Pentestit Corporate Labs: Practical Information Security Skills

It's no secret that many courses or training materials are of little use in practical life and quickly disappear from the minds of students. This is usually due to the large amount of theoretical material (often outdated) with little or no practical fixation. It may also be due to the heterogeneity of the material, the inability to apply the acquired knowledge in solving specific problems of ensuring information security.
In this article, I will look at examples of skills acquired at Corporate Laboratories for solving infrastructure safety tasks.
Learning process
The learning process is built on the principle: 20% of the theoretical part and 80% of practice to consolidate the material. The theoretical parts are given in portions, after which the students gain access to practical laboratories.
One of the distinguishing features of Corporate Laboratories is the relevance of the material. The lack of a long process of coordinating the training program with various authorities allows us to update the course with each set (every 2 months).
Theory
The course is completely remote. For maximum comfort of students, we have developed a specialized webinar, a convenient personal account and a virtual laboratory environment, which is connected to via a VPN connection.
The Corporate Labs program is developed taking into account materials and practices used by both hackers and employees of information security departments of various companies. Listening to the wishes of the specialists who are studying with us, we regularly update the content of the course in such a way as to ensure comfortable and high-quality training.
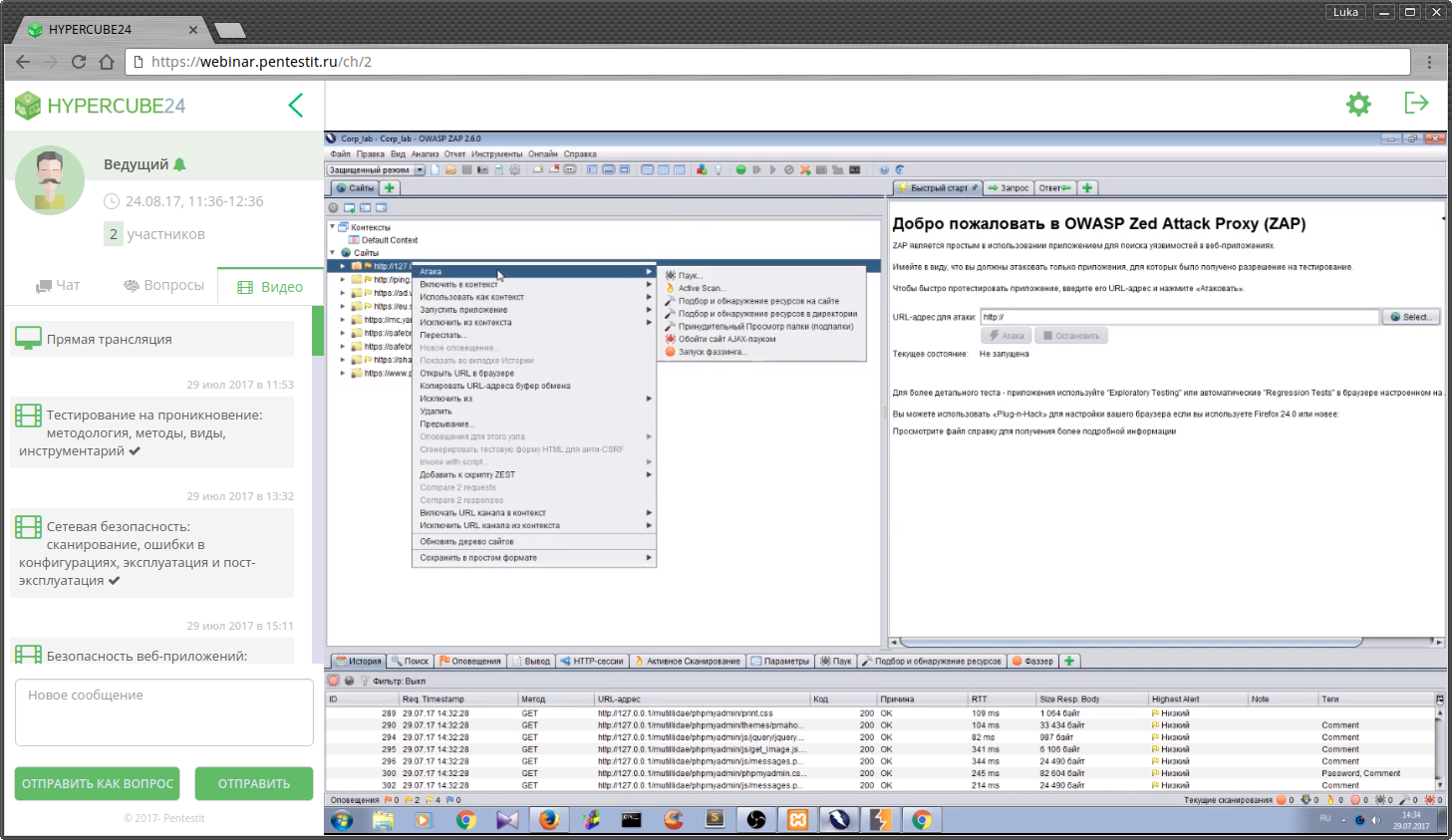
To obtain theoretical knowledge, our specialists have developed a specialized webinar site where theoretical classes are held. Also, at any time during training, you can review any of the webinars in the recording. Below is a screenshot of the webinar site:
Information on webinars is published in your account in the form of teaching aids and practical tasks, class schedules and notifications from the group’s curator.
Practice
The knowledge gained through the unique courses of ethical hacking and penetration testing from Pentestit is consolidated by completing tasks on hacking and protecting systems of varying complexity under conditions close to real ones. In the process of training, employees study the nature of vulnerabilities, exploitation tools, get acquainted with the psychology and tools of the attacker, and with protection methods.
Practical laboratories contain 26 tasks and become more complicated as the learning process progresses. The tasks in the laboratories are interconnected and are an imitation of real computer networks and systems. In the course of solving practical tasks, students receive the following work skills:
- identifying vulnerabilities in network and server devices;
- web application penetration testing - SQL injection, RCE, bruteforce;
- privilege escalation in modern OS;
- a study of the logs of Windows and Linux systems to identify hacking systems;
- research of logs of Windows and Linux systems to identify insider;
- investigation of memory dumps and network traffic;
- reversing mobile applications;
These skills will allow testing for penetration of their own infrastructure, using modern methods and tools. Knowledge related to the investigation of certain incidents will help to quickly deal with the events of the entrusted systems, as well as quickly and accurately respond to them.
Exam
The final step is to pass the examination laboratory.
In modern realities, hacking a corporate network by attackers begins with a compromise of the company's corporate website or email account, the authorization form of which is often located within the site or on a subdomain. Obtaining access to the company’s website allows attackers to carry out further attacks inside the organization’s network or, at this stage, gain financial gain. The examination laboratory is built on the same principle: on the network perimeter there is a site + several services. An example of an “entry point” in the form of a web application with an RCE vulnerability:

Attacking web applications and services, students enter the internal network and develop attack vectors within the infrastructure. All tasks are interconnected - attacking a particular service, students receive information for attacking other systems: credentials, possible technologies and services, technical information.
These skills will help identify scenarios of penetration into the corporate network and build effective defensive countermeasures. An employee who has gained testing experience from the perspective of an external intruder can help identify flaws in the intrusion detection or monitoring system.
Red Team: Teamwork in Penetration Testing
For those who want to form their own Red Team team, having received the best practices for organizing team collaboration, our specialists have developed a new training program: Red Team. The course program will help you learn how to effectively use both the tools for conducting attacks, and the methods and technologies for identifying and analyzing the actions of attackers. The theoretical part will be fixed in a specialized laboratory, which allows to put into practice all the acquired skills.
The course will allow you to effectively apply teamwork skills when conducting penetration testing, gain insight into the systems of interaction and data analysis, develop large-scale Red Team operations to identify attack vectors for complex infrastructure, conduct sociotechnical campaigns and analyze results, methods for detecting and countering attacks in real time , analysis of incidents and affected objects.
Specialists trained in Corporate Laboratories gain invaluable practical experience working with modern methods and tools to penetrate the system, study the psychology of intruders, conduct an investigation of cybercrimes, and, on the basis of this, learn to develop the most effective defense mechanisms.
Find out more and sign up for the next courses here .
