Researchers from Princeton discovered a "shadow" user identification tool in the AddThis plugin
Recently, several publications appeared on the Web at once , the theme of which is a hidden way of identifying users by visited sites. This method (called “canvas fingerprint”) is very difficult, if at all possible, to block using standard methods, such as blocking cookies or installing AddBlock or similar plugins.
Moreover, such a method of identification has already been found on 5% of the most popular sites in the world, including WhiteHouse.gov and YouPorn.com. The method itself is quite understandable: when entering a website with the user tracking code installed, such a resource requests the user's browser to draw a hidden image, and text is drawn using fonts and a renderer available to the system. The font set and anti-aliasing methods are slightly different on different machines. The renderer depends on the browser version, OS, and even the GPU ( thanks to Goodkat for the addition ). As a result, the rendered image is unique.
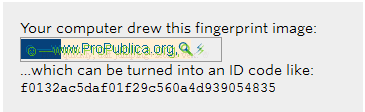 The rendered image can be used as a “fingerprint”, with a unique identifier assigned to the device. Well, and then, as they say, it’s a matter of technology - tracking a PC with an assigned identifier and the actions of the owner of this PC on the Web is not difficult. At the same time, as mentioned above, using standard methods to block such an identification method is almost impossible.
The rendered image can be used as a “fingerprint”, with a unique identifier assigned to the device. Well, and then, as they say, it’s a matter of technology - tracking a PC with an assigned identifier and the actions of the owner of this PC on the Web is not difficult. At the same time, as mentioned above, using standard methods to block such an identification method is almost impossible. Researchers found that the code with the identifier was used on sites that collaborated with AddThis . As it turned out, such a code is installed on 5% of 100 thousand top sites. Most of the “infected” sites used AddThis tools for social interaction, a set of plug-ins, where a section was built with instructions for the browser to render the image.
All this is not something very new, similar methods of user identification were announced back in 2012, researchers from the University of California.
In June, the Tor Project developers even added a function to notify the user that a site is trying to use the described authentication method in their browser . At the moment, no other browser company has offered a similar tool.
By the way, a year earlier, Russian developer Valentin Vasiliev posted his code on the Web with a similar method of user identification. According to Vasiliev, the accuracy of identification using the rendering of a latent image is about 90%. According to Vasiliev, “Drawing a special image is only the first part. The main thing is the conversion of PNG to binary form, and then to base64. The GPU is almost always responsible for this in modern browsers. Here is the difference in GPUs and the implementation of PNG decoding and produces different base64 lines in the output. Canvas fingerprinting is just one of many sources that adds a few bytes to entropy. The main part is plugins and browser capabilities. The total footprint is built using all the features. "
At the same time, mobile devices are not compatible with this method.
Representatives of AddThis, as far as I can tell, finalized Vasiliev’s project, and decided to try out their own code by posting it in their social plugin. According to company representatives, all this was used not by malicious intent, but as a study of the possibility of replacing cookies with something else. And the sites hosting the AddThis code were not notified of the presence of a site with an identification tool so that the test results “in the field” were as real as possible.
In addition, AddThis reported that the data of already identified users was not used for any purpose other than the already mentioned study of the possibility of replacing cookies with alternative tools.
Via propublica
