News from the 31C3 forum: new intrigues of the NSA, computer control of the brain and the Internet of toilets
On December 27, one of the world's largest hacker conferences, the Chaos Communications Congress (31C3), opened in Hamburg. The annual congress gathers a huge number of engineers, makers, political activists, artists and hackers in the broad sense of the word. More than 12,000 participants came to the 31st Congress to witness some very interesting events.
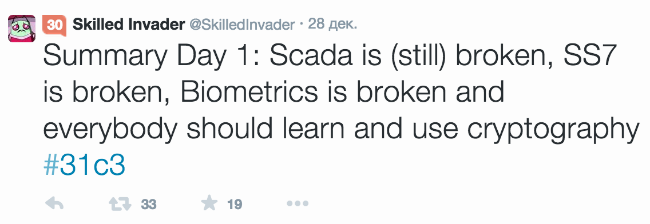
This year, the atmosphere at the event can hardly be called peaceful. It can best be characterized by a quote from a tweet : "SCADA is still broken, SS7 is hacked, biometrics are hacked, and everyone needs to learn cryptography."
The keynote speaker was Alec Empire, a member of the popular techno-hardcore band Atari Teenage Riot, who noted that there was much in common between techno world, art, hacking, and called onrepresentatives of these "oceans" to friendship and exchange of ideas.
Following the main report, Positive Technologies experts Sergey Gordeychik and Alexander Timorin spoke. They showed how to break into solar and wind energy systems that generate 8 GW of electricity, which is comparable to the fifth largest power plant in the world of hydroelectric power stations.
Readers of our blog are already partially familiar with the problems of smart grids from this article . The number of SmartGrid devices connected to the Internet without any protection is growing like an avalanche. In the world there are dozens of platforms, hundreds of vendors and millions of end devices.

After the presentation, Positive Technologies experts from the SCADA StrangeLove group received a lot of questions about such vulnerabilities.
This prompted them to organize a non-profit SCADASOS initiative to raise awareness in this area, encouraging volunteers to search for Internet-connected solar and windmills using Shodan or Google Dorks., and then report similar facts to manufacturers, to the local CERT or the IB community. “And do not try to break anything. It could be your grandmother’s hospital or cottage, ”the group said in a statement.
Next, we list the most memorable performances.
An excellent report was presented by Sylvain Munot, familiar with PHDays 2012 and the osmocombb project. The Frenchman spoke about the satellite communications standard GMR-1 (GEO Mobile Radio), which he traditionally hacked.
This was followed by a series of studies on the interception and surveillance of users of mobile network operators and vulnerabilities of the SS7 protocol. Our readers should remember publications on this subject (about NSA surveillance , wiretapping of Ukrainian mobile phones , etc.).
Tobias Engel: SS7: Locate. Track Manipulate
SS7map: mapping vulnerability of the international mobile roaming infrastructure
Karsten Nohl: Mobile self-defense
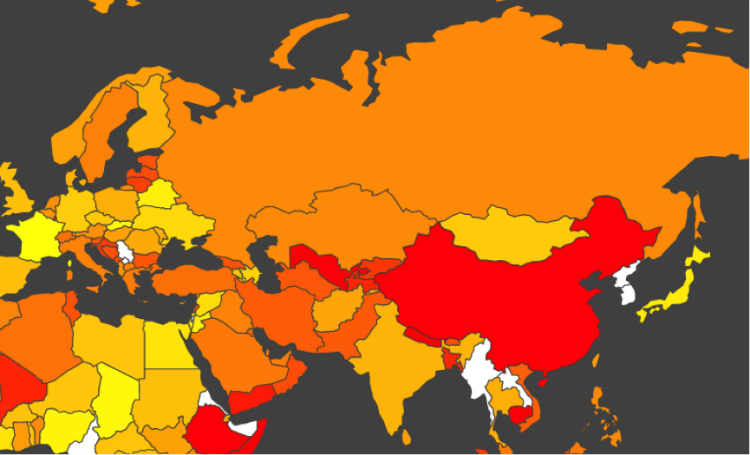
By the way, Carsten Nole (who was at PHDays IV) introduced the SnoopSnitch utility , which detects attacks using the baseband debugging features. I also liked the ss7map project .
In Hamburg, a lot of words were said about encryption in 3G / 4G, which, as it turned out in practice, is not better than in 2G, since many providers use the insecure stream algorithm A5 / 1, and even if they use A5 / 3, in some cases along with too short 64-bit keys on SIM cards. A lot has also been said about the disadvantages of SIM card encryption .
The second day was calmer
It is worth highlighting Iridium Pager Hacking about wiretapping satellite pagers - an excellent example, on the one hand, reverse engineering in the broadest sense of the word, and on the other, carelessness based on security by obscurity.
For those who want to immerse themselves in the topic of glitching, you should watch this performance (the same topic was touched on PHDays III).
Well, just a star of Congress - a review about the Internet of toilets. Technically empty, but the execution and sensitive theme did not leave anyone indifferent. Some participants are sure that this report was to become a “keynote" at the conference.
And then a terrible thing happened, the NSA broke everything again !

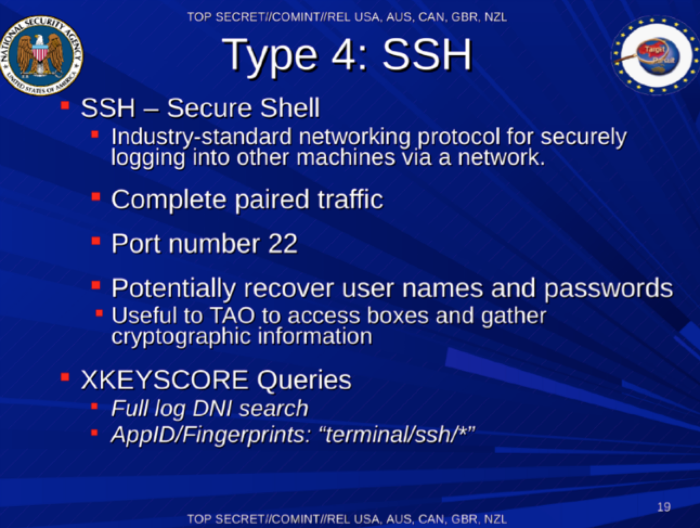
Jacob Appelbaum, a researcher and one of the main documentary filmmakers of Edward Snowden, stated that the NSA had methods for decrypting PPTP, IPSEC, SSL, SSH traffic. Among the priority goals for hacking, the documents of the American intelligence agency noted Zoho, the anonymous Tor network, an application for encrypting files Truecrypt and the Russian service Mail.Ru.
The third day
The final third of the conference started with a speech by Richard Matthew Stallman, who spoke about freedom in general and free software in particular (something like this ).

Many, however, wanted to quickly see X-ray scanners, where a number of interesting pictures were expected.
What else would I like to note on the 31C3? Impressive hacking by Apple, a wonderful report by Advanced binary tricks , attempts to put a computer in your ear and control the brain . In addition, Marina Krotofil touched upon the unusual topic of “hacking” a chemical process (rather than the system that controls this process), and Positive Technologies experts spoke a bit about USB modems during Lighting Talks .
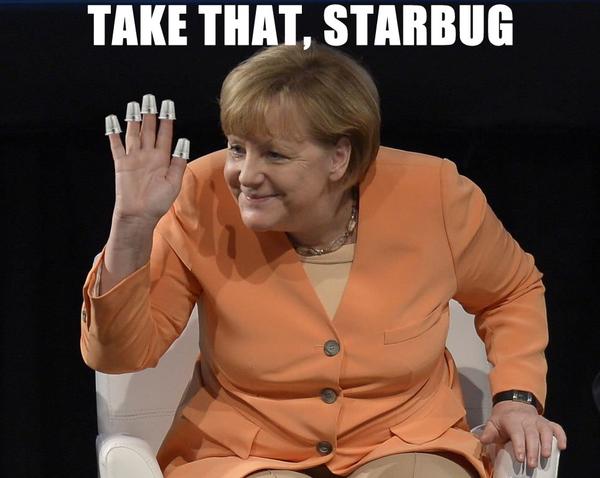
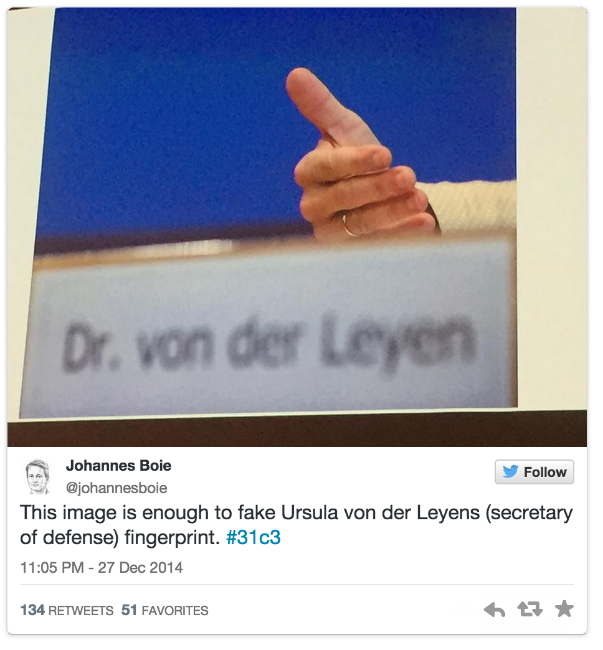
The conference in Hamburg left a distinct feeling that in our world it will not become calmer in the near future. A simple guy live remotely receives the biometric data of Angela Merkel, everyone is watching each other, and even a certain Mutti, whoever he is,watching us.