Differentiation of information systems in the protection of personal data
The subject of this article is the delimitation of information systems when protecting personal data using the Cybersafe Firewall program. The article will show an example of program deployment and access control for PC groups in a real company.

ISPDn (Personal Data Information System) - an information system that is a combination of personal data contained in the database, as well as information technology and technical means that allow the processing of such personal data using automation tools or without using such tools.
According to the order of the FSTEC of Russia No. 21 dated February 18, 2013, in order to ensure 3 levels of protection of personal data, the following are applied (paragraph 12b):
firewalls of at least class 3 in case of relevance of type 2 threats or interaction of an information system with information and telecommunication networks of international information exchange and firewalls of at least 4 classes in case of relevance of type 3 threats and lack of interaction of an information system with information and telecommunication networks of international information exchange;
This article will discuss the practical use of the Cybersafe Firewall program , which is currently certified at the 4th security level, but will be certified at the 3rd level within a month (the certificate is already signed by the FSTEC). The corresponding certificate can be found on the CyberSoft website. A link to the state register of certified software will be given at the end of the article.
The structure of the company in which we recently implemented the Cybersafe Firewall program is shown in Fig. 1.
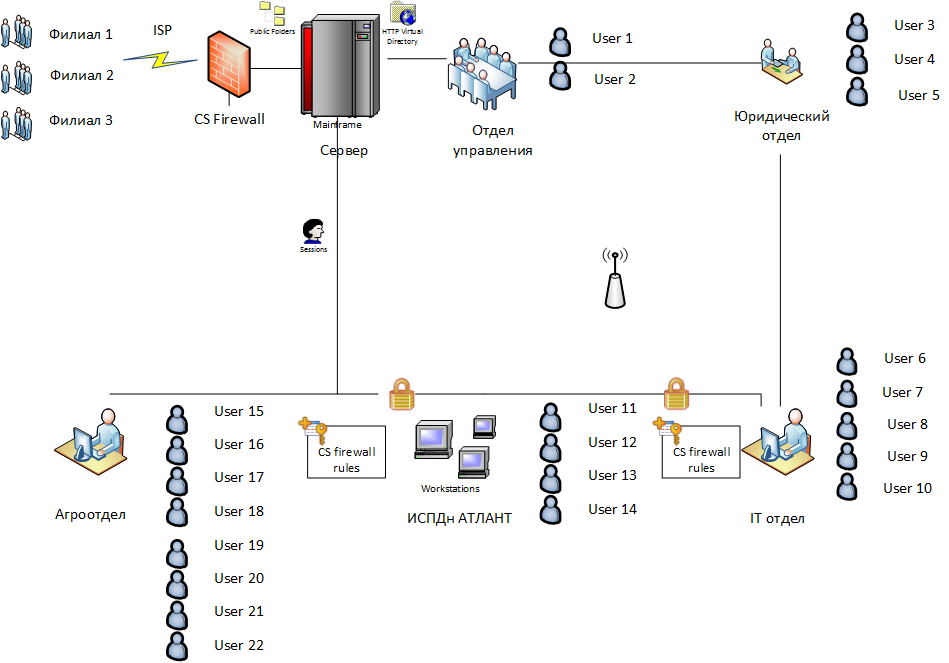
Fig. 1. Structure of the company
The company under consideration contains five departments (Agro Department, IT department, legal department, management department, ISPD Atlant PD) and three branches. Communication with remote branches is via the Internet. On the gateway, as on other computers on the network, the Cybersafe Firewall program is installed.
Later in this article, you will see how to deploy the Cybersafe Firewall program to all computers on the network using Active Directory, as well as configure group rules.
Our task is to protect the ISPD group from the outside world (that is, close its Internet access) and from the rest of the local network. Thus, computers in ISPDn will be able to "communicate" only with each other. It is worth noting that this product was specifically created for the fastest possible solution to tasks to restrict access to PC groups. In other products, solving the task takes much more time or is impossible at all (if the system of dynamic distribution of network addresses is used). If you do not take into account the time required to deploy the program using Active Directory, you can limit the access of one group of computers to another in a matter of minutes.
This scheme does not claim to originality or novelty. The task was to make the product as convenient as possible for distinguishing between several IPs or to limit one IP with confidential information from other sectors of the local network and the Internet in strict accordance with the legislation of the Russian Federation.
The first step is to create a transformation file (MST file) so that you can deploy the Cybersafe Firewall to all computers on the network with the same settings. After that, you don’t have to manually configure the firewall, for example, create a user to enter the program, specify the IP address of the remote server, its port, etc.
Install the program on a computer that will be used as a remote Cybersafe firewall server, and which you will use to manage the firewalls of the entire network. You can install the program on your own computer, or you can install the program directly on the gateway, which will provide other computers access to the Internet.
Complete the following steps to create a deployment script:
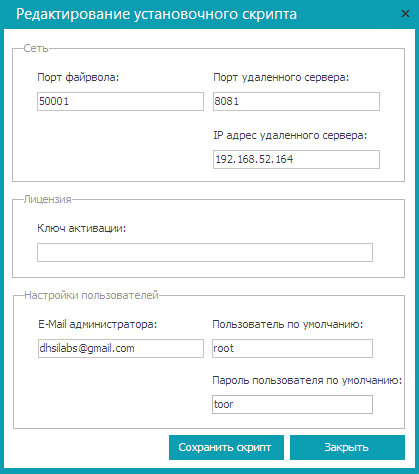
Fig. 2. Creating a deployment scenario
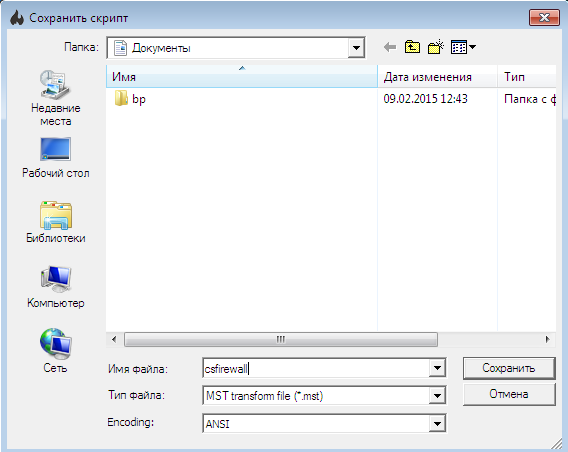
Fig. 3. Saving the deployment scenario The
Cybersafe Remote Server program is described in detail in the Cybersafe Firewall program guide (http://cybersafesoft.com/eng/products/cybersafe-firewall/).
If your organization does not use Active Directory, then using the Cybersafe Remote Server program, you can create a batch file (* .bat). To deploy the program on all computers on the network, it will be enough to copy it to each computer along with the program installer (MSI file) and run it (batch file). If for each computer unique users are needed, then you can manually run the program installer (MSI file) on each computer, while you do not need either a transformation file or a batch file.
Now let's look at the process of deploying a Cybersafe Firewall program using ActiveDirectory. All illustrations for this section were created in Microsoft Windows Server 2012 R2, but all of the instructions given will work in older versions (Microsoft Windows Server 2003/2008), illustrations may slightly differ.
The first step is to create a folder for the software deployment. It will contain all the MSI packages that you need to deploy (you do not need to create a separate folder for the Cybersafe Firewall program).
Let it be the C: \ Install folder. In this folder, create a subfolder of CSFirewall. You need to place the csfirewall.msi installation file and the csfirewall.mst transformation file that you created in the previous section in it.
The C: \ Install folder must be shared. To do this, right-click on the folder and select the Properties command . On the Access tab, click the Sharing button and provide read and write access to the administrator and read-only access to all other network users.
Next, run the gpmc.msc Group Policy Editor. We assume that the Cybersafe Firewall program needs to be installed on all computers on the network. Therefore, right-click on the domain and select Create a GPO in this domain and link it (Fig. 4).
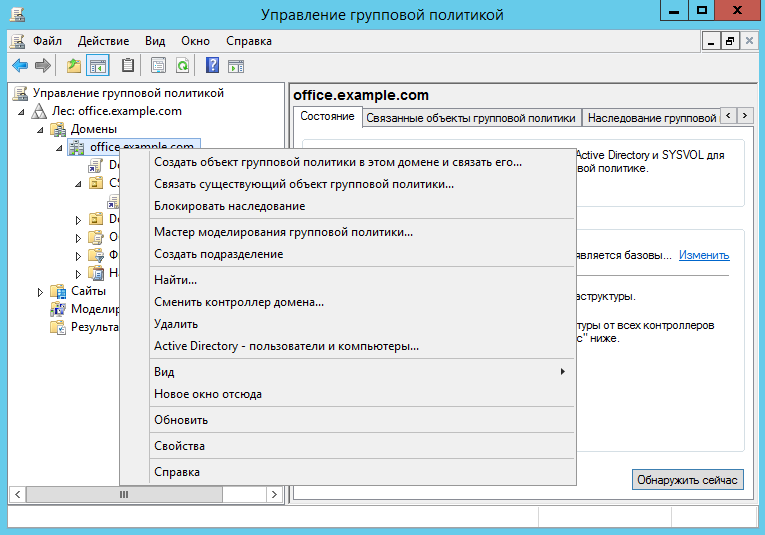
Fig. 4. Group Policy Editor.
Name the new GPO CS_Firewall (Figure 5). In chapterSecurity filters, delete the Authenticated Users group and add the computers, groups and users to whom the settings of this GPO will be applied (Fig. 6). In other words, add the computers on which the program should be installed.
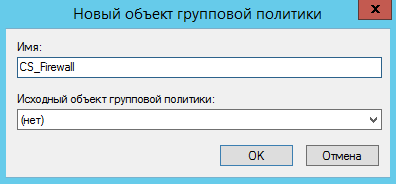
Fig. 5. Creating a new GPO

. 6. Created GPO Object
Right-click on the newly created GPO (CS Firewall) and select the Modify command . Go to the section User Configuration, Policies, Application Configuration, Installing Programs (Fig. 7).
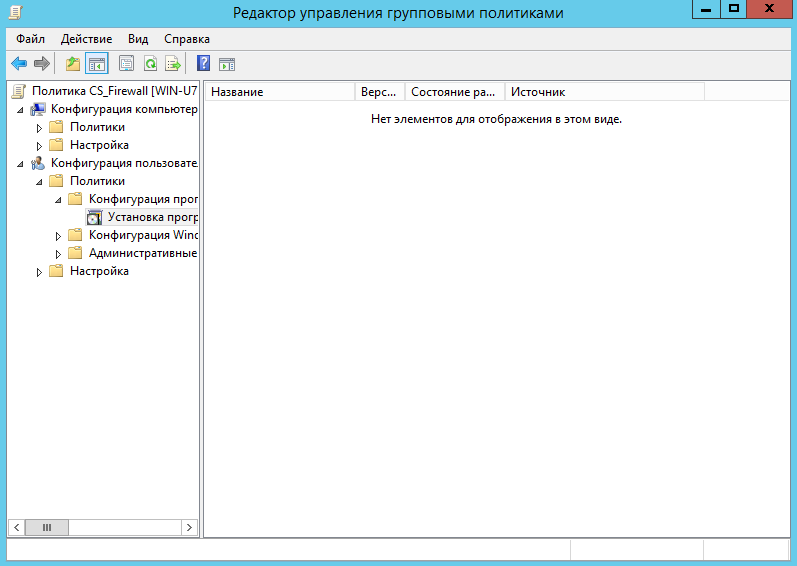
Fig. 7. Section User Configuration, Policies, Software Configuration, Installing Programs.
Right-click on the section.Install programs and select Create, Package . In the window that appears, you need to select the path to the MSI file of the program. Please note that you need to enter not a local path, but a network path, since users will access the package over the network.
The next step is to choose a deployment method. Since we want to provide a transformation file (.mst file created by the Cybersafe Remote Server program), we need to select a special deployment method (Fig. 8). This will open the deployment package configuration window (Figure 9). Then go to the Modifications tab , click the Add button and select the transformation file (.mst file), Fig. 10.

Fig. 8. Choosing a deployment method
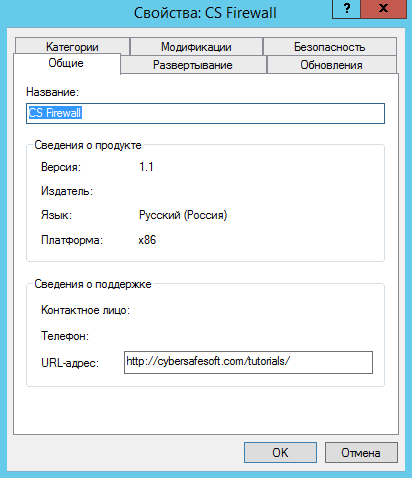
Fig. 9. Set up the deployment package

Fig. 10. Specify the transformation file.
Click OK .
Note . After clicking OK, the package and the transformation file (.msi and .mst files, respectively) will be cached. If you need to change the transformation file after creating the package, you will have to create the deployment package again.
This completes the work with the Group Policy Editor. Close all windows, open a command prompt (or at least Run , by pressing Win + R) and enter the command:
That's all. The program will be automatically installed on computers after they are rebooted and before the login window is displayed. The user cannot influence anything and cannot be mistaken in anything.
Sometimes the program does not install automatically. Most often, this problem is observed on workstations running Windows XP. To install it, you must manually enter the gpupdate / force command on it.
Using the Cybersafe admin panel firewall, you can set global and group rules for all Cybersafe firewalls installed on your network. Global rules apply to all computers on which the Cybersafe firewall is installed, and group rules determine the behavior of the Cybersafe firewall installed on a specific group of computers.
Before setting up global and group rules, you need to designate the user as an administrator. This can only be done using the Cybersafe Remote Server program.
An administrator can use the administration panel to manage a remote firewall. So, in the Cybersafe Remote Server program, expand the Users nodeand select the user you want to make an administrator and enable the Administrator switch (Fig. 11).
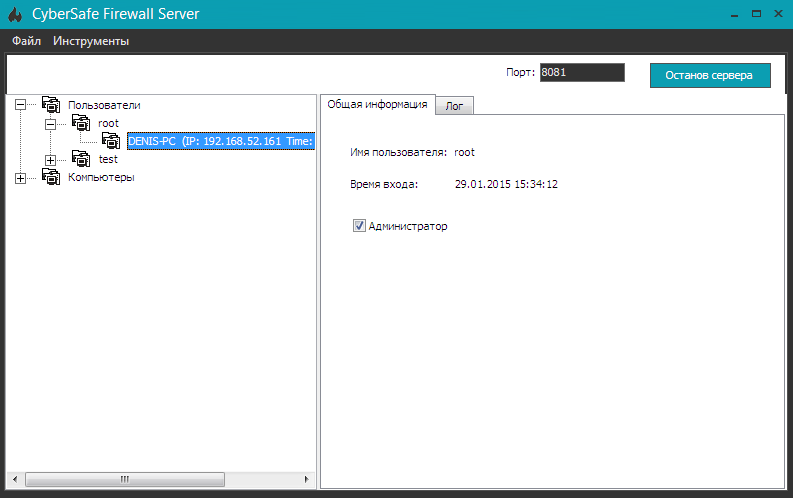
Fig. 11. Appointment of the user as an administrator.
Now we proceed to solve our problem. Let me remind you that we need to prohibit access to the Internet and other computers of the network to computers of ISTD Atlant computers.
Enter the Cybersafe Firewall program and select the menu command Firewall, Administration Panel .
Create different groups of computers that will correspond to the departments on the network (see Fig. 1). To create a group, right-click on the workspace and select the Add Group command.. And to add a computer to a group, simply drag its icon onto the group icon. The final result is shown in Fig. 12. Be sure to click the Apply button so that the program “remembers” the created groups.
It should be noted that when changing the IP addresses of the computers included in the group, the composition of the created group will not change. Therefore, do not worry about the composition of the group if you use a DHCP server in your organization.
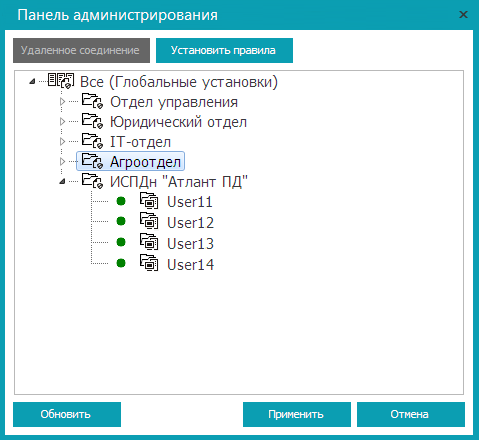
Fig. 12. Created groups
Highlight ISPD “Atlant PD” and click the Set rules button . So you can set group rules. To set global rules, select the All node and click the Set Rules button .
So, we will establish the rules for the ISPDn group “Atlant PD” . In the window that appears, go to the Security Rules section and click the Add button (Fig. 13).

Fig. 13. Security rules: not yet set.
On the General tab (Fig. 14), specify the rule description - "Prohibition of data exchange with the group <Group name>".
Set the rule type - Deny packets , select the direction of packets - For all packets and protocol - Any .
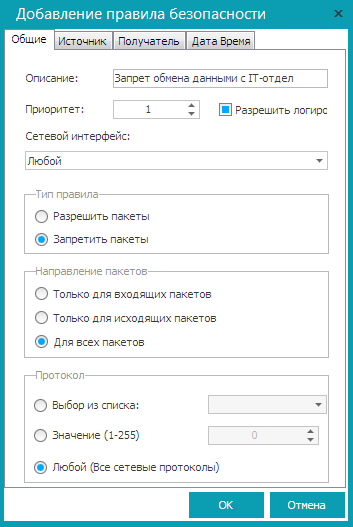
Fig. 14. General tab.
As a source, specify ISPD “Atlant PD”, and as a recipient - one of the groups in your enterprise, for example, an IT department. Click OK .
What does this rule do? It prohibits ISTD computers “Atlant PD” from transferring any packets to the IT department group. Even if some computer from the IT department group tries to establish a connection with the computer of ISPDn group “Atlant PD” , then the computers of the ISPDn group “Atlant PD” will still not be able to answer him, because the rule forbids them.
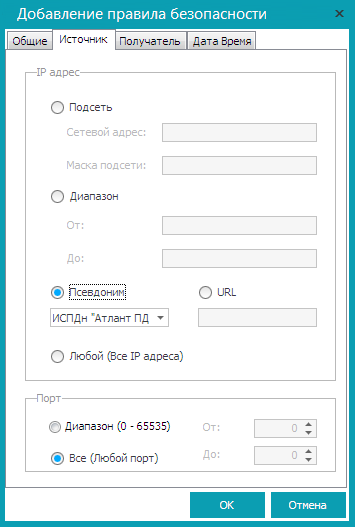
Fig. 15. Source tab

Fig. 16. Recipient tab
Repeat the procedure for the remaining groups on your network. You should get the set of rules shown in fig. 17.

Fig. 17. The created rules for the ISPDn group “Atlant PD” It
remains to prohibit access to the Internet. To do this, it is enough to prohibit any data exchange with the gateway. To do this, create another security rule for ISPD “Atlant PD”. On the General tab, set the parameters as follows:
On the Source tab, select “Atlant PD” as the source of ISPD (Fig. 15). On the Recipient tab, set the server IP address (internal), for example, 192.168.1.1 (Fig. 18).
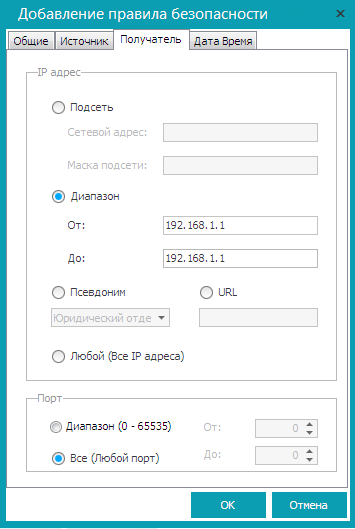
Fig. 18. Deny access to the Internet.
Click OK . By default, all rules are disabled. To enable them, right-click on each rule and select the Enable command . The final version of the rules is shown in Fig. 19. Pay attention to the status of the rule - Enabled .
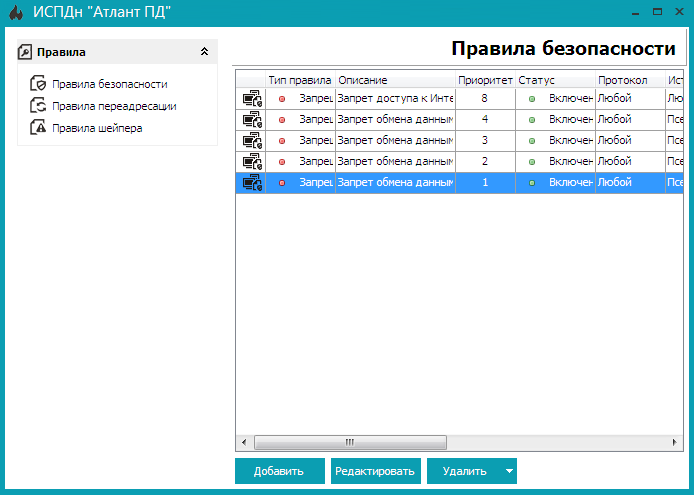
Fig. 19. Final version of the rules
Close the window for editing security rules, and in the Administration Panel window clickApply , and then close the window itself.
The problem has been solved and now the computers of the ISTD group “Atlant PD” cannot interact with other computers on the local network and they do not have access to the Internet. By means of the Cybersafe Firewall programs, the personal data information system was completely isolated from the rest of the network.
CyberSoft LLC
Cybersafe Firewall Program
Order of the FSTEC of Russia No. 21
State Register of Certified Information Security Means

Requirements for the protection of personal data information systems
ISPDn (Personal Data Information System) - an information system that is a combination of personal data contained in the database, as well as information technology and technical means that allow the processing of such personal data using automation tools or without using such tools.
According to the order of the FSTEC of Russia No. 21 dated February 18, 2013, in order to ensure 3 levels of protection of personal data, the following are applied (paragraph 12b):
firewalls of at least class 3 in case of relevance of type 2 threats or interaction of an information system with information and telecommunication networks of international information exchange and firewalls of at least 4 classes in case of relevance of type 3 threats and lack of interaction of an information system with information and telecommunication networks of international information exchange;
This article will discuss the practical use of the Cybersafe Firewall program , which is currently certified at the 4th security level, but will be certified at the 3rd level within a month (the certificate is already signed by the FSTEC). The corresponding certificate can be found on the CyberSoft website. A link to the state register of certified software will be given at the end of the article.
Formulation of the problem
The structure of the company in which we recently implemented the Cybersafe Firewall program is shown in Fig. 1.
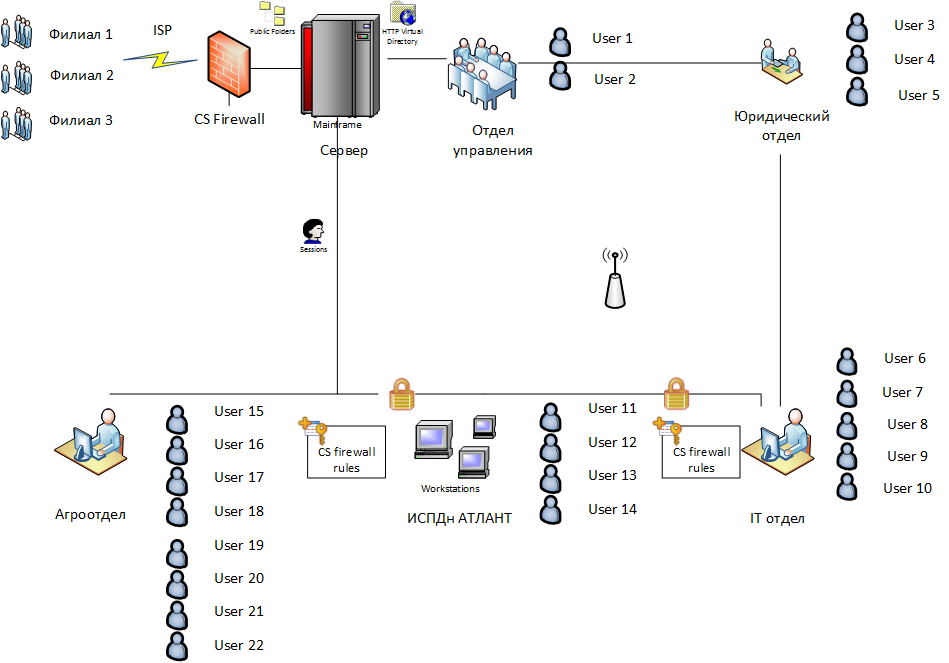
Fig. 1. Structure of the company
The company under consideration contains five departments (Agro Department, IT department, legal department, management department, ISPD Atlant PD) and three branches. Communication with remote branches is via the Internet. On the gateway, as on other computers on the network, the Cybersafe Firewall program is installed.
Later in this article, you will see how to deploy the Cybersafe Firewall program to all computers on the network using Active Directory, as well as configure group rules.
Our task is to protect the ISPD group from the outside world (that is, close its Internet access) and from the rest of the local network. Thus, computers in ISPDn will be able to "communicate" only with each other. It is worth noting that this product was specifically created for the fastest possible solution to tasks to restrict access to PC groups. In other products, solving the task takes much more time or is impossible at all (if the system of dynamic distribution of network addresses is used). If you do not take into account the time required to deploy the program using Active Directory, you can limit the access of one group of computers to another in a matter of minutes.
This scheme does not claim to originality or novelty. The task was to make the product as convenient as possible for distinguishing between several IPs or to limit one IP with confidential information from other sectors of the local network and the Internet in strict accordance with the legislation of the Russian Federation.
Create Transformation File
The first step is to create a transformation file (MST file) so that you can deploy the Cybersafe Firewall to all computers on the network with the same settings. After that, you don’t have to manually configure the firewall, for example, create a user to enter the program, specify the IP address of the remote server, its port, etc.
Install the program on a computer that will be used as a remote Cybersafe firewall server, and which you will use to manage the firewalls of the entire network. You can install the program on your own computer, or you can install the program directly on the gateway, which will provide other computers access to the Internet.
Complete the following steps to create a deployment script:
- Open the Cybersafe Remote Server program (included in the Cybersafe Firewall software package).
- Select the menu command Tools, Installation script file .
- Fill in the parameters that will be entered in the deployment scenario, namely the port on which the firewall will work (usually 50001), the remote server port, the remote server IP address, activation key, administrator e-mail, default user and password (Fig. 2).
- Click the Save Script button .
- In the file save window, select the script format - for deployment using Active Directory you need to select the * .mst format (Fig. 3)
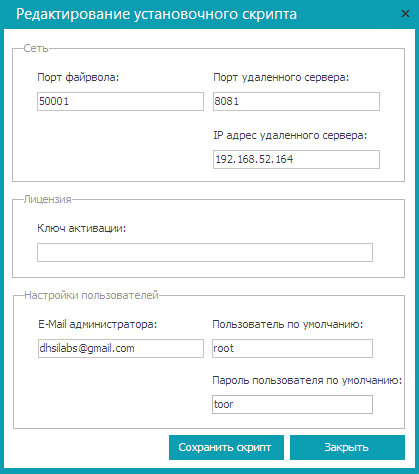
Fig. 2. Creating a deployment scenario
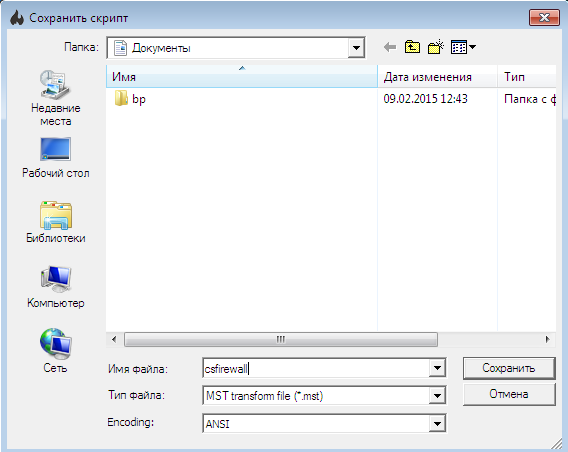
Fig. 3. Saving the deployment scenario The
Cybersafe Remote Server program is described in detail in the Cybersafe Firewall program guide (http://cybersafesoft.com/eng/products/cybersafe-firewall/).
If your organization does not use Active Directory, then using the Cybersafe Remote Server program, you can create a batch file (* .bat). To deploy the program on all computers on the network, it will be enough to copy it to each computer along with the program installer (MSI file) and run it (batch file). If for each computer unique users are needed, then you can manually run the program installer (MSI file) on each computer, while you do not need either a transformation file or a batch file.
Deploying Cybersafe Firewall with Active Directory
Now let's look at the process of deploying a Cybersafe Firewall program using ActiveDirectory. All illustrations for this section were created in Microsoft Windows Server 2012 R2, but all of the instructions given will work in older versions (Microsoft Windows Server 2003/2008), illustrations may slightly differ.
The first step is to create a folder for the software deployment. It will contain all the MSI packages that you need to deploy (you do not need to create a separate folder for the Cybersafe Firewall program).
Let it be the C: \ Install folder. In this folder, create a subfolder of CSFirewall. You need to place the csfirewall.msi installation file and the csfirewall.mst transformation file that you created in the previous section in it.
The C: \ Install folder must be shared. To do this, right-click on the folder and select the Properties command . On the Access tab, click the Sharing button and provide read and write access to the administrator and read-only access to all other network users.
Next, run the gpmc.msc Group Policy Editor. We assume that the Cybersafe Firewall program needs to be installed on all computers on the network. Therefore, right-click on the domain and select Create a GPO in this domain and link it (Fig. 4).
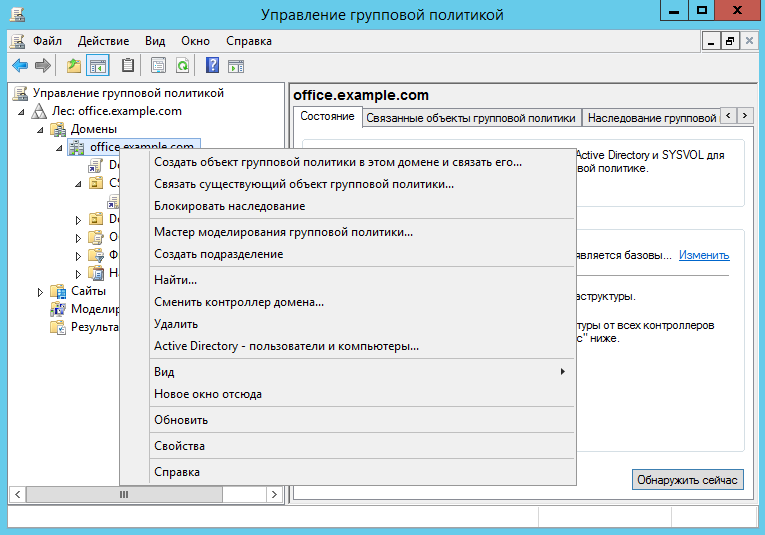
Fig. 4. Group Policy Editor.
Name the new GPO CS_Firewall (Figure 5). In chapterSecurity filters, delete the Authenticated Users group and add the computers, groups and users to whom the settings of this GPO will be applied (Fig. 6). In other words, add the computers on which the program should be installed.
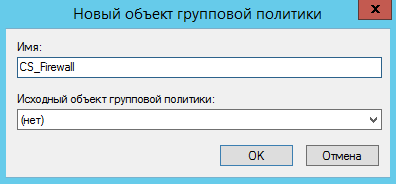
Fig. 5. Creating a new GPO

. 6. Created GPO Object
Right-click on the newly created GPO (CS Firewall) and select the Modify command . Go to the section User Configuration, Policies, Application Configuration, Installing Programs (Fig. 7).
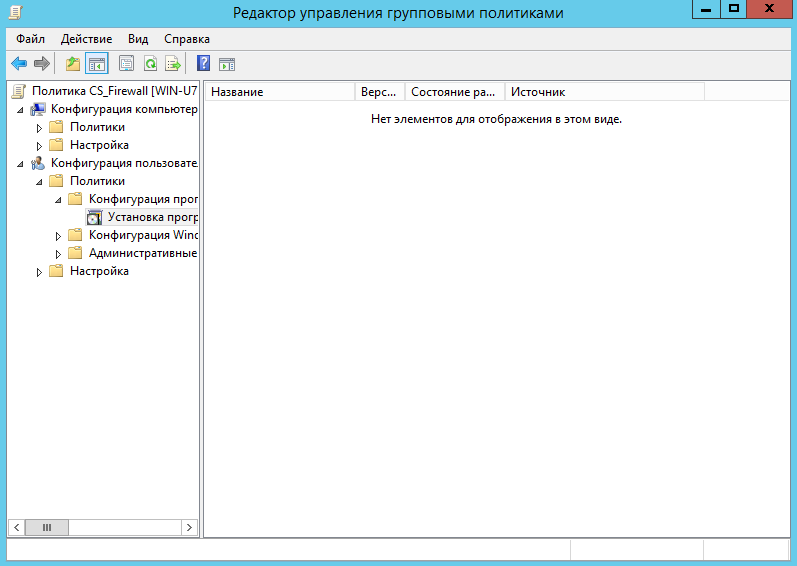
Fig. 7. Section User Configuration, Policies, Software Configuration, Installing Programs.
Right-click on the section.Install programs and select Create, Package . In the window that appears, you need to select the path to the MSI file of the program. Please note that you need to enter not a local path, but a network path, since users will access the package over the network.
The next step is to choose a deployment method. Since we want to provide a transformation file (.mst file created by the Cybersafe Remote Server program), we need to select a special deployment method (Fig. 8). This will open the deployment package configuration window (Figure 9). Then go to the Modifications tab , click the Add button and select the transformation file (.mst file), Fig. 10.

Fig. 8. Choosing a deployment method
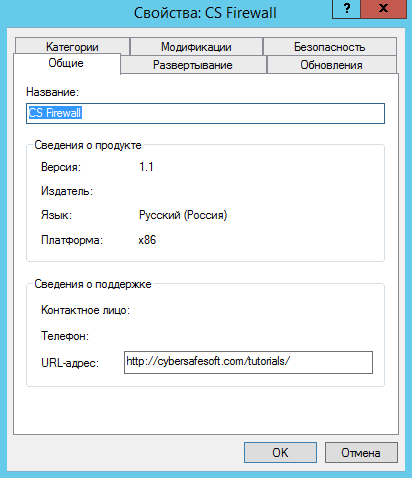
Fig. 9. Set up the deployment package

Fig. 10. Specify the transformation file.
Click OK .
Note . After clicking OK, the package and the transformation file (.msi and .mst files, respectively) will be cached. If you need to change the transformation file after creating the package, you will have to create the deployment package again.
This completes the work with the Group Policy Editor. Close all windows, open a command prompt (or at least Run , by pressing Win + R) and enter the command:
gpupdate /force
That's all. The program will be automatically installed on computers after they are rebooted and before the login window is displayed. The user cannot influence anything and cannot be mistaken in anything.
Sometimes the program does not install automatically. Most often, this problem is observed on workstations running Windows XP. To install it, you must manually enter the gpupdate / force command on it.
Configure Firewall Rules
Using the Cybersafe admin panel firewall, you can set global and group rules for all Cybersafe firewalls installed on your network. Global rules apply to all computers on which the Cybersafe firewall is installed, and group rules determine the behavior of the Cybersafe firewall installed on a specific group of computers.
Before setting up global and group rules, you need to designate the user as an administrator. This can only be done using the Cybersafe Remote Server program.
An administrator can use the administration panel to manage a remote firewall. So, in the Cybersafe Remote Server program, expand the Users nodeand select the user you want to make an administrator and enable the Administrator switch (Fig. 11).
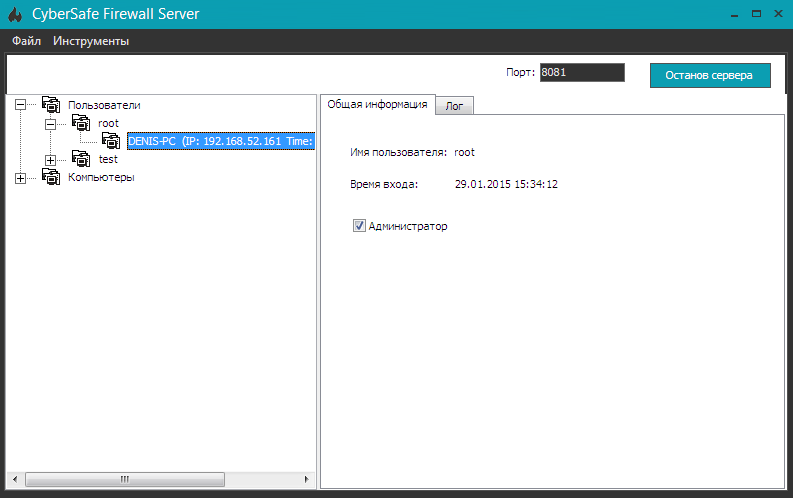
Fig. 11. Appointment of the user as an administrator.
Now we proceed to solve our problem. Let me remind you that we need to prohibit access to the Internet and other computers of the network to computers of ISTD Atlant computers.
Enter the Cybersafe Firewall program and select the menu command Firewall, Administration Panel .
Create different groups of computers that will correspond to the departments on the network (see Fig. 1). To create a group, right-click on the workspace and select the Add Group command.. And to add a computer to a group, simply drag its icon onto the group icon. The final result is shown in Fig. 12. Be sure to click the Apply button so that the program “remembers” the created groups.
It should be noted that when changing the IP addresses of the computers included in the group, the composition of the created group will not change. Therefore, do not worry about the composition of the group if you use a DHCP server in your organization.
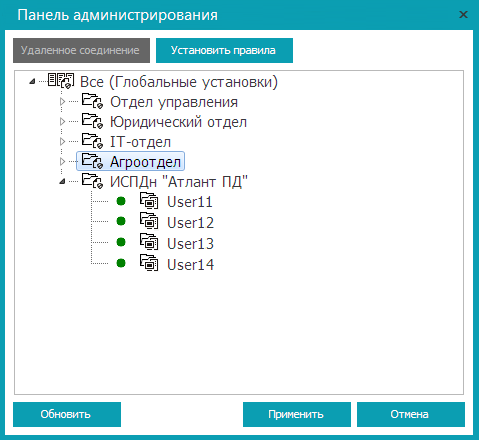
Fig. 12. Created groups
Highlight ISPD “Atlant PD” and click the Set rules button . So you can set group rules. To set global rules, select the All node and click the Set Rules button .
So, we will establish the rules for the ISPDn group “Atlant PD” . In the window that appears, go to the Security Rules section and click the Add button (Fig. 13).

Fig. 13. Security rules: not yet set.
On the General tab (Fig. 14), specify the rule description - "Prohibition of data exchange with the group <Group name>".
Set the rule type - Deny packets , select the direction of packets - For all packets and protocol - Any .
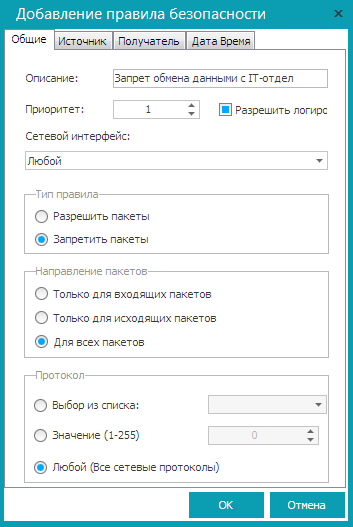
Fig. 14. General tab.
As a source, specify ISPD “Atlant PD”, and as a recipient - one of the groups in your enterprise, for example, an IT department. Click OK .
What does this rule do? It prohibits ISTD computers “Atlant PD” from transferring any packets to the IT department group. Even if some computer from the IT department group tries to establish a connection with the computer of ISPDn group “Atlant PD” , then the computers of the ISPDn group “Atlant PD” will still not be able to answer him, because the rule forbids them.
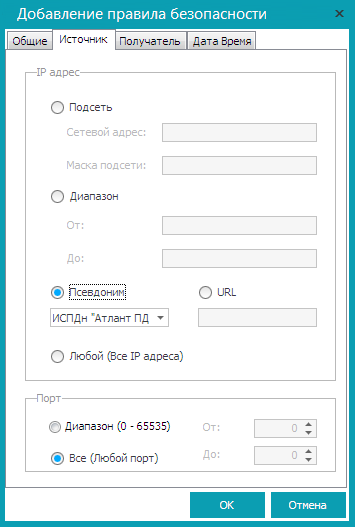
Fig. 15. Source tab

Fig. 16. Recipient tab
Repeat the procedure for the remaining groups on your network. You should get the set of rules shown in fig. 17.

Fig. 17. The created rules for the ISPDn group “Atlant PD” It
remains to prohibit access to the Internet. To do this, it is enough to prohibit any data exchange with the gateway. To do this, create another security rule for ISPD “Atlant PD”. On the General tab, set the parameters as follows:
- Description - Deny access to the Internet
- Rule Type - Deny Packets
- Packet Direction - For all packages
- Protocol - Any
On the Source tab, select “Atlant PD” as the source of ISPD (Fig. 15). On the Recipient tab, set the server IP address (internal), for example, 192.168.1.1 (Fig. 18).
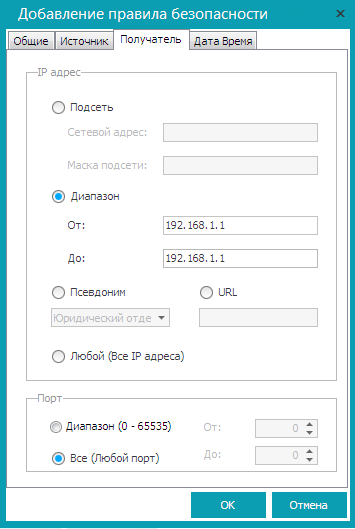
Fig. 18. Deny access to the Internet.
Click OK . By default, all rules are disabled. To enable them, right-click on each rule and select the Enable command . The final version of the rules is shown in Fig. 19. Pay attention to the status of the rule - Enabled .
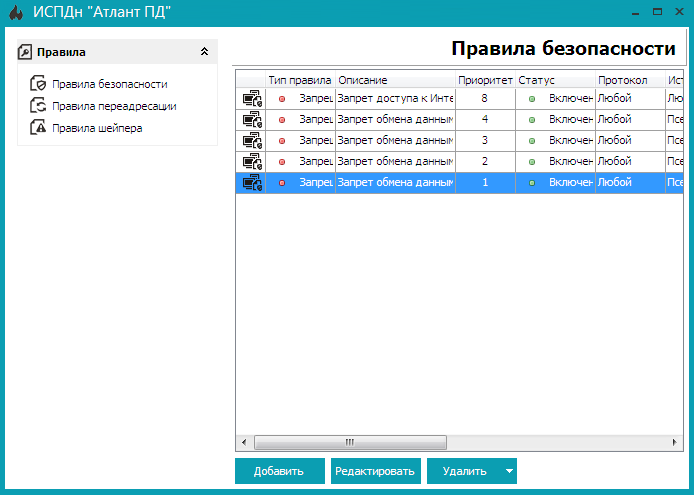
Fig. 19. Final version of the rules
Close the window for editing security rules, and in the Administration Panel window clickApply , and then close the window itself.
Conclusion
The problem has been solved and now the computers of the ISTD group “Atlant PD” cannot interact with other computers on the local network and they do not have access to the Internet. By means of the Cybersafe Firewall programs, the personal data information system was completely isolated from the rest of the network.
References
CyberSoft LLC
Cybersafe Firewall Program
Order of the FSTEC of Russia No. 21
State Register of Certified Information Security Means
