Positive Technologies experts identify attempts to mass exploit critical vulnerability in Confluence
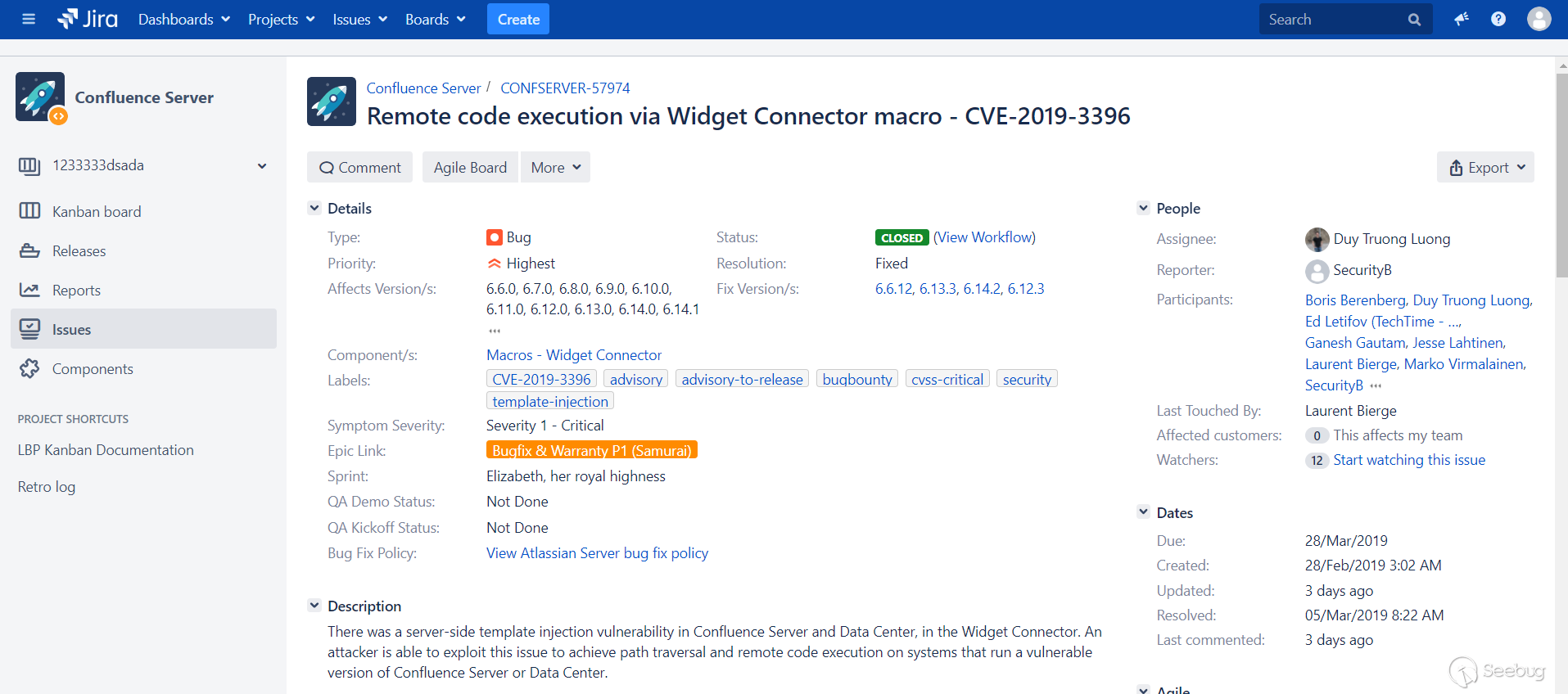
Image: Knownsec 404 Team
Information security researchers at the Knownsec 404 Team examined the patch for the Confluence vulnerability discovered in March and published a code for its operation. Using this security error allows attackers to gain the ability to execute any commands on the Confluence server and download malware.
Shortly after the publication of the exploit for the vulnerability, PT ESC experts discovered a massive attempt to exploit it. We tell you what the problem is and how to protect yourself.
What is the problem
Vulnerability CVE-2019-3396 occurred due to an error in the code of the Widget Connector module in Confluence Server. With its help, an attacker can force the vulnerable Confluence to download a malicious template from his server and execute any commands. The attack does not require authorization on the server.
In a security bulletin published by Atlassian's Confluence developers , the vulnerability is described as follows:
An attacker could exploit the vulnerability to inject templates on the service side, bypass paths and remotely execute code on systems with vulnerable Confluence Server and Data Server.
In addition, researchers from Assetnote and DEVCORE discovered the vulnerability CVE-2019-3395 in the WebDAV plugin. It allows you to fake queries on the server side (Server Side Request Forgery, SSRF). Hackers can send random HTTP and WebDAV requests from vulnerable instances of Confluence Server and Data Server.
Vulnerable software versions:
- All versions 1.xx, 2.xx, 3.xx, 4.xx and 5.xx
- All versions 6.0.x, 6.1.x, 6.2.x, 6.3.x, 6.4.x, and 6.5.x
- All versions 6.6.x to 6.6.12
- All versions 6.7.x, 6.8.x, 6.9.x, 6.10.x and 6.11.x
- All versions 6.12.x to 6.12.3
- All versions 6.13.x to 6.13.3
- All versions 6.14.x to 6.14.2
Bug fixed:
- In version 6.6.12 and later versions 6.6.x
- In version 6.12.3 and later versions 6.12.x
- In version 6.13.3 and later versions 6.13.x
- In version 6.14.2 and higher.
Exploitation
Details of the vulnerability were published on April 10, and the very next day, Positive Technologies ESC experts discovered a mass scan of 8090 ports on the Internet - this is the standard port for the Confluence server.
It’s easy to detect attacks: it will always be accompanied by incoming POST requests to URL / rest / tinymce / 1 / macro / preview and, in case of a server hack, outgoing requests to an attacker’s FTP server to download a file with the .vm extension. According to ZoomEye's search service, at least 60,000 Confluence servers are available on the Internet.
In addition, experts witnessed the infection of Confluence servers with malware from Linux Spike Trojan, formerly known as MrBlack. It is an ELF file and is primarily intended for DDoS attacks.
When it enters the system, malware is fixed using the rc.local file and starts every time the infected computer starts. After starting, in a separate thread and in an endless loop, it collects information about the system and sends it to a server controlled by attackers C2. Among the data collected is information about the processor, network interfaces, and running processes. After that, an endless loop is started in a separate thread, in which it sends the string “VERSONEX: 1 | 1 | 1 | 1 | 1 | Hacker” to the server, and in response it waits for a command.
The commands that the malware can execute are:
- execute command through shell
- start DDOS
- to finish work
The command for DDOS contains encrypted AES addresses of the servers to which the attack must be launched. The malware decrypts with a wired key.
Available DDOS attack options:
- Syn flood
- LSYN flood
- UDP flood
- UDPS flood
- TCP flood
- CC flood
How to protect yourself
The vulnerability CVE-2019-3396 was fixed on March 20, 2019. A security bulletin is available on the Atlassian website with its description and a list of patched versions. To fix the vulnerability, users need to update the system to the versions included in the patch.
Also, to detect attempts to exploit the CVE-2019-3396 vulnerability and Linux Spike activity, we developed rules for Suricata IDS:
