How to protect data in cloud neural networks - a new encryption method is proposed
Researchers from MIT have developed a new encryption method for working with neural networks in the cloud - Gazelle. The server processes the user data without knowing their content, that is, they remain anonymous. We talk about the system and its prospects.

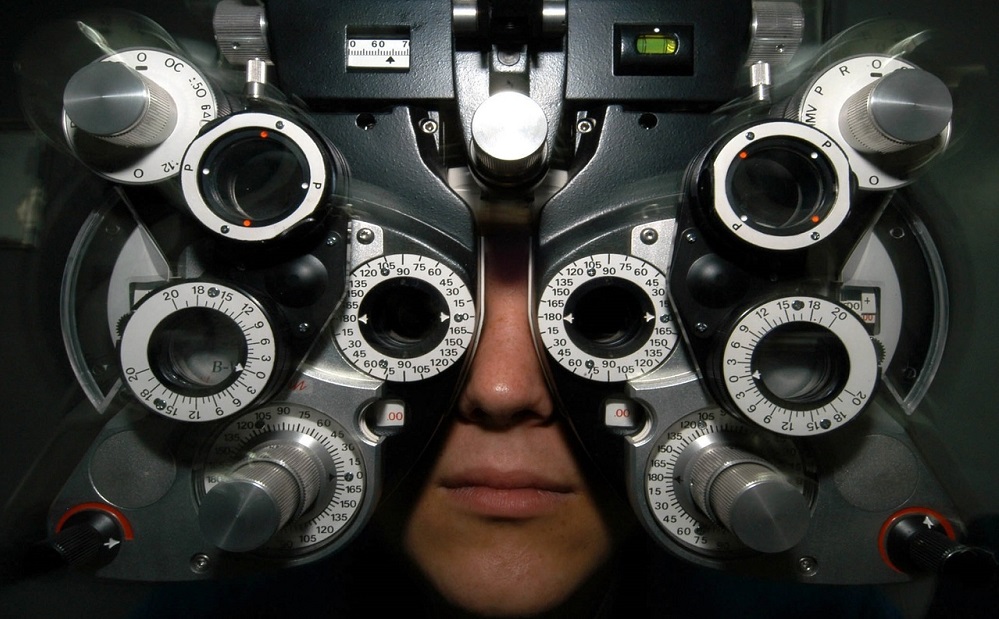
/ photo by John Jones CC
Machine learning outsourcing is a growing trend in the IT industry. Large firms launch cloud platforms with convolutional neural networks. These networks are often used to classify images (in medicine, for example, to classify X-rays and CT images). However, their network communication mechanisms seriously slow down the entire process, which limits the range of applications of such services.
Gazelle will allow you to protect data that is transmitted to neural networks in the cloud, and speed up their processing. The MIT solution is 20–30 times faster than similar algorithms .
The system uses two forms of encryption. The first - homomorphic encryption - it allows you to perform various mathematical operations on the encrypted user data and generate an encrypted result. Moreover, it corresponds to the result of operations performed with “open” values.
The second form is a distorted contour protocol . This is a confidential calculation protocol that allows system participants to evaluate a value (for example, more, less or equal), without disclosing information about the input data and without attracting a third party (arbitrator).
In general, the system consists of three components. The first is the homomorphic layer (Homomorphic Layer), which contains fast implementations of homomorphic operations: SIMD-complex and SIMD-multiplication (scalar), as well as automorphisms . The second component is the kernel of linear algebra (Linear Algebra kernels). The algorithms of matrix-vector multiplication and homomorphic convolution, as well as the system for searching for signs of images, are “concluded”
The third component is called Gazelle Network Inference. This is an inference system that combines distorted contour systems with the kernels of linear algebra. It is the basis of the protocol for outputting the results of neural network processing.
The very same data processing is as follows. First, the client encrypts its data using the homomorphic encryption scheme and sends it to the server with a neural network. Further, the neural network performs the necessary computations in the linear layer, and then transfers them further to the non-linear (in convolutional neural networks, these layers constantly alternate).
After that, the data is shared between the network and the user's device. On the device of the latter there should be a system that is able to work with schemes based on the construction of distorted contours. The user independently conducts a series of calculations and sends the encrypted results back to the cloud.
This load sharing ensures that the neural system will perform complex homomorphic calculations for one layer at a time. This avoids data noise and improves system performance (since the distorted contour works best on non-linear layers). Similar data exchange is performed alternately for all layers of the network.
Further, the procedure for sharing secrets. The data, divided into several parts, synchronized and collected together at the client. The cloud service sends the last key to decrypt the result. So one side (the user) receives the results of the classification, and the other side (the server with the neural network) does not receive anything.
More information about the system can be found in the article published by the researchers on the results of their work.
So far, the algorithm is experimental and has not been implemented in any particular application. Creating programs with practical application is the next stage in the development of the system.
/ photo PxHere PD
Perhaps one of the yuzkeys will be a machine learning algorithm that detects the presence of diabetic retinopathy in patients by taking an eye picture. The system has already been approved by the Food and Drug Administration of the United States and is used in hospitals. There is a possibility that it will be the first for which Gazelle is being implemented.
The technology is planned to be used not only in the field of medicine. It will also be used in analytical systems for the financial market and face recognition systems. So, the server will not have access to the original photos of people, which should increase the security of these solutions.
PS What else do we write on the IaaS blog:
PPS Fresh posts from our blog on Habré:

/ photo by John Jones CC
What is needed Gazelle
Machine learning outsourcing is a growing trend in the IT industry. Large firms launch cloud platforms with convolutional neural networks. These networks are often used to classify images (in medicine, for example, to classify X-rays and CT images). However, their network communication mechanisms seriously slow down the entire process, which limits the range of applications of such services.
Gazelle will allow you to protect data that is transmitted to neural networks in the cloud, and speed up their processing. The MIT solution is 20–30 times faster than similar algorithms .
How technology works
The system uses two forms of encryption. The first - homomorphic encryption - it allows you to perform various mathematical operations on the encrypted user data and generate an encrypted result. Moreover, it corresponds to the result of operations performed with “open” values.
The second form is a distorted contour protocol . This is a confidential calculation protocol that allows system participants to evaluate a value (for example, more, less or equal), without disclosing information about the input data and without attracting a third party (arbitrator).
In general, the system consists of three components. The first is the homomorphic layer (Homomorphic Layer), which contains fast implementations of homomorphic operations: SIMD-complex and SIMD-multiplication (scalar), as well as automorphisms . The second component is the kernel of linear algebra (Linear Algebra kernels). The algorithms of matrix-vector multiplication and homomorphic convolution, as well as the system for searching for signs of images, are “concluded”
The third component is called Gazelle Network Inference. This is an inference system that combines distorted contour systems with the kernels of linear algebra. It is the basis of the protocol for outputting the results of neural network processing.
The very same data processing is as follows. First, the client encrypts its data using the homomorphic encryption scheme and sends it to the server with a neural network. Further, the neural network performs the necessary computations in the linear layer, and then transfers them further to the non-linear (in convolutional neural networks, these layers constantly alternate).
After that, the data is shared between the network and the user's device. On the device of the latter there should be a system that is able to work with schemes based on the construction of distorted contours. The user independently conducts a series of calculations and sends the encrypted results back to the cloud.
This load sharing ensures that the neural system will perform complex homomorphic calculations for one layer at a time. This avoids data noise and improves system performance (since the distorted contour works best on non-linear layers). Similar data exchange is performed alternately for all layers of the network.
Further, the procedure for sharing secrets. The data, divided into several parts, synchronized and collected together at the client. The cloud service sends the last key to decrypt the result. So one side (the user) receives the results of the classification, and the other side (the server with the neural network) does not receive anything.
More information about the system can be found in the article published by the researchers on the results of their work.
Technology perspectives
So far, the algorithm is experimental and has not been implemented in any particular application. Creating programs with practical application is the next stage in the development of the system.
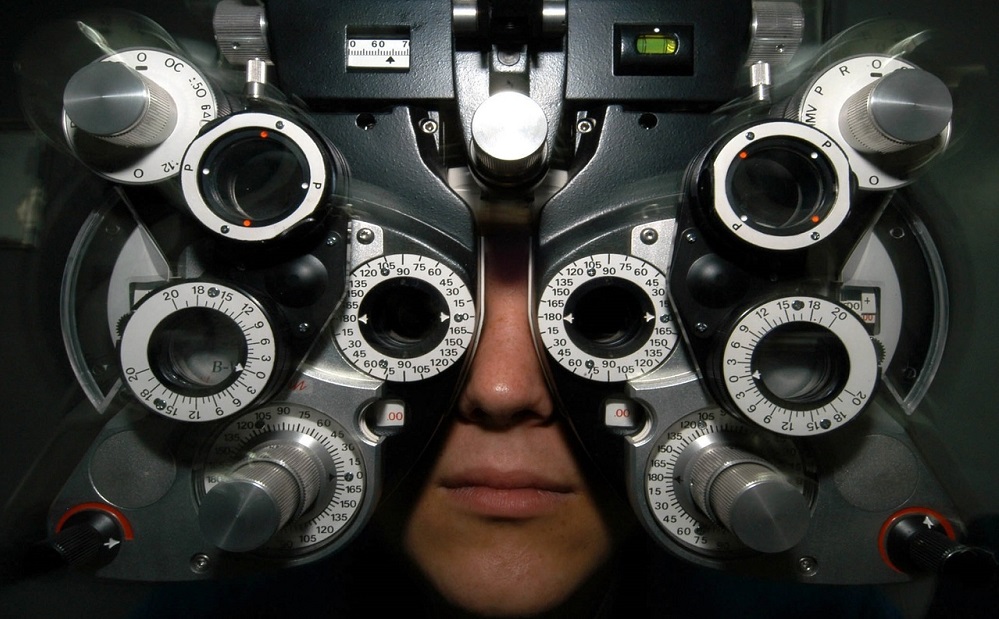
/ photo PxHere PD
Perhaps one of the yuzkeys will be a machine learning algorithm that detects the presence of diabetic retinopathy in patients by taking an eye picture. The system has already been approved by the Food and Drug Administration of the United States and is used in hospitals. There is a possibility that it will be the first for which Gazelle is being implemented.
The technology is planned to be used not only in the field of medicine. It will also be used in analytical systems for the financial market and face recognition systems. So, the server will not have access to the original photos of people, which should increase the security of these solutions.
PS What else do we write on the IaaS blog:
- Serverless computing in the cloud - a trend of modernity or necessity?
- Cloud technologies in the financial sector: the experience of Russian companies
- How to test disk system in the cloud
PPS Fresh posts from our blog on Habré:
