WebAuthn standard formally completed
The W3C and FIDO Alliance have announced the completion of WebAuthn's passwordless authentication standard , which has been in place since 2015. We will tell you more about it later. / Flickr / Mark Burnett / CC BY (photo resized)
Weak passwords remain the most common cause of data leaks in companies. They are responsible for most attacks - 81% of cases, according to Verizon. Those organizations that really work on password policies spend a lot of resources on this. The Ponemon Institute claims that in total, the reset and update procedures for authentication data cost companies $ 5.2 million annually.
If we talk about the general situation in the field of authentication, we can refer to the data of specialists from Cambridge University. Back in 2010, they analyzed the security policies of 150 large sites and found that 57% of them do not use TLS. At the same time, 84% of sites allow you to endlessly select authentication data.
Nine years later, the situation with the spread of encryption has improved, but it still raises some concerns - according to WatchGuard statistics for the third quarter of 2018, almost 21% of the 100 thousand Alexa top sites do not use HTTPS.
WebAuthn passwordless authentication standard comes to the rescue here. He must solve the above problems. Instead of passphrases, its developers suggest using biometric data: fingerprint, retina and face.
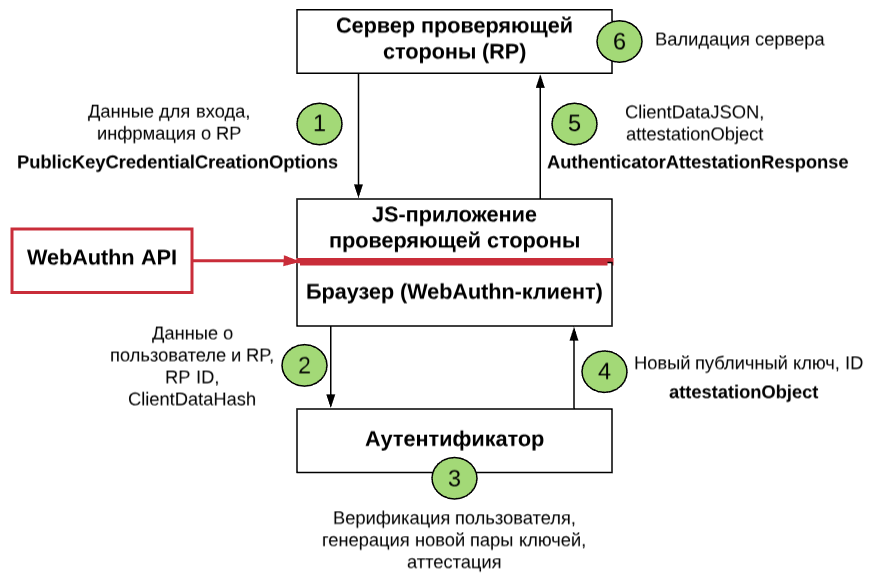
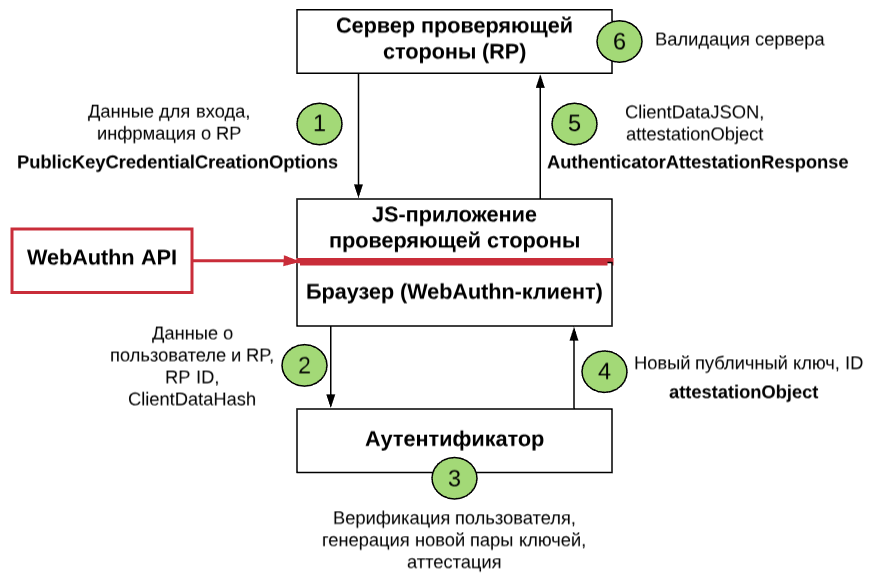
Three entities are involved in the authentication process. The first is WebAuthn Relying Party . It is a site that a user wants to enter.
The second entity is the WebAuth API . It is based on two basic methods responsible for registration and login: navigator.credentials.create () and navigator.credentials.get () . One creates access details when registering a new account and associates a key pair with an existing one. Another - uses known data for authorization on the site. Both methods use a secure connection to transmit information (for example, HTTPS).
The third entity is the authenticator. It manages user credentials and is responsible for generating public account keys.
In general, the authorization procedure on the site may look like this:
To protect against phishing, the standard uses special transactions that are attached to a specific session. If the server notices that the identifier has changed, it understands that the request comes from fraudsters and will not confirm authorization.
According to the creators of WebAuthn, the implementation of the new standard will help get rid of passwords, and hence the vulnerabilities that are associated with them. FIDO Alliance senior certification engineer Yuri Ackermann says password-free login protects users from phishing, simplifies interaction with sites, and makes biometric technologies more accessible.
In our blog we published an interview with Yuri , in which we talked about web security and passwordless solutions.
A number of security experts, however, are concerned about the fact that WebAuthn uses an asymmetric ECDAA encryption scheme. It is needed to create digital signatures. Paragon engineers believe that using cryptography methods based on elliptic curves (which ECDAA uses) is unsafe due to a number of potential vulnerabilities.
Paragon also criticized the creators of the standard themselves. Allegedly, they did not consult with leading cryptographers of the IT industry and led the development “secretly”, without providing a standard for conducting large-scale cryptographic tests.
But despite all the above, representatives of Paragon Initiative still believe in the prospect of passwordless authentication and advocate for the massive implementation of WebAuthn.
WebAuthn alreadyIt is supported in the most popular browsers and OS. The completion of the standard was only the first step towards the spread of password-free systems.
Why do you need a standard
Weak passwords remain the most common cause of data leaks in companies. They are responsible for most attacks - 81% of cases, according to Verizon. Those organizations that really work on password policies spend a lot of resources on this. The Ponemon Institute claims that in total, the reset and update procedures for authentication data cost companies $ 5.2 million annually.
If we talk about the general situation in the field of authentication, we can refer to the data of specialists from Cambridge University. Back in 2010, they analyzed the security policies of 150 large sites and found that 57% of them do not use TLS. At the same time, 84% of sites allow you to endlessly select authentication data.
Nine years later, the situation with the spread of encryption has improved, but it still raises some concerns - according to WatchGuard statistics for the third quarter of 2018, almost 21% of the 100 thousand Alexa top sites do not use HTTPS.
WebAuthn passwordless authentication standard comes to the rescue here. He must solve the above problems. Instead of passphrases, its developers suggest using biometric data: fingerprint, retina and face.
How it works
Three entities are involved in the authentication process. The first is WebAuthn Relying Party . It is a site that a user wants to enter.
The second entity is the WebAuth API . It is based on two basic methods responsible for registration and login: navigator.credentials.create () and navigator.credentials.get () . One creates access details when registering a new account and associates a key pair with an existing one. Another - uses known data for authorization on the site. Both methods use a secure connection to transmit information (for example, HTTPS).
The third entity is the authenticator. It manages user credentials and is responsible for generating public account keys.
In general, the authorization procedure on the site may look like this:
- The user visits the site and selects the option of passwordless authentication (for example, using a telephone).
- The site sends a corresponding JavaScript request to the WebAuthn client (browser).
- The browser contacts the authenticator (smartphone) so that it generates the keys and sends them to the relying party.
- The server checks the login information.
- If everything is in order, then the user is authorized on the site.
To protect against phishing, the standard uses special transactions that are attached to a specific session. If the server notices that the identifier has changed, it understands that the request comes from fraudsters and will not confirm authorization.
Potential and disadvantages
According to the creators of WebAuthn, the implementation of the new standard will help get rid of passwords, and hence the vulnerabilities that are associated with them. FIDO Alliance senior certification engineer Yuri Ackermann says password-free login protects users from phishing, simplifies interaction with sites, and makes biometric technologies more accessible.
In our blog we published an interview with Yuri , in which we talked about web security and passwordless solutions.
“WebAuthn can change the way we interact with Internet resources,” said Sergey Belkin , head of development for IaaS provider 1cloud.ru . - Users do not have to invent and remember passwords. However, up to this point, website owners and application developers should start using the standard. It is already being implemented by Google, Dropbox, Bank of America. But before passwordless authentication becomes widespread, it will take some time. ”
A number of security experts, however, are concerned about the fact that WebAuthn uses an asymmetric ECDAA encryption scheme. It is needed to create digital signatures. Paragon engineers believe that using cryptography methods based on elliptic curves (which ECDAA uses) is unsafe due to a number of potential vulnerabilities.
Paragon also criticized the creators of the standard themselves. Allegedly, they did not consult with leading cryptographers of the IT industry and led the development “secretly”, without providing a standard for conducting large-scale cryptographic tests.
But despite all the above, representatives of Paragon Initiative still believe in the prospect of passwordless authentication and advocate for the massive implementation of WebAuthn.
WebAuthn alreadyIt is supported in the most popular browsers and OS. The completion of the standard was only the first step towards the spread of password-free systems.
