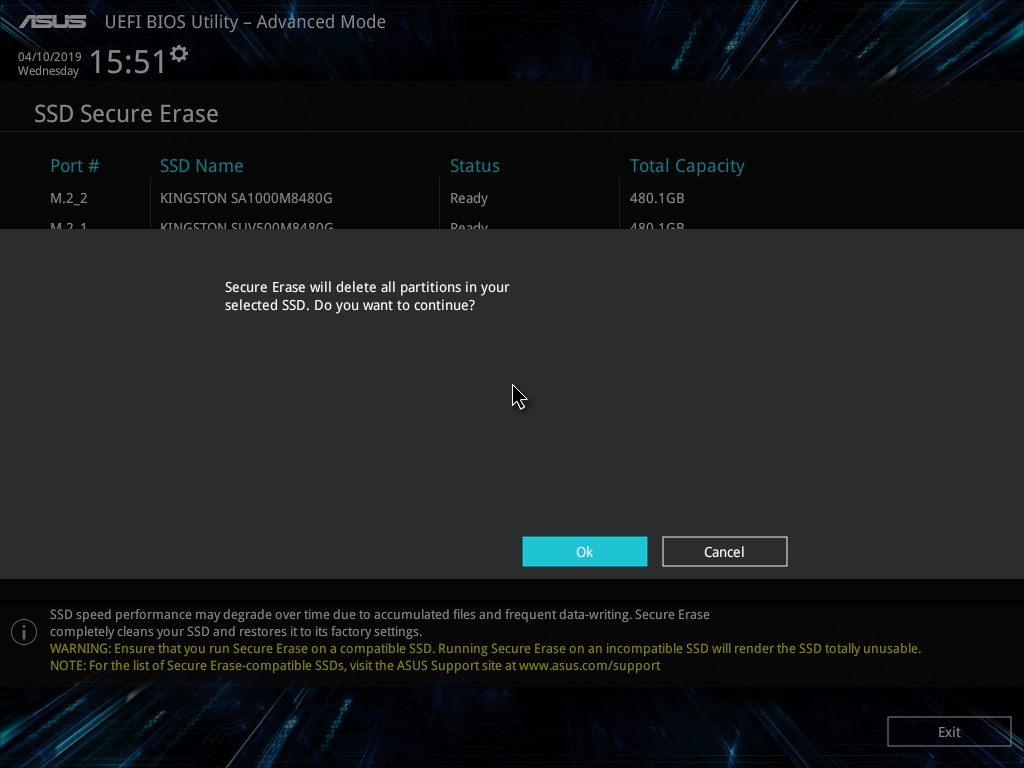
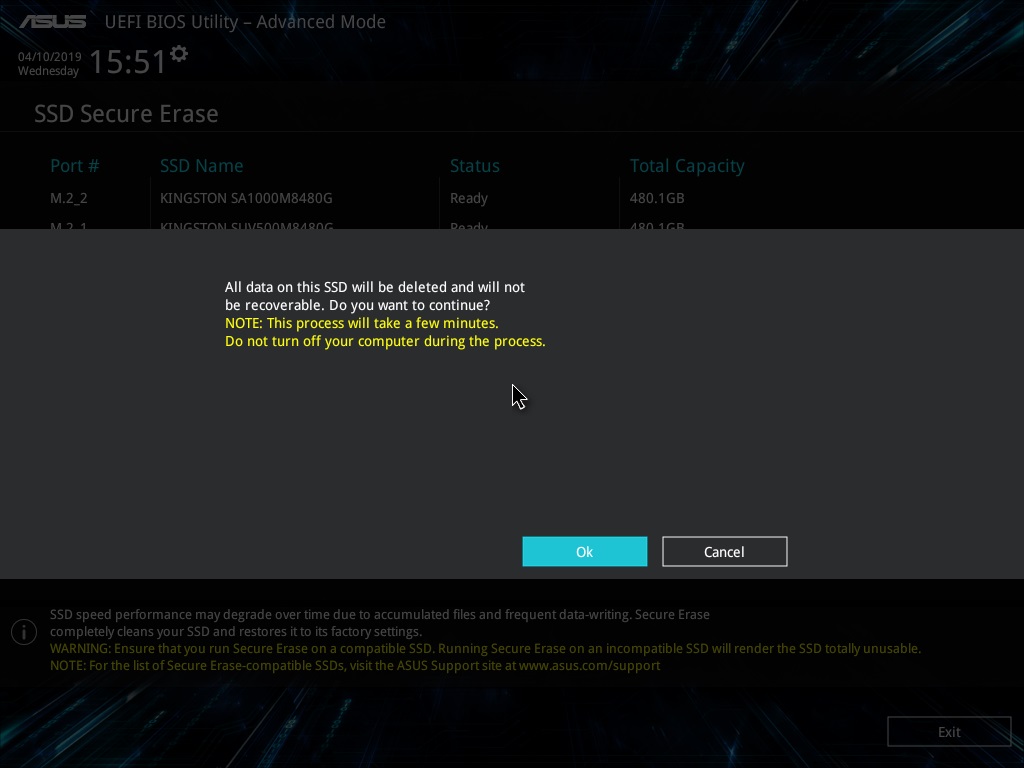
And again - is it really? After all, the process is irreversible.
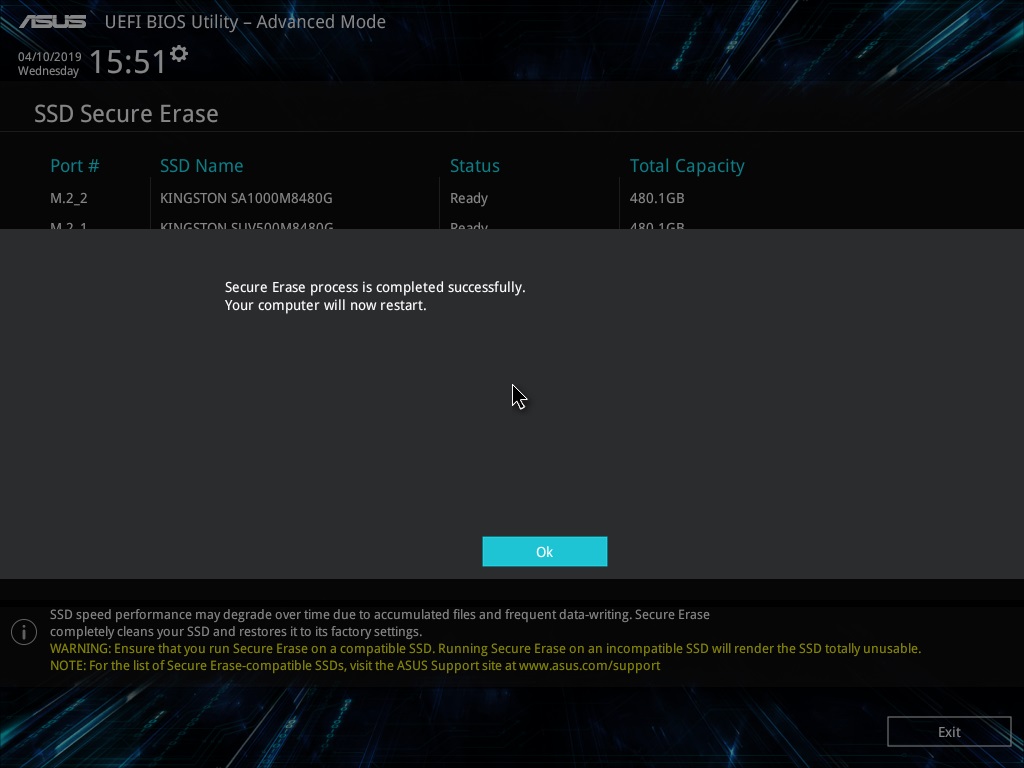
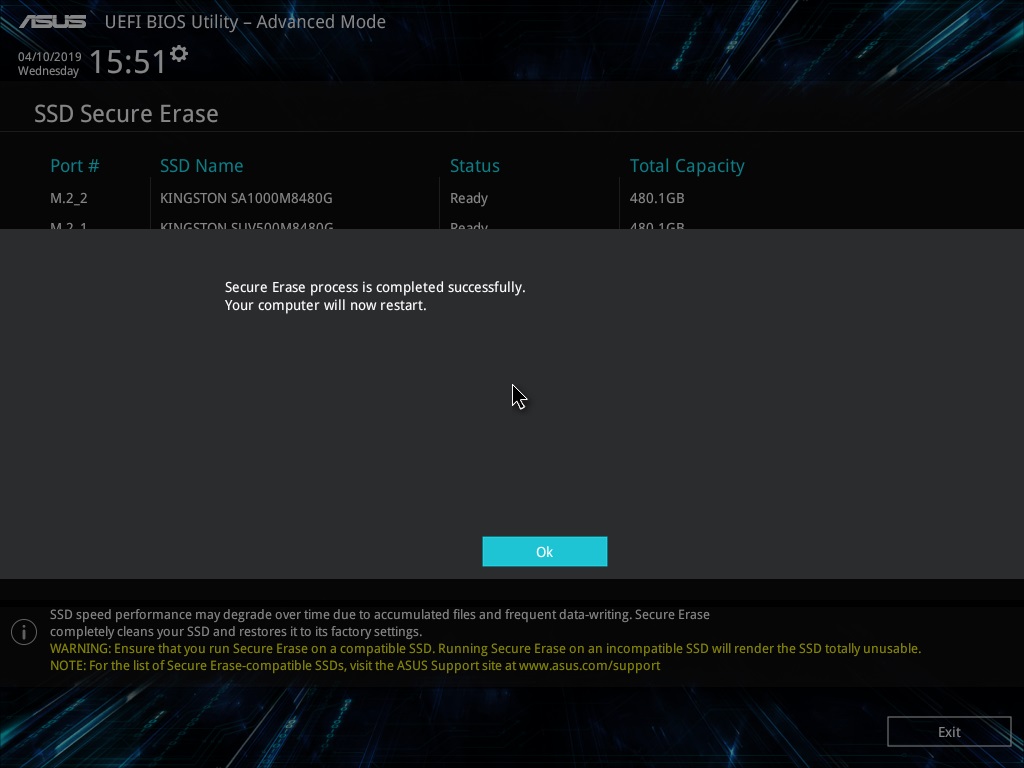
After a while, the task will be completed. It only remains to turn off or reboot the system, and the drive will be in a “like from a store” state.
Now it’s impossible to find anything on the drive.

Even if you use the in-depth analysis function.

Now consider an option that can be used if you don’t have a system with Windows 7 or a motherboard with a built-in stripper program on hand. Let's turn to the free software. It will not be possible to restore the drive speed in this way (or it will, but not as if it were the “same” Secure Erase), but no one will restore your data.
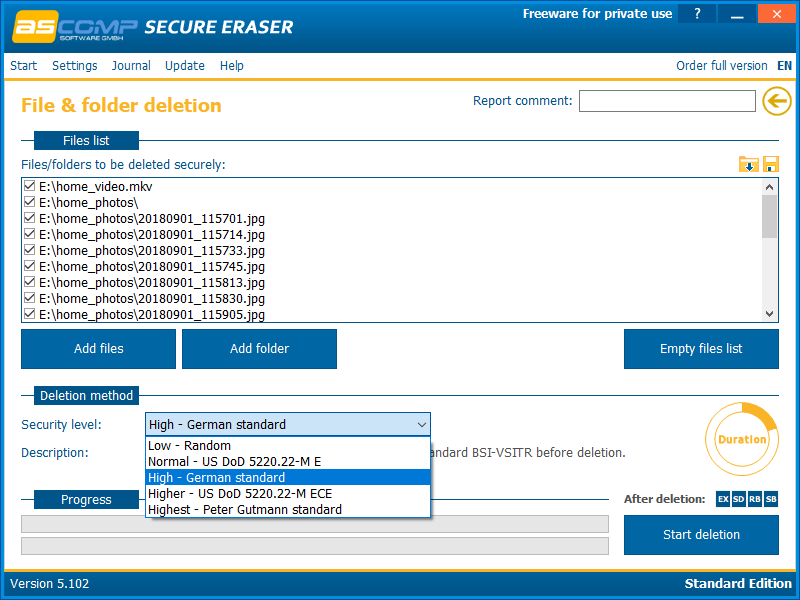
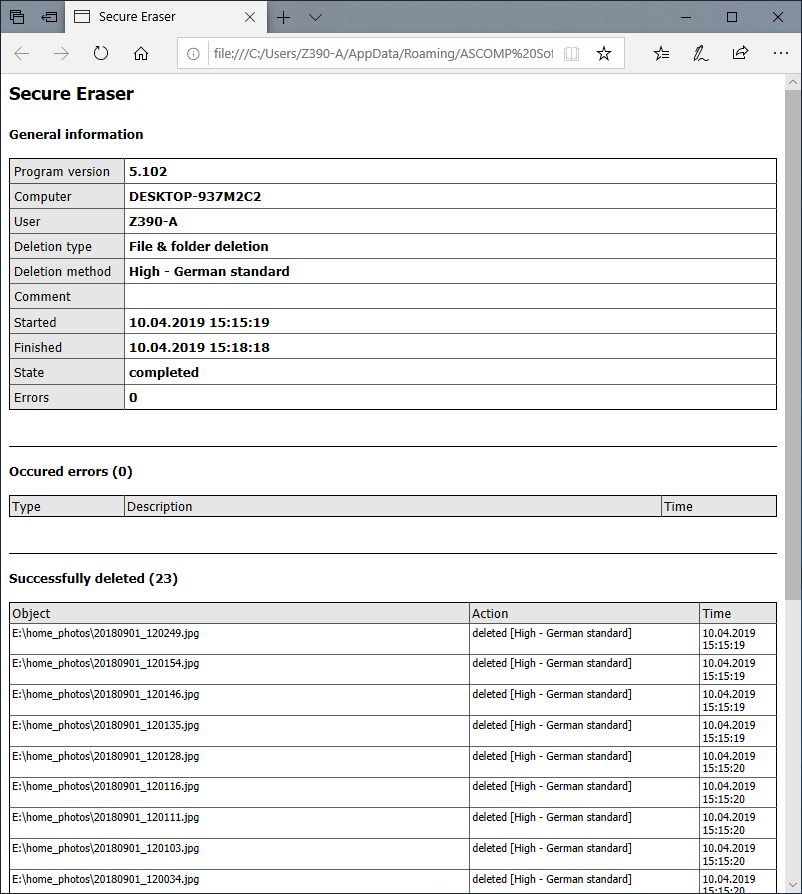
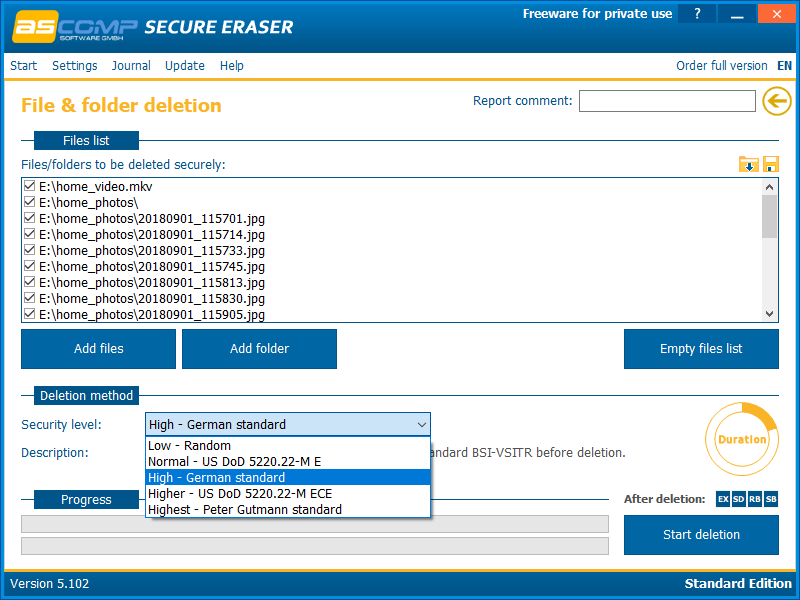
First program - Secure Eraserfrom ASCOMP Software. Its interface is as simple as possible. First, add files and folders to the delete list.

Then we select the data deletion algorithm.
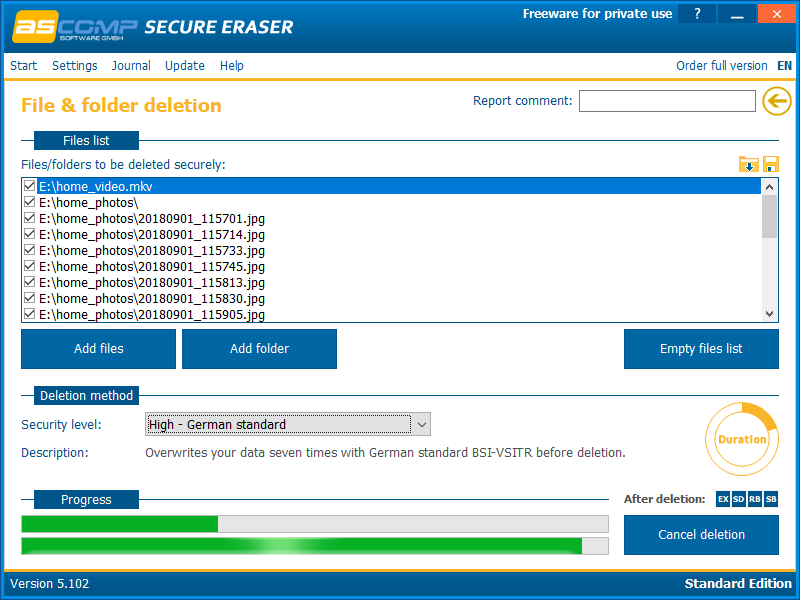
And we start the removal process. It remains only to wait a while, which depends on the amount of data to be deleted and the selected algorithm.
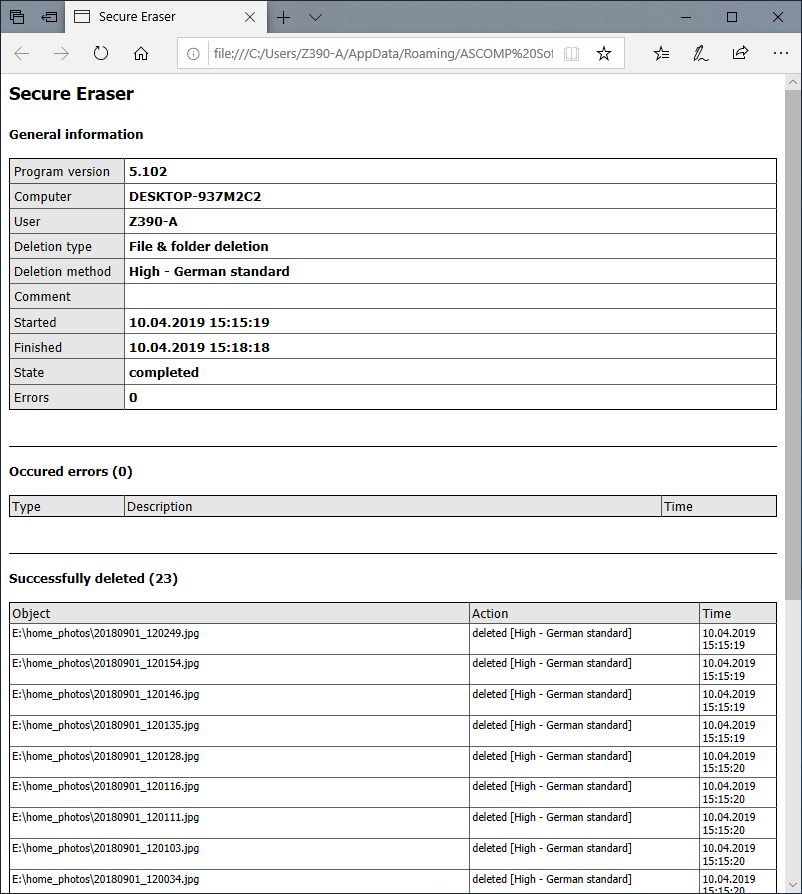
After the removal process is completed, the program displays a report on the work done.
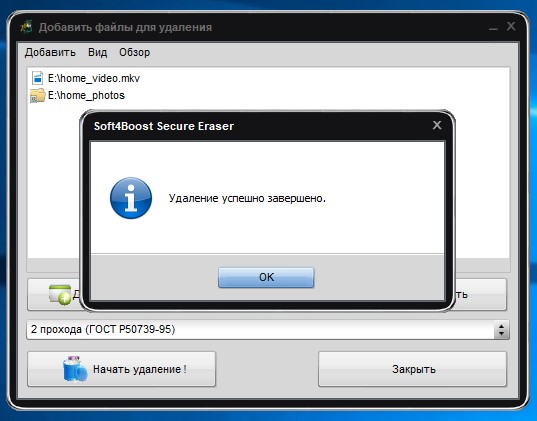
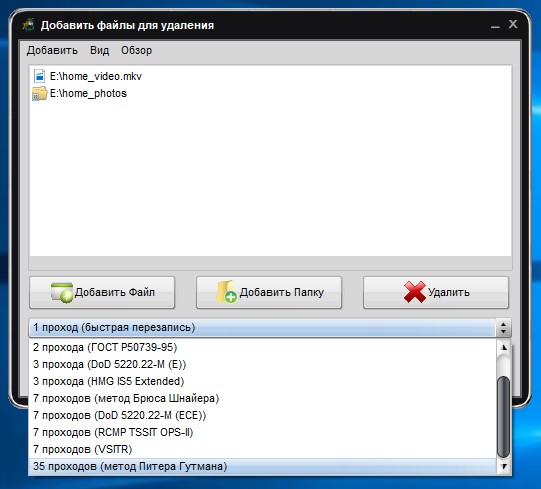
Another program is Soft4Boost Secure Eraser. This is an extremely easy to use program where you need a minimum of action. First, select the files and folders that we want to destroy.

Then, the data deletion algorithm
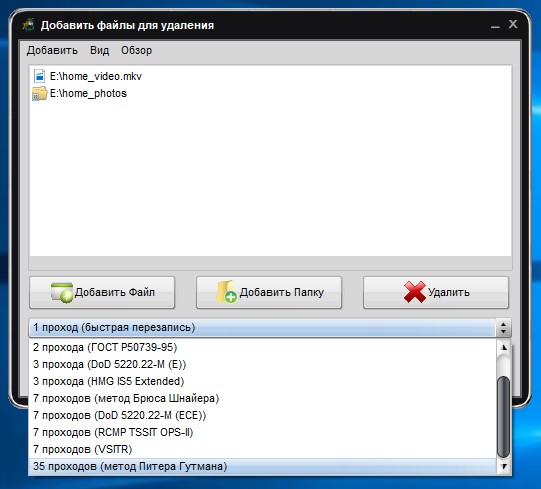
A will only have to start the process and wait for it to finish.
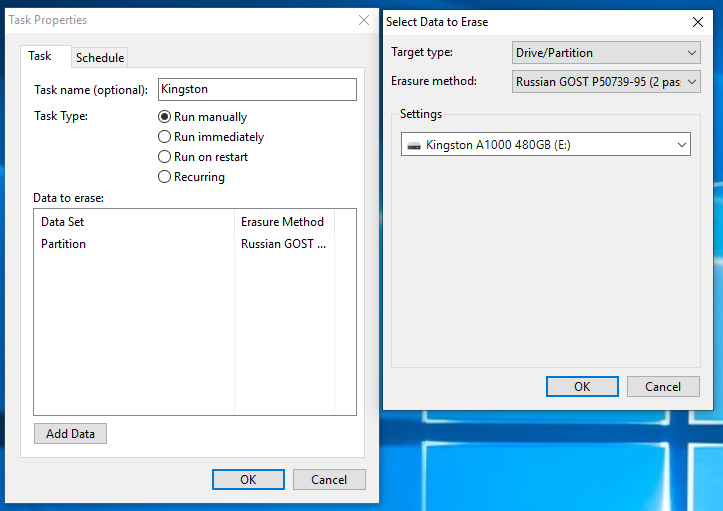
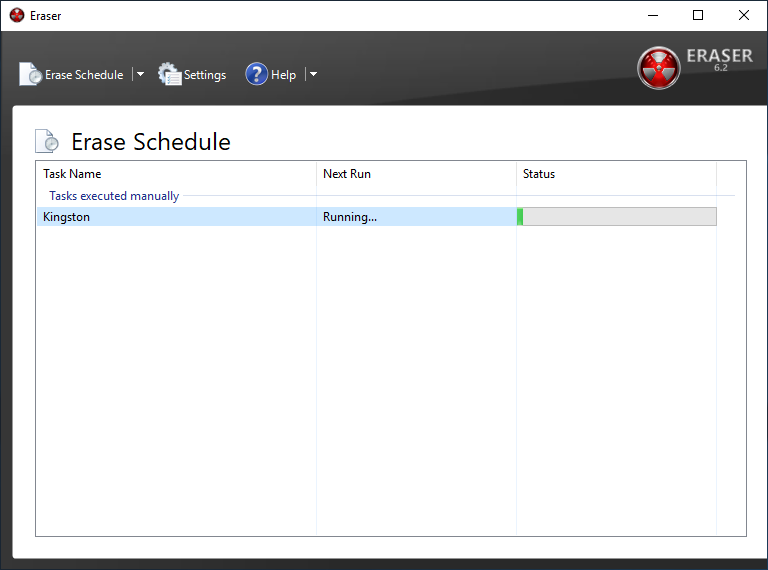
And get acquainted with another program - Eraser. This program has a fairly rich set of features, such as clearing entire partitions or disks, clearing unallocated disk space, certain files or folders, and creating a schedule for all of the above.
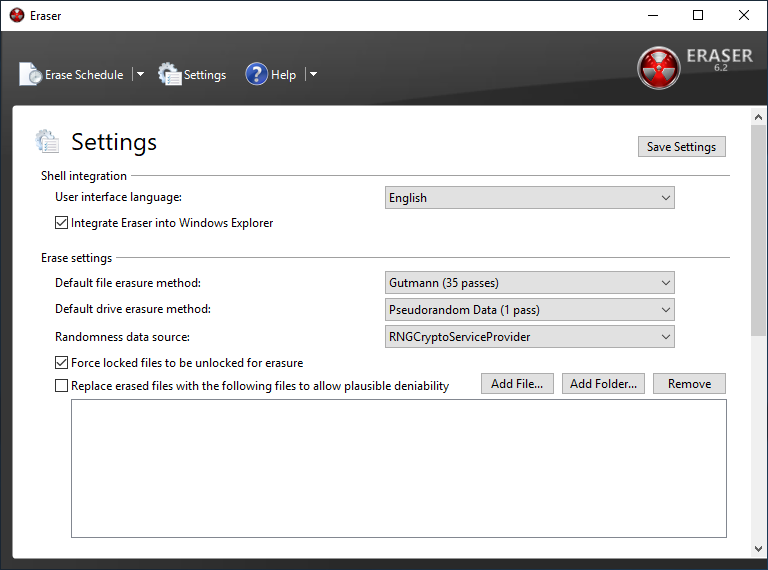
To delete certain data, you need to create a task with certain parameters.

We created a task to delete data from the entire drive. For example, this is true before selling an SSD.
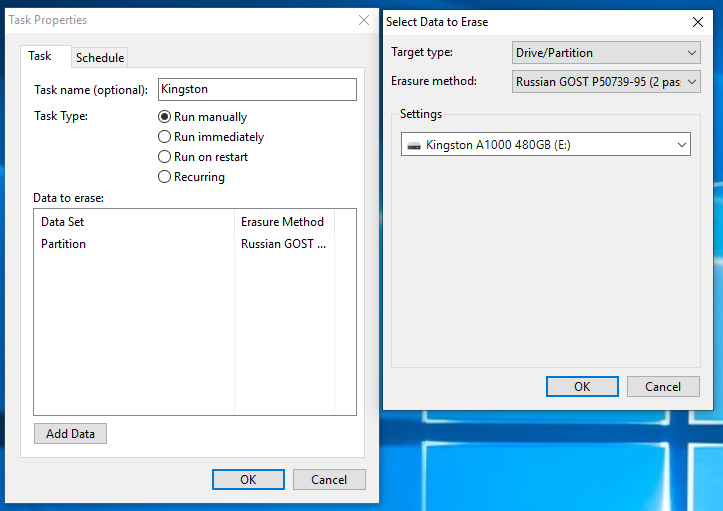
The speed of the cleaning process varies depending on the method chosen. But fast is not a single option. But there is nothing to be done - it takes time to completely destroy data.
And yet, a very brief look at another program, but the Secure Erase function is available only in its paid version. This is aboutAOMEI Partition Assistant . The program has the richest functionality for working with drives, but we are only interested in the disk cleaning function. It is noteworthy that in Windows 10 (as well as 8 or 8.1) this function is not available, which is confirmed by the corresponding pop-up window.

The program also allows you to delete data in accordance with the selected algorithm, after which it will be impossible to restore it.

Actually, nothing. Now you can be calm - your personal data that was stored on the drive cannot be restored. And the disk’s speed will be restored to almost declared (they will never be ideal, whatever one may say). A possible decrease in performance in the future is expected if the problem with TRIM / Deallocate is not resolved. Therefore, although Secure Erase is an effective way, it only removes symptoms, but the disease remains. Be sure to check for new firmware for the drive, drivers for the motherboard, or use a "clean" operating system, and not an assembly from craftsmen. In addition, it is recommended to use software developed by the manufacturer to work with the drive, otherwise there will again be a chance to “break” something, especially if you get into such settings,
And today we have seen a few points. First: the safest and fastest method of deleting data is using proprietary software from the manufacturer. All raspberries are spoiled by Windows 8 / 8.1 / 10, in which this functionality is not available or is available after dancing with a tambourine, but a solution can be found, which we talked about. Second: the use of the Secure Erase function integrated into the motherboard has a right to life. Here everything is as simple as possible - no restrictions, a few mouse clicks or keystrokes on the keyboard and the disk is pristine. And third: using third-party software to delete data. This is not exactly what the essence of the Secure Erase function is at the controller / firmware level, but the result will be approximately identical. True, with a markedly increased time to complete the task, namely, cleaning. This method is not suitable for restoring drive speed instead of the TRIM command or the first two methods, but only allows you to permanently destroy information. Delete your personal data correctly and sleep peacefully!
For more information on HyperX and Kingston products, go to the companies website.

But, for starters, let's clarify the situation. This material is aimed at ordinary (no matter - beginners or advanced) users who, for one reason or another, decided to permanently delete data from it or try to restore the drive’s high-speed performance if it began to drop significantly lower than stated (at the same time , SLC caching and other “official” reasons for speed reduction in this case we do not consider, since these are already the hardware features of the drives). The essence of the problem that Secure Erase can solve can also be that the drive began to work slowly - writing and reading data. There can be a lot of reasons, and some of them are related to the hardware component, and some to the software component. SSDs are very different in service from classic HDDs, therefore, simply deleting the data or formatting the drive does not really mean resetting the cell - it needs to be cleared before recording, which slows down the process of writing new data. In theory, there shouldn’t be such problems, because there is TRIM - a command to clear the data marked for deletion in cells during a system outage, so that we don’t notice this. This command only works with 2.5 ”and M.2 SATA drives. For drives connected to the PCIe bus (M.2 or PCIe on the motherboard) there is an analogue - Deallocate. But it happens that these functions are disabled for some reason - an OS error, a user error in setting up a disk through third-party software, the use of non-standard OS assemblies with unknown software components. And soon the disc will start to work noticeably slower,
And a few words for those who find this material an instruction for actions within organizations where data deletion is necessary as a class. In order to protect information that is critical, both for serious organizations that are concerned about the safety of data and for public sector enterprises working with information classified as state secrets, as a rule, protection systems (software and / or hardware), built on cryptographic data protection using domestic GOST 28147-89, satisfying regulatory and regulatory documents of regulators. The thing is that in Russia at the moment there is no really effective algorithm for the complete removal of data from solid-state drives, and GOST P50739-95 is focused on HDD (common HDD) for this is not quite suitable. Let's be patient - about our and not our standards a bit later. It was necessary to tell this, but with terrible formulations in this material we tie. Well, or almost :)

Why data is not deleted immediately?
Any of us once thought, and perhaps even thinks now, that by clicking the "Delete" button and then "Empty the trash", the selected files will be deleted. But in reality this is not entirely true and now we will explain why. The HDD operation algorithms are designed in such a way that when you delete a file, the operating system actually removes the link to it from the file system table. It's like removing a shortcut from the desktop - in this case, the program or game remains in place and you can still access it. Still, once at the request of parents removed the label CS or another favorite game with the phrase "everything, the game is deleted"? So here - the file physically remains on the medium, but until a new one is written in its place. Although, even after this, information can be restored by studying the magnetic fields on the surface of the disk, but this is a completely different story ... As you may have guessed, safe erasing of the HDD was very simple - absolutely every sector of the hard disk was overwritten with zeros and ones, as well as their combinations many times. Moreover, the more the better! This procedure takes a lot of time. A lot of time. That is why this method is not suitable for instant and irrevocable data deletion, if suddenly a capture group visits you. Here we need radical methods like instant physical destruction ... Not the point, the conversation is not about that. That is why this method is not suitable for instant and irrevocable data deletion, if suddenly a capture group visits you. Here we need radical methods like instant physical destruction ... Not the point, the conversation is not about that. That is why this method is not suitable for instant and irrevocable data deletion, if suddenly a capture group visits you. Here we need radical methods like instant physical destruction ... Not the point, the conversation is not about that.
With SSD, everything is completely different. Unlike HDDs, SSDs have more complex data distribution algorithms. One example of how data remains intact is related to managing it in an SSD. This is done so that the wear of the memory cells is at least approximately uniform, because they have a limited "life time". When you edit a document and save changes, they do not overwrite the original data. Instead, SSDs write new content to an empty data block and then update the logical map to indicate a new location. This leaves a place in which the source data on the SSD is marked as free, but the actual data remains untouched. Over time, data marked as free can be deleted, but until then it can be restored. Actually this is also the reason for the slowdown of consumer drives, which was mentioned a little higher. The way the flash controller controls the distribution of data does not guarantee to a large extent that the method used in erasing the HDD will completely overwrite all SSD memory locations.
Standards, standards, standards ... Are they relevant?
Secure Erase is recognized by the US National Institute of Standards and Technology (NIST) as an efficient and secure way to meet legal data sanitation requirements.
ATA Secure Erase is part of the ANSI ATA specification. In cases of its correct implementation, it erases the entire contents of the disk at the hardware level, and not using software.
ATA Secure Erase (SE) is designed for controllers in SSDs. The SSD controller resets all memory cells, leaving them empty. In fact, this method restores the SSD to its factory state, not only deleting data, but also returning the original performance. When implemented correctly, this standard will process all memory, including service areas and secure sectors.
DomesticGOST P50739-95 recommends erasing information by completely rewriting sectors. At the same time, it does not specify how many times it is required to do this and, as we have already said, this method is not entirely effective, because data can be restored with special equipment. Yes, and it is relevant again for the HDD - what to do, if they do not keep pace with new technologies abroad, then with us - even more so. True, questions of such importance, in fact, are not quickly resolved - those who worked with the FSB or, at least, the FSTEC, are well aware of what this is about. And it’s not a matter of bureaucracy or someone’s reluctance, but that it is necessary to achieve the most useful result, which is very, very difficult. And expensive.
NAVSO P-5239-26 Wipe Method- The most common worldwide recycling standard hails from the US Department of Defense. The execution algorithm is as follows:
- first pass - the specified character is recorded (for example, zero);
- second pass - reverse data is recorded (zero is replaced by one);
- third pass - recording a random sequence.
This method minimizes the residual magnetization and makes it possible to restore special. means extremely problematic. Yeah, it's not about SSDs anymore, right?
German standard VSITR . The execution algorithm runs in 7 complete rewrite cycles:
- write 0;
- write 1;
- write 0;
- write 1;
- write 0;
- write 1;
- record random data.
It turns out that at the moment of time specifically for solid state drives, normative documents do not exist or they are inaccessible to the public.

The more complex the system, the easier it is to break it.
It would seem that SSD drives have a non-trivial system of work, therefore, the scheme for the complete destruction of data should also not be the easiest. But in reality, this is not so at all. Any SSD has a controller that is the “brain” of the drive. He not only tells the system where to write data, but also skillfully encrypts the information passing through it, and stores the key with himself. If you delete (or rather, replace) a given key, then all the information will turn into a random set of ones and zeros - it will be impossible to decrypt it in any way (at least until such computing power and tools that allow you to select this key are created ) Just one simple enough action on the part of the user can solve the problem of safe data erasure. This method is the fastest and most effective.
If you combine the two methods (replacing the key and resetting the cells), you get the perfect algorithm for obtaining an absolutely sterile disk in the state of its maximum performance. This, firstly, solves the problem that we raised at the very beginning of the article, and, secondly, it can help us answer the question about the degree of wear of the drive. It is important to note that some drives with built-in encryption can receive only one algorithm upon receipt of a safe erase command - this depends on the controller settings by the manufacturer. If you “reset” your SSD and compare the actual performance with the declared one, then you will get the answer to this question. This procedure does not affect disk wear, which is very important. Note that these actions are designed specifically to analyze the state of the disk, but a long-term increase in read / write speed cannot be achieved due to the peculiarities of the operation of SSD disks - the situation may depend on both the drive model and the controller firmware. And it must be noted that not all drives support encryption. In this case, the controller simply resets the cells.
Features of cleaning SSDs with NVM Express
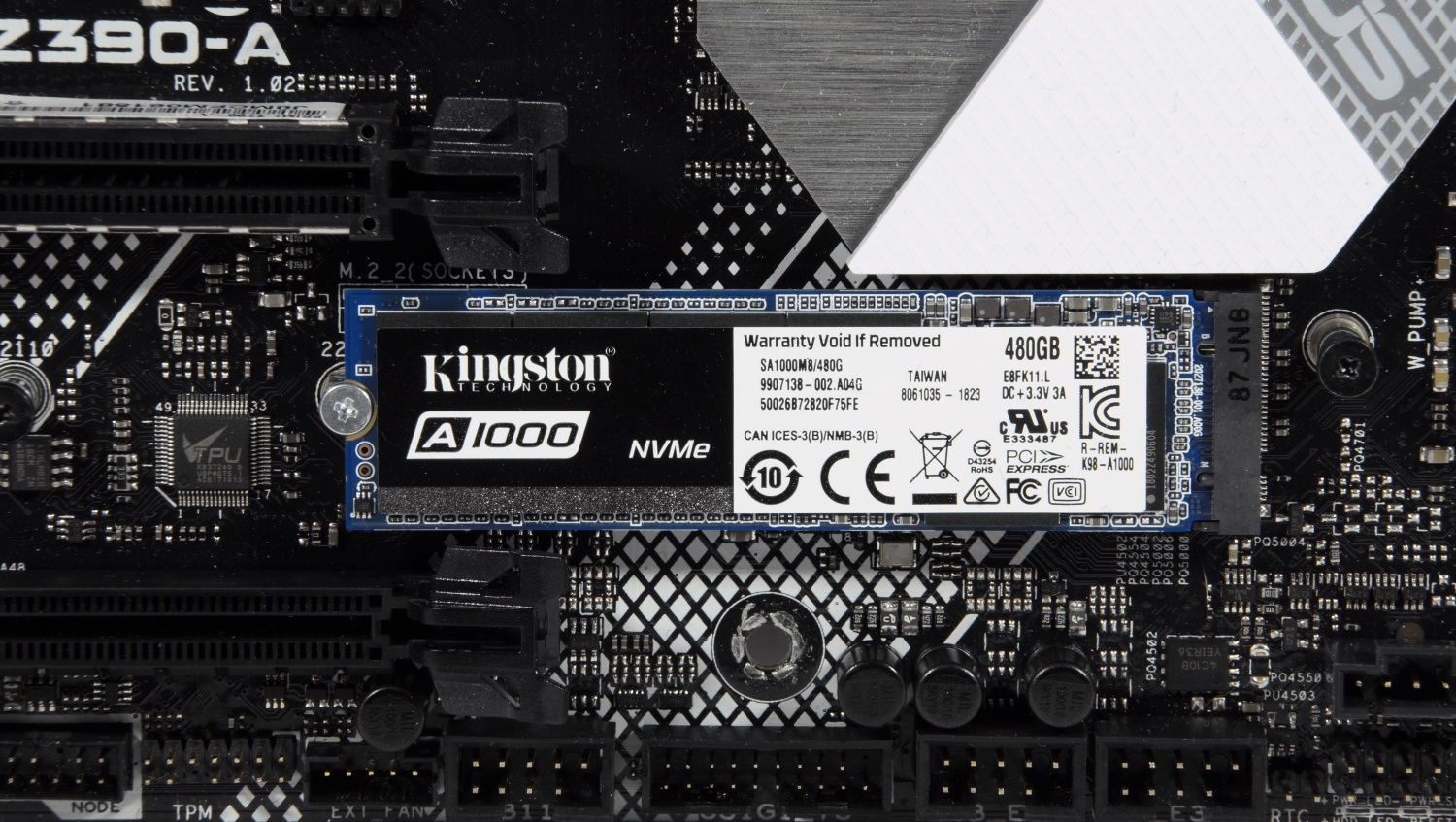
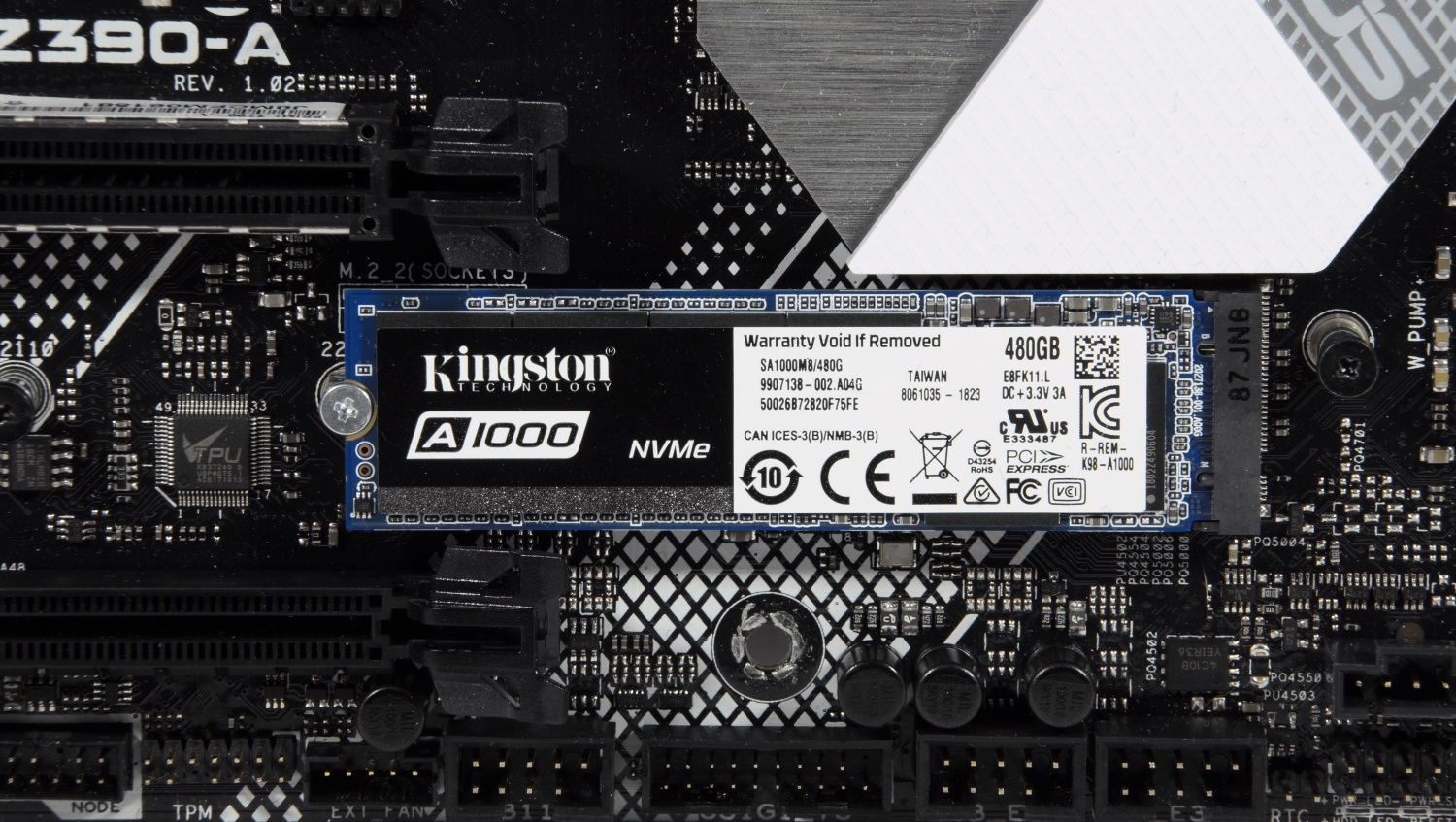
All of the above information described work with magnetic disks based on ATA / SATA interfaces, as well as SSDs based on SATA - 2.5 ”or M.2 devices, which are most common on the market now. But the modern high-speed interface of NVMe is something else. SSDs with this interface can be made in the form of M.2 cards and PCI-Express cards (similar to small video or sound cards - as you like). The NVM Express Interface (NVMe) is the specification of the logical device interface for accessing non-volatile memory connected via the PCI Express bus. NVM acts as an initializer for non-volatile memory, which is usually flash memory in the form of SSDs. NVM Express, as a logical device interface, was designed from the ground up, to maximize the benefits of low latency and internal parallelism of flash-based storage devices, reflecting the parallelism of modern processors, platforms, and applications. Disks of this type do not support standard commands, but since, as mentioned earlier, the problem is not new, the developers took this into account when designing such drives, so all (or almost all) SSDs have in their arsenal a command to run Secure Erase algorithms.
By the way, the latest NVMe specification adds new commands that can clear every nanometer of a disk (bus cache, etc.). The only problem remains software, which should be able to work with disks of this type.
When you need to erase everything. But how?
Specifications, algorithms, complex names, this, of course, is very interesting. But we want to erase our disk! What do I need to do?
Let's start with the sad. Sad for Mac OS users. The problem is that for the most part none of the utilities produced by SSD manufacturers that support Secure Erase Unit or Format NVM does not work on a Mac, so you will need to connect your drive to a system running Windows, Linux or DOS
All major manufacturers of SSDs provide utilities for working with their solutions, and you can find them on official sites. You can also use free and paid solutions, which are also suitable for data deletion, but operate on the basis of the standards mentioned above, since no one except the SSD developers knows the hardware component so that it works correctly, and also create a universal tool for all existing SSDs . For an example, we will take Kingston UV500 and A1000 drives with SATA and NVMe interfaces, respectively.
First, we add that cleaning the drive from the operating system operating on it will not work. Actually, it’s logical and nothing surprising. But you never know ...
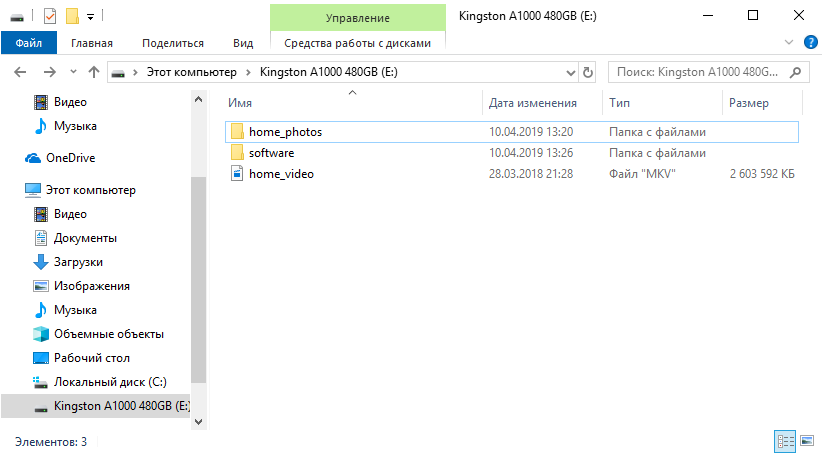
To demonstrate the processes of data deletion and recovery, we will prepare test A1000. We will drop a set of photos, videos and various software on it both in archives and in the form of executable files.
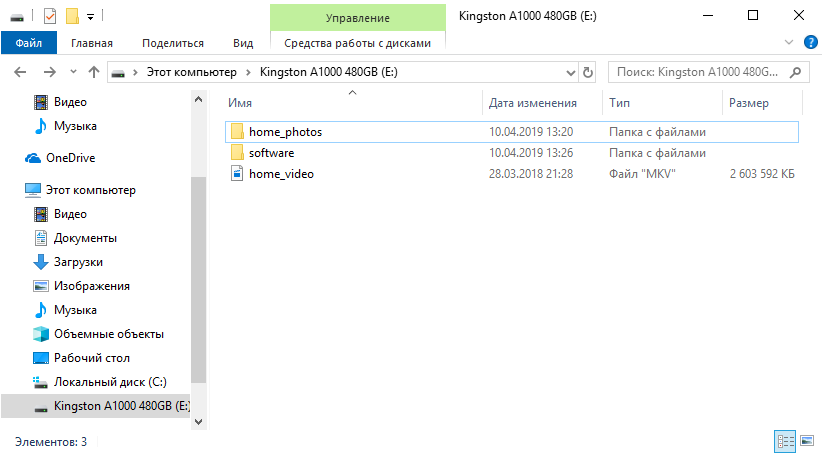
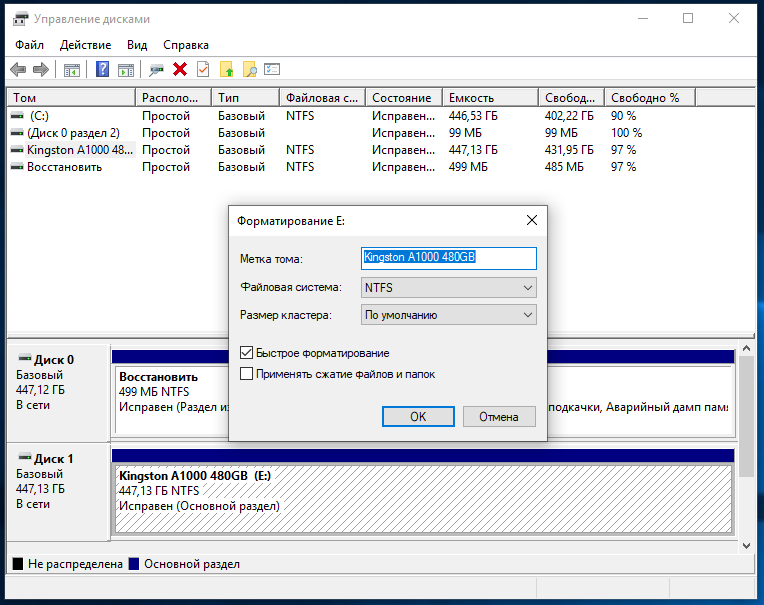
What do users usually do when they want to “delete” data from disk? For example, before selling it. That's right, format it with the default settings.
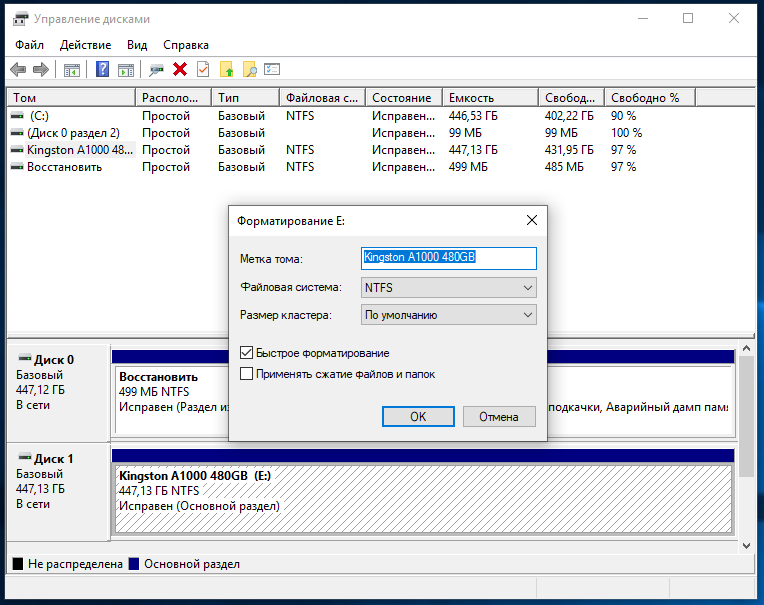
And what can a new drive owner do? Again it’s true - check your purchase for all sorts of interesting things. As you can see, the data is in excellent condition!

And it took very little time to restore them (if both drives are fast):
Now many people know that you need to delete data correctly. There are several ways to do this, but there are some limitations. For example, in Windows 8 and later, SSDs operate in such a mode that Secure Erase will not work just like that. If you can still struggle with 2.5 ”drives (to remove the“ lock ”, it is necessary to disconnect the power cable from the drive and turn it on after a switched on system with a loaded operating system), then this will not work with M.2 solutions. Similarly with the NVMe M.2 SSD. Kingston has an SSD Manager program that has all the necessary functionality to monitor the status of drives or their maintenance, including Secure Erase. Actually, when used in Windows 10, the program tells us what to do,

You can use a system with Windows 7 - everything should work correctly in it, unless, of course, you use an incomprehensible "assembly" from craftsmen with unknown how working SATA drivers for the motherboard controller are. Another option if the Secure Erase feature in Kingston SSD Manager is not available regardless of your actions is to use a USB dock to connect your drive. Then immediately no problems - the function is available without any problems. The drive is visible in the system.
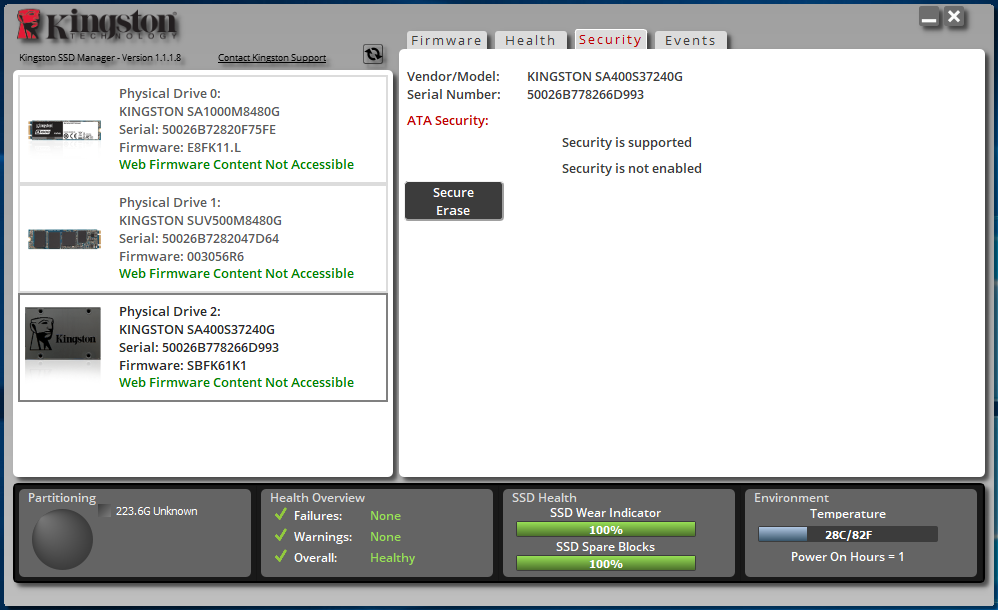
Here we need to select the connected drive, click the Secure Erase button and enter the last 4 characters of the serial number of our drive.
The process does not take much time, so you can soon start using the disk again.
Another option to run Secure Erase is from the motherboard BIOS, if such functionality is implemented by their manufacturer. Usually, the program is in the appropriate section. For example, some models of boards do not have such an opportunity.

But in a considerable number of models the program is ready to help you:

In it we see a list of mapped drives and their statuses.
To get Ready status for SATA drives, you need to disconnect and connect their power without turning off the general power of the system, as we said a little earlier. Then you need to restart the SSD Secure Erase utility. We see that the status has changed to Ready.
For NVMe disks, you must select the sector size before performing the cleanup.
And then we will be asked if we want to clean the drive.
And again - is it really? After all, the process is irreversible.
After a while, the task will be completed. It only remains to turn off or reboot the system, and the drive will be in a “like from a store” state.
Now it’s impossible to find anything on the drive.

Even if you use the in-depth analysis function.

Now consider an option that can be used if you don’t have a system with Windows 7 or a motherboard with a built-in stripper program on hand. Let's turn to the free software. It will not be possible to restore the drive speed in this way (or it will, but not as if it were the “same” Secure Erase), but no one will restore your data.
First program - Secure Eraserfrom ASCOMP Software. Its interface is as simple as possible. First, add files and folders to the delete list.

Then we select the data deletion algorithm.
And we start the removal process. It remains only to wait a while, which depends on the amount of data to be deleted and the selected algorithm.
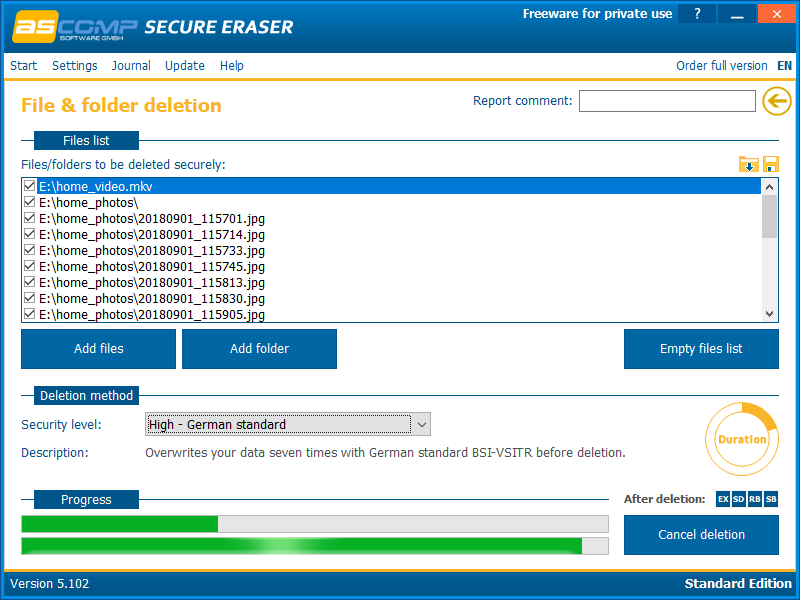
After the removal process is completed, the program displays a report on the work done.
Another program is Soft4Boost Secure Eraser. This is an extremely easy to use program where you need a minimum of action. First, select the files and folders that we want to destroy.

Then, the data deletion algorithm
A will only have to start the process and wait for it to finish.
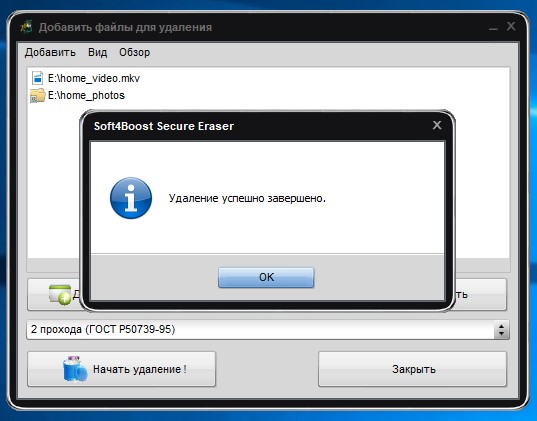
And get acquainted with another program - Eraser. This program has a fairly rich set of features, such as clearing entire partitions or disks, clearing unallocated disk space, certain files or folders, and creating a schedule for all of the above.
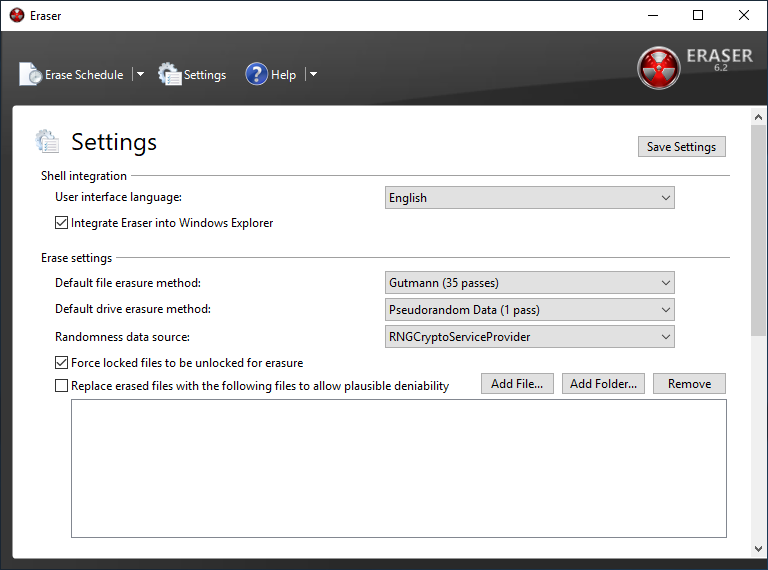
To delete certain data, you need to create a task with certain parameters.

We created a task to delete data from the entire drive. For example, this is true before selling an SSD.
The speed of the cleaning process varies depending on the method chosen. But fast is not a single option. But there is nothing to be done - it takes time to completely destroy data.
And yet, a very brief look at another program, but the Secure Erase function is available only in its paid version. This is aboutAOMEI Partition Assistant . The program has the richest functionality for working with drives, but we are only interested in the disk cleaning function. It is noteworthy that in Windows 10 (as well as 8 or 8.1) this function is not available, which is confirmed by the corresponding pop-up window.

The program also allows you to delete data in accordance with the selected algorithm, after which it will be impossible to restore it.

What's next?
Actually, nothing. Now you can be calm - your personal data that was stored on the drive cannot be restored. And the disk’s speed will be restored to almost declared (they will never be ideal, whatever one may say). A possible decrease in performance in the future is expected if the problem with TRIM / Deallocate is not resolved. Therefore, although Secure Erase is an effective way, it only removes symptoms, but the disease remains. Be sure to check for new firmware for the drive, drivers for the motherboard, or use a "clean" operating system, and not an assembly from craftsmen. In addition, it is recommended to use software developed by the manufacturer to work with the drive, otherwise there will again be a chance to “break” something, especially if you get into such settings,
And today we have seen a few points. First: the safest and fastest method of deleting data is using proprietary software from the manufacturer. All raspberries are spoiled by Windows 8 / 8.1 / 10, in which this functionality is not available or is available after dancing with a tambourine, but a solution can be found, which we talked about. Second: the use of the Secure Erase function integrated into the motherboard has a right to life. Here everything is as simple as possible - no restrictions, a few mouse clicks or keystrokes on the keyboard and the disk is pristine. And third: using third-party software to delete data. This is not exactly what the essence of the Secure Erase function is at the controller / firmware level, but the result will be approximately identical. True, with a markedly increased time to complete the task, namely, cleaning. This method is not suitable for restoring drive speed instead of the TRIM command or the first two methods, but only allows you to permanently destroy information. Delete your personal data correctly and sleep peacefully!
For more information on HyperX and Kingston products, go to the companies website.
