Information Security Instances on the platform attackdefense.com

... We live in an era of big events and small people
... Winston Churchill
Today we present to your attention the first article from the cycle on the analysis and passage of laboratory work from the resource attackdefense.com with the support of the well-known conference organizer ( Black Hat and Pentes Academy ) - a project that allows you to understand in many aspects of attacks on various protocols, services, systems. For the most part, this resource is a platform with laboratory work on the most relevant topics.
We will immediately answer some of the questions that may appear during the reading of this material:
Under the spoiler
- What did you like about this resource? (Its ease of use. You do not need to have a whole range of programs and services to hone your "skills", there are already many.)
- Is this article promotional? (This series of articles will be of a purely technical nature, aimed at passing laboratory work, and not at the PR resource. But we do not exclude that interest in this site may increase.)
- “Immediately by the way, the community will ask a question about how ethical to describe the solutions of other people's problems and whether we received an acceptance for a similar series of articles from the authors of the resource”
(Unfortunately, but no, we are trying to get in touch with them through public mailing addresses. But the answer so far what not.) - How often and how many articles are expected to be released? (plans to publish 2 more materials with a video presentation. And further articles will be formed already from your wishes in the comments.)
- The site already has answers to laboratory work and a description with a video. Why then this article? (Yes, all right, such material is especially present in old laboratory works. But unfortunately, some of the fact-finding materials on the topics are paid. Just like the video. We will not talk about all laboratory works. And publish our solution, with “ our "materials and our video recordings. Thus, we will not compete with the site itself and not interfere with it in the sale of paid subscriptions to materials)
- Questions comments and criticisms appropriate? (Of course! Always open for conversation, for this there is: Telegram: @ orion_0ri0n)
- Are there other related topics? (Of course! There are a lot of them, some of which even form their TOP of the best, as an example: HackTheBox)
- From a legal point of view, actions on this resource are contrary to the law? (There can be no definite answer to this question, because according to the rules of this resource. Performing laboratory work, you do not violate any laws. But if you try to “crack” the architecture of this resource or other actions prohibited by the rules, for example : attackdefense.com/policy/ pp.txt . That resource warns you that your data may be transmitted to the police or other authority
Disclosure for Law Enforcement: Under certain circumstances, Binary Security Inc. may be required to disclose your Personal Data if required to do so by law or in response to valid requests by public authorities (eg a court or a government agency).)
In this article, we briefly review:
- Lyrics about features and resources. And what will it give us.
- What types of "attacks" the resource offers.
- Material on the attack vector according to the laboratory work that we will describe.
- The solution of one of the "test" laboratories.
- Conclusions.
The following articles are planned:
- Complete the full line of one type of attack direction. (Traffic Analysis)
- We will prepare materials for the course.
- Let us analyze the main errors that arise when solving laboratory work.
- We will collect a brief theory in this direction (theses / cribs)
- We answer the questions in the previous article.
Introduction
The aim pursued by us: To develop interest in the study of services for those who had not previously been devoted to this topic, but had a burning interest in this area.
Some people and communities have already started this topic, but no one has revealed the potential of the resource. What we try to offer, what others do not. These are explanations in technologies where a particular vulnerability arose, which will help to understand why this vulnerability arose and how it can be closed, avoided or counteracted.
For more skillful people who have already formed their opinion and have their “own” direction of development, we suggest that you familiarize yourself with the possibility of discovering new vectors for yourself.
For professionalsWe offer to discover the new "Capture the Flag". This direction will not be given a detailed review. This will remain for independent passage. (But, if there are volunteers who want to share their achievements, results or original solutions. We will be pleased to add your thoughts to a separate section of the articles. As an additional review. With the mention of heroes.
See here for more details:
For those who are interested in publishing their results, we suggest including them in this series of articles. Where it will be necessary from you:
What we can offer you: (unfortunately, a little)
- Provide information about which layer of the solved laboratory work you want to demonstrate. (Maybe someone has already passed it and material is being prepared on it)
- The very solution to this Lab. The solution should include:
- The code necessary to solve this lab. (most often it is already on the site. And if it matches, there is no need to copy)
- Comments on the code. After all, maybe you used your original solution. Or a decision not stipulated by the condition. Which speeds up, reduces time and labor costs.
- Conclusions in the laboratory. What are comments suggestion or your opinion.
- Materials for this course. (since there are many directions and the community (including us) can be inferior to you in knowledge)
- Video materials and / or screenshots are required.
What we can offer you: (unfortunately, a little)
- The publication of your material in the context of a general article on the passage of laboratory work. (except if the material is sufficient for a separate article, then it will go as a special issue.)
- Link to you, your profile or your other resources (at your request.)
- Advertising mention of your service or resource. At the beginning of the article. In the section about the Author.
- Our respect and recognition of the community.
- The plans: When publishing a video of the passage of laboratory work, where you participated. Link to you or your resource. (under the video in the description)
Loading
Some statistics:
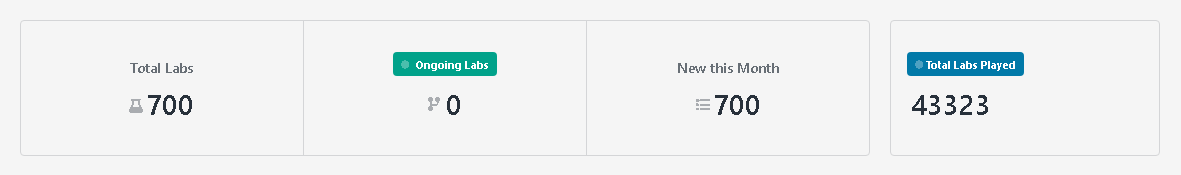
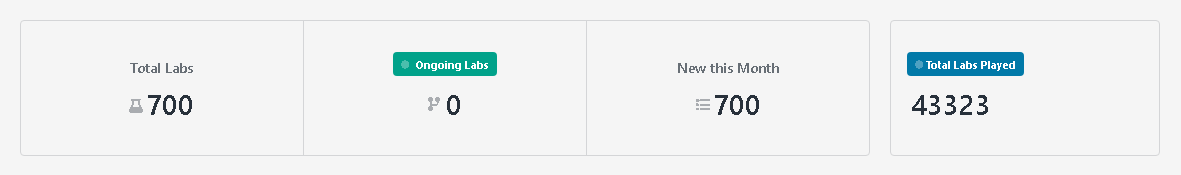
At the time of writing, the number of laboratories increased from 505 - 664 - 700 pcs.
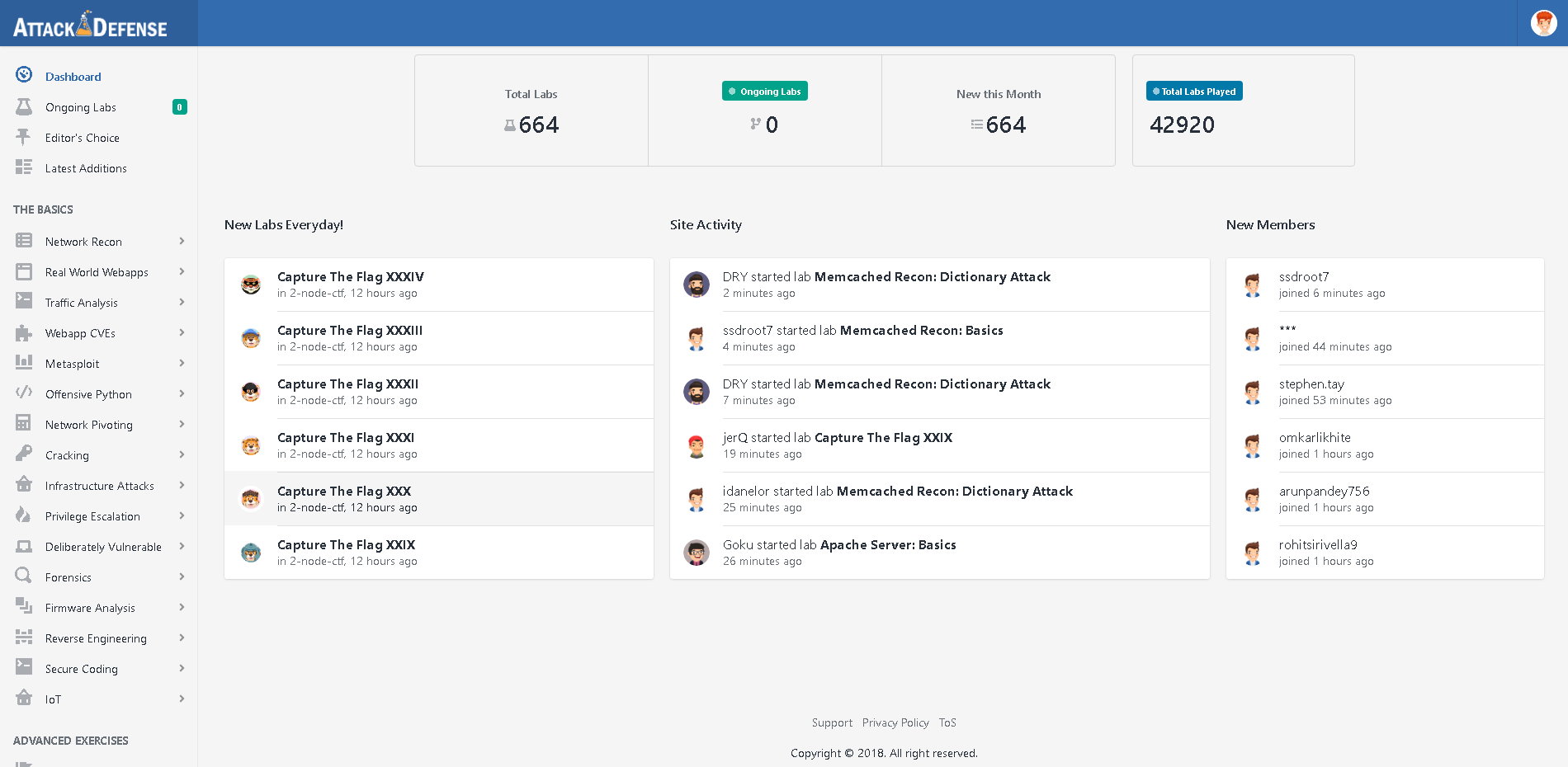
Screenshots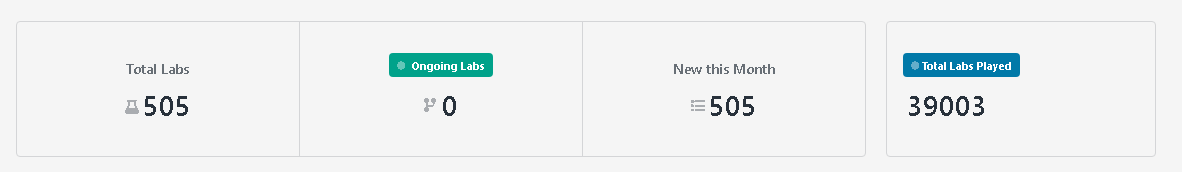
Let's quickly go through the menu:
| Network recon | Network intelligence: Scanning, collecting information about the most popular services (IMAP Servers, DNS, SIEM Platforms, SMB Servers, SSH Servers, Telnet Servers and others.) |
| Real World Webapps | Web applications: Exploiting vulnerabilities on the web. SQL Injection, File Upload, Stored XSS, and others |
| Traffic analysis | Traffic analysis: We learn to work with tshark and traffic analysis including Wi FI. |
| Webapp CVEs | Webapp CVEs: CVE Tasks Set (broken down by year, very convenient) |
| Metasploit | Metasploit attacks: instance on working with metasplit. Themes are different. |
| Offensive Python | Python attack: |
| Network pivoting | Network Pivoting - Not Subject to Correct Translation |
| Cracking | Cracking *: |
| Infrastructure attacks | Attacks on Network Infrastructure: Exploiting Vulnerabilities in Network Services |
| Privilege Escalation | Privilege escalation: instance to elevate privileges across platforms. Linux / web |
| Deliberately vulnerable | Intentional vulnerabilities *: ??? |
| Forensics | Forensics: For the most part, analysis of logs and the ability to work with them. |
| Firmware analysis | Analysis of firmware: Analysis of firmware of routers, search for backdoors. |
| Reverse engineering | Reverse engineering: instance with “pulling” passwords and keys. |
| Secure coding | Safe coding: A new section is still being formed |
| IoT | IoT: A new section is still being formed |
| I really liked the last two points: (Secure Coding and IoT) for a reason. Previously, I have not seen similar laboratories for testing. (on the resource they appeared on 02/27/2019 - fresh) We advise you to try to figure it out on your own. | |
Lab Analysis: Network Recon - Memcashed [Theory]
Memcached is a software that implements a hash table-based data cache service. Using the client library, it allows you to cache data in the RAM of many available servers (see wiki or habr.com for a little more details ).
What is the interest of this product, why is it given such attention?
The problem lies in the simplicity of using this tool in the interests of "attackers" because the protocol used in this application is UDP. As you remember, what is the difference between TCP vs UDP protocols (I’ll remind you who forgot about the example: otvet.mail / Wiki or link) Those. UDP allows you to send frame data without worrying about receiving it by the addressee. And most importantly, the amount of data transmitted through UDP is many times greater than through TCP.
But what is such attention? And the fact is that when accessing this software through a network / Internet to port 11211 with an incoming packet size of 100 kb. The answer can be obtained in 1,000-50,000 times more. Those. Sent 100 kb will return 100 000 kb. Good ratio? Best!
But what is the danger? You ask. Why is this information needed?
But the problem is this: in local networks and telecom operators that do not control traffic, an attack like ip spoofing is possible, i.e. substitution of outgoing ip. It turns out that now the malefactor can not only introduce himself as anyone, but also on his behalf will request any information.
And here it turns out this (briefly illustrated in the image):
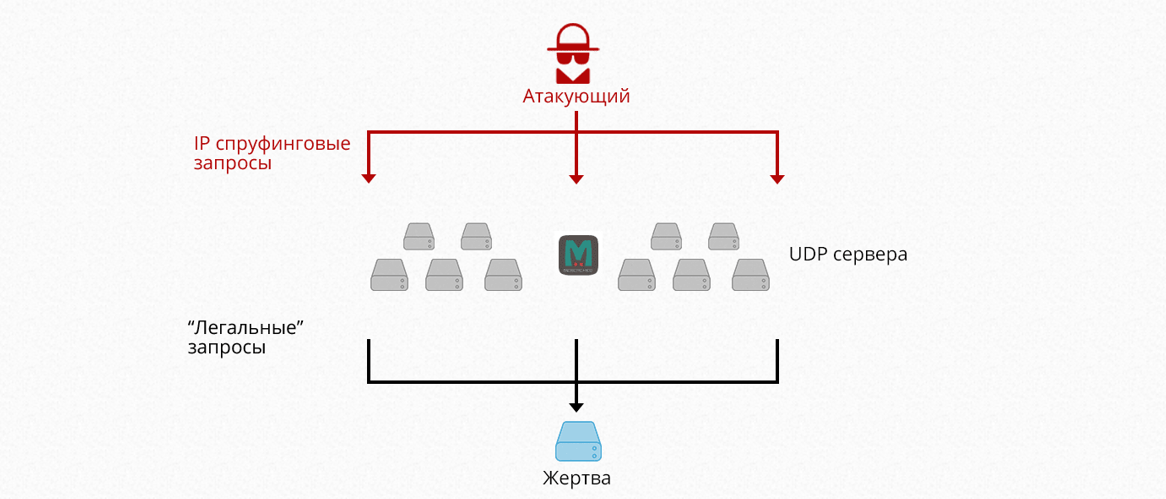
- An attacker using ip spoofing spoofs his ip. On the ip "victim".
- Makes a request to the Memcashed server. With a changed IP address
- The server responds to the request. But the response to the appeal already sends to the “victim”
- The “victim” receives a response 100 times the size of the request.
As a result, a large number of such request-responses. A Dos or DDos attack may occur depending on the number of zombie machines.
More details can be found here: securitylab , xakep.ru , 360totalsecurity
Or search on Google.
Mitigation: How to Fix Memcached Server Vulnerabilities?
One of the easiest ways to prevent Memcached servers from being misbehaved as reflectors is a firewall, blocking, or limiting UDP speeds on source port 11211. Because Memcached uses INADDR_ANY and starts with UDP support by default, administrators recommend disabling UDP support if they do not use it. An attack through Memcached cannot be easily stopped by Internet service providers (ISPs) if spoofing IP is allowed on the Internet.
An example of a service search using nmap (not the most rational way)
nmap 192.168.1.1 -p 11211 -sU -sS --script memcached-infoIn this series of laboratory work, you will be able to familiarize yourself with the simple intelligence functions of the Memcashed service. Where tools from the Metasploit arsenal will be affected. And standard Linux system commands. Not that complicated and ordinary.
Lab Analysis [Practice]
[Menu]
Each laboratory work has menu items:
1. Task
2. Rules
3. Answers to the task
4. Hints for the solution. (not always and not in all labs)
5. References for reading (En only)
[ The task ]
1. Find the version of memcached server using nmap.
2. Find the version information using netcat or telnet.
3. Find the maximum number of simultaneous incoming connections allowed by the memcached server use available nmap scripts.
4. Find the number of current items on the memcached server using memcstat.
5. Find the value stored in key “flag” from the key value pairs dumped by available metasploit module.
6. Find the name of all keys present on the memcached server using memcdump.
[ Start ]

Click “Lad link” a new window will open with the kali linux terminal.
This will be our main window with you. (not any virtual machines. Everything has already been installed and configured for you. All the scripts for the laboratory are already inside. There is no need to download, search, invent anything!) As a rule (but not always) the materials, scripts and databases are in the root folder, or at home.
Task 1: Find the version of memcached server using nmap.
Hint already given earlier. We use nmap
Nmap –p 11211 ipaddress –sV
–p порт. Порт по умолчанию 11211
-sV – показывает версию сервиса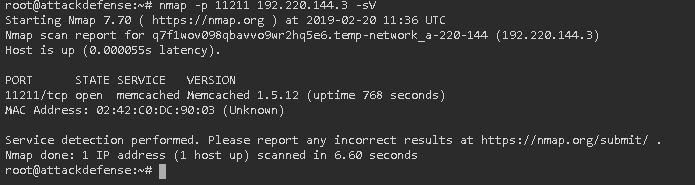
More details about nmap can be found at the end of the article. In the section Extras. materials. We’ll put cribs there.
Result: 1.5.12 (the answer in the lab they write 1.5.6 is more visible to them)
Task 2: Find version information using netcat or telnet.
How much they didn’t ask:
I have not received an answer.
Result: Failed to get the result.
Task 3: Find the maximum number of concurrent incoming connections allowed by the memcached server to use available nmap scripts.
Hint: google search: memcached nmap
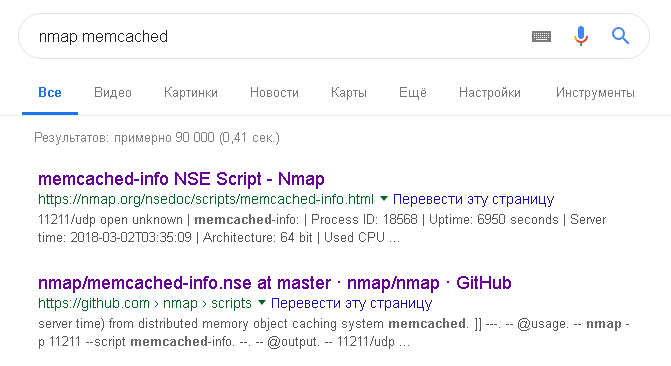
Follow the links and see that there is already a ready-made solution for finding info about memcache. Since we were assured that all the scripts are already installed, we try:
Nmap –p 111211 –script memcached-info 182.220.144.3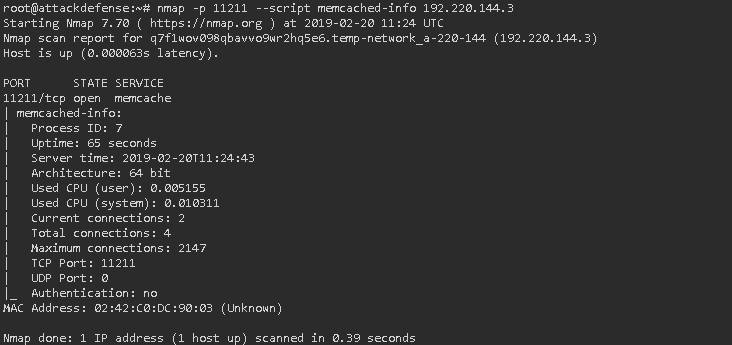
Result: 2147
Task 4: Find the number of current items on the memcached server using memcstat.
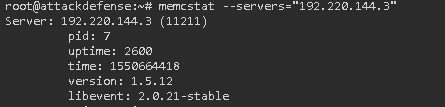
memcstat –h
memcstat --servers=”IP”Result: curr_items: 10
Task 5: Find the value stored in the “flag” key from the pairs of key values reset by the available metasploit module
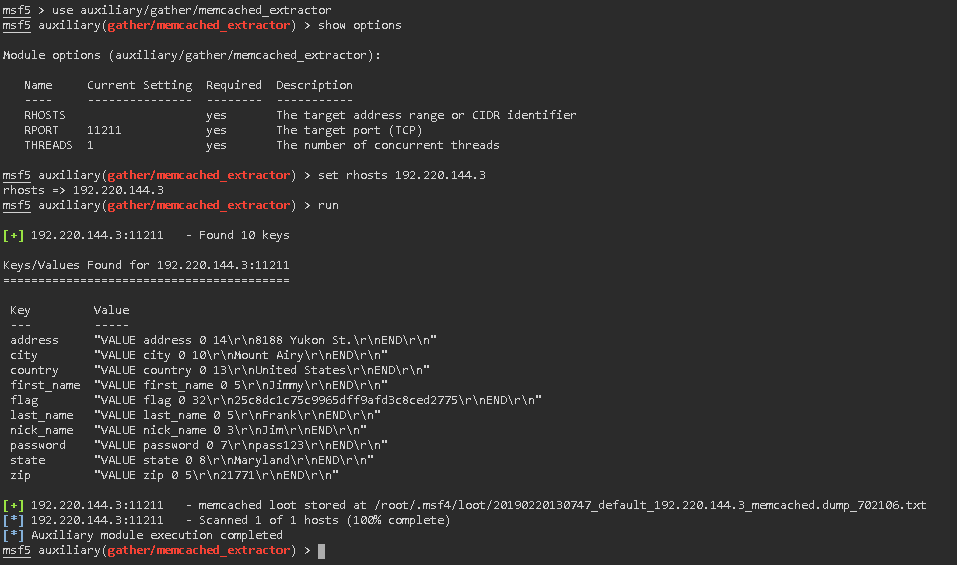
use auxiliary/gather/memcached_extractor
show options
set rhosts 192.220.144.3
runScript response: flag "VALUE flag 0 32 \ r \ n25c8dc1c75c9965dff9afd3c8ced2775 \ r \ nEND \ r \ n"
Result: "VALUE flag 0 32 \ r \ n25c8dc1c75c9965dff9afd3c8ced2775 \ r \ nEND \ r \ n"
(25ccc75cc7575cc75ccc75cc9c975ccc9c9c9c9c9ccc75cc9c9ccc75cfcdcfcfcdcfcdc .
Task 6: Find the name of all keys on the memcached server using memcdump.
Hint: we already know them. With the help of our metasplit in the previous task. Well, we can still see:
root@attackdefense:~# memcdump 192.220.144.3flag, password, country, zip, state, city, address, nick_name, last_name, first_name

Result: flag, password, country, zip, state, city, address, nick_name, last_name, first_name
Task 7: Find the value stored in the “first_name” key with the memcached-tool.
You want to try it yourself with the memcached-tool tool
Result: But the answer will be the same: Jimmy
How did you find out? We look at a screenshot from "Result 5".
To summarize
1. Regarding this Lab,
as we have seen, there are several approaches to solving the assigned tasks (clearly visible on questions 5, 6 and 7) and, most importantly, your time depends on the choice of solution.
Unfortunately, I still did not understand the essence of task number 2. But alas, I did not get success (
2. Regarding the entire resource.
What we liked this resource:
Spoiler heading
1. Множество лабораторных работ по разны тематикам
2. Нет необходимости искать различные утилиты для той или иной атаки. (уже все есть в лабе)
3. Нет необходимости разворачивать на своем железе виртуальные образы / контейнеры. И тратить на это время. (экономит массу времени)
4. Все работает через браузер. Не нужно иметь под рукой путти и другие утилиты. Уже все есть
5. Бесплатно!
6. Постоянные обновления (Последнее обновление + 160 лабораторных работ.)
7. На каждую лабу есть ответы. Даже если Вы не уверены в результате, можешь проверить себя.
8. Безопасно! Не наказуемо законом. (Если не нарушать его)
9. Нет ограничений на время выполнения и количество попыток. (Вру – есть. Но это детали см. минусы проекта)
10. И думаю самое важное, чем зацепил меня этот проект. Это возможность самостоятельного изучения новых направлений. Тут нет готовых решений (есть подсказки в лаба), а только направления с ожиданием определенного результата.
11. Можно проходить совместно часть лаб.
12. Есть CSF.
2. Нет необходимости искать различные утилиты для той или иной атаки. (уже все есть в лабе)
3. Нет необходимости разворачивать на своем железе виртуальные образы / контейнеры. И тратить на это время. (экономит массу времени)
4. Все работает через браузер. Не нужно иметь под рукой путти и другие утилиты. Уже все есть
5. Бесплатно!
6. Постоянные обновления (Последнее обновление + 160 лабораторных работ.)
7. На каждую лабу есть ответы. Даже если Вы не уверены в результате, можешь проверить себя.
8. Безопасно! Не наказуемо законом. (Если не нарушать его)
9. Нет ограничений на время выполнения и количество попыток. (Вру – есть. Но это детали см. минусы проекта)
10. И думаю самое важное, чем зацепил меня этот проект. Это возможность самостоятельного изучения новых направлений. Тут нет готовых решений (есть подсказки в лаба), а только направления с ожиданием определенного результата.
11. Можно проходить совместно часть лаб.
12. Есть CSF.
Что не понравилось:
Заголовок спойлера
1. Ограничение на количество запусков инстансов. За сутки только 10 запусков инстансов.
2. Парой результат не совпадает с ответом на сайте
3. Нет поддержки русского языка.
4. Слабое железо, выделяемое на каждый инстанс. (все-таки долго обрабатываются команды)
5. Консоль обрывает соединение по истечению определённого времени. Нужно открывать повторно.
2. Парой результат не совпадает с ответом на сайте
3. Нет поддержки русского языка.
4. Слабое железо, выделяемое на каждый инстанс. (все-таки долго обрабатываются команды)
5. Консоль обрывает соединение по истечению определённого времени. Нужно открывать повторно.
Доп. Материалы
Man nmap :
Cheat sheet :
Man rus nmap
PS Supplement from the authors:
Sites to find the services you need
