3. Check Point to the maximum. Content Awareness
- Tutorial

Hello Colleagues, welcome to the third lesson of the Check Point course to the maximum. This time I would like to discuss Content Awareness blade. This is a relatively new feature that appeared in R80.10 and many still do not use it, although in vain! Personally, I think this blade is a great addition to protecting the network perimeter, but let's talk about everything in order.
Before you start discussing this blade, I’d like to get a little insight into the issue. Those. why can this blade be useful to us in principle. First, let's look at some statistics.
2016 Check Point Report
According to the Check Point company report for 2016, we have the following figures:
I have already quoted these figures earlier, in the course on Check Point SandBlast. Unfortunately, I do not have newer data (at least for 2017), but I suspect that the statistics have only worsened. What is the message of these numbers? The number of targeted attacks is growing! Those. when before an attack the malware is developed for a specific victim, well, or a company. Modern technology allows you to do this in seconds. No need to be a genius. Ready-made tools for creating viruses are downloaded, and just a couple of commands create malware that will no longer be detected by the antivirus by signature. In the following lessons I will definitely show it. Most antiviruses, of course, still have various heuristic mechanisms, but again, this can be called just another type of signature, where the patterned actions of viruses are tracked. Various methods of obfuscation allow you to get around this level. As practice shows, modern malware learned to behave like ordinary users. For example, when a twitter page is used as a command center, where an attacker places his commands (in the form of text, or even as a picture). In this case, try to distinguish the activities of an ordinary user from a virus that knocks on twitter to get the next instruction.
And if from the top you still have to apply the constantly appearing 0-day vulnerabilities, then for the antivirus in general a sad situation develops. It is rather difficult to develop a signature for what you still don't know about. According to statistics, recently 0-day appear more often. Moreover, some vulnerabilities exist for years. Recall the same processor vulnerabilities - Meltdown and Specter. Yes, they were discovered only at the beginning of January, but they are already many years old. (Many believe that manufacturers have known about them for a long time). And there is no 100% guarantee that no one has exploited these vulnerabilities before.
To solve the 0-day malware problem, so-called sandboxes are usually used. At Check Point, this technology is called SandBlast . Now we will not consider it in detail. We will devote a separate lesson to this.
So what about antivirus and IPS that work with signatures? Are there really no more sense from them? Of course have. The percentage of attacks that use the long-known viruses is still high. And these attacks can be successfully repelled by signature analysis, without the use of a sandbox, which consumes significant system resources of the device. The sandbox, if you use it, turns on at the very last moment when all the other blades have not found anything. So to speak, the last frontier. Once again, the main idea of this slide - Anti - Virus and IPS is not enough for full protection. But of course you need to use them!
Categories of files and their extensions
We mentioned a little higher that 28% of infected files are SWF. In addition to SWF, office documents, various archives, pictures, pdf, exe are most often infected. Yes, i.e. it is not only exe and flash. In fact, there are much more files, of course:
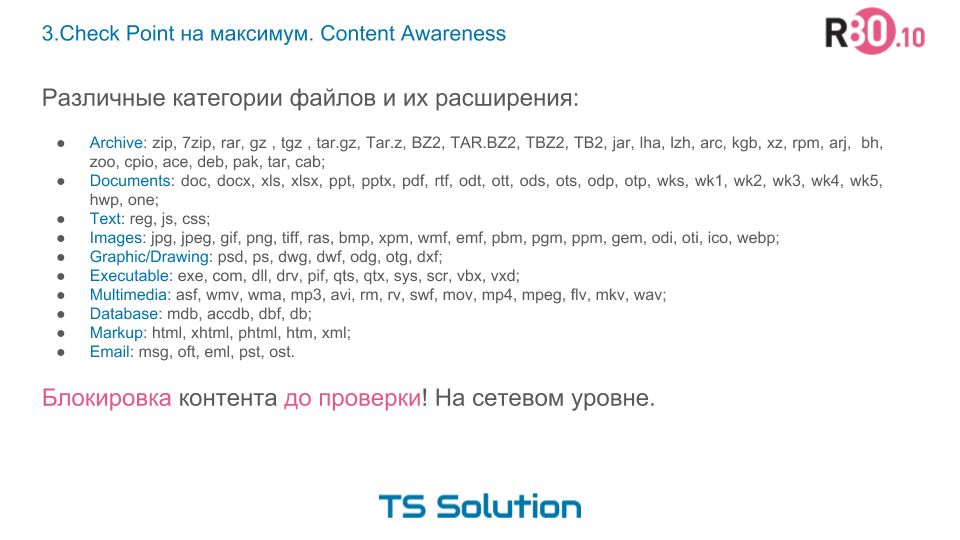
Now ask yourself, is it worth downloading some of these files in principle? Do your users need them? I’m sure not. Especially all sorts of exe, dll, vbs scripts, archives and much more. Why allow downloading what in theory is your users and do not need to download! Each file is a load on the gateway, because it must be checked. And the more files go through, the more likely that one of the viruses will nevertheless slip through. The most interesting thing is that some files are downloaded at all without notifying the user (the same malware). A little later I will show this in practice.
Of course, everything depends purely on your security policy, but it seems to me that in the general case, downloading executable files from the Internet is not necessary for 95% of company users. In some cases, the same can be said about archives and flash (swf). But it is these files that most often turn out to be infected.
Imagine how much we simplify the work of the antivirus and IPS if such files are blocked before them. As I said earlier, this will certainly have a positive effect on the performance of the device, as loading will naturally decrease. In addition, we will significantly reduce the risk of passing a previously unknown virus, as we will discard such files before verification. Why take the risk once again?
As you can see, the idea is quite simple, but significantly increases the security of your network. This is what the new Content Awareness blade does.
Check Point Content Awareness
And so, we got to the main subject of discussion of this lesson. Content Awareness is a blade that allows you to identify the type of files and the type of content in their content. All traffic going through the Check Point gateway is checked.

Out of the box, more than 60 file types are supported. A complete list can be found at sk114640 . As you understand this, office documents (doc, excel, pdf) and executable files, and much more. Actually, I reflected most of the previous slide.
In addition, Content Awareness allows you to identify what exactly is contained in these files. For example, an excel plate with credit card numbers, or a file containing data on health insurance, or a text file with MAC addresses, and much more. It is worth recognizing that most of the templates are EXACTLY content oriented to Western markets.
Content Awareness can check protocols such as ftp, smtp, http / https (naturally, with ssl inspection enabled).
And most importantly, this blade allows you to not only identify the type of file, but also block its download (Download) and upload (Upload). From this we have the following profit:
- You can prevent users from downloading a certain type of file, which we have already discussed. This will significantly increase your security, and even unload the gateway, which no longer needs to check everything in a row.
- You can prohibit uploading files to the Internet. For example, when working, your users need access to some kind of cloud storage. But you are afraid that users will merge confidential information. With Content Awareness, you can prevent them from any upload. This is closer to the DLP functionality, but do not be confused. Check Point has a separate DLP blade, whose functionality is much wider and more flexible. It supports integration with the Exchange server. But this is a separate issue, now we will not consider it. Content Awareness is unlikely to protect against deliberate attempts to “merge” some kind of information into the network, but it protects against accidental “drainage” more than well.
Those who are already familiar with Check Point may object, they say such an opportunity was earlier. It was possible to block various types of AntiVirus files. Yes, indeed, there is such an opportunity (a little later I will definitely show it). Only in this case the file reaches the AntiVirus engine (besides passing through the IPS engine) and naturally eats up system resources, because Security functionality is ALWAYS more energy consuming. Content Awareness allows you to lock files almost at the network level with minimal cost. It is very comfortable!
Disadvantages of Check Point Content Awareness
Unfortunately, Content Awareness has not only advantages. There are several significant drawbacks:
- Files are grouped into categories (archives, documents, executable files, ...). For example, if you block all archives, you may experience problems with some sites that use archived data to display. Or for example, if you need to block a separate file type (only .doc), then using Content Awareness this will not work. (This should be fixed in R80.20). But here the same antivirus will come to our aid. We will talk about this in the next lesson.
- Works only for http / https, ftp, smtp protocols. In 95% of cases this is enough,
but it happens when you need similar functionality in the framework of other protocols. - If MTA is enabled, then Content Awareness does not work for smtp.
- Only works for R80.10.
Check Point Content Awareness Demo
The video tutorial presented contains the practical part. The first half of the video duplicates the theoretical part described, so you can safely rewind.
Conclusion
In summary, Content Awareness is a very interesting feature and an additional level of protection for your network. Do not neglect it! If you still have questions, then write them in the comments, or email us . You can also contact our specialists on the portal.
PS I would like to thank Alexey Beloglazov (Check Point company) for their help in preparing this article.
Only registered users can participate in the survey. Please come in.
Do you use Content Awareness? (question for Check Point owners)
- 23% Yes 3
- 23% No 3
- 53.8% Not yet updated to R80.10 7
