Doctor rides, rides
In the public domain, a MongoDB database was found that does not require authentication, which contained information from Moscow ambulance stations (SSMP).

Unfortunately, this is not the only problem: firstly, this time the data really leaked, and secondly, all sensitive information was stored on a server located in Germany ( I would like to ask if this violates any law or departmental instructions? ) .
Дисклеймер: вся информация ниже публикуется исключительно в образовательных целях. Автор не получал доступа к персональным данным третьих лиц и компаний. Информация взята либо из открытых источников, либо была предоставлена автору анонимными доброжелателями.
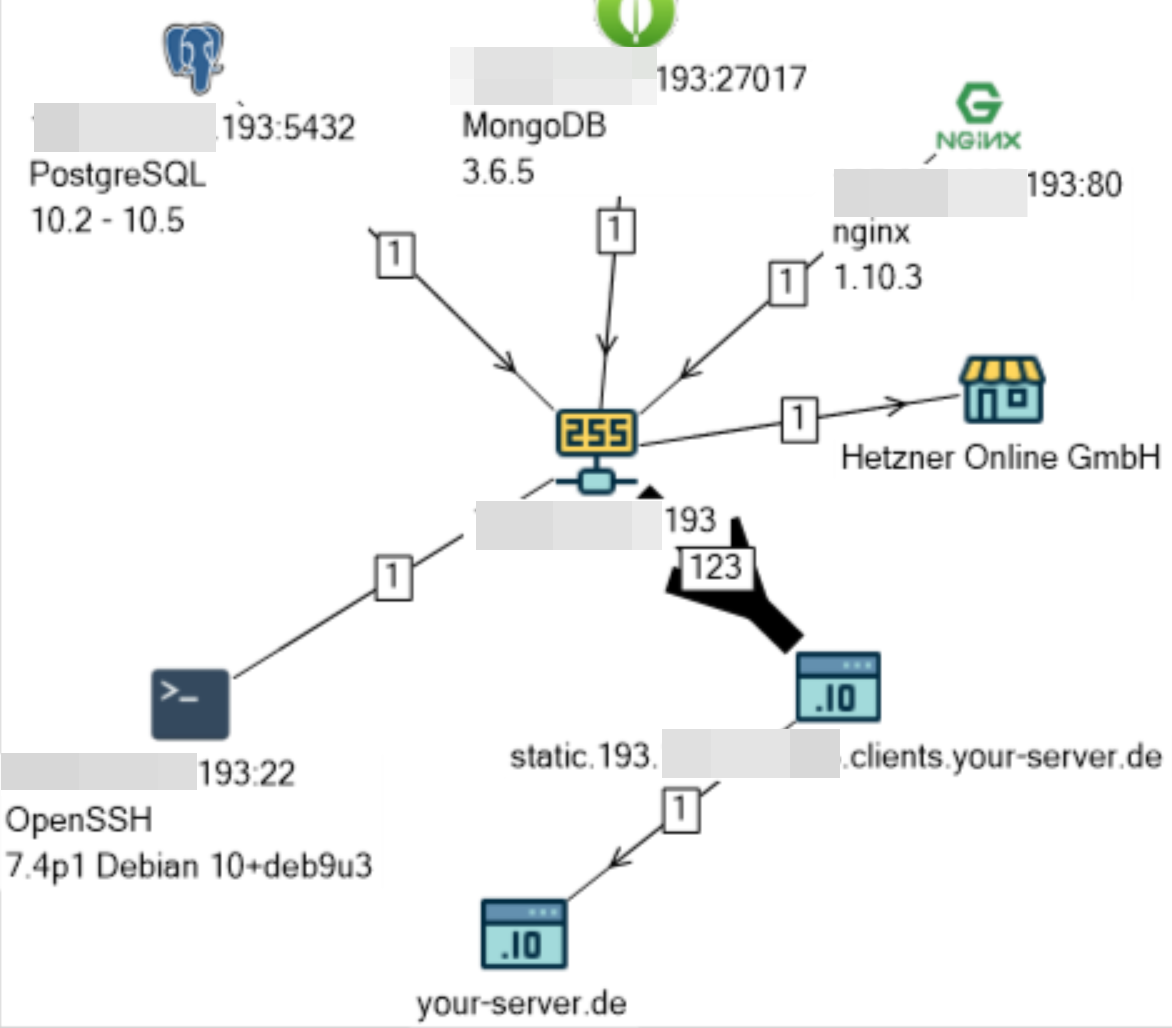
The server with the base called ssmp is located on the site of the renowned hosting provider Hetzner in Germany.
By indirect evidence, it was possible to establish the alleged owner of the server and the base - the Russian company Computer Intelligent Systems LLC .
On the page ci-systems.com/solutions/programs-smp/, the company informs us:
KIS SMP is a software product designed to automate the operation of emergency (specialized) medical care (SMP) stations within the boundaries of the subject of the Russian Federation and provides:
- receiving calls;
- call registration and redirection;
- formation, monitoring and management of field teams of the NSR stations;
- mass reassignment of ambulance brigades during emergency response;
- the work of a single call center for the NSR;
- data exchange with external information systems.
The base had a size of 17.3 GB and contained:
- Date / time of emergency call
- Name of ambulance crew members (including driver)
- license plate number of ambulance crew
- Ambulance crew car status (for example, “arrival on call”)
- call address
- Name, Date of birth, Patient gender
- a description of the patient's condition (for example, “temperature> 39, decreases poorly, adult”)
- Name of the ambulance
- contact number
- and much more…
The data in the database is similar to the log of some kind of monitoring / tracking system for the process of completing a task. Of interest is the data field in the assign_data_history table .
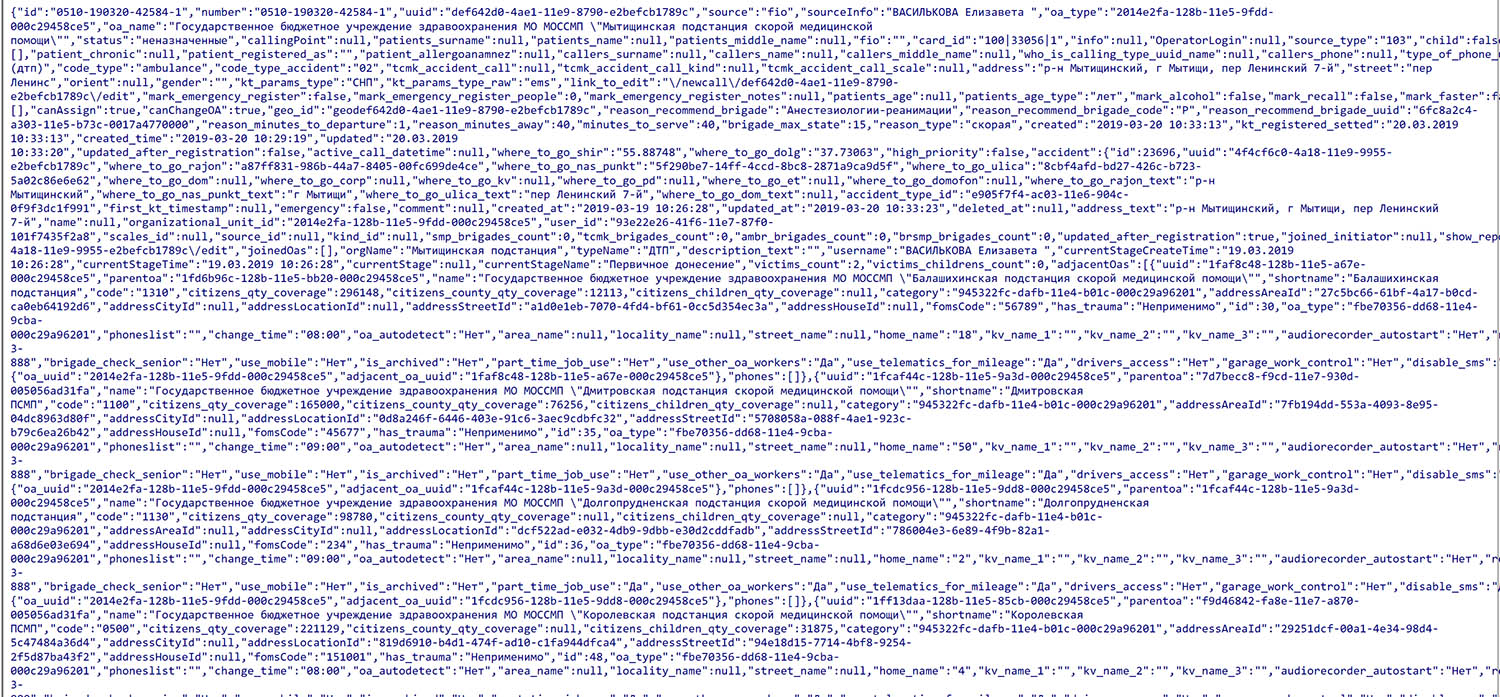
(Of course, in the picture above, I tried to hide all personal data.)
As it was written at the very beginning - the lack of authentication this time is not the only problem.
Most importantly, this database was the first to be discovered by Ukrainian hackers from the THack3forU group who leave different messages in the found MongoDB and destroy the information. This time the lads distinguished themselves by this:
"Hacked by THack3forU! Chanel. \ NPutin huylo, \ nMєdvєdєv schmo, \ nStrєlkov gamno, \ nROS_Ya BOTTOM!"
and of course by the fact that, having downloaded all 17 GB, we uploaded them in CSV format to Mega.nz file hosting . About how MongoDB open databases are discovered here .
As soon as the owner of the database was established, I sent him a notification with a proposal to still close access to the database, although it was already too late - the data "left".
The first time the Shodan search engine recorded this database on 06/28/2018, and access to it was finally closed on 04/08/2019, somewhere between 17:20 and 18:05 (GMT). Less than 6 hours have passed since the notification.
News about information leaks and insiders can always be found on my Telegram channel " Information leaks. "
