Cloud Encryption Backup
Many of us have already appreciated the advantages of cloud technologies , which today set the fashion for working on the Internet and storing files. Depending on the size of the occupied space, the user has the opportunity, for free or for free, to store quite large amounts of data on remote servers. At the same time, access to stored information is possible from anywhere in the world - from anywhere where there is Internet access, from any device (local computer, tablet, smartphone) and from any OS.

The ability to synchronize data is also interesting ., allowing you to always have on hand updated information. For example, you need to finish working with a specific document in the backup folder as soon as possible. You work with him in the office, but before you finish, continue to work on the way home on the tablet (where the document will open with all the changes already made) and end on your home computer, where all the information, after synchronizing with a cloud copy of this document, also will be updated.
In addition, installing on the computer those applications with which we are all used to working almost daily is also not necessary now. For example, the entire set of office applications from Microsoft is now available to work directly through a browser using Office Online, from where the created documents can be immediately saved on OneDrive and, if necessary, shared with other users. You can also work with documents through Google Docs , Google Sheets, etc.
Thus, cloud technologies provide quite extensive and interesting opportunities and, most likely, the transition from using the contents of a personal computer to using cloud services, where resources and computing technologies are distributed among all not so far. After all, all that is needed for the full use of cloud technology is stable high-speed Internet access.
At the same time, there is another side. By sending his files to the cloud, the user, in fact, trusts them to an unauthorized person - the provider of this service and falls into a certain dependence on him. Is there a guarantee that tomorrow the owner of the cloud will not raise prices for his services or will not refuse access at all without knowingly warning you about it, as a result of which you will lose all your files? In addition, not a single cloud service is insured against malfunctions (recall at least the cases with the fall of Amazon ES2 ).
No less important is the issue of protecting information in the clouds from third-party access. Is it worth it to fully trust the holders of cloud services, relying on the measures taken by them to protect information, is a private matter for everyone. And, even if so, is it possible to be sure that employees of the service itself will not get access to your information?
Of course, you feel much more confident and calm if the files are encrypted by you personally on your own computer, using the method, program and algorithm that you have chosen.
Which approach in this case to choose? Refusing to use cloud technology is, of course, unreasonable. But fully relying on cloud resources is also hardly worth it. It is possible, for example, to store non-confidential large files (video, audio and photos) on the cloud, trusting the security measures of the provider itself and not store them on your computer, thereby unloading it from a significant amount of data. At the same time, all confidential documents will be better stored on your hard drive, and send encrypted backups to the cloud.
CyberSafe provides the ability to encrypt files on any cloud storage: Google Drive, Dropbox, Microsoft OneDrive, Apple iCloud (PC version of the client), Box, etc. At the same time, the application that you use for backup can be any and perform backup files not only to the “cloud”, but also over the local network, to network storage, RAID-array or using any other technology and storage location.
When you add a local backup folder to CyberSafe, the program creates a mirror copy of it. After that, all files added to the mirror folder are encrypted and transferred to the backup folder in an already encrypted form. Then, the encrypted data goes to a remote resource (cloud). All work with encrypted files comes from the mirror folder in the modetransparent encryption .

CyberSafe has the following advantages over encryption designed to cloud services program BoxCryptor :
1. While BoxCryptor stores private user keys on your server, in CyberSafe your private key stored only on your computer and, if desired (by means of the built-in kpriptoprovaydera CryptoPro ) may created and stored on a token.
2. In Boxcryptor, encrypted files are stored on a cryptodisk, which is also vulnerable . CyberSafe uses transparent encryption to protect files with a trusted application system that provides additional protection for your files.
3. Boxcryptor charges users for a one-year subscription, which can lead to account blocking if it is not renewed, while in CyberSafe the license is not limited in time.
Thus, when working with CyberSafe, the encryption of data sent to the cloud resource is carried out on the user side, after which the encrypted files are constantly available for any operations on the fly. All the important information that you store on the cloud service is reliably protected and, at the same time, available for use at any time.

The ability to synchronize data is also interesting ., allowing you to always have on hand updated information. For example, you need to finish working with a specific document in the backup folder as soon as possible. You work with him in the office, but before you finish, continue to work on the way home on the tablet (where the document will open with all the changes already made) and end on your home computer, where all the information, after synchronizing with a cloud copy of this document, also will be updated.
In addition, installing on the computer those applications with which we are all used to working almost daily is also not necessary now. For example, the entire set of office applications from Microsoft is now available to work directly through a browser using Office Online, from where the created documents can be immediately saved on OneDrive and, if necessary, shared with other users. You can also work with documents through Google Docs , Google Sheets, etc.
Thus, cloud technologies provide quite extensive and interesting opportunities and, most likely, the transition from using the contents of a personal computer to using cloud services, where resources and computing technologies are distributed among all not so far. After all, all that is needed for the full use of cloud technology is stable high-speed Internet access.
At the same time, there is another side. By sending his files to the cloud, the user, in fact, trusts them to an unauthorized person - the provider of this service and falls into a certain dependence on him. Is there a guarantee that tomorrow the owner of the cloud will not raise prices for his services or will not refuse access at all without knowingly warning you about it, as a result of which you will lose all your files? In addition, not a single cloud service is insured against malfunctions (recall at least the cases with the fall of Amazon ES2 ).
No less important is the issue of protecting information in the clouds from third-party access. Is it worth it to fully trust the holders of cloud services, relying on the measures taken by them to protect information, is a private matter for everyone. And, even if so, is it possible to be sure that employees of the service itself will not get access to your information?
Of course, you feel much more confident and calm if the files are encrypted by you personally on your own computer, using the method, program and algorithm that you have chosen.
Which approach in this case to choose? Refusing to use cloud technology is, of course, unreasonable. But fully relying on cloud resources is also hardly worth it. It is possible, for example, to store non-confidential large files (video, audio and photos) on the cloud, trusting the security measures of the provider itself and not store them on your computer, thereby unloading it from a significant amount of data. At the same time, all confidential documents will be better stored on your hard drive, and send encrypted backups to the cloud.
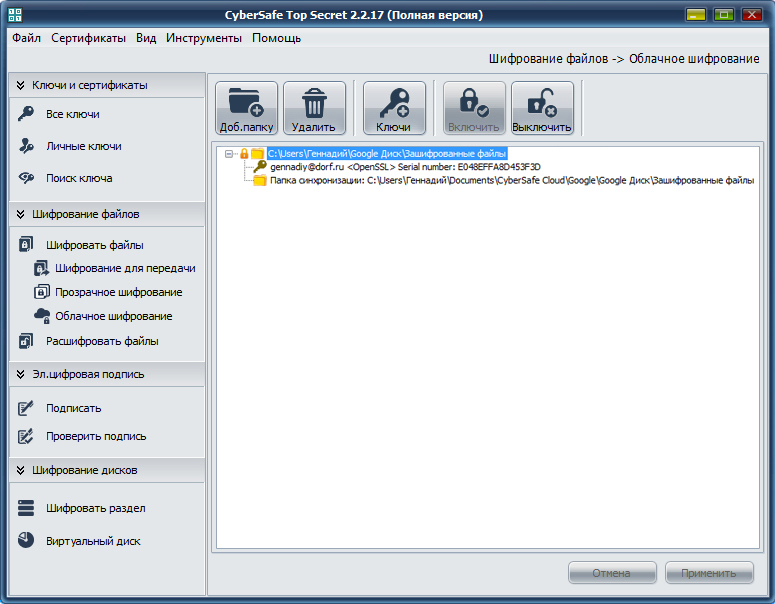
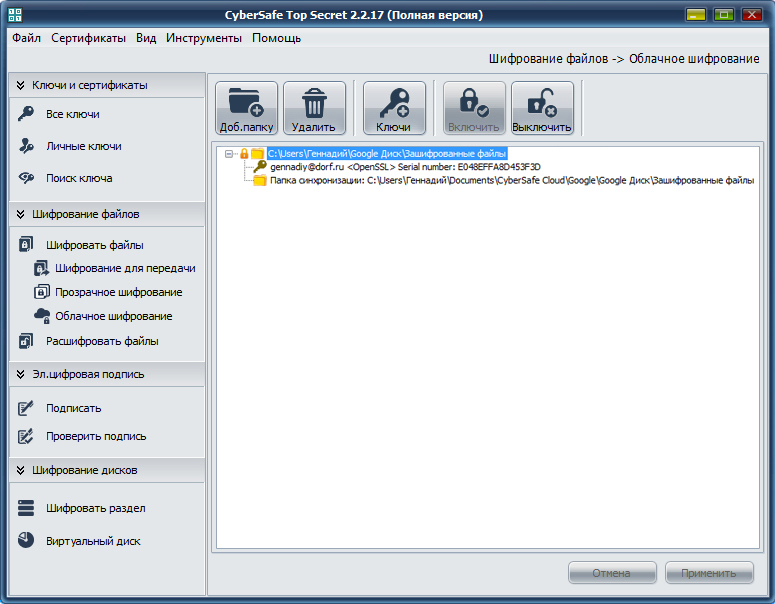
Backup Encryption with CyberSafe
CyberSafe provides the ability to encrypt files on any cloud storage: Google Drive, Dropbox, Microsoft OneDrive, Apple iCloud (PC version of the client), Box, etc. At the same time, the application that you use for backup can be any and perform backup files not only to the “cloud”, but also over the local network, to network storage, RAID-array or using any other technology and storage location.
When you add a local backup folder to CyberSafe, the program creates a mirror copy of it. After that, all files added to the mirror folder are encrypted and transferred to the backup folder in an already encrypted form. Then, the encrypted data goes to a remote resource (cloud). All work with encrypted files comes from the mirror folder in the modetransparent encryption .

CyberSafe has the following advantages over encryption designed to cloud services program BoxCryptor :
1. While BoxCryptor stores private user keys on your server, in CyberSafe your private key stored only on your computer and, if desired (by means of the built-in kpriptoprovaydera CryptoPro ) may created and stored on a token.
2. In Boxcryptor, encrypted files are stored on a cryptodisk, which is also vulnerable . CyberSafe uses transparent encryption to protect files with a trusted application system that provides additional protection for your files.
3. Boxcryptor charges users for a one-year subscription, which can lead to account blocking if it is not renewed, while in CyberSafe the license is not limited in time.
Thus, when working with CyberSafe, the encryption of data sent to the cloud resource is carried out on the user side, after which the encrypted files are constantly available for any operations on the fly. All the important information that you store on the cloud service is reliably protected and, at the same time, available for use at any time.
