DoS-attack, which can not be closed: in the procurement of its own atmosphere
- Law: the bidding platform must provide access to any accredited participant.
- Practice: one of the participants registers some LLC “Romashka”, receives an electronic signature and begins to flood the site with heavy inquiries. Requests include cryptography, and not the fastest.
- Standard counteraction: disable it or temporarily block.
As you can see, points 1 and 3 are mutually exclusive.
And we live like that.
So, if an access is denied to an accredited participant, a large fine arises during a complaint. We will block one request from a million - immediately a penalty for the work of the firewall. If it was a package with a legally significant action.
This is logical, but goes against the issues of information security. All existing tools work on the principle of determining the malicious component of traffic and its blocking. When participants come to the site and participate in auctions - you cannot trust the filtering system, whom to let in, whom - no. All must get to the auction. No algorithms have the right to decide who to prevent from entering the site. The signature is a huge 10 kilobyte cryptogram. By the standards of web traffic - this is one of the heaviest incoming messages (except for downloading files). Used robust algorithms, voracious on performance.
There are rules of the site. And if users use a client-server application, and if they do it within the framework of the regulations, then everything is fine. The system can handle many trades at once.
We have the right to block non-browser clients. They do not comply with the rules of the site. There are craftsmen who create alternative software that simulates the work of a live user using a browser - and it can create a series of high-frequency queries to the server.
Anonymous requests can be dropped.
Signed need to process.
If they are signed - this is the submission of price offers, for example. The first idea is to give session keys in order not to handle complex authentication every time. We survived the wave, the struggle escalated.
There have been cases when everyone is no longer a DoS, but DDoS requests contained a legitimate electronic signature. At the same time, technologies of concealing the source (erosion) were used: under the same user, requests came from dozens of different subnets. They are complex in that they merge with the flow of legitimate requests. Even having separated, they cannot be blocked.
The second idea: to block the signature of such comrades. There are signatures issued by certifying centers with a fast connection, there are those who do not want to cooperate. But even if the certifying authority blocks the signature, it will be a problem, because the complaint to the FAS will continue. And they will strongly punish you for blocking without technical expertise. Accreditation on the site also can not be suspended - it is under the law for three years, and it can not be suspended in any way. There is simply no procedure.
Now - why it is necessary to process each request with difficulty. The fact is that requests for price or monitoring are put in the processing queue on a hot base. Because of one ten thousandth of a second, a dispute may arise before the trial. The request is decrypted, an exceptional lock goes on, then a change in several tables, then the processing of the next request. If the price offer cannot be accepted, then the procedure of rolling back changes is in progress (for example, if the offer was greater than the current auction price). Each decision has a legal status.
It is necessary to have full logs of each price offer. This imposes restrictions on the infrastructure, in particular, on the possibility of crushing the base and encapsulating its individual sections.
From classic DDoS protects us complex filtering system based on the "Arbor" and "Curator". They work in severe cases on the white list. We have all participants in the procedures in the white list. They attracted one anti-virus laboratory under the contract, and according to their recommendations made some changes. They will give a positive effect for some time, but this is a tactical measure.
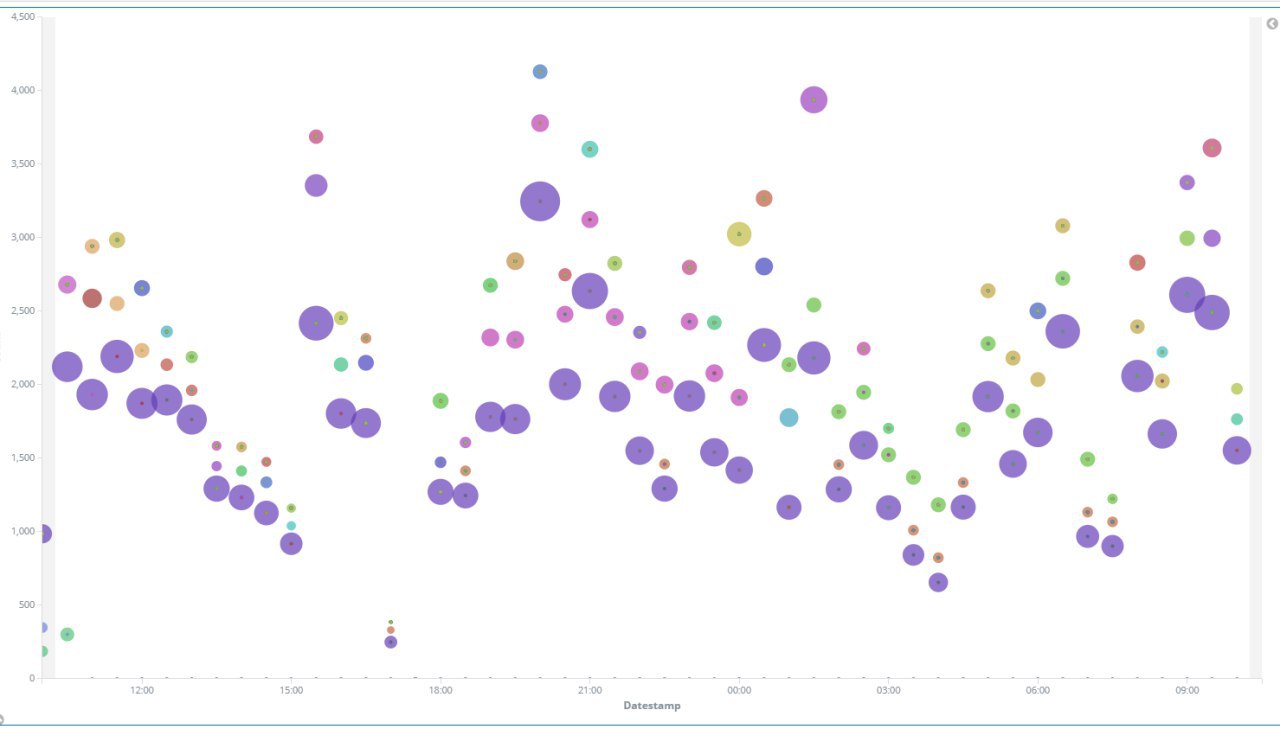
Analyzed using machine learning traffic
Attacks are organized by those who want to win the auction. For example, one participant puts the price lower, and then clogs the site so that others cannot kill it. There are more complex schemes and their combinations. There are types of procedures where the first who legislatively wins a certain price offer wins. This is a bit irrelevant in the digital world already, but such is the legislation since the days of the paper.
Sometimes it is not clear who is behind the signature. Decorated on one, but in fact the other is involved. There is no article for DDoS itself. There are 274 - violation of the rules of the system. It is assumed that simply DDoS - this is normal, if not written in the rules. We wrote.
There was a practice to catch intruders and severely punish them. These measures are still stopping the problem, but do not solve it.
We also have excellent dialogs with suppliers of DDoS solutions. At first the manager comes and says that everything will work. Then, even before the conclusion of the contract, the sales manager no longer comes, who has everything in the openwork, but a technical specialist. He will look and say in his eyes what he has and how it worked. They are already starting to buy back before the purchase: “It can start naughty. But a little bit. Maybe we do not guarantee. A little bit". And then somehow it goes smoothly into "maybe not a bit."
We also use machine learning elements. We make profiles - a cast of normal user behavior. The system relies on these good practices snapshots and automatically starts blocking when rejected. We try to do it yourself. And we display the commands of the “Soviet automatics” in advance. We know that if there are big important trades on Tuesday, they will try to put them on. People want to interfere with the bidding process. We have more than one hundred attacks a year (now it is a little less). Often we can just wait for the load to grow: 5–10 thousand bots are not a very big problem. When the situation is already critical, we begin selective locks. At the same time, we block the top (most active) bots, because we have no task to stop the attack completely, but there is a need to reduce the load to a sustained level,
The second part of the attacks is the channel-related attacks right on the data center. There was a case when the data center went to bed. There were problems with the provider's channel. We have determined in advance the format of cooperation with the provider. In particular, we manage the entire IP segment, do not allow to make filtering rules for our IP group. Any contract with a traffic clearing system means that we will lose people and receive fines. It is enough for the attackers to put the system for a second in order to fix the fact of the non-completion of the transaction: these are not quite usual attacks, the task of which is to limit access to the resource or make it completely inoperable.
We use Elastic Search to save the match data by user profiles. It is important not just to track down that someone started doing potentially anomalous. Because there is still a lot of activity similar to DDoS, when one of the activists or journalists throws off a link to the purchase, and people go in a crowd to look at it.
It takes about two or three minutes for the algorithm to start comparing, and thus a deviation is detected. At this time, exactly the infrastructure must withstand all traffic. Whatever it is. We have a stock of 15-fold business load.
Attacks are predictable on large purchases. It is dangerous to get up from the computer. I went somewhere - SMS and telegram monitoring. There is a half-minute lag to run back. Battle in seconds. Trying to put on 10-15 minutes in the morning. On the day attacked only a couple of times. In general, I was late with the reaction for 5 minutes - the procedure is over.
What we need is either to give a legislative right to defend against malicious traffic (when the site fixes it: what, at what time and why it is rejected), or to change the accreditation procedure (suspend accreditation and legally initiate proceedings with violators).
We are working on it now, but for now we offer you to admire the example of the problem that arises when the legislation created for paper-based procedures is adapted to the electronic world.
References:
- Ecosystem of the digital procurement world (to steal less)
- Electronic signature for participation in procurement
- Why do we need purchases, and what does it look like from an IT point of view
- Attack model: where they are mainly abused on competitive purchases and how they are struggling with it
- What are the procurement procedures (in simple terms)
- A brief history of electronic public procurement in Russia
- How we opened development offices
