The Equation, Carbanak, Desert Falcons: report with Security Analyst Summit
 The fourth annual Kaspersky Security Analyst Summit conference was held on February 16 and 17 in Cancun (this is in Mexico). This is a very important event for Kaspersky Lab, where we share our research and invite colleagues from other companies in the information security industry to speak. Two of our presentations have already been discussed on Habré: the research The Equation APT and Carbanak attracted a lot of attention (thanks, with pleasureread comments, ready to answer questions here). In this post - a brief report on the presentations of research by Carbanak, The Equation and on the activities of another, previously unknown group, called Desert Falcons. All three - with links to detailed reports of our researchers on the Securelist website. Well, a few photos. Important: almost all the speeches will be available later in the video, we will post them in a separate post.
The fourth annual Kaspersky Security Analyst Summit conference was held on February 16 and 17 in Cancun (this is in Mexico). This is a very important event for Kaspersky Lab, where we share our research and invite colleagues from other companies in the information security industry to speak. Two of our presentations have already been discussed on Habré: the research The Equation APT and Carbanak attracted a lot of attention (thanks, with pleasureread comments, ready to answer questions here). In this post - a brief report on the presentations of research by Carbanak, The Equation and on the activities of another, previously unknown group, called Desert Falcons. All three - with links to detailed reports of our researchers on the Securelist website. Well, a few photos. Important: almost all the speeches will be available later in the video, we will post them in a separate post. Carbanak. Great robbery. Securelist (rus)
article . Full report with technical details (eng). Indicators of compromise (format. IOC ).
In the discussions for this post, most attention was paid to hacking ATMs. Indeed, this is perhaps the most resonant part of the Carbanak story: we give the command and the ATM starts issuing money, without a card, a PIN code, just like that.

On this, the creators of Carbanak and pierced: it is clear that ATMs do not behave like this without outside interference. Further investigation revealed that hacking at ATMs was only one way of withdrawing money. Attackers could transfer funds to their own accounts, manipulate the balance so that numerous security systems did not notice this. Without full control over domestic banking systems, it was impossible to crank up such an operation. Therefore, after the penetration, various methods were used to collect information about how the infrastructure of the bank was structured, including video recording:

And the attack began quite simply, more precisely, as usual:
A letter with an infected attachment exploiting, among other things, vulnerabilities in Microsoft Office (CVE-2012-0158; CVE-2013-3906) and Microsoft Word (CVE-2014-1761).
Where did the billion dollars come from?
The Carbanak study was carried out in close collaboration with law enforcement agencies in different countries. Peter Zinn of the National Hi-Tech Crime Unit spoke about this part of the work at the SAS conference.

Information from law enforcement agencies allowed us to estimate the total number of victims of Carbanak - about a hundred financial organizations. Given that the casualties of each victim ranged from $ 2.5 to $ 10 million, the maximum damage from Carbanak could amount to just a billion dollars.
Body shirts
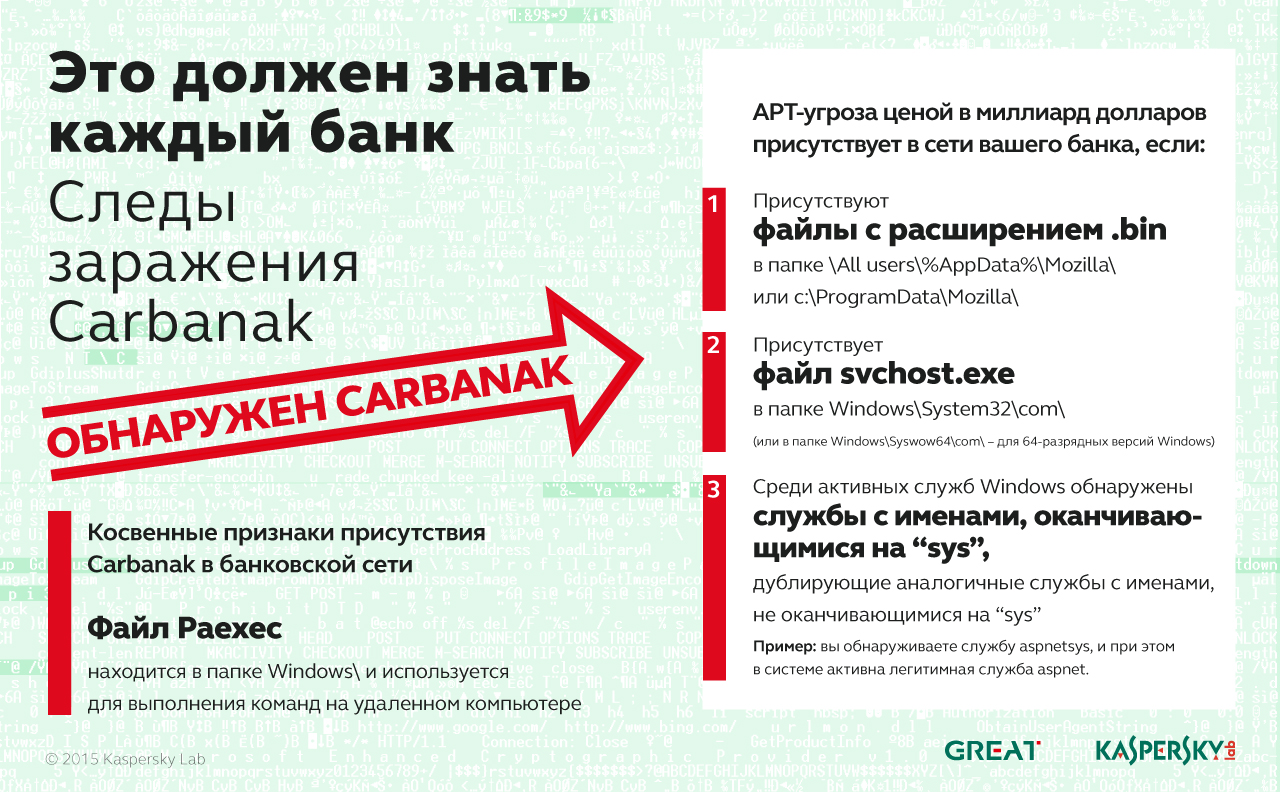
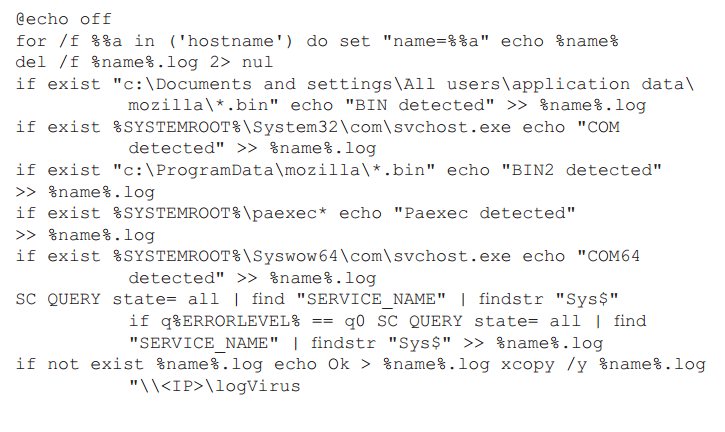
An interesting story occurred during the investigation, when the fact of infection was already confirmed and it was necessary to identify infected computers. This had to be done as quickly as possible: firstly, to block the threat, and secondly, to collect samples for research. A simple script was written for this:
The Equation or “Stucks, I'm your father” or attribution difficulties. Securelist
article . Q&A (eng). The study of the Fanny module (eng).
This year, all SAS guests received a bookKim Zetter on Stuxnet Autographed by the Author. To make you understand: this is such a Talmud of 500 pages, and, according to Zetter, the publisher asked to minimize (as much as possible) the technical details. If you ever write a book about The Equation, then its size will be no less. An important point: now the study of this operation is at an initial stage. We published only general details and examined in detail one of the modules. Further research will require time and effort, both on the part of the Laboratory and other companies. Why? Those who are behind the Equation APT have been doing their job for more than 10 years, and possibly more than 20 (if you count by the date of registration of the first domains for C&C servers).

Researchers at Kaspersky Lab who spoke about The Equation at SAS: Igor Sumenkov, Sergey Mineev, Vitaliy Kamlyuk, Kostin Raiu.
Grzegorz Brzęczyszczykiewicz
We were able to reliably identify more than 500 victims of The Equation. Given the fact that a self-destruction mechanism is built into the malicious modules of the operation, the total number of victims can reach tens of thousands. Among them are government agencies, telecommunications companies, representatives of the aircraft industry, the oil and gas sector and so on. And our investigation began when a man named Grzhegorzh Brzhezhishchichievich began to suspect that he was the victim of a malicious attack after he inserted a photo disc into the CD-ROM drive. The disc was sent to him from a scientific conference in Houston, in which he had previously participated.
Of course, we changed the name of this person due to confidentiality. It is possible that such an alias was chosen thanks to this video:
What do we know about The Equation now? Judging by the dates of domain registration and compilation of modules, the campaign has been active for decades. The oldest modules, in particular, support Windows 95/98. To attack and collect information, different modules and different methods of infection were used (for example, through infection of forums). One of the modules, known as Fanny, was used to collect information about victims in Asia and the Middle East, was created in 2008 and exploited two Zero-Day vulnerabilities. The same vulnerabilities were later used in Stuxnet. The key word here is “later,” this fact, as well as some others, give a hint of the connection between Stuxnet and The Equation.
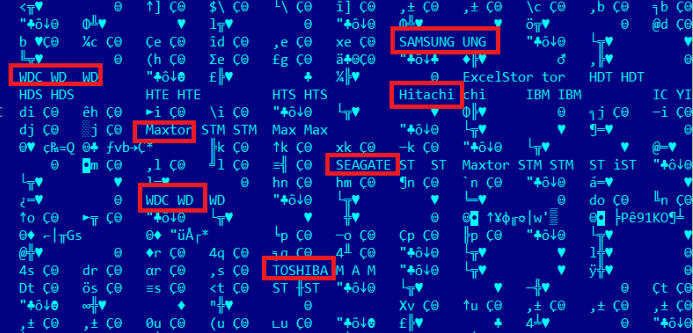
And this plugin is perhaps the most interesting. Known only by the file name (nls_933w.dll), it seems to have been used extremely rarely, in exceptional cases, allowing you to modify the firmware of your hard drive (or SSD). What for? Well, firstly, to regain control of the victim’s computer, even if the information is completely deleted from the drive. Secondly, for reliable and most secretive data storage. Identifiers of 12 drive models that could be subjected to this procedure were found in the plugin code. Given the complexity of the firmware analysis and the fact that any error in the code in this case leads to the complete inoperability of the hard drive, this module shows how wide the possibilities of the group that created it are.
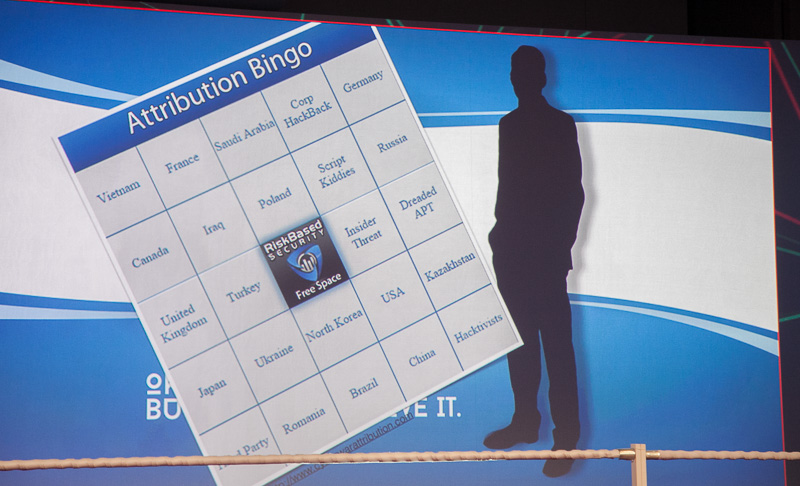
Attribution
This is a very important point: Kaspersky Lab cannot yet say anything about who exactly is behind the Equation APT. We simply do not have enough facts to reasonably accuse someone of involvement in this campaign, or at least to identify the region or country from which the operation was conducted. Everything else at the moment is speculation and speculation, we do not do this. Attribution is generally a very difficult task, since even explicit hints of the origin of the creators of the malicious program found in the code (not in the Equation code, but in general) are sometimes specially introduced in order to direct researchers (or investigators) in the wrong direction.
Attribution complexity has been discussed more than once during the two days Security Analyst Summit. Here's an anecdotal example of a speculative approach in a presentation by Christopher Hoff of Juniper Networks:
Desert Falcons: New APT Campaign in the Middle East Securelist
article . Detailed research (eng, pdf).

In Dmitry Bestuzhev’s story about the Desert Falcons campaign, I was most surprised by how thoughtfully attackers use social engineering methods. Naturally, they attack via e-mail:
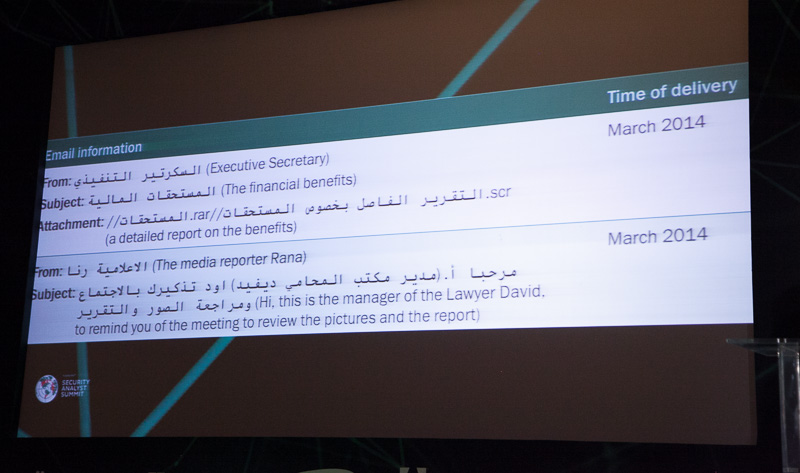
But not only. Use Facebook. Stuff in friends, chat in private, prepare for monthsare trusted to finally send a link to the infected file. Or simpler: they take advantage of the fact that influential people do not close posting on their wall from other users. Instantly respond to significant events that are important for potential victims and adapt their messages and mailings by e-mail.
Those behind the Desert Falcons campaign know their victims very well. Most likely because they themselves live in one of the countries of the Middle East. This is precisely what is important in this study: we see a new player developing his own tools for attacking and collecting information (rather than using stolen goods), who knows the local landscape well. Unlike The Equation, operations of a long and now inactive, “desert falcons” began work relatively recently (since 2011), and are now in the best shape. Result: malware infecting computers and Android-based mobile devices in order to steal data, and according to our data, more than a million files and documents from 3,000+ victims fell into the hands of the attackers .
Further on our blog. We are preparing several more topics based on the results of presentations at the Security Analyst Summit, including on the features of using legitimate software for criminal purposes, in particular in crypto-lockers, for which there will be a separate review and statistics. You can get acquainted with quotes from almost all performances on SAS and the most interesting remarks of the audience on social networks in this epic live blog on Kaspersky Daily.
