Cybersecurity experts created a skimmer detector - SkimReaper
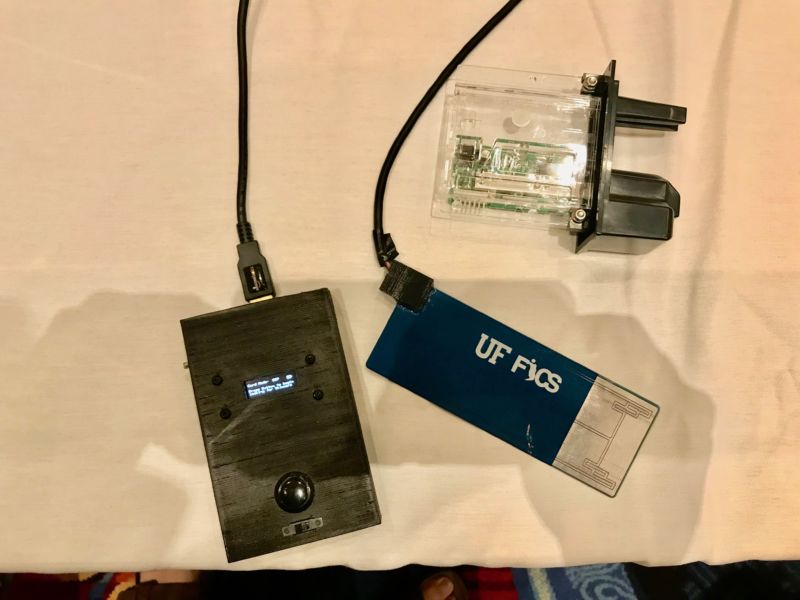
This is how the anti-anti-agem developed by representatives of the University
of Florida Researcher from the University of Florida at the USENIX Security Symposium presented the results of his large-scale project on the development of skimmer detection systems. We are talking about spy readers for credit cards that bank customers use to withdraw money from ATMs and to pay in stores.
There are a large number of skimmer varieties; many of them are almost impossible to find even for a specialist in such devices. They are masked by their creators simply masterfully, in addition, skimmers are a DIY device, of course they do not have a single standard, which further complicates their search. So, the expert in question developed the SkimReaper deviceallowing to detect installed skimmers.
Device developers gained access to police databases that contained information about the types of skimmers used by cybercriminals. In addition, researchers studied skimmers and live, which allowed to get a huge amount of information about the principles of their work and how spyware devices interact with ATMs and cards of banks' customers.
In principle, there were no surprises - data on skimmers are not something secret, descriptions, photographs and descriptions of the principle of their work can be found without problems in the network. Total devices of this type are divided into four categories.
Overhead- those that are placed on top of the slots for the introduction of ATM cards or in other places on top of the ATM. In some cases, overlay keyboards are used. There is also a more rare type of credit card scanners - those that are placed on sales terminals in stores. But this is the exception rather than the rule - the risks for attackers are great, and the chance of being caught is high.

Internal - those that are located in the slots for reading cards or somehow are placed even deeper in the electronic device. In some cases, attackers drill holes in the right place, placing a skimmer in the case and connecting it to the infrastructure of the common system. There is a variety of devices that read the characteristics of transactions - their craftsmen are connected to the electronic filling of the ATM.
Network skimmers - they are located in the network equipment to which the ATM is connected. If employees of a bank or other organization where the ATM is located are rather careless, it is not so difficult to do.

Other varieties - among them there are both exotic ones, which are located, for example, at the doors of banks, and quite ordinary ones, which simply look and act not like other systems of this kind.
Most often, criminals use invoices and internal types of skimmers - the fact is that they are difficult to detect. By the way, a skimmer is not everything, attackers often need pincodes of bank clients. Their criminals get using miniature video cameras, which are located somewhere near the ATM or on it, in an inconspicuous place. It is clear that the cameras are also masked so that they cannot be noticed.
So, SkimReaper, a device to combat skimmers, is designed to work with overhead and internal systems. The device circuit contains a sensor capable of detecting changes in the magnetic field that occur during the reading of a card. As a rule, the ATM reads the card once. If SkimReaper detects two or more unexpected changes in the configuration of the magnetic field, the device signals the detection of a skimmer.
All this is not a theory, but a practice; the gadget was tested when checking a number of ATMs. The raids were carried out with New York police officers who helped register violations and promptly eliminate skimmers. As it turned out, the SkimReaper efficiency is about 100%. Now police are beginning to actively use the device provided by researchers to detect skimmers. The developers of antiskimmer say that the demand from the police is so great that they simply do not have time to produce them.
But be that as it may, there are a huge number of advantages from using such a system. The fact is that if you identify skimmers on-line, almost immediately after installation, the criminals may not have enough time or resources to create new devices. These are high-tech devices that work on complex algorithms and have a rather unusual design. Recreating the withdrawn device online does not always work, so hackers are not destiny.
It is necessary to think that with the increasing popularity of skimmers, criminals will significantly reduce their activity. On the other hand, new types of devices can be created that will learn to deceive the SkimReaper.
