How dangerous is an open recursive DNS server?
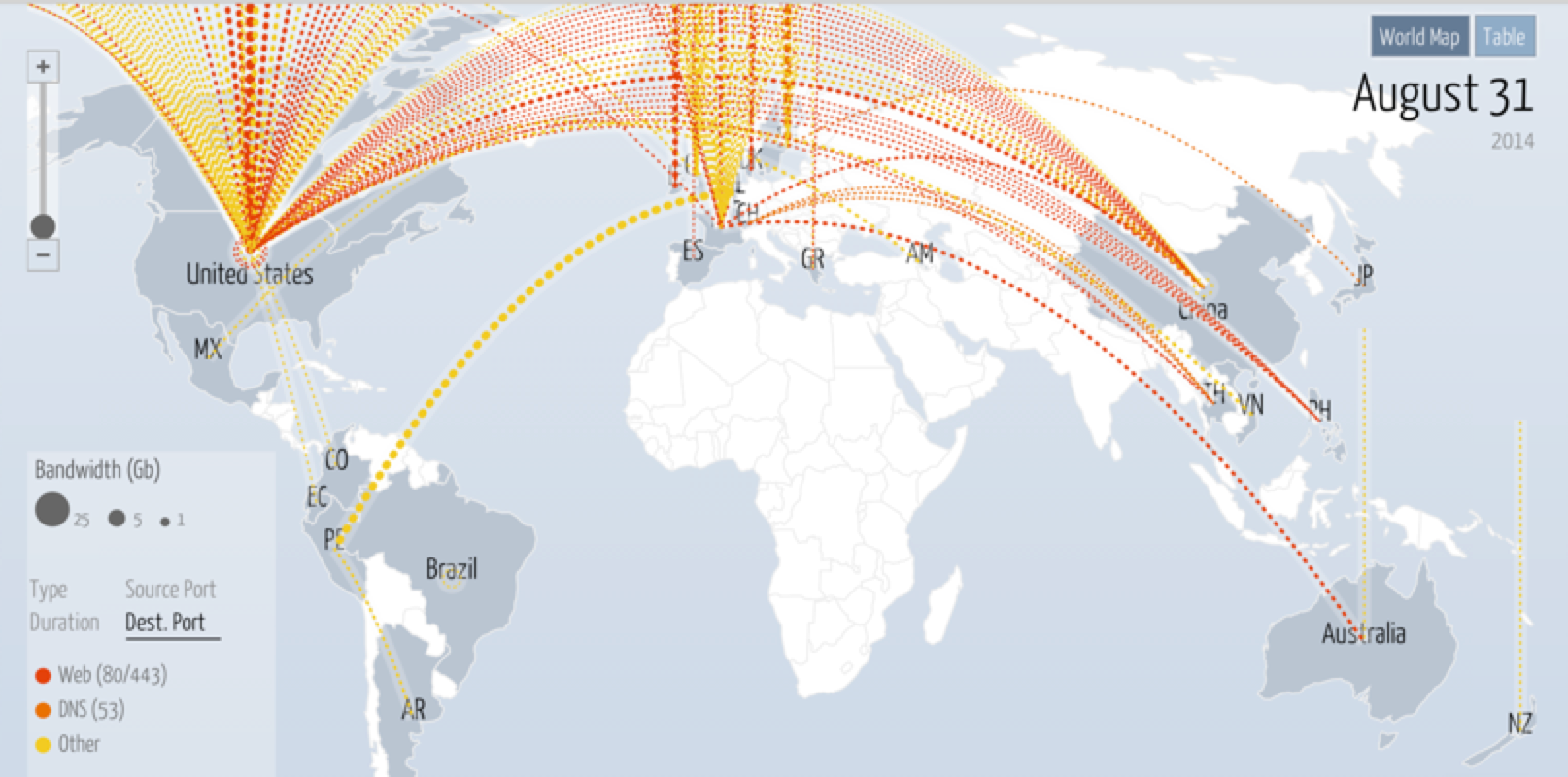
It is indisputable that “putting a server” on the Internet, you need to take care of its security and limit access to it as much as possible. The DNS protocol can be used both for attacks on the victim’s infrastructure (DNS server, channel) and for attacks on other companies. Over the past year, the number of such attacks has increased at least 2 times. At digitalattackmap.com , which visualizes DDoS attacks, DNS is highlighted on a par with attacks on the Web (80/443).
The DNS service works (mainly) over the UDP protocol, which does not imply a preliminary connection, so it can be used without problems for attacks on other servers (spoofing) without special preparation. According to information from various sources 1.2Currently, between 8 and 20 million DNS servers respond to recursive queries. These can be either incorrectly configured authoritative and caching DNS servers, or simple CPEs.
I was interested in how dangerous it is (for myself and others) to keep an open recursive DNS server, so I decided to do a little research.
Formulation of the problem
The following questions were formulated, to which I would like to receive answers:
- How quickly an open recursive DNS server will be detected;
- When will they start using the server for illegal purposes;
- Determine the load on the server (the number of requests per second);
- Try to determine which organizations are targeted;
- Whether compromised (blacklisted) domains and / or IP addresses will be requested.
For testing, the server installed in the Nuremberg Hetzner data center is used. An authoritative DNS server was previously located on this server, the number of queries to which did not exceed 200 per day. The server IP address (due to moving to a new joint-stock company) changed in July. To check the domains, the RPZ (response policy zone) mechanism and the black list from Infoblox were used .
Bit of theory
The following principles are used to carry out attacks through the DNS server:
- DNS works over UDP, so an attacker can change his IP address to the victim's address;
- DNS queries are asymmetric, response traffic can exceed incoming several times.
Based on these principles, we can distinguish the following types of attacks using DNS:
- Amplification attack (attack with gain) - is aimed at overloading the outgoing channel of the DNS server. It starts with sending a large number of DNS queries, specially selected in such a way as to get a very large response, the size of which can be up to 70 times the size of the query, which will lead to an overload of the outgoing channel of the DNS server and ultimately to denial of service (DoS );
- Reflection attack (attack with reflection) - third-party DNS servers (for example mine) are used to spread DoS or DDoS attacks by sending a large number of requests. In such an attack, the address from which DNS queries are sent is replaced by the IP address of the victim, and the request will have the data of the victim's server, and not the attacker. As a result, when the name server receives requests, it will send all responses to the victim's IP address. A large amount of such “reflected” traffic can disable the victim’s server / network;
- Distributed reflection DoS (DrDoS) - combines reflection and amplification attacks, which significantly increases the likelihood of disruption to the victim's server. At the same time, DNSSEC, designed specifically to protect DNS responses and prevent cache poisoning, can make this type of attack even more effective as the size of DNS messages increases. Amplification can reach up to 100 times, and attackers can use botnet networks - which can include thousands of computers.
The listed list of possible attacks is not complete, but it is sufficient for this study.
Research results
During the week, a total of 416 thousand requests were received for 63 domains from 1169 clients, which indicates the success of the study and the importance of this topic.
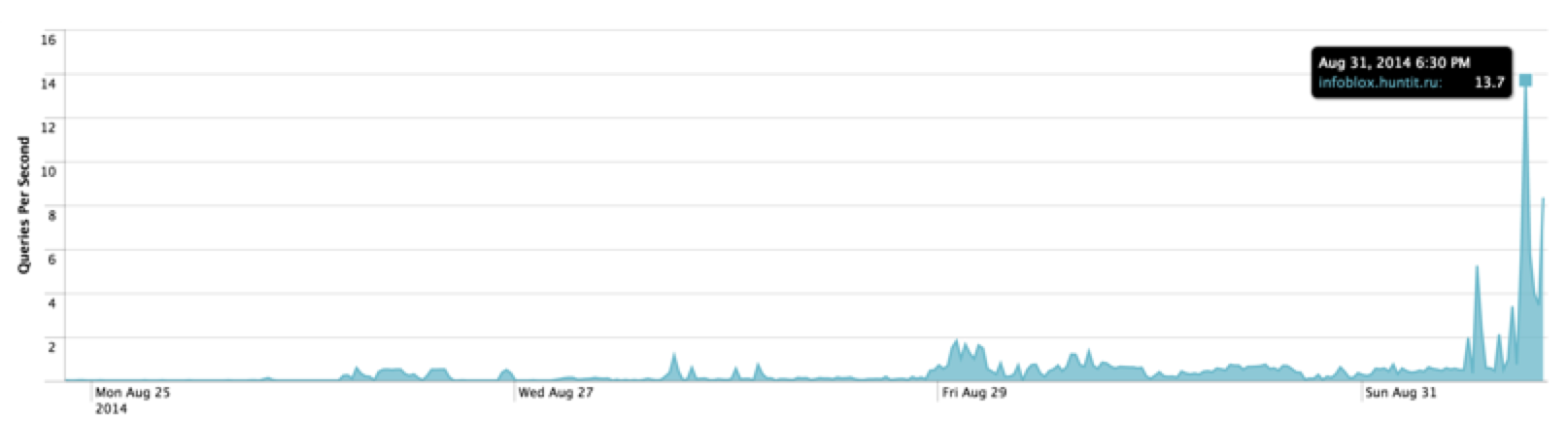
Below is a graph of the number of queries to the DNS server per second.
First of all, we will answer the questions posed:
- How quickly an open recursive DNS server will be detected;
The first request came from China after 1 hour 20 minutes to the domain www.google.it - When will they start using the server for illegal purposes;
After 1 day (the first small surge in the chart), the server began to be used periodically for attacks. In 30 minutes, 300 requests to the webpanel.sk domain were received. Gradually, the number of requests and the duration of attacks increased. - Determine the load on the server (the number of requests per second);
At the time of the attack, the server experienced a maximum load of 2-4 requests per second. On the last day of testing, the number of requests increased sharply to 20 requests per second. The DNS Amplification attack was used, whether it was combined with DNS Reflection is difficult to determine. - Trying to determine which organizations targeted the attacks: The

number of domains requested was small, so it was easy to identify potential victims and the domains used exclusively for attacks.
- The US Department of Labor, domain doleta.gov , uses DNSSEC, the server response is about 4 KB, 127 thousand requests. The distribution of the number of requests by customers is fairly even, TOP10 are located in different countries around the world (South and North America, Australia and New Zealand, Europe);
- The company in Slovakia, the webpanel.sk domain , uses DNSSEC, the server response is about 4 Kb - 162 thousand requests (most of the requests came on the day the article was written, the numbers are constantly increasing). dnsamplificationattacks.blogspot.rususpects that this domain is used exclusively for DNS amplification attacks. In fact, the responses from this server are no different from any other servers that use DNSSEC. A large number of requests come from German hosting servers, Russian game hosting and some customers in the USA;
- The US Environmental Protection Agency, domain energystar.gov , uses DNSSEC, the server response is about 4 KB - 79 thousand requests. In total, 69 clients requested the domain, most of which are located in the USA. 18 thousand requests were received from the Royal Empire game server. Since there are no users on the server, and the news indicates that beta has been online since 07/11/2014, we can assume that this server was hacked. IP addresses from Qwerty and Microsoft networks were noticed.
- FamiNetwork, domain famicraft.com , 7.5 million requests. The domain contained meaningless TXT “wowowow” records, as a result of which the server response reached 4kb (50x attack boost). In the process of writing the article, I found that famicraft.com server response has changed and it no longer poses a threat. Most likely, the domain owner detected a hack and made the necessary corrections. Requests came from 4 servers, two of which belong to Akamai Technologies (5 thousand requests);
- 14 Akamai Technologies servers were suspected of suspicious activity in all of the above domains, perhaps this is an attack on Akamai or their servers were hacked;
- TOP10 in terms of the number of incoming requests (30% of the total number of requests) included: German hosting (ironically providing DDoS protection), game hosting (Russian), game server, two Akamai servers. Most likely, these servers were hacked, and the rest of the clients are included in botnets. - Whether compromised domains will be requested.
Not. During the entire testing period, only one domain (ballsack.pw) was blocked at the IP address 104.28.0.111. The reason for the blocking can be viewed on the ThreatStop server ( http://threatstop.com/checkip ). In principle, this is logical, since botnet / malware attacks via an external recursive DNS server, and connecting and receiving commands from the control center occurs during initialization, and the provider uses a recursive DNS server for this.
During the analysis of the log files, the following were revealed:
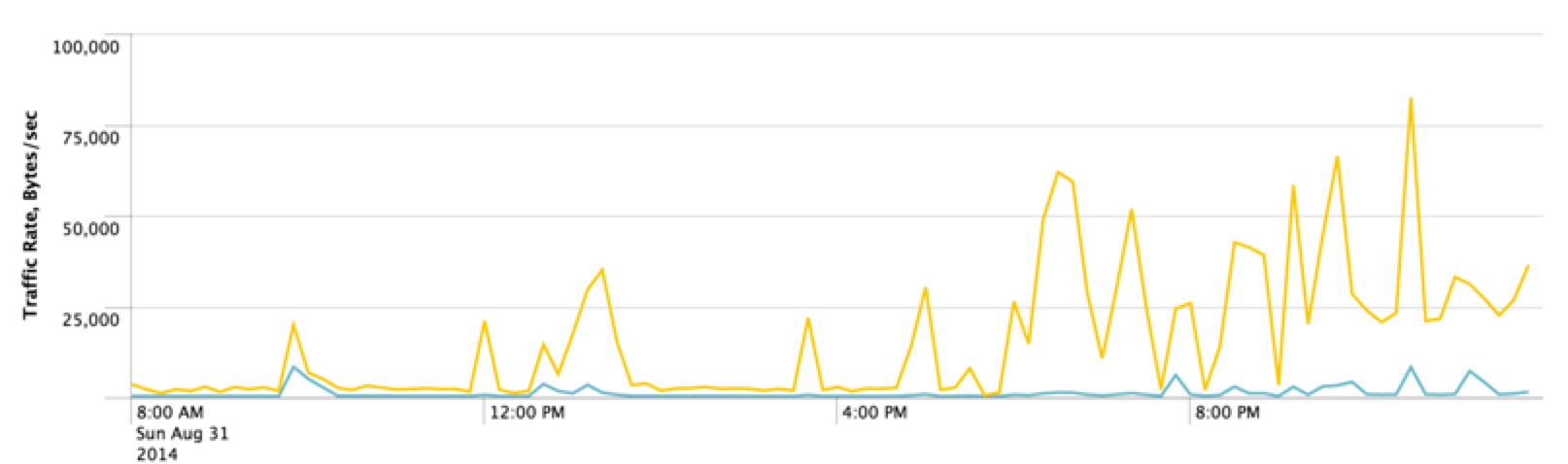
- domains that were created and / or hacked for DDoS attacks: jerusalem.netfirms.com (gives a large number of A-records) and famicraft.com (described above). The response from these DNS servers is 4 Kb, that is, when using data, you can achieve 50 times the overload of the outgoing channel (yellow on the graph);
- Organizations that actively monitor open recursive DNS servers:
- www.openresolverproject.org;
- dnsscan.shadowserver.org;
- There have been several requests for the openresolvertest.net domain, but there is no information on the website.
Open recursive DNS servers
The dnsscan.shadowserver.org service has 8 million open recursive DNS servers. Most of these systems are located in China, Russia is located in an honorable 6th place.
| Country | Total |
| China | 2,886,523 |
| United states | 662,593 |
| Korea, Republic of | 591,803 |
| Taiwan | 449,752 |
| Brazil | 339,416 |
| Russian Federation | 264,101 |
An interesting graphical representation of the distribution of DNS servers by country, both open recursive and authoritative.

conclusions
Based on the results obtained, the following obvious conclusions can be drawn:
- It is necessary to restrict access to all server resources, and in particular to a recursive DNS server;
- You must constantly monitor the load of the DNS server and data channel. A sharp increase in load can indicate both a DDoS attack and a server hack;
- When using DNSSEC, it is necessary to reasonably limit the number of incoming requests (rate limit);
- Check your CPE for access to DNS through the WAN interface;
- It makes sense for providers to restrict access from the Internet to recursive DNS server clients.
At first, I expected to complete testing in a week, but taking into account the significant increase in load (from 2 to 20 QPS) on the last day of testing, I decided to extend the study for another week.
List of sources:
(c) Vadim Pavlov
