About leaking user password database
Yesterday on Habré, in the comments to the article about the leak of the Yandex password database, information appeared that the database of password from Mail.Ru mailboxes got into the network. We have analyzed all the accounts that are in this database, and we want to talk about what it was and what measures we took.
What happened Where is the base from?
Mass hacking, having for itself a specific reason or security hole, did not happen. Analysis of the database showed that, most likely, it was collected in parts from several password databases that were stolen from users at different times and in different ways, including using viruses, phishing, etc.What gives us reason to think so?
Firstly, a rather large percentage of passwords from the database that got into the network is currently irrelevant, that is, the owners of the boxes have already managed to change them.Secondly, approximately 95% of the remaining accounts are already suspicious in our system (that is, we believe that they are either created by a robot or hacked). Such accounts are limited in sending mail, and we recommend that their owners change their password.
How it works? We have a complex system, which, starting from registration, analyzes the actions of each account according to a number of criteria (we don’t want to talk about all so as not to make it easier for attackers, but for example, one of the most obvious is an attempt to send spam from this account or a sharp one change of behavior pattern). In this system, each account has a dynamic rating (called “karma”). As soon as karma falls below a certain parameter, various sanctions will be applied to the account, including the persistent recommendation to change the password.
Thus, the owners of almost all mailboxes from the found database, the passwords for which were still relevant, have long received a notification from us that suspicious activity has been recorded from their mailbox and that they need to change the password as soon as possible. Judging by the fact that they still have not done this, the conclusion suggests itself that many of them are “auto-registrations”. Such mailboxes, as a rule, are not restored after blocking, since it is quite expensive for cybercriminals to bypass protection to change the password. Another significant part is the boxes abandoned by the owners (after all, it is difficult to actively use the account if you are not allowed to send mail, and a window asking you to change the password pops up in the mailbox all the time).
But what about the remaining 5%?
During yesterday, the owners of these boxes have already received a notification about the need to change the password.And yet, how did the boxes get stolen?
The most common ways to crack mailboxes are phishing, viruses on user computers, and passwords that are too simple. Another very common situation: users are too lazy to come up with unique passwords for each of their accounts and use a password from mail on forums, torrent trackers or some other resources with a low level of protection, which are then attacked. As a result, attackers gain access to a whole database of passwords, and then pick them up to other services, first of all, to mailboxes, which are often indicated as a login or communication method.We strongly recommend having a separate and very strong password on your mail account, as many other services are tied to it.
And what do we do to protect our users?
We really do a lot to prevent theft of boxes.Firstly, we ruled out the possibility of a MITM attack, because the transfer of user data both in the web interface, in our mobile applications, and in POP / IMAP / SMTP in Mail.Ru Mail takes place via HTTPS / TLS / STARTTLS. Moreover, in the web interface, HTTPS always works by default, using the Strict Transport Security (STS) technology, which makes the browser always access Mail.Ru Mail immediately via HTTPS.
By the way, unlike Yandex, our main page also always works via HTTPS and is protected via STS, which makes it impossible to steal a password through an SSL Strip attack.
It is also impossible to intercept the password from Mail.Ru through the MITM attack of the IMAP service, because our IMAP service always and everywhere works only on TLS / STARTTLS. This is important, since it is the IMAP service that is most susceptible to this attack, since it is often used on mobile applications, and it is most convenient to listen to traffic from Wi-Fi networks. In addition, some mail services neglect such protection, and attackers know about it.
I would also like to note that the leak of such data from the inside of the company is practically excluded. Access to production servers and databases is strictly regulated. In addition, the passwords of Mail.Ru users are stored in an encrypted and "salty" form (that is, additional data is mixed with passwords during encryption). This means that even the theft of the password database does not allow the possibility of its decryption. But theft itself is impossible thanks to a multi-level security system.
so
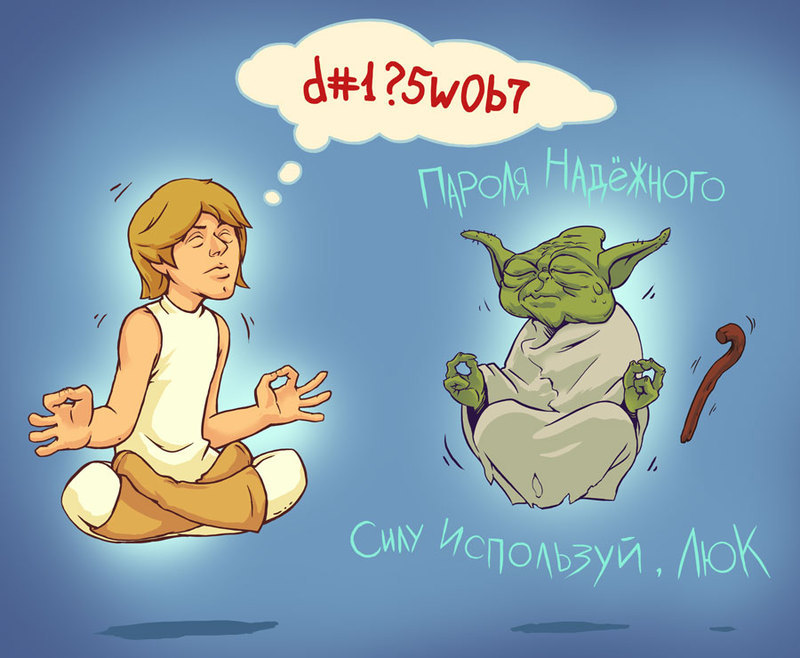
We are trying very hard to protect our users. Only in the last year or two we have implemented a number of large security features, for example, forced HTTPS in Mail and on the portal’s main page, content security policy, separation of sessions on the portal and much more. Launched the Bug Bounty program .Unfortunately, all our efforts will be in vain if the user does not do his part of protecting the mailbox. We, like many other Internet services, constantly talk about this to users, including on Habré, where we had a very detailed posthow hacked boxes are and what needs to be done to protect your data. We won’t talk about them in detail now, just the main ones: the password for the Mail should be a) complex, b) unique, and c) it is desirable to change it regularly (ideally - at least once every three months).
